Abstract
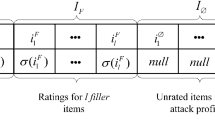
Recommender systems enable a user to decide which information is interesting and valuable in our world of information overload. Collaborative Filtering (CF), one of the most successful technologies in recommender systems suffers from improper use of personal information and the incredibility of recommendations. To deal with these issues, we have been focusing on the trust relationships between individuals, i.e. web of trust, especially for protecting the recommender system against profile injection attack. Based on trust propagation scheme, we proposed TCFMA architecture which is added agent-based scheme obtaining attack resistance property as well as improving the efficiency of distributed computing. In web of trust, users’ personal agents find a unique migration path made up of latent neighborhoods and reduce search scope to a reasonable level for mobile agents by using the Advogato algorithm. The experimental evaluation on Epinions.com datasets shows that the proposed method brings significant advantages in terms of dealing with profile injection attack without any loss of prediction quality.
Access provided by Autonomous University of Puebla. Download to read the full chapter text
Chapter PDF
Similar content being viewed by others
Keywords
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
Miller, B., Konstan, J., Terveen, L., Riedl, J.: PocketLens: Towards a Personal Recommender System. ACM Transactions on Information Systems 22, 437–476 (2004)
Guha, R., Kumar, R., Raghavan, P., Tomkins, A.: Propagation of Trust and Distrust. In: Proc. of the 13th Int. Conf. on World Wide Web, ACM Press, New York (2004)
Ziegler, C.-N., Lausen, G.: Propagation Models for Trust and Distrust in Social Networks. In: Information Systems Frontiers, vol. 7, pp. 337–358. Springer, Dordrecht (2005)
Levien, R., Aiken, A.: Attack Resistant, Scalable Name Service. Draft submission to the 4th Int. Conf. on Financial Cryptography (2000)
Sarwar, B., Karypis, G., Konstan, J., Reidl, J.: Item-based Collaborative Filtering Recom-mendation Algorithms. In: Proc. of the 10th Int. Conf. on World Wide Web (2001)
Sinha, R., Swearingen, K.: Comparing Recommendations Made by Online Systems and Friends. In: Proc. of the DELOS-NSF Workshop on Personalization and Recommender Systems in Digital Libraries (2001)
Ziegler, C.-N., Lausen, G.: Analyzing Correlation between Trust and User Similarity in Online Communities. In: Jensen, C., Poslad, S., Dimitrakos, T. (eds.) iTrust 2004. LNCS, vol. 2995, pp. 251–265. Springer, Heidelberg (2004)
Massa, P., Avesani, P.: Trust-aware Collaborative Filtering for Recommender Systems. In: Proc. of Int. Conf. on Cooperative Information Systems (2004)
Herlocker, J.L., Konstan, J.A., Borchers, A., Riedl, J.: An Algorithmic Framework for Performing Collaborative Filtering. In: Proc. of the 22nd ACM SIGIR Conf. on Research and Development in Information Retrieval (1999)
Lange, D.B., Oshima, M.: Programming and Deploying Java Mobile Agents with Aglets. Addison-Wesley, Reading (1998)
Jung, J.J.: Visualizing recommendation flow on social networks. Journal of Universal Computer Science 11(11), 1780–1791 (2005)
Kim, H.J., Jung, J.J., Jo, G.S.: Conceptual Framework for Recommendation System based on Distributed User Ratings. In: Li, M., Sun, X.-H., Deng, Q.-n., Ni, J. (eds.) GCC 2003. LNCS, vol. 3032, pp. 115–122. Springer, Heidelberg (2004)
O’Mahony, M., Hurley, N., Kushmerick, N., Silvestre, G.: Collaborative Recommendation: A Robustness Analysis. ACM Transactions on Internet Technology 4(4), 344–377 (2004)
Mobesher, B., Bruke, R., Bhaumik, R., Williams, C.: Towards Trustworthy Recommender Systems: An Analysis of Attack Models and Algorithm Robustness. To appear in ACM Transactions on Internet Technology7(2) (2007)
Leivien, R.: Attack Resistant Trust Metrics. Ph.D thesis, UC Berkeley, Berkeley, CA, USA (2003)
Page, L., Brin, S., Motwani, R., Winograd, T.: The Pagerank Citation Ranking: Bringing Order to the Web. Technical Report, Stanford Digital Library Technologies Project (1998)
Twigg, A., Dimmock, N.: Attack-resistance of computational trust models. In: Proc. of the 12th IEEE Int. Workshop on Enabling Technologies, pp. 275–280 (2003)
Author information
Authors and Affiliations
Editor information
Rights and permissions
Copyright information
© 2007 Springer Berlin Heidelberg
About this paper
Cite this paper
Ji, AT., Yeon, C., Kim, HN., Jo, GS. (2007). Distributed Collaborative Filtering for Robust Recommendations Against Shilling Attacks. In: Kobti, Z., Wu, D. (eds) Advances in Artificial Intelligence. Canadian AI 2007. Lecture Notes in Computer Science(), vol 4509. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-540-72665-4_2
Download citation
DOI: https://doi.org/10.1007/978-3-540-72665-4_2
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-72664-7
Online ISBN: 978-3-540-72665-4
eBook Packages: Computer ScienceComputer Science (R0)