Abstract
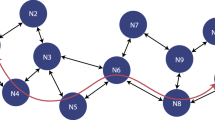
Wireless Mesh Network (WMN) has become popular, as it allows fast, easy and inexpensive network deployment. It is observed that the current peer link establishment mechanism presented in IEEE 802.11s draft standard is vulnerable to various kinds of relay and wormhole attacks. In this paper, we propose a certificate-based peer link establishment protocol that employs location information to prevent such attacks. The security analysis shows that the proposed mechanism is resistant against different kinds of wormhole, relay and Sybil attacks.
Access provided by Autonomous University of Puebla. Download to read the full chapter text
Chapter PDF
Similar content being viewed by others
Keywords
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
Akyildiz, I.F., Wang, X., Wang, W.: Wireless mesh networks: A survey. Computer Networks and ISDN Systems (2005)
IEEE P802.11s/D5.0 Part 11: Wireless LAN Medium Access Control (MAC) and Physical Layer (PHY)specifications, Amendment 10: Mesh Networking
Zapata, M., Asokan, N.: Securing ad-hoc routing protocols. In: Proceedings of ACM Workshop on Wireless Security, pp. 1–10 (September 2002)
Li, C., Wang, Z., Yang, C.: Secure Routing for Wireless Mesh Networks. International Journal of Network Security 13(2), 109–120 (2011)
Zhu, S., Xu, S., Setia, S., Jajodia, S.: LHAP: A Lightweight Hop-by-Hop Authentication Protocol for Ad-Hoc Networks. In: Proceedings of ICDCS International Workshop on Mobile and Wireless Network, Providence, Rodhe Island, pp. 749–755 (May 2003)
Sangiri, K., Dahil, B.: A secure routing protocol for ad hoc networks. In: Proceedings of 10th IEEE International Conference on Network Protocols, pp. 78–89 (2002)
Matam, R., Tripathy, S.: FRI Attack: Fraudulent Routing Information Attack on Wireless Mesh Networks. In: Proc. of IEEE Xplore, ACWR (2011)
Hu, Y., Perrig, A., Johnson, D.: Packet leashes: A defence against wormhole attacks in wireless networks. In: Proc. of the Twenty-second IEEE International Conference on Computer Communications (April 2003)
Poovendran, R., Lazos, L.: A graph theoretic framework for preventing the wormhole attack in wireless ad hoc networks. ACM Journal of Wireless Networks 13(1), 2759 (2005)
Wang, X., Wong, J.: An end-to-end detection of wormhole attack in wireless ad-hoc networks. In: Proc. of the Thirty-First Annual International Computer Software and Applications Conference (July 2007)
Wang, Y., Zhang, Z.: A Distributed Approach for Hidden Wormhole Detection with Neighborhood Information. In: IEEE Fifth International Conference on Networking, Architecture and Storage, NAS (2010)
Hayajneh, T., Krishnamurthy, P., Tipper, D.: Deworm: A simple protocol to detect wormhole attacks in wireless ad hoc networks. In: Proceedings of the IEEE Symposium on Network and System Security (2009)
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2012 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Bhumireddy, S., Tripathy, S., Matam, R. (2012). Secure Peer-Link Establishment in Wireless Mesh Networks. In: Meghanathan, N., Nagamalai, D., Chaki, N. (eds) Advances in Computing and Information Technology. Advances in Intelligent Systems and Computing, vol 176. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-31513-8_19
Download citation
DOI: https://doi.org/10.1007/978-3-642-31513-8_19
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-31512-1
Online ISBN: 978-3-642-31513-8
eBook Packages: EngineeringEngineering (R0)