Abstract
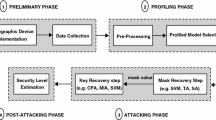
Side channel attacks take advantage of information leakages in cryptographic devices. Template attacks form a family of side channel attacks which is reputed to be extremely effective. This kind of attacks assumes that the attacker fully controls a cryptographic device before attacking a similar one. In this paper, we propose to relax this assumption by generalizing the template attack using a method based on a semi-supervised learning strategy. The effectiveness of our proposal is confirmed by software simulations, by experiments on a 8-bit microcontroller and by a comparison to a template attack as well as to two supervised machine learning methods.
Access provided by Autonomous University of Puebla. Download to read the full chapter text
Chapter PDF
Similar content being viewed by others
Keywords
References
Alpaydin, E.: Introduction to Machine Learning, 2nd edn. The MIT Press (2010)
Batina, L., Gierlichs, B., Lemke-Rust, K.: Differential Cluster Analysis. In: Clavier, C., Gaj, K. (eds.) CHES 2009. LNCS, vol. 5747, pp. 112–127. Springer, Heidelberg (2009)
Breiman, L.: Random forests. Machine Learning 45, 5–32 (2001)
Chari, S., Rao, J.R., Rohatgi, P.: Template attacks. In: Kaliski Jr., B.S., Koç, Ç.K., Paar, C. (eds.) CHES 2002. LNCS, vol. 2523, pp. 13–28. Springer, Heidelberg (2003)
Cortes, C., Vapnik, V.: Support-vector networks. Machine Learning, 273–297 (1995)
Daemen, J., Rijmen, V.: The Design of Rijndael: AES - The Advanced Encryption Standard. Springer (2002)
Dimitriadou, E., Hornik, K., Leisch, F., Meyer, D., Weingessel, A.: e1071: Misc Functions of the Department of Statistics (e1071), TU Wien. R package version 1.6 (2011)
Dyrkolbotn, G.O., Snekkenes, E.: Modified Template Attack: Detecting Address Bus Signals of Equal Hamming Weight. In: Ntnu, S.F.M. (ed.) The 2nd Norwegian Information Security Conference (NISK 2009), pp. 43–56. Tapir Akademisk Forlag (November 2009)
Gan, G., Ma, C., Wu, J.: Data clustering - theory, algorithms, and applications. Series on Statistics and Applied Probability. SIAM, Society for Industrial and Applied Mathematics (2007)
Gandolfi, K., Mourtel, C., Olivier, F.: Electromagnetic Analysis: Concrete Results. In: Koç, Ç.K., Naccache, D., Paar, C. (eds.) CHES 2001. LNCS, vol. 2162, pp. 251–261. Springer, Heidelberg (2001)
Hardle, W., Hlavka, Z.: Multivariate Statistics: Exercises and Solutions, 1st edn. Springer Publishing Company, Incorporated (2007)
Hastie, T., Tibshirani, R., Friedman, J.: The Elements of Statistical Learning: Data Mining, Inference, and Prediction, 2nd edn. Springer Series in Statistics. Springer (September 2009)
Heuser, A., Zohner, M.: Intelligent machine homicide. In: Schindler, W., Huss, S.A. (eds.) COSADE 2012. LNCS, vol. 7275, pp. 249–264. Springer, Heidelberg (2012)
Hollestelle, G., Burgers, W., Hartog, J.I.D.: Power Analysis on Smartcard Algorithms Using Simulation. Imported from DIES (2004)
Hospodar, G., Gierlichs, B., De Mulder, E., Verbauwhede, I., Vandewalle, J.: Machine learning in side-channel analysis: a first study. J. Cryptographic Engineering 1(4), 293–302 (2011)
Hospodar, G., De Mulder, E., Gierlichs, B., Vandewalle, J., Verbauwhede, I.: Least Squares Support Vector Machines for Side-Channel Analysis. Center for Advanced Security Research Darmstadt, pp. 99–104 (2011)
