Abstract
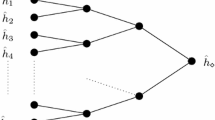
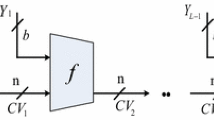
The parallel FFT-Hashing function was designed by C. P. Schnorr and S. Vaudenay in 1993. The function is a simple and light weight hash algorithm with 128-bit digest. Its basic component is a multi-permutation which helps in proving its resistance to collision attacks.
In this work we show a preimage attack on the parallel FFT-Hashing function using 2t + 64 + 2128 − t time complexity and 2t memory, which is less than the generic complexity 2128. Specifically, when t = 32 , we can find a preimage using 297 time and 232 memory. Our method can be described as “disseminative-meet-in-the-middle-attack”. we actually use the properties of multi-permutation (helpful against collision attack) to our advantage in the attack. Overall, this type of attack (beating the generic one) demonstrates that the structure of the parallel FFT-Hashing function has some weaknesses when preimage attack is considered (and relevant). To the best of our knowledge,this is the first attack on the parallel FFT-Hashing function.
This research was supported by the MIC(Ministry of Information and Communication), Korea, under the ITRC(Information Technology Research Center) support program supervised by the IITA(Institute of Information Technology Advancement) (IITA-2006-(C1090-0603-0025)). Part of this work was done while the first author visited Columbia University.
Access provided by Autonomous University of Puebla. Download to read the full chapter text
Chapter PDF
Similar content being viewed by others
References
Baritaud, T., Gilbert, H., Girault, M.: FFT Hashing is not Collision-free. In: Rueppel, R.A. (ed.) EUROCRYPT 1992. LNCS, vol. 658, pp. 35–44. Springer, Heidelberg (1993)
Schnorr, C.P.: FFT-Hashing: An Efficient Cryptographic Hash Function. In: Presented at the rump session of the Crypto’91
Schnorr, C.P.: FFT-Hash II, efficient hashing. In: Rueppel, R.A. (ed.) EUROCRYPT 1992. LNCS, vol. 658, pp. 45–54. Springer, Heidelberg (1993)
Schnorr, C.P., Vaudenay, S.: Parallel FFT-Hashing. In: Anderson, R. (ed.) Fast Software Encryption. LNCS, vol. 809, pp. 149–156. Springer, Heidelberg (1994)
Schnorr, C.P., Vaudenay, S.: Black Box Cryptanalysis of Hash Networks based on Multipermutations. In: De Santis, A. (ed.) EUROCRYPT 1994. LNCS, vol. 950, pp. 47–57. Springer, Heidelberg (1995)
Vaudenay, S.: FFT-Hash II is not yet Collision-free. In: Brickell, E.F. (ed.) CRYPTO 1992. LNCS, vol. 740, pp. 587–593. Springer, Heidelberg (1993)
Author information
Authors and Affiliations
Editor information
Rights and permissions
Copyright information
© