Abstract
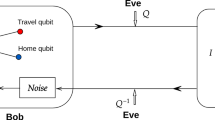
A generalized approach to Ping-Pong protocol analysis is introduced. The method is based on investigation of the density operator describing joint systems of communicating parties and an eavesdropper. The method is more versatile than approaches used so far as it permits on incorporation of different noise models in a unified way and make use of well grounded theory of quantum discrimination in estimation of eavesdropper’s information gain. As the proof of the method usefulness an example of its application to the analysis of the protocol execution over depolarizing and dephasing channels is given.
Access provided by Autonomous University of Puebla. Download to read the full chapter text
Chapter PDF
Similar content being viewed by others
References
Nielsen, M.A., Chuang, I.L.: Quantum Computation and Quantum Information. Cambridge University Press (2000)
Shor, P.W.: Polynomial-time algorithms for prime factorization and discrete logarithms on a quantum computer. SIAM J. Comput. 26(5), 1484–1509 (1997)
Zawadzki, P.: A numerical simulation of quantum factorization success probability. In: Tkacz, E., Kapczyński, A. (eds.) Internet – Technical Developments and Applications. AISC, vol. 64, pp. 223–231. Springer, Heidelberg (2009)
Zawadzki, P.: A fine estimate of quantum factorization success probability. Int. J. Quant. Inf. 8(8), 1233–1238 (2010)
Bennett, C.H., Brassard, G.: Quantum cryptography: Public key distribution and coin tossing. In: Proceedings of International Conference on Computers, Systems and Signal Processing, New York, pp. 175–179 (1984)
Izydorczyk, J., Izydorczyk, M.: Microprocessor scaling: What limits will hold? IEEE Computer 43(8), 20–26 (2010)
Gisin, N., Ribordy, G., Tittel, W., Zbinden, H.: Quantum cryptography. Rev. Mod. Phys. 74, 145–195 (2002)
Bennett, C.H., Wiesner, S.J.: Communication via one- and two-particle operators on Einstein-Podolsky-Rosen states. Phys. Rev. Lett. 69, 2881–2884 (1992)
Wang, C., Deng, F.G., Li, Y.S., Liu, X.S., Long, G.L.: Quantum secure direct communication with high-dimension quantum superdense coding. Phys. Rev. A 71(4), 044305 (2005)
Bennett, C.H., Brassard, G., Crépeau, C., Jozsa, R., Peres, A., Wootters, W.K.: Teleporting an unknown quantum state via dual classical and Einstein-Podolsky-Rosen channels. Phys. Rev. Lett. 70, 1895–1899 (1993)
Stinson, D.R.: Cryptography: Theory and Practice, 2nd edn. Chapman & Hall/CRC (2002)
Long, G.L., Deng, F.G., Wang, C., Li, X.H., Wen, K., Wang, W.Y.: Quantum secure direct communication and deterministic secure quantum communication. Front. Phys. China 2(3), 251–272 (2007)
Boström, K., Felbinger, T.: Deterministic secure direct communication using entanglement. Phys. Rev. Lett. 89(18), 187902 (2002)
Ostermeyer, M., Walenta, N.: On the implementation of a deterministic secure coding protocol using polarization entangled photons. Opt. Commun. 281(17), 4540–4544 (2008)
Vasiliu, E.V.: Non-coherent attack on the ping-pong protocol with completely entangled pairs of qutrits. Quantum Inf. Process. 10, 189–202 (2011)
Zawadzki, P.: Security of ping-pong protocol based on pairs of completely entangled qudits. Quantum Inf. Process. 11(6), 1419–1430 (2012)
Wójcik, A.: Eavesdropping on the ping-pong quantum communication protocol. Phys. Rev. Lett. 90(15), 157901 (2003)
Zhang, Z., Man, Z., Li, Y.: Improving Wójcik’s eavesdropping attack on the ping-pong protocol. Phys. Lett. A 333, 46–50 (2004)
Zawadzki, P.: The Ping-Pong protocol with a prior privacy amplification. Int. J. Quant. Inf. 10(3), 1250032 (2012)
Peres, A.: How to differentiate between non-orthogonal states. Phys. Lett. A 128(1-2), 19 (1988)
Herzog, U.: Optimal state discrimination with a fixed rate of inconclusive results: analytical solutions and relation to state discrimination with a fixed error rate. Phys. Rev. A 86, 032314 (2012)
Herzog, U., Bergou, J.A.: Distinguishing mixed quantum states: Minimum-error discrimination versus optimum unambiguous discrimination. Phys. Rev. A 70, 022302 (2004)
Miszczak, J.A.: Singular value decomposition and matrix reorderings in quantum information theory. Int. J. Mod. Phys. C 22(9), 897–918 (2011)
Fuchs, C.A., van de Graaf, J.: Cryptographic distinguishability measures for quantum-mechanical states. IEEE Trans. Inform. Theor. (4), 1216–1227 (1999)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2013 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Zawadzki, P. (2013). An Analysis of the Ping-Pong Protocol Operation in a Noisy Quantum Channel. In: Kwiecień, A., Gaj, P., Stera, P. (eds) Computer Networks. CN 2013. Communications in Computer and Information Science, vol 370. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-38865-1_36
Download citation
DOI: https://doi.org/10.1007/978-3-642-38865-1_36
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-38864-4
Online ISBN: 978-3-642-38865-1
eBook Packages: Computer ScienceComputer Science (R0)