Abstract
This paper, presents a novel chaos-based image steganography algorithm. Because of efficient property of chaos based security systems besides steganography applicability in providing secure communication, chaos based steganography algorithms served as a hot topic in recent researches. The proposed scheme possess novelties and advantageous such as: 1) Introducing a novel 3-dimensional chaotic map (LCA map) with strong chaotic characteristics and maximum Lyapunov exponent 20.58, which is used for generating three chaotic sequences, each of them represents the number of row, column, and colour component, respectively. 2) Utilizing random selection procedure for selecting subsequences with length of 2L, which L is the length of secret message 3) Specifying L pairs of triples host positions for embedding LSBs and MSBs of secret message by using three high level chaotic maps. 4) Entering some parameters dependent on elementary initial values, host image, and secret message features as a key point for adding additional layer of security alongside providing high sensitivity. 5) Providing high capacity for embedding secret message, which is equal to 50 % of whole image capacity (M × N × 12). The proposed method could be applied in different criterion such as, confidential communication and data storing, protection of data alteration, and etc. Our experimental results guarantees that our scheme is not only robust against differential attacks, but also has promising results such as highly sensitive keys, Quality index, PSNR, MSE, and hiding capacity as shown in statistical security analysis.
Similar content being viewed by others
Avoid common mistakes on your manuscript.
1 Introduction
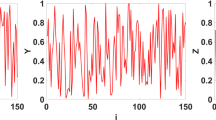
Due to the growth of internet connections for transmitting secret data, steganography plays an important role in the secure communications. Therefore, too many studies have been done in this field and it becomes an interesting research field in the information hiding. Indeed, the word steganography is obtained from the Greek words “stegos” means “cover” and “grapha” means “writing”, defining it as “covered writing” that hides the existence of the message in itself [23]. Its main idea is to hide secret data in a carrier during communication. Besides, it provides potential for private and secure communication that has become a necessity of most of applications in today’s world [6, 7, 13, 14, 18, 19]. The security systems categorized in two types, the first one is “cryptography” and the other one is “information hiding” [4]. The information hiding systems classified into two groups, which entitled “steganography” and “watermarking”. The methodologies of watermarking and steganography is the same, but the purpose of these techniques is different [3]. Cryptography and steganography have the same purpose, i.e., to conceal the information message, but they use different methods in order to achieve this aim [5]. Watermarking used for copyright protection of digital data, while steganography used for information hiding. Steganography includes two categories. The first one is “linguistic steganography”, which utilize natural language as a carrier for hiding secret data. The other one is “technical steganography”, which uses multimedia carrier, such as image, audio and video for embedding secret data. With rising of chaos theory in the recent decades, researchers have used it as a reliable tool in their methods. Sensitivity to primary conditions, non-periodic, non-convergence and controlling parameters are unique properties of chaotic cryptography compared to traditional ones. These characteristics have attracted many researchers to use this tool as a vital solution in their studies. Potdar et al. [17] used a spatial domain technique in producing a fingerprinted secret sharing steganography for robustness against image cropping attacks. They break the image to some sub images and do the same with secret data and finally, put this segmented data in sub images. Shirali-Shahreza et al. [22] proposed a method for steganography based on linguistic methods. They used Persian and Arabic alphabet as a carrier for hiding secret data. Sabery et al. [21] proposed a method for hiding a secret image in a host image by using a simple logistic map. The logistic map used for determining the blocks of pixels that used for embedding process. Kanso et al. [15] proposed a digital image steganography method based on Arnold cat map. Roy et al. [20], presented a chaos based adaptive image steganography, which combines the efficiency of matrix encoding and LSBM to embed data besides using chaos to provide enhanced security. Bilal et al. [10], introduced a novel chaos-based zero-steganography algorithm, which embeds data based on relationship between cover image, chaotic sequence and payload, instead of directly embedding data in cover image. Bandyopadhyay et al. [9], proposed a chaotic method for steganography that encrypt secret bits before embedding procedure by using chaos. Ghebleh and Kanso [12], proposed a robust chaotic algorithm for digital image steganography that used 3-dimensional chaotic cat map alongside discrete wavelet transform. Das and Kar [11], presented a novel DNA-based image steganography that is using 2D chaotic map that used to construct DNA strand from cover image. Alam et al. [1], presented an improved method for image steganography using edge detection besides using logistic map as a secret key random number generation for random LSB substitution. Finally, Anees et al. [3] introduced a steganography technique in spatial domain for digital images based on chaotic maps for resolving pixel positions. Their method has two security shortcomings. First, this scheme does not have a dependency on its secret keys and host image. Therefore, the indices that produced for determining rows, columns, and colour components of carrier pixels are not sensitive to host image. This causes an adversary can use this breach to achieve some useful information about positions of embedded data and break steganography algorithm (Fig. 1). Second, in their method, the host image is first broken into “upper part” and “downer part” respectively to determine the positions of embedded data. This leads an adversary to find a position of embedded data with the help of the other place of them. In fact, he/she can obtain the positions of some embedded data by plus or minus of them with n/2, where n, represent the column size of the host image. Hence, these weaknesses exposed their algorithm to known message attack.
