Abstract
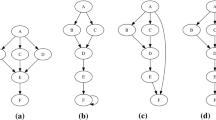
A software birthmark is a unique characteristic of a program that can be used as a software theft detection. In this paper we suggest and empirically evaluate a static birthmark of binary executables based on API call structure. The program properties employed in this birthmark are functions and standard API calls when the functions are executed. The API calls from a function includes the API calls explicitly found from the function and its descendants within limited depth in the call graph. To statically identify functions, call graphs and API calls, we utilizes IDAPro disassembler and its plug-ins. We define the similarity between two functions as the proportion of the number of all API calls to the number of the common API calls. The similarity between two programs is obtained by the maximum weight bipartite matching between two programs using the function similarity matrix. To show the credibility of the proposed techniques, we compare the same applications with different versions and the various types of applications which include text editors, picture viewers, multimedia players, P2P applications and ftp clients. To show the resilience, we compare binary executables compiled from various compilers. The empirical result shows that the similarities obtained using our birthmark sufficiently indicates the functional and structural similarities among programs.
This work was supported by the Korea Science and Engineering Foundation (KOSEF) through the Advanced Information Technology Research Center(AITrc).
Access provided by Autonomous University of Puebla. Download to read the full chapter text
Chapter PDF
Similar content being viewed by others
References
Schleimer, S., Wilkerson, D., Aiken, A.: Winnowing: local algorithms for document fingerprinting. In: Proceedings of the 2003 ACM SIGMOD international conference on Management of data, pp. 76–85. ACM Press, New York (2003)
Wise, M.: YAP3: improved detection of similarities in computer program and other texts. In: Proceedings of the twenty-seventh SIGCSE technical symposium on Computer science education, pp. 130–134 (1996)
Prechelt, L., Malpohl, G., Philippsen, M.: Finding plagiarisms among a set of programs with JPlag. Journal of Universal Computer Science 8(11), 1016–1038 (2002)
SABRE BinDiff, http://www.sabre-security.com/products/bindiff.html
Using BinDiff for Code theft detection, http://www.sabre-security.com/products/CodeTheft.pdf
Tamada, H., Okamoto, K., Nakamura, M., Monden, A., Matsumoto, K.: Dynamic Software Birthmarks to Detect the Theft of Windows Applications. International Symposium on Future Software Technology 20(22) (2004)
Okamoto, K., Tamada, H., Nakamura, M., Monden, A., Matsumoto, K.: Dynamic Software Birthmarks Based on API Calls. IEICE Transactions on Information and Systems 89(8), 1751–1763 (2006)
The IDA Pro Disassembler and Debugger, http://www.datarescue.com/idabase
Collberg, C., Thomborson, C.: Watermarking, tamper-proofing, and obfuscation-tools for software protection. Software Engineering, IEEE Transactions on 28(8), 735–746 (2002)
Collberg, C., Thomborson, C.: Software watermarking: models and dynamic embeddings. In: Proceedings of the 26th ACM SIGPLAN-SIGACT symposium on Principles of programming languages, pp. 311–324. ACM Press, New York (1999)
Collberg, C., Myles, G., Huntwork, A.: Sandmark-A tool for software protection research. Security & Privacy Magazine, IEEE 1(4), 40–49 (2003)
Tamada, H., Nakamura, M., Monden, A., Matsumoto, K.: Design and evaluation of birthmarks for detecting theft of java programs. In: Proc. IASTED International Conference on Software Engineering (IASTED SE 2004), pp. 569–575 (2004)
Tamada, H., Nakamura, M., Monden, A., Matsumoto, K.: Java Birthmarks–Detecting the Software Theft–. IEICE Transactions on Information and Systems 88(9), 2148–2158 (2005)
Myles, G., Collberg, C.: K-gram based software birthmarks. In: Proceedings of the 2005 ACM symposium on Applied computing, pp. 314–318. ACM Press, New York (2005)
Myles, G., Collberg, C.: Detecting software theft via whole program path birthmarks. Information Security Conference, 404–415 (2004)
Myles, G.M.: Software Theft Detection Through Program Identification. PhD thesis, Department of Computer Science, The University of Arizona (2006)
Larus, J.: Whole program paths. In: Proceedings of the ACM SIGPLAN 1999 conference on Programming language design and implementation, pp. 259–269. ACM Press, New York (1999)
Bunke, H., Shearer, K.: A graph distance metric based on the maximal common subgraph. Pattern Recognition Letters 19(3-4), 255–259 (1998)
Schuler, D., Dallmeier, V., Lindig, C.: A Dynamic Birthmark for Java. In: Proceedings of the 22nd IEEE/ACM International Conference on Automated Software Engineering
Kuhn, H.: The Hungarian method for the assignment problem. Naval Research Logistics 52(1), 7–21 (2005)
Kibria, R.: frhed - free hex editor, http://www.codeproject.com/tools/frhed.asp
Cloakware security suite, http://www.cloakware.com/products_services/security_suite
Wang, C.: A Security Architecture for Survivability Mechanisms. PhD thesis, University of Virginia
Balakrishnan, G., Reps, T.: Recency-abstraction for heap-allocated storage. Static Analysis Symp. (2006)
Author information
Authors and Affiliations
Editor information
Rights and permissions
Copyright information
© 2007 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Choi, S., Park, H., Lim, Hi., Han, T. (2007). A Static Birthmark of Binary Executables Based on API Call Structure. In: Cervesato, I. (eds) Advances in Computer Science – ASIAN 2007. Computer and Network Security. ASIAN 2007. Lecture Notes in Computer Science, vol 4846. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-540-76929-3_2
Download citation
DOI: https://doi.org/10.1007/978-3-540-76929-3_2
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-76927-9
Online ISBN: 978-3-540-76929-3
eBook Packages: Computer ScienceComputer Science (R0)