Abstract
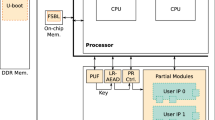
There are numerous techniques, methods and tools to promote the security of a digital system, however, each day the mechanisms of attack evolve and are integrated, creating separate spheres of combined attacks. In this context, this paper presents an embedded security system (into a SoC system) that has as main goal an integration of the security services. It reaches an improved performance and prevents malicious attacks on systems and networks. The SoC prioritizes the implementation of dedicated functions in hardware as cryptographic algorithms, communication interfaces, among others. In our prototype, initially, the flow control functions and settings are running in software. This article shows the architecture, functionality and performance of the system developed, and we discuss a real implementation in FPGA.
Access provided by Autonomous University of Puebla. Download to read the full chapter text
Chapter PDF
Similar content being viewed by others
References
Bell, D.E., Lapadula L.: Secure Computer System: Unified Exposition and Multics Interpretation. Technical Report MTR-2997 Rev. 1, MITRE Corporation, Bedford, MA (1975)
Baker, M.P.: Integrated security system. In: Proceedings International Carnahan Conference on Security Technology (1989)
Okamoto, E.: Proposal for integrated security systems. In: Proceedings of the Second International Conference on Systems Integration ICSI 1992 (1992)
Ferraiolo, D.F., Sandhu, R., Gavrila, S., Kuhn, D.R., Chandramouli, R.: Proposed NIST standard for role-based access control. ACM Transactions on Information and System Security 4(3), 224–274 (2001)
Zilys, M., Valinevicius, A., Eidukas, D.: Optimizing strategic control of integrated security systems. In: 26th International Conference on Information Technology Interfaces (2004)
Ghindici, D., Grimaud, G., Simplot-Ryl, I., Liu, Y., Traore, I.: Integrated Security Verification and Validation: Case Study. In: IEEE Conference on Local Computer Networks (2006)
Jonsson, E.: Towards an integrated conceptual model of security and dependability, Availability, Reliability and Security. In: ARES 2006 (2006)
Nissanke, N.: An Integrated Security Model for Component–Based Systems. In: IEEE Conference Emerging Technologies & Factory Automation, ETFA (2007)
Zambreno, J., Nguyen, D., Choudhary, A.: Exploring Area/Delay Tradeoffs in an AES FPGA Implementation, Department of Electrical and Computer Engineering Northwestern University (2004)
Deepakumara, J., Heys, H.M., Venkatesan, R.: FPGA implementation of MD5 hash algorithm. In: Emerging VLSI Technologies and Architectures. IEEE Computer Society, Los Alamitos (2006)
McEvoy, R.P., Crowe, F.M., Murphy, C.C., Marnane, W.P.: Optimisation of the SHA-2 family of hash functions on FPGAs. In: Emerging VLSI Technologies and Architectures. IEEE Computer Society, Los Alamitos (2006)
Brian Connell, J.: A huffman-shannon-fano code. In: Proceedings of the IEEE, pp. 1046–1047 (July 1973)
Michalski, A., Buell, D.: A Scalable Architecture for RSA Cryptography on Large FPGAs, Field-Programmable Custom Computing Machines. In: FCCM 14th Annual IEEE Symposium (2006)
Monta Vista Embedded Linux Software, http://www.mvista.com/
Xilinx Document, PowerPC 405 Processor Block Reference Guide, Embedded Development Kit, document: ug018 (2008)
den Boer, B., Bosselaers, A.: Collisions for the compression function of MD-5. In: Helleseth, T. (ed.) EUROCRYPT 1993. LNCS, vol. 765, pp. 293–304. Springer, Heidelberg (1994)
Fry, J., Langhammer, M.: RSA & Public Key Cryptography in FPGAs, Altera document (2005)
Rasheed, H., Randy, Y.C., Chow: An Information Model for Security Integration. In: 11th IEEE International Workshop on Future Trends of Distributed Computing Systems (FTDCS 2007) (2007)
Sasaki, Y., Wang, L., Ohta, K., Kunihiro, N.: Security of MD5 challenge and response: Extension of APOP password recovery attack. In: Malkin, T.G. (ed.) CT-RSA 2008. LNCS, vol. 4964, pp. 1–18. Springer, Heidelberg (2008)
Mazzeo, A., Romano, L., Saggese, G.P.: FPGA-based Implementation of a serial RSA processor. In: Proceedings of the Design, Automation and Test in Europe Conference and Exhibition (DATE) (2003)
Järvinen, K., Tommiska, M., Skyttä, J.: Hardware Implementation Analysis of the MD5 Hash Algorithm. In: Proceedings of the 38th Hawaii International Conference on System Sciences (2005)
Zambreno, J., Nguyen, D., Choudhary, A.: Exploring area/Delay tradeoffs in an AES FPGA implementation. In: Becker, J., Platzner, M., Vernalde, S. (eds.) FPL 2004. LNCS, vol. 3203, pp. 575–585. Springer, Heidelberg (2004)
Chaves, R., Kuzmanov, G., Sousa, L., Vassiliadis, S.: Improving SHA-2 Hardware Implementations. LNCS. Springer, Heidelberg (2006)
Zeng, G., Ito, H.: Efficient Test Data Decompression for System-on-a-Chip Using an Embedded FPGA Core. In: Proceedings of the 18th IEEE International Symposium on Defect and Fault Tolerance in VLSI Systems (DFT) (2003)
Kim, J.: Design and implementation of integrated security engine for secure networking. In: IEEE Advanced Communication Technology (2004)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2009 Springer-Verlag Berlin Heidelberg
About this chapter
Cite this chapter
Pereira, F.D., Ordonez, E.D.M. (2009). A Hardware Architecture for Integrated-Security Services. In: Gavrilova, M.L., Tan, C.J.K., Moreno, E.D. (eds) Transactions on Computational Science IV. Lecture Notes in Computer Science, vol 5430. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-01004-0_12
Download citation
DOI: https://doi.org/10.1007/978-3-642-01004-0_12
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-01003-3
Online ISBN: 978-3-642-01004-0
eBook Packages: Computer ScienceComputer Science (R0)