Kocher, P.C.: Timing Attacks on Implementations of Diffie-Hellman, RSA, DSS, and Other Systems. In: Koblitz, N. (ed.) CRYPTO 1996. LNCS, vol. 1109, pp. 104–113. Springer, Heidelberg (1996)
Kocher, P.C., Jaffe, J., Jun, B.: Differential Power Analysis. In: Wiener, M. (ed.) CRYPTO 1999. LNCS, vol. 1666, pp. 388–397. Springer, Heidelberg (1999)
Lerman, L., Bontempi, G., Markowitch, O.: Power analysis attack: an approach based on machine learning. International Journal of Applied Cryptography (to appear)
Lerman, L., Bontempi, G., Markowitch, O.: Side Channel Attack: an Approach Based on Machine Learning. Center for Advanced Security Research Darmstadt, pp. 29–41 (2011)
Lerman, L., Bontempi, G., Markowitch, O.: sideChannelAttack: Side Channel Attack, R package version 1.0-6 (2012)
Liaw, A., Wiener, M.: Classification and regression by randomforest. R. News 2(3), 18–22 (2002)
Maechler, M., Rousseeuw, P., Struyf, A., Hubert, M.: Cluster Analysis Basics and Extensions (2005)
Messerges, T.S., Dabbish, E.A., Sloan, R.H.: Investigations of Power Analysis Attacks on Smartcards. In: Proceedings of the USENIX Workshop on Smartcard Technology on USENIX Workshop on Smartcard Technology, Berkeley, CA, USA, p. 17 (1999)
Oren, Y., Renauld, M., Standaert, F.-X., Wool, A.: Algebraic side-channel attacks beyond the hamming weight leakage model. In: Prouff, E., Schaumont, P. (eds.) CHES 2012. LNCS, vol. 7428, pp. 140–154. Springer, Heidelberg (2012)
Oswald, E., Mangard, S.: Template Attacks on Masking—Resistance Is Futile. In: Abe, M. (ed.) CT-RSA 2007. LNCS, vol. 4377, pp. 243–256. Springer, Heidelberg (2006)
Renauld, M., Standaert, F.-X.: Algebraic side-channel attacks. In: Bao, F., Yung, M., Lin, D., Jing, J. (eds.) Inscrypt 2009. LNCS, vol. 6151, pp. 393–410. Springer, Heidelberg (2010)
Sergios, T., Konstantinos, K.: Pattern Recognition, 3rd edn. Academic Press, Inc., Orlando (2006)
Singh, S.S., Chauhan, N.C.: K-means v/s k-medoids: A comparative study. In: National Conference on Recent Trends in Engineering and Technology (2011)
Standaert, F.-X., Peeters, E., Archambeau, C., Quisquater, J.-J.: Towards Security Limits in Side-Channel Attacks. IACR Cryptology ePrint Archive 2007, 222 (2007)
Velmurugan, T., Santhanam, T.: Computational complexity between k-means and k-medoids clustering algorithms for normal and uniform distributions of data points. Journal of Computer Science 6(3), 363–368 (2010)
Wang, S., Le, T.-H., Berthier, M.: When CPA and MIA go hand in hand. In: Center for Advanced Security Research Darmstadt, pp. 82–98 (2011)
Arduino website, http://www.arduino.cc (consulted December 8, 2011)
Zhu, X.: Semi-Supervised Learning Literature Survey Contents. SciencesNew York 10(1530), 10 (2008)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2013 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Lerman, L., Medeiros, S.F., Veshchikov, N., Meuter, C., Bontempi, G., Markowitch, O. (2013). Semi-Supervised Template Attack. In: Prouff, E. (eds) Constructive Side-Channel Analysis and Secure Design. COSADE 2013. Lecture Notes in Computer Science, vol 7864. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-40026-1_12
Download citation
DOI: https://doi.org/10.1007/978-3-642-40026-1_12
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-40025-4
Online ISBN: 978-3-642-40026-1
eBook Packages: Computer ScienceComputer Science (R0)