Abstract
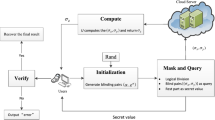
Provable Data Possession (PDP) allows a file owner to outsource her files to a storage server such that a verifier can check the integrity of the outsourced file. Public verifiable PDP schemes allow any one other than the file owner to be a verifier. At the client side (file owner or verifier), a substantial number of modular exponentiations is often required. In this paper we make PDP more practical via proposing a protocol to securely outsource the (most generic) variable-exponent variable-base exponentiations in one untrusted program model. Our protocol demonstrates advantages in efficiency or privacy over existing protocols coping with only special cases in two or single untrusted program model. We then apply our generic protocol to Shacham-Waters PDP and a variant of Yuan-Yu PDP. The analyses show that our protocol makes PDP much more efficient at the client side.
Chapter PDF
Similar content being viewed by others
Keywords
References
Deng, H., Wu, Q., Qin, B., Chow, S.S.M., Domingo-Ferrer, J., Shi, W.: Tracing and Revoking Leaked Credentials: Accountability in Leaking Sensitive Outsourced Data. In: 9th ACM Symposium on Information, Computer and Communications Security (ASIACCS), pp. 425–443. ACM, New York (2014)
Deng, H., Wu, Q., Qin, B., Domingo-Ferrer, J., Zhang, L., Liu, J., Shi, W.: Ciphertext-Policy Hierarchical Attribute-Based Encryption with Short Ciphertexts. Information Sciences 275, 370–384 (2014)
Deng, H., Wu, Q., Qin, B., Mao, J., Liu, X., Zhang, L., Shi, W.: Who is touching my cloud. In: Kutylowski, M., Vaidya, J. (eds.) ESORICS 2014. LNCS, vol. 8712, pp. 362–379. Springer, Heidelberg (2014)
Chow, S.S.M., Yiu, S.M., Hui, L.C.K., Chow, K.P.: Efficient Forward and Provably Secure ID-Based Signcryption Scheme with Public Verifiability and Public Ciphertext Authenticity. In: Lim, J.-I., Lee, D.-H. (eds.) ICISC 2003. LNCS, vol. 2971, pp. 352–369. Springer, Heidelberg (2004)
Qin, B., Wang, H., Wu, Q., Liu, J., Domingo-Ferrer, J.: Simultaneous Authentication and Secrecy in Identity-Based Data Upload to Cloud. Cluster Computing 16, 845–859 (2013)
Ateniese, G., Burns, R., Curtmola, R., Herring, J., Kissner, L., Peterson, Z., Song, D.: Provable Data Possession at Untrusted Stores. In: 14th ACM Conference on Computer and Communications Security (CCS), pp. 598–609. ACM, New York (2007)
Juels, A., Kaliski Jr., B.S.: PoRs: Proofs of Retrievability for Large Files. In: 14th ACM Conference on Computer and Communications Security (CCS), pp. 584–597. ACM, New York (2007)
Shacham, H., Waters, B.: Compact Proofs of Retrievability. In: Pieprzyk, J. (ed.) ASIACRYPT 2008. LNCS, vol. 5350, pp. 90–107. Springer, Heidelberg (2008)
Wang, B., Chow, S.S.M., Li, M., Li, H.: Storing Shared Data on the Cloud via Security-Mediator. In: 33rd IEEE International Conference on Distributed Computing Systems (ICDCS), pp. 124–133 (2013)
Wang, C., Chow, S.S.M., Wang, Q., Ren, K., Lou, W.: Privacy-Preserving Public Auditing for Secure Cloud Storage. IEEE Transactions on Computers 62(2), 362–375 (2013)
Yuan, J., Yu, S.: Proofs of Retrievability with Public Verifiability and Constant Communication Cost in Cloud. In: International Workshop on Security in Cloud Computing, pp. 19–26. ACM, New York (2013)
Hohenberger, S., Lysyanskaya, A.: How to Securely Outsource Cryptographic Computations. In: Kilian, J. (ed.) TCC 2005. LNCS, vol. 3378, pp. 264–282. Springer, Heidelberg (2005)
Chen, X., Li, J., Ma, J., Tang, Q., Lou, W.: New Algorithms for Secure Outsourcing of Modular Exponentiations. In: Foresti, S., Yung, M., Martinelli, F. (eds.) ESORICS 2012. LNCS, vol. 7459, pp. 541–556. Springer, Heidelberg (2012)
Dijk, M., Clarke, D., Gassend, B., Suh, G., Devadas, S.: Speeding up Exponentiation using an Untrusted Computational Resource. Designs, Codes and Cryptography 39(2), 253–273 (2006)
Wang, H., Wu, Q., Qin, B., Domingo-Ferrer, J.: Identity-Based Remote Data Possession Checking in Public Clouds. Information Security, IET 8(2), 114–121 (2014)
