Abstract
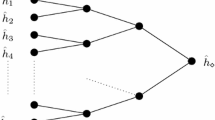
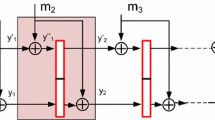
We expand a previous result of Dean [Dea99] to provide a second preimage attack on all n-bit iterated hash functions with Damgård-Merkle strengthening and n-bit intermediate states, allowing a second preimage to be found for a 2k-message-block message with about k × 2n/2 + 1 + 2n − k + 1 work. Using RIPEMD-160 as an example, our attack can find a second preimage for a 260 byte message in about 2106 work, rather than the previously expected 2160 work. We also provide slightly cheaper ways to find multicollisions than the method of Joux [Jou04]. Both of these results are based on expandable messages–patterns for producing messages of varying length, which all collide on the intermediate hash result immediately after processing the message. We provide an algorithm for finding expandable messages for any n-bit hash function built using the Damgård-Merkle construction, which requires only a small multiple of the work done to find a single collision in the hash function.
Chapter PDF
Similar content being viewed by others
Keywords
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
Anderson, R.J., Biham, E.: Tiger—A Fast New Hash Function. In: Gollmann, D. (ed.) FSE 1996. LNCS, vol. 1039, Springer, Heidelberg (1996)
Adams, C.M., Kramer, G., Mister, S., Zuccherato, R.J.: On the security of key derivation functions. In: Zhang, K., Zheng, Y. (eds.) ISC 2004. LNCS, vol. 3225, pp. 134–145. Springer, Heidelberg (2004) (to appear)
Baldwin: Preliminary Analysis of the BSAFE 3.x Pseudorandom Number Generators, RSA Laboratories Bulletin No. 8, RSA Laboratories (1998)
Barreto, P.S.L.M., Rijmen, V.: The Whirlpool Hashing Function. In: First open NESSIE Workshop, Leuven, Belgium, November 13–14 (2000)
Black, J.A., Rogaway, P., Shrimpton, T.: Black-box analysis of the block-cipher-based hash-function constructions from PGV. In: Yung, M. (ed.) CRYPTO 2002. LNCS, vol. 2442, p. 320. Springer, Heidelberg (2002)
Biham, E., Shamir, A.: Differential Cryptanalysis of the Data Encryption Standard. Springer, Heidelberg (1993)
Dobbertin, H., Bosselaers, A., Preneel, B.: RIPEMD-160, A Strengthened Version of RIPEMD. In: Gollmann, D. (ed.) FSE 1996. LNCS, vol. 1039, Springer, Heidelberg (1996)
Dean, R.D.: Formal Aspects of Mobile Code Security, Ph.D Dissertation, Princeton University (January 1999)
Damgård, I.B.: A Design Principle for Hash Functions. In: Brassard, G. (ed.) CRYPTO 1989. LNCS, vol. 435, pp. 416–427. Springer, Heidelberg (1989)
Desai, A., Hevia, A., Yin, Y.L.: A Practice-Oriented Treatment of Pseudorandom Number Generators. In: Knudsen, L.R. (ed.) EUROCRYPT 2002. LNCS, vol. 2332, p. 368. Springer, Heidelberg (2002)
Joux, A.: Multicollisions in Iterated Hash Functions. Applications to Cascaded Constructions. In: Franklin, M. (ed.) CRYPTO 2004. LNCS, vol. 3152, pp. 306–316. Springer, Heidelberg (2004)
Kelsey, J., Schneier, B., Ferguson, N.: Yarrow-160: Notes on the Design and Analysis of the Yarrow Cryptographic Pseudorandom Number Generator. In: Heys, H.M., Adams, C.M. (eds.) SAC 1999. LNCS, vol. 1758, p. 13. Springer, Heidelberg (1999)
Lucks, S.: Design Principles for Iterated Hash Functions, IACR preprint archive (2004), http://eprint.iacr.org/2004/253.pdf
Merkle, R.C.: One Way Hash Functions and DES. In: Brassard, G. (ed.) CRYPTO 1989. LNCS, vol. 435, pp. 428–446. Springer, Heidelberg (1989)
Merkle, R.C.: A Fast Software One-Way Hash Function. Journal of Cryptology 3(1), 43–58 (1990)
Miyaguchi, S., Ohta, K., Iwata, M.: Confirmation that Some Hash Functions are Not Collision Free. In: Menezes, A., Vanstone, S.A. (eds.) CRYPTO 1990. LNCS, vol. 537, Springer, Heidelberg (1990)
Menezes, W., van Oorschot, P.C., Vanstone: Handbook of Applied Cryptography. CRC Press, Boca Raton (1996)
NIST Special Publication 800-56, Recommendations on Key Establishment Schemes, Draft 2.0 (January 2003), available from http://csrc.nist.gov/CryptoToolkit/kms/keyschemes-jan02.pdf
Preneel, B., Govaerts, R., Vandewalle, J.: Hash Functions Based on Block Ciphers: A Synthetic Approach. In: Stinson, D.R. (ed.) CRYPTO 1993. LNCS, vol. 773, pp. 368–378. Springer, Heidelberg (1993)
Preneel, B.: Personal Communication (March 2005)
Rivest: The MD5 Message-Digest Algorithm, RFC1321 (April 1992)
National Institute of Standards and Technology, Secure Hash Standard, FIPS180-2 (August 2002)
van Oorschot, P.C., Wiener, M.: Parallel Collision Search with Cryptanalytic Applications. J. of Cryptology 12, 1–28 (1999)
van Oorschot, P.C., Wiener, M.: Improving Implementable Meet-in-the-Middle Attacks by Orders of Magnitude. In: Koblitz, N. (ed.) CRYPTO 1996. LNCS, vol. 1109, pp. 229–236. Springer, Heidelberg (1996)
ANSI X9.63—Public Key Cryptography for the Financial Services Industry: Key Agreement and Transport Using Elliptic Curve Cryptography, American Bankers Association, Working Draft (1999)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2005 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Kelsey, J., Schneier, B. (2005). Second Preimages on n-Bit Hash Functions for Much Less than 2n Work. In: Cramer, R. (eds) Advances in Cryptology – EUROCRYPT 2005. EUROCRYPT 2005. Lecture Notes in Computer Science, vol 3494. Springer, Berlin, Heidelberg. https://doi.org/10.1007/11426639_28
Download citation
DOI: https://doi.org/10.1007/11426639_28
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-25910-7
Online ISBN: 978-3-540-32055-5
eBook Packages: Computer ScienceComputer Science (R0)