Abstract
Verifiable secret sharing (VSS) is a vital primitive in secure distributed computing. It allows an untrusted dealer to verifiably share a secret among n parties in the presence of an adversary controlling at most t of them. VSS in the synchronous communication model has received tremendous attention in the cryptographic research community. Nevertheless, recent interest in deploying secure distributed computing over the Internet requires going beyond the synchronous model and thoroughly investigating VSS in the asynchronous communication model.
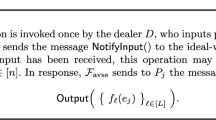
In this work, we consider the communication complexity of asynchronous VSS in the computational setting for the optimal resilience of n = 3t + 1. The best known asynchronous VSS protocol by Cachin et al. has O(n 2) message complexity and O(κn 3) communication complexity, where κ is a security parameter. We close the linear complexity gap between these two measures for asynchronous VSS by presenting two protocols with O(n 2) message complexity and O(κn 2) communication complexity. Our first protocol satisfies the standard VSS definition, and can be used in stand-alone VSS scenarios as well as in applications such as Byzantine agreement. Our second and more intricate protocol satisfies a stronger VSS definition, and is useful in all VSS applications including multiparty computation and threshold cryptography.
An extended version of this paper is available [3].
Access provided by Autonomous University of Puebla. Download to read the full chapter text
Chapter PDF
Similar content being viewed by others
Keywords
References
Abraham, I., Dolev, D., Halpern, J.Y.: An Almost-surely Terminating Polynomial Protocol for Asynchronous Byzantine Agreement with Optimal Resilience. In: Proceedings of ACM PODC 2008, pp. 405–414 (2008)
Au, M.H., Susilo, W., Mu, Y.: Practical Anonymous Divisible E-Cash from Bounded Accumulators. In: Tsudik, G. (ed.) FC 2008. LNCS, vol. 5143, pp. 287–301. Springer, Heidelberg (2008)
Backes, M., Datta, A., Kate, A.: Asynchronous Computational VSS with Reduced Communication Complexity. Cryptology ePrint Archive, Report 2012/619 (2012), http://eprint.iacr.org/2012/619
Backes, M., Kate, A., Patra, A.: Computational Verifiable Secret Sharing Revisited. In: Lee, D.H., Wang, X. (eds.) ASIACRYPT 2011. LNCS, vol. 7073, pp. 590–609. Springer, Heidelberg (2011)
Ben-Or, M., Canetti, R., Goldreich, O.: Asynchronous Secure Computation. In: Proceedings of ACM STOC 1993, pp. 52–61 (1993)
Blakley, G.R.: Safeguarding Cryptographic Keys. In: Proceedings of the National Computer Conference, pp. 313–317 (1979)
Boneh, D., Boyen, X.: Short Signatures Without Random Oracles. In: Cachin, C., Camenisch, J.L. (eds.) EUROCRYPT 2004. LNCS, vol. 3027, pp. 56–73. Springer, Heidelberg (2004)
Bracha, G.: An Asynchronous [(n-1)/3]-Resilient Consensus Protocol. In: Proceedings of PODC 1984, pp. 154–162 (1984)
Cachin, C., Kursawe, K., Lysyanskaya, A., Strobl, R.: Asynchronous Verifiable Secret Sharing and Proactive Cryptosystems. In: Proceedings of ACM CCS 2002, pp. 88–97 (2002)
Canetti, R.: Studies in Secure Multiparty Computation and Applications. Ph.D. thesis, The Weizmann Institute of Science (1996)
Canetti, R., Rabin, T.: Fast Asynchronous Byzantine Agreement with Optimal Resilience. In: Proceedings of ACM STOC 1993, pp. 42–51 (1993)
Chor, B., Goldwasser, S., Micali, S., Awerbuch, B.: Verifiable Secret Sharing and Achieving Simultaneity in the Presence of Faults. In: Proceedings of IEEE FOCS 1985, pp. 383–395 (1985)
Cramer, R., Damgård, I., Dziembowski, S.: On the Complexity of Verifiable Secret Sharing and Multiparty Computation. In: Proceedings of STOC 2000, pp. 325–334 (2000)
Dolev, D., Reischuk, R.: Bounds on Information Exchange for Byzantine Agreement. Journal of ACM 32(1), 191–204 (1985)
Feldman, P.: A Practical Scheme for Non-interactive Verifiable Secret Sharing. In: Proceedings of IEEE FOCS 1987, pp. 427–437 (1987)
Herzberg, A., Jarecki, S., Krawczyk, H., Yung, M.: Proactive Secret Sharing or: How to Cope with Perpetual Leakage. In: Coppersmith, D. (ed.) CRYPTO 1995. LNCS, vol. 963, pp. 339–352. Springer, Heidelberg (1995)
Kate, A., Goldberg, I.: Distributed Key Generation for the Internet. In: Proceedings of 29th IEEE International Conference on Distributed Computing Systems (ICDCS), pp. 119–128 (2009)
Kate, A., Zaverucha, G.M., Goldberg, I.: Constant-Size Commitments to Polynomials and Their Applications. In: Abe, M. (ed.) ASIACRYPT 2010. LNCS, vol. 6477, pp. 177–194. Springer, Heidelberg (2010)
Katz, J., Koo, C.-Y., Kumaresan, R.: Improving the Round Complexity of VSS in Point-to-Point Networks. In: Aceto, L., Damgård, I., Goldberg, L.A., Halldórsson, M.M., Ingólfsdóttir, A., Walukiewicz, I. (eds.) ICALP 2008, Part II. LNCS, vol. 5126, pp. 499–510. Springer, Heidelberg (2008)
Patra, A., Choudhary, A., Rangan, C.P.: Efficient Asynchronous Byzantine Agreement with Optimal Resilience. In: Proceedings of ACM PODC 2009, pp. 92–101 (2009)
Pedersen, T.P.: Non-interactive and Information-Theoretic Secure Verifiable Secret Sharing. In: Feigenbaum, J. (ed.) CRYPTO 1991. LNCS, vol. 576, pp. 129–140. Springer, Heidelberg (1992)
Pedersen, T.P.: A Threshold Cryptosystem without a Trusted Party. In: Davies, D.W. (ed.) EUROCRYPT 1991. LNCS, vol. 547, pp. 522–526. Springer, Heidelberg (1991)
Schultz, D.A., Liskov, B., Liskov, M.: MPSS: Mobile Proactive Secret Sharing. ACM Trans. Inf. Syst. Secur. 13(4), 34 (2010)
Shamir, A.: How to Share a Secret. Commun. ACM 22(11), 612–613 (1979)
Zhou, L., Schneider, F.B., van Renesse, R.: APSS: Proactive Secret Sharing in Asynchronous Systems. ACM Trans. Inf. Syst. Secur (TISSec) 8(3), 259–286 (2005)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2013 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Backes, M., Datta, A., Kate, A. (2013). Asynchronous Computational VSS with Reduced Communication Complexity. In: Dawson, E. (eds) Topics in Cryptology – CT-RSA 2013. CT-RSA 2013. Lecture Notes in Computer Science, vol 7779. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-36095-4_17
Download citation
DOI: https://doi.org/10.1007/978-3-642-36095-4_17
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-36094-7
Online ISBN: 978-3-642-36095-4
eBook Packages: Computer ScienceComputer Science (R0)