We proposed a novel method to overcome these shortcomings, which is not only highly dependent on “secret keys” and “original image”, but also it has high-grade results. Indeed, we introduced a novel 3-dimensional chaotic map (LCA map) with maximum Lyapunov exponent 20.58. Moreover, by applying LCA map, three sequences X, Y and Z with length of more than 2L generated, where L is the length of secret message. These chaotic sequences are used for determining the number of rows, columns and color components of carrier pixels, respectively. Afterward, subsequences with a length of 2L of generating sequences are intercepted. Next, three high level chaotic maps are used for selection of desirable pairs of triples as host pixel positions for embedding LSBs and MSBs of secret message. Hence, for each letter of secret message, there are two proper positions that should be converted into binary of eight bits. Then, these bits are segmented into two equal parts. The first part “MSB” will remain unchanged and the second part “LSB” will be replaced by the first MSB bits of secret message. The same procedure will be applied for the second selected pixel position to replace LSB bits of secret message. Finally, we convert binary positions into decimal and make steganography image. Our experimental results guarantees that the proposed method is robust against differential attacks and has eligible results such as highly sensitive keys, Quality index, PSNR, MSE, and hiding capacity.
The paper structure is as follows. Section 2 describes necessary mathematical basics. Our proposed method is explained in Section 3, after that, in Section 4 we come through statistical security analysis and finally, the conclusion is declared in Section 5.
2 High level chaotic maps
2.1 3-dimensional LCA map
We introduced a novel 3-dimensional chaotic map (LCA map) on interval [0, 1] that possesses strong chaotic characteristics and its maximum Lyapunov exponent is equal to 20.58, where control parameter α = 0.0001, r = 4, and N = 4. The mathematical formula is as below:
Where α ∈ [0, 1/N] and r ∈ [3.65, 4] are control parameters for LCA map. Besides, variables x n-1 , y n-1 , and z n-1 are initial state conditions, which are on the interval [0, 1], respectively. The maximum Lyapunov exponent of LCA map for α ϵ [0, 0.25] (in this case 1/N equal to 0.25) and spatiotemporal diagram are shown in Figs. 2 and 3, respectively.
In following subsection (2.2, 2,3), in order to specify L pairs of triples host positions for embedding LSBs and MSBs of secret message, we utilized two high level chaotic maps that have been introduced in our previous work [16], besides Chebyshev map.
2.2 The cosines-arcsines system
The “CA map” is defined on the interval [0, 1] with the following mathematical formula:
Where γ, is a control parameter in a range (0, 4) and X n is initial state condition, which is in the interval [0, 1]. Moreover, in parameter value γ = 3.976 Lyapunov exponent has maximum value λ =1.38.
2.3 The sinus-power logistic system
The “SPL map” is defined on interval [-0.48, 0.48]. Moreover, in parameter value β = 3.465 Lyapunov exponent has maximum value λ = 1.518. The mathematical formula of this chaotic map is as below:
Where β is control parameter in the range (0, 3.5) and X n is initial state condition with a range (-0.48, 0.48).
2.4 Chebyshev map
The last chaotic map that used in this scheme is “Chebyshev map”, which is defined on interval [-1, 1]. The mathematical formula of this map is as below:
Where k is control parameter and X n is an initial state condition that lies in interval [-1, 1]. Furthermore, this map has chaotic behaviour for k ≥ 2 and its Lyapunov exponent is equal to ln k.
