Abstract
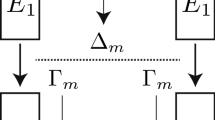
This paper studies the security of the block cipher ARIA against impossible differential cryptanalysis. We find a new impossible differential property of ARIA, and propose an attack against ARIA-256 reduced to 7 rounds based on this property, while previous attacks can only attack ARIA up to 6 rounds. Our new attack needs 2125 chosen plaintexts and 2238 7-round encryptions. This is the best result for impossible differential cryptanalysis of ARIA known so far.
Access provided by Autonomous University of Puebla. Download to read the full chapter text
Chapter PDF
Similar content being viewed by others
References
Biham, E., Biryukov, A., Shamir, A.: Cryptanalysis of Skipjack Reduced to 31 Rounds Using Impossible Differentials. In: Stern, J. (ed.) EUROCRYPT 1999. LNCS, vol. 1592, pp. 12–23. Springer, Heidelberg (1999)
Biham, E., Dunkelman, O., Keller, N.: Related-Key Impossible Differential Attacks on 8-round AES-192. In: Pointcheval, D. (ed.) CT-RSA 2006. LNCS, vol. 3860, pp. 21–33. Springer, Heidelberg (2006)
Biham, E., Keller, N.: Cryptanalysis of Reduced Variants of Rijndael. In: The Third AES Candidate Conference (2000)
Biham, E., Shamir, A.: Differential Cryptanalysis of DES-like Cryptosystems. Journal of Cryptology 4(1), 3–72 (1991)
Biryukov, A., De Canniere, C., Lano, J., Ors, S.B., Preneel, B.: Security and Performance Analysis of Aria. Version 1.2 (Janaury 7, 2004)
Cheon, J.H., Kim, M., Kim, K., et al.: Improved Impossible Differential Cryptanalysis of Rijndael and Crypton. In: Kim, K. (ed.) ICISC 2001. LNCS, vol. 2288, pp. 39–49. Springer, Heidelberg (2002)
Daemen, J., Rijmen, V.: The Design of Rijndael. In: Information Security and Cryptography. Springer, Heidelberg (2002)
Jakimoski, G., Desmedt, Y.: Related-Key Differential Cryptanalysis of 192-bit key AES Variants. In: Matsui, M., Zuccherato, R. (eds.) SAC 2003. LNCS, vol. 3006, pp. 208–221. Springer, Heidelberg (2004)
Jakobsen, T., Knudsen, L.R.: The Interpolation Attack against Block Ciphers. In: Biham, E. (ed.) FSE 1997. LNCS, vol. 1267, pp. 28–40. Springer, Heidelberg (1997)
Knudsen, L.R.: Truncated and Higher Order Differentials. In: Preneel, B. (ed.) FSE 1994. LNCS, vol. 1008, pp. 196–211. Springer, Heidelberg (1995)
Knudsen, L.R., Wagner, D.: Integral Cryptanalysis (extended abstract). In: Daemen, J., Rijmen, V. (eds.) FSE 2002. LNCS, vol. 2365, pp. 629–632. Springer, Heidelberg (2002)
Kwon, D., Kim, J., Park, S., et al.: New Block Cipher: ARIA. In: Lim, J.-I., Lee, D.-H. (eds.) ICISC 2003. LNCS, vol. 2971, pp. 432–445. Springer, Heidelberg (2004)
Li, S., Song, C.: Improved Impossible Differential Cryptanalysis of ARIA. In: ISA 2008, pp. 129–132. IEEE Computer Society, Los Alamitos (April 2008)
Matsui, M.: Linear Cryptanalysis Method for DES Cipher. In: Helleseth, T. (ed.) EUROCRYPT 1993. LNCS, vol. 765, pp. 386–397. Springer, Heidelberg (1994)
National Security Research Institute: Specification of ARIA, Version 1.0 (January 2005), http://www.nsri.re.kr/ARIA/doc/ARIAspecification-e.pdf
Phan, R.C.: Impossible Differential Cryptanalysis of 7-round AES. Inf. Process. Lett. 91(1), 33–38 (2004)
Wu, W., Zhang, W., Feng, D.: Impossible Differential Cryptanalysis of Reduced-Round ARIA and Camellia. Journal of Computer Science and Technology 22(3), 449–456 (2007)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2010 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Du, C., Chen, J. (2010). Impossible Differential Cryptanalysis of ARIA Reduced to 7 Rounds. In: Heng, SH., Wright, R.N., Goi, BM. (eds) Cryptology and Network Security. CANS 2010. Lecture Notes in Computer Science, vol 6467. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-17619-7_2
Download citation
DOI: https://doi.org/10.1007/978-3-642-17619-7_2
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-17618-0
Online ISBN: 978-3-642-17619-7
eBook Packages: Computer ScienceComputer Science (R0)