Abstract
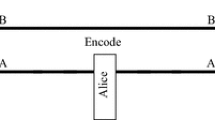
A quantum circuit providing an undetectable eavesdropping of information encoded by bit flip operations in Ping-Pong protocol has been recently proposed by Pavičić [Phys. Rev. A, vol. 87, pp. 042326, 2013]. A modification of the protocol’s control mode is proposed. The introduced improvement remedies deficiencies of the protocol seminal version and permits Pavičić’s attack detection with overwhelming probability. The improved version is also immune to famous Wójcik’s attack [Phys. Rev. Lett., vol. 90, pp. 157901, 2003]. As a result, the Ping-Pong protocol asymptotic security is restored both in perfect and lossy quantum channels.
Access provided by Autonomous University of Puebla. Download to read the full chapter text
Chapter PDF
Similar content being viewed by others
References
Kłosowski, P.: Speech processing application based on phonetics and phonology of the Polish language. In: Kwiecień, A., Gaj, P., Stera, P. (eds.) CN 2010. CCIS, vol. 79, pp. 236–244. Springer, Heidelberg (2010)
Kucharczyk, M.: Blind signatures in electronic voting systems. In: Kwiecień, A., Gaj, P., Stera, P. (eds.) CN 2010. CCIS, vol. 79, pp. 349–358. Springer, Heidelberg (2010)
Sułek, W.: Pipeline processing in low-density parity-check codes hardware decoder. B. Pol. Acad. Sci.-Tech. 59(2), 149–155 (2011)
Dustor, A., Kłosowski, P.: Biometric voice identification based on fuzzy kernel classifier. In: Kwiecień, A., Gaj, P., Stera, P. (eds.) CN 2013. CCIS, vol. 370, pp. 456–465. Springer, Heidelberg (2013)
Dziwoki, G., Kucharczyk, M., Sulek, W.: OFDM transmission with non-binary LDPC coding in wireless networks. In: Kwiecień, A., Gaj, P., Stera, P. (eds.) CN 2013. CCIS, vol. 370, pp. 222–231. Springer, Heidelberg (2013)
Shor, P.W.: Polynomial-time algorithms for prime factorization and discrete logarithms on a quantum computer. SIAM J. Comput. 26(5), 1484–1509 (1997)
Zawadzki, P.: A numerical simulation of quantum factorization success probability. In: Tkacz, E., Kapczynski, A. (eds.) Internet – Technical Development and Applications. AISC, vol. 64, pp. 223–231. Springer, Heidelberg (2009)
Zawadzki, P.: A fine estimate of quantum factorization success probability. Int. J. Quantum Inf. 8(8), 1233–1238 (2010)
Izydorczyk, J., Izydorczyk, M.: Microprocessor scaling: What limits will hold? IEEE Computer 43(8), 20–26 (2010)
Gisin, N., Ribordy, G., Tittel, W., Zbinden, H.: Quantum cryptography. Rev. Mod. Phys. 74, 145–195 (2002)
Long, G.L., Deng, F.G., Wang, C., Li, X.H., Wen, K., Wang, W.Y.: Quantum secure direct communication and deterministic secure quantum communication. Front. Phys. China 2(3), 251–272 (2007)
Boström, K., Felbinger, T.: Deterministic secure direct communication using entanglement. Phys. Rev. Lett. 89(18), 187902 (2002)
Boström, K., Felbinger, T.: On the security of the ping-pong protocol. Phys. Lett. A 372(22), 3953–3956 (2008)
Vasiliu, E.V.: Non-coherent attack on the Ping-Pong protocol with completely entangled pairs of qutrits. Quantum Inf. Process. 10, 189–202 (2011)
Zawadzki, P.: Security of Ping-Pong protocol based on pairs of completely entangled qudits. Quantum Inf. Process. 11(6), 1419–1430 (2012)
Jahanshahi, S., Bahrampour, A., Zandi, M.H.: Security enhanced direct quantum communication with higher bit-rate. Int. J. Quantum Inf. 11(2), 1350020 (2013)
Jahanshahi, S., Bahrampour, A., Zandi, M.H.: Three-particle deterministic secure and high bit-rate direct quantum communication protocol. Quantum Inf. Process. 12(7), 2441–2451 (2013)
Zawadzki, P.: Improving security of the Ping-Pong protocol. Quantum Inf. Process. 12(1), 149–155 (2013)
Zawadzki, P.: The Ping-Pong protocol with a prior privacy amplification. Int. J. Quantum Inf. 10(3), 1250032 (2012)
Ostermeyer, M., Walenta, N.: On the implementation of a deterministic secure coding protocol using polarization entangled photons. Opt. Commun. 281(17), 4540–4544 (2008)
Wójcik, A.: Eavesdropping on the Ping-Pong quantum communication protocol. Phys. Rev. Lett. 90(15), 157901 (2003)
Pavičić, M.: In quantum direct communication an undetectable eavesdropper can always tell ψ from φ Bell states in the message mode. Phys. Rev. A 87, 042326 (2013)
Coles, P.J.: Role of complementarity in superdense coding. Phys. Rev. A 88, 062317 (2013)
Zawadzki, P., Puchała, Z., Miszczak, J.: Increasing the security of the Ping-Pong protocol by using many mutually unbiased bases. Quantum Inf. Process. 12(1), 569–575 (2013)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2014 Springer International Publishing Switzerland
About this paper
Cite this paper
Zawadzki, P. (2014). Ping-Pong Protocol Strengthening against Pavičić’s Attack. In: Kwiecień, A., Gaj, P., Stera, P. (eds) Computer Networks. CN 2014. Communications in Computer and Information Science, vol 431. Springer, Cham. https://doi.org/10.1007/978-3-319-07941-7_21
Download citation
DOI: https://doi.org/10.1007/978-3-319-07941-7_21
Publisher Name: Springer, Cham
Print ISBN: 978-3-319-07940-0
Online ISBN: 978-3-319-07941-7
eBook Packages: Computer ScienceComputer Science (R0)