3 Proposed method
Two main phases of proposed scheme are embedding and extraction phases, which are described in detailed as follows:
3.1 Embedding phase
The overall view of proposed method shown in Fig. 4. In order to make our scheme highly dependent on all of its secret keys and original image, we define four parameters as stated below:
where L, represent the length of secret message, MSBs (LSBs) is most (least) significant bits of secret message, P is the sum of the whole of pixel values in the host image, and Q represents sum of all secret message letters (M i ) in binary mode. In order to provide high key sensitivity, we multiply this parameter to initial state conditions of the LCA map for building desired initial state conditions as below:
Then this modulated initial sate condition is used as an input for LCA map. We iterate this map s times where s is the maximum of Q + M and Q + N. Next, we utilize a random selection technique in order to select 2L random elements of generated sequences in previous steps. Indeed, this random selection method decreases transient effect and improves security of our scheme. In the following the procedure of random selection technique is described.
Subsequences \( \tilde{X},\tilde{Y},\tilde{Z} \) with the length of 2L are intercepted from X, Y, Z by starting from indices i Row , i Column , i Color , respectively, where indices are produced based on following pseudo-code:
We note that if the procedure of the selection subsequences is stopped by reaching to the end of the main sequence, we start from the beginning to select remain elements. After that, by multiplying 106 and modulating, we reform these subsequences \( \tilde{X},\tilde{Y},\tilde{Z} \) to integer sequences in intervals [1, m], [1, n], and [14, 23], which represent the number of row, column, and colour component, respectively. Now, we seek for random pairs of triples in subsequences \( \tilde{X},\tilde{Y},\tilde{Z} \), which are used to embed MSBs and LSBs of secret message. For this, chaotic maps CA, SPL and Chebyshev with initial conditions, x0, y0, z0 are iterated 2L times. After sorting these three generating sequences, the corresponding indices for random selection of row, column, and colour component from \( \tilde{X},\tilde{Y},\tilde{Z} \) are determined. We denote notation (i l , j l , k l ), 1 ≤ l ≤ 2L, as lth random triple. The selected pixel values and secret message are converted into binary of eight bits and split into two equal parts MSBs and LSBs. The information of MSBs and LSBs will be embedded into LSBs in the specified positions (i c , j c , k c ) and (i d , j d , k d ), respectively, where c = 2l + 1 and d = 2l + 2, 0 ≤ l ≤ L− 1. Finally, by converting pixel values to decimal, the steganographic image will be obtained. In Fig. 5 the original and its steganographic image have been shown.
3.2 Extraction phase
In this phase, the extraction process secret message from steganographic image is described. Indeed, this procedure is the reverse of embedding algorithm. The receiving party must know secret keys (L, L M, L L , P, α, r, β, γ, k, x 0 , y 0 , z 0 , x LCA0 , y LCA0 , z LCA0 ) to extract the secret message by following procedure. Frist, the stego-image used as an input in this phase. After that, by applying LCA map and using of desired initial state conditions (Eqs. 9–11), chaotic sequences X, Y, Z will be produced, respectively. In order to determine the positions of embedded data, 2L random elements for each sequence \( \tilde{\boldsymbol{X}},\tilde{\boldsymbol{Y},}\tilde{\boldsymbol{Z}} \), will be intercepted from X, Y, Z by starting indices specified in Eqs. 12–14, respectively. Thereafter, we use three chaotic maps (CA, SPL and Chebyshev) to find L pairs (ic, jc, kc) and (id, jd, kd), of host pixel positions, in which the MSBs and LSBs of secret message are embedded, respectively. Next, receiver extracts data, including MSBs and LSBs from mentioning positions and joins them to each other. Finally, the secret message can be revealed after converting data to decimal.
4 Statistical security analysis
In this section, we provide some statistical analysis such as, correlation, entropy, homogeneity, contrast, energy, key sensitivity, mean squared error, peak signal to noise ratio, quality of the index, histogram, and chi-square test, which prove our method is robust against statistical attacks. We use standard images that are used broadly in this criterion.Footnote 1
4.1 Correlation
The purpose of this test is to determine the similarity between two images. The correlation of the image can be calculated based on below equation:
Where i, j represents the pixel positions; p (i, j) is the pixel value at ith row and jth column; μ is the variance; σ is the standard deviation.