Kate, A., Zaverucha, G.M., Goldberg, I.: Constant-Size Commitments to Polynomials and Their Applications. In: Abe, M. (ed.) ASIACRYPT 2010. LNCS, vol. 6477, pp. 177–194. Springer, Heidelberg (2010)
Benabbas, S., Gennaro, R., Vahlis, Y.: Verifiable Delegation of Computation over Large Datasets. In: Rogaway, P. (ed.) CRYPTO 2011. LNCS, vol. 6841, pp. 111–131. Springer, Heidelberg (2011)
Li, J., Tan, X., Chen, X., Wong, D.S.: An Efficient Proof of Retrievability with Public Auditing in Cloud Computing. In: 5th International Conference on Intelligent Networking and Collaborative Systems (INCoS), pp. 93–98 (2013)
Ma, X., Li, J., Zhang, F.: Outsourcing Computation of Modular Exponentiations in Cloud Computing. Cluster Computing 16(4), 787–796 (2013)
Tsang, P.P., Chow, S.S.M., Smith, S.W.: Batch Pairing Delegation. In: Miyaji, A., Kikuchi, H., Rannenberg, K. (eds.) IWSEC 2007. LNCS, vol. 4752, pp. 74–90. Springer, Heidelberg (2007)
Canard, S., Devigne, J., Sanders, O.: Delegating a Pairing Can Be Both Secure and Efficient. In: Boureanu, I., Owesarski, P., Vaudenay, S. (eds.) ACNS 2014. LNCS, vol. 8479, pp. 549–565. Springer, Heidelberg (2014)
Xu, G., Amariucai, G., Guan, Y.: Delegation of Computation with Verification Outsourcing: Curious Verifiers. In: ACM Symposium on Principles of Distributed Computing (PODC), pp. 393–402. ACM, New York (2013)
Gennaro, R., Gentry, C., Parno, B.: Non-interactive Verifiable Computing: Outsourcing Computation to Untrusted Workers. In: Rabin, T. (ed.) CRYPTO 2010. LNCS, vol. 6223, pp. 465–482. Springer, Heidelberg (2010)
Carter, H., Mood, B., Traynor, P., Butler, K.: Secure Outsourced Garbled Circuit Evaluation for Mobile Devices. In: 22nd USENIX Conference on Security, pp. 289–304. USENIX Association, Berkeley (2013)
Zhang, L.F., Safavi-Naini, R.: Private Outsourcing of Polynomial Evaluation and Matrix Multiplication Using Multilinear Maps. In: Abdalla, M., Nita-Rotaru, C., Dahab, R. (eds.) CANS 2013. LNCS, vol. 8257, pp. 329–348. Springer, Heidelberg (2013)
Wang, B., Li, M., Chow, S.S.M., Li, H.: Computing Encrypted Cloud Data Efficiently Under Multiple Keys. In: 4th IEEE Security and Privacy in Cloud Computing, co-located with IEEE Conference on Communications and Network Security (CNS), pp. 504–513 (2013)
Wang, B., Li, M., Chow, S.S.M., Li, H.: A Tale of Two Servers: Efficient Privacy-Preserving Computation over Cloud Data under Multiple Keys. In: 2nd IEEE Conference on Communications and Network Security, CNS (2014)
Chow, S.S.M., Lee, J.H., Subramanian, L.: Two-Party Computation Model for Privacy-Preserving Queries over Distributed Databases. In: Network and Distributed System Security Symposium, NDSS (2009)
Nguyen, P., Shparlinski, I.E., Stern, J.: Distribution of Modular Sums and the Security of the Server Aided Exponentiation. In: Cryptography and Computational Number Theory. Progress in Computer Science and Applied Logic, vol. 20, pp. 331–342. Birkhäuser, Basel (2001)
Boyko, V., Peinado, M., Venkatesan, R.: Speeding up Discrete Log and Factoring Based Schemes via Precomputations. In: Nyberg, K. (ed.) EUROCRYPT 1998. LNCS, vol. 1403, pp. 221–235. Springer, Heidelberg (1998)
Boneh, D., Lynn, B., Shacham, H.: Short Signatures from the Weil Pairing. Journal of Cryptology 17(4), 297–319 (2004)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2014 Springer International Publishing Switzerland
About this paper
Cite this paper
Wang, Y. et al. (2014). Securely Outsourcing Exponentiations with Single Untrusted Program for Cloud Storage. In: Kutyłowski, M., Vaidya, J. (eds) Computer Security - ESORICS 2014. ESORICS 2014. Lecture Notes in Computer Science, vol 8712. Springer, Cham. https://doi.org/10.1007/978-3-319-11203-9_19
Download citation
DOI: https://doi.org/10.1007/978-3-319-11203-9_19
Publisher Name: Springer, Cham
Print ISBN: 978-3-319-11202-2
Online ISBN: 978-3-319-11203-9
eBook Packages: Computer ScienceComputer Science (R0)