Abstract
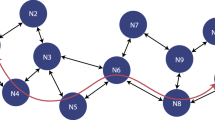
Mobile peer-to-peer networking (MP2P) is a relatively new paradigm compared to other wireless networks. In the last years, it has gained popularity because of its practice in applications such as file sharing over Internet in a decentralized manner. Security of mobile P2P networks represents an open research topic and a main challenge regarding to their vulnerability and convenience to different security attacks, such as black hole, Sybil...etc. In this paper, we analyze the black hole attack in mobile wireless P2P networks using AODV as routing protocol. In a black hole attack, a malicious node assumes the identity of a legitimate node, by creating forged answers with a higher sequence number, and thus forces the victim node to choose it as relay. We propose a solution based on a modification of the well-known AODV routing protocol and taking into account the behavior of each node participating in the network. Performances of our proposal are evaluated by simulation.
Access provided by Autonomous University of Puebla. Download to read the full chapter text
Chapter PDF
Similar content being viewed by others
References
Dunaytsev, R.: Client/Server and Peer-to-Peer models. Space Internetworking Center Democritus University of Thrace (2012)
Jarraya, H.: Un système de sauvegarde P2P sécurisé s’appuyant sur une architecture AAA, Maryline Laurent-Maknavicius (2008)
Shen, X., et al.: Handbook of peer to peer networking. Springer (2010)
Klemm, A., et al.: A Special-Purpose Peer-to-Peer File Sharing System for Mobile Ad Hoc Networks. Department of Computer Science, University of Dortmund
Deng, et al.: Routing “Security in Wireless Ad-hoc Networks”. IEEE Communications Magazine (2002)
Raj, P.N., Swadas, P.B.: DPRAODV: A Dynamic Learning System Against Black hole Attack in AODV based MANET. International Journal of Computer Science (2009)
Shurman, M.A., Yoo, S.M., Park, S.: Black hole attack in wireless ad hoc networks. In: Proceedings of the ACM 42nd Southeast Conference (ACMSE 2004) (April 2004)
Mandhata, S.C., Patro, S.N.: A counter measure to Black hole attack on AODV- based Mobile Ad-Hoc Networks. International Journal of Computer & Communication Technology (IJCCT) 2(VI) (2011)
Véronique Legrand et Stéphane Ubéda Vers un modèle de confiance pour les objets communicants: une approche sociale, Laboratoire CITI, INRIA ARES (2004)
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2013 Springer International Publishing Switzerland
About this chapter
Cite this chapter
Hafi, H., Bilami, A. (2013). Cooperative Strategy to Secure Mobile P2P Network. In: Amine, A., Otmane, A., Bellatreche, L. (eds) Modeling Approaches and Algorithms for Advanced Computer Applications. Studies in Computational Intelligence, vol 488. Springer, Cham. https://doi.org/10.1007/978-3-319-00560-7_19
Download citation
DOI: https://doi.org/10.1007/978-3-319-00560-7_19
Publisher Name: Springer, Cham
Print ISBN: 978-3-319-00559-1
Online ISBN: 978-3-319-00560-7
eBook Packages: EngineeringEngineering (R0)