4.2 Information entropy
In information theory, entropy is a scale for showing randomness in information. This scale can be calculated based on below equation:
In the above equation, P (s i ) is likelihood frequency of symbol s i ∈ s and Q is the number of bits, used for displaying symbol s i .
4.3 Homogeneity
The homogeneity analysis is a metric that returns a value, for determining the closeness of the distribution of elements in the gray level co-occurrence matrix (GLCM) to the GLCM diagonal. The homogeneity of an image can be calculated based on the following equation:
Where p (i, j) is the pixel value at the ith row and jth column and the values of (i, j) represent the indices of row and column numbers, respectively.
4.4 Contrast
Contrast analysis returns a measure of the intensity contrast between a pixel and its neighbor over the whole image. This analysis enables the viewer to better recognize the objects in the texture of an image. The mathematical formula of this analysis is as below:
4.5 Energy
The energy analysis is used to measure the energy of the encrypted image. It returns the sum of squared elements in the GLCM. This analysis can be done with the help of Eq. (19):
The results of correlation, entropy, homogeneity, contrast and energy analysis provided in Table 1. As it is shown obvious based on the results provided in Table 1, the original image and steganographic image are identical. This proves that our proposed method not only has good efficiency, but also it produces an image with high quality. A key point is that when the steganographic image be the same as host image, an adversary cannot use statistical attacks, due to the fact that all statistical characteristics of host image are the same as steganographic one. Therefore, our scheme is robust against statistical attacks.
4.6 Image histogram
The steganographic image resistant against statistical attack when the colour histogram of steganographic image is the same as host image. The image histogram of Baboon plain image and its steganographic image are depicted in Fig. 6.
4.7 Key sensitivity
Based on using high level chaotic maps, such as LCA map with large maximum Lyapunov exponent besides making dependent relations between initial condition and effective parameters, we enhance key sensitivity. In order to show this sensitivity, the baboon image is used for test, we apply a little change (10−16) to one of initial state conditions of chaotic maps. As it is obvious in Fig. 7, secret data cannot be extracted, which embedded into the steganographic image.
4.8 Hiding capacity
One important subject in steganographic algorithm is hiding capacity. A steganographic algorithm called powerful, if it can embed a high mass of secret data. In our proposed method, we used 4bits of LSBs in all channels to embed data, so our hiding capacity is equal to 4/8. A comparison between our method and other available methods provide in Table 2.
As you can see in Table 2, our proposed method has the highest hiding capacity among other available chaos-based methods. Hence, we can embed secret messages with longer length and this is a vital advantage for steganography algorithm.
4.9 Quality index
In order to measure, quality of steganographic image, we use quality index [24] that is calculated based on below formula:
Where,
In the above equation, n is the number of pixels in the image, H is the host image and T is the steganography image. The value of Q is between 1 and -1. If the calculated value be -1, it means that, the host image and the steganographic image don’t have any similarity, but if it equals to 1, it means that the two images are identical. The calculated value for this test after applying our method with fifty thousand letters equal to 0.999705171806858, which is so close to one. It means that our method has a good image quality. A comparison of quality index between proposed method and some available methods for Baboon image provided in Table 3.
Based on Table 3, this subject can be deduced that our steganographic image has high similarity with the original image. Furthermore, its values for the test image is better than other available methods. Therefore, as mentioned before, if the steganographic image is very close to its original one the adversary cannot use statistical analysis to extract secret message and achieve his purpose of breaking steganography algorithm.
4.10 Chi-square test
In the proposed method, we use LSBs of the host image to embed secret data, therefor, the LSB plane of image would be changed after embedding process. Chi-square test, [8] is kinds of statistical analysis that helps us to understand whether a difference between expected signal and observed signal exist or not. The result of this test is shown in Fig. 8. If the red line comes close to 1, it means that, there is a data, which is embedded in host image, in contrast, if it’s close to zero, it means existence of hidden secret data in the host image can’t observe.
4.11 MSE
Mean squared error shows the difference between host image and steganography image. It’s calculated based on below formula:
As you can see in Fig. 8, our proposed method embed secret data in such a way that the LSB plane of the image would not be changed, because the red line is equal to zero. Indeed, the adversary cannot gain any useful information from steganographic image, due to the fact that there is no change occurred in the LSB plane of the image. Therefore, our scheme passes this test successfully and it will be robust against this kind of analysis.
4.12 PSNR analysis
Another important test which shows the strength of steganography method is PSNR test. As it’s shown in below equation, we get the signal strength and divide it by mean squared error, so provides a better comparative statistical analysis.
The results of Quality index and PSNR for Baboon (256 × 256,512 × 512) are stated in Tables 4 and 5, respectively.
As you can see in the above table, the proposed method has a promising result of PSNR analysis. The Quality index for all length of secret messages has the amazing value 0.999. This value for Quality index means that the steganographic image is identical to the original image. Hence, the adversary cannot do statistical analysis to break the steganography algorithm and extract secret message.
Based on the above table, if the size of the image becomes higher the results get better in both of analytical aspects. Therefore, we should remark this key point that such a good value for booth PSNR and Quality index lead to robustness against statistical attack, because when the host image and steganographic image be identical he cannot achieve information about the steganographic image and extract secret message.
4.13 Image fidelity
Another metric, which is used to show robustness of our scheme is image fidelity. The fidelity measure is measured by Image Fidelity that is calculated based on below equation:
A comparison between proposed method and other available schemes based on PSNR, quality index, and image fidelity for baboon image (with 262144 bit embedding) provided in Table 6.
As it is obvious, based on the above table, our proposed method has better PSNR, Quality index, and image fidelity value among other available methods. Hence, the proposed method has strength as mentioned and robust against statistical attack.
4.14 Known cover attack
In this type of attack, the adversary has information about cover image H, and then he compares this cover image with steganographic image by using statistical analysis, in order to find different patterns between them. Determination of host pixel positions, which has done by high level chaotic maps, avoids this kind of attack for two reasons. First, specification of host pixel positions are highly dependent on message (Eq. 9-11) that causes an adversary by having cover and steganography image (without secret message) cannot be able to achieve critical information by statistical analysis. Second, uniformly distribution of chaotic orbits on total space of cover image for determining host pixel positions, prevents adversary from gaining useful information. Based on aforementioned facts beside experimental analysis (4.1 through 4.6), the proposed method embed data in such a way that there exist only a vital change between original and steganographic image. Therefore, the adversary could not be able to gain anything except similar patterns. Indeed, our method has a good statistical analysis, which makes our scheme robust against this type of attack.
4.15 Known message attack
In this attack, the adversary knows the original message (M). With original message and cover image H, nobody can obtain hidden information, because our proposed method is highly dependent on its secret keys and cover image, and if one of this parameters value changes a bit, the position of embedded data will change. So, our method is robust against this kind of attack.
5 Conclusion
This paper presented a novel 3-dimensional chaotic map (LCA map) with strong chaotic characteristics and high maximum Lyapunov exponent 20.58. Indeed, by using LCA map along with three high level chaotic maps, desirable pair of triples host positions for embedding LSBs and MSBs of secret message are determined. Indeed, the aforementioned high level chaotic maps provide a uniformly distributation of chaotic orbits in the total space of cover image, which produce a steganographic image that is possess high similarity with cover image. By entering some parameters, which are dependent on elementary initial values, host image and secret message features, we achieve high key sensitivity (10−16) besides adding additional layer of security. In fact, as it is shown in Fig. 1, similar secret messages for different cover image or converse circumstance, produced different host pixel positions, which implies that the adversary could not be able to gain useful information to break our steganography scheme. Our statistical analysis (4.1 through 4.6) is not only prove that our scheme provide good statistical quality, but also guarantees robustness of our scheme against differential attacks (4.14, 4.15). Indeed, the steganographic image and cover image are similar to each other in high rate, which prevents obtaining different patterns that are useful for an adversary to break a steganography algorithm. Furthermore, comparison of proposed scheme with other available methods (Tables 2, 3, and 6) shows priority of our scheme in sense of hiding capacity (12 MN bits for M × N cover image), quality index, PSNR, and image fidelity. Moreover, Our experimental results guarantees that our scheme is not only robust against differential attacks, but also has a promising results such as highly sensitive keys, Quality index (0.999705171806858), PSNR, and hiding capacity as shown in statistical security analysis.
References
Alam S, Kumar V, Siddiqui W, Ahmad M (2014) Key dependent image steganography using edge detection. In: Advanced Computing & Communication Technologies (ACCT), 2014 Fourth International Conference on. IEEE, pp 85–88
Alam S, Kumar V, Siddiqui WA, Ahmad M (2014) Key dependent image steganography using edge detection. In: Advanced Computing & Communication Technologies (ACCT), 2014 Fourth International Conference on. IEEE, pp 85–88
Anees A et al (2014) A technique for digital steganography using chaotic maps. Nonlinear Dyn 75(4):807–816
Arshad H, Nikooghadam M (2014) Three-factor anonymous authentication and key agreement scheme for telecare medicine information systems. J Med Syst 38(12):1–12
Arshad H, Nikooghadam M (2015) Security analysis and improvement of two authentication and key agreement schemes for session initiation protocol. J Supercomput 71(8):3163–3180
Arshad H, Nikooghadam M (2016) An efficient and secure authentication and key agreement scheme for session initiation protocol using ECC. Multimed Tools Appl 75(1):181–197
Arshad H, Teymoori V, Nikooghadam M, Abbassi H (2015) On the security of a two-factor authentication and key agreement scheme for telecare medicine information systems. J Med Syst 39(8):1–10
Aziz M, Tayarani-N MH, Afsar M (2015) A cycling chaos-based cryptic-free algorithm for image steganography. Nonlinear Dyn 80(3):1271–1290
Bandyopadhyay D, Dasgupta K, Mandal JK, Dutta P (2014) A novel secure image steganography method based on chaos theory in spatial domain. Int J Secur Priv Trust Manag (IJSPTM) 3(1):11–22
Bilal M, Imtiaz S, Abdul W, Ghouzali S, Asif S (2014) Chaos based Zero-steganography algorithm. Multimed Tools Appl 72(2):1073–1092
Das P, Kar N (2014) A DNA based image steganography using 2D chaotic map. In: Electronics and Communication Systems (ICECS), 2014 International Conference on. IEEE, pp 1–5
Ghebleh M, Kanso A (2014) A robust chaotic algorithm for digital image steganography. Commun Nonlinear Sci Numer Simul 19(6):1898–1907
Johnson NF, Jajodia S (1998) Exploring steganography: seeing the unseen. Computer 31(2):26–34
Judge J (2001) Steganography: past, present, future. SANS white paper
Kanso A, Own HS (2012) Steganographic algorithm based on a chaotic map. Commun Nonlinear Sci Numer Simul 17(8):3287–3302
Mollaeefar M, Sharif A, Nazari M (2015) A novel encryption scheme for colored image based on high level chaotic maps. Multimedia Tools Appl 1–23
Potdar VM, Han S, Chang E (2005) Fingerprinted secret sharing steganography for robustness against image cropping attacks. In: Industrial Informatics, 2005. INDIN’05. 2005 3rd IEEE International Conference on. IEEE, pp 717–724
Provos N, Honeyman P (2003) Hide and seek: an introduction to steganography. IEEE Secur Priv 1(3):32–44
Provos N, Honeyman P (2001) Detecting steganographic content on the internet. Center for Information Technology Integration
Roy R, Sarkar A, Changder S (2013) Chaos based edge adaptive image steganography. Procedia Technol 10:138–146
Sabery KM, Yaghoobi M (2008) A simple and robust approach for image hiding using chaotic logistic map. In Advanced Computer Theory and Engineering, 2008. ICACTE’08. International Conference on. IEEE, pp 623–627
Shirali-Shahreza MH, Shirali-Shahreza M (2006) A new approach to Persian/Arabic text steganography. In: Computer and Information Science, 2006 and 2006 1st IEEE/ACIS International Workshop on Component-Based Software Engineering, Software Architecture and Reuse. ICIS-COMSAR 2006. 5th IEEE/ACIS International Conference on. IEEE, pp 310–315
Subhedar MS, Mankar VH (2014) Current status and key issues in image steganography: a survey. Comput Sci Rev 13:95–113
Wang Z, Bovik AC (2002) A universal image quality index. IEEE Signal Process Lett 9(3):81–84
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Sharif, A., Mollaeefar, M. & Nazari, M. A novel method for digital image steganography based on a new three-dimensional chaotic map. Multimed Tools Appl 76, 7849–7867 (2017). https://doi.org/10.1007/s11042-016-3398-y
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11042-016-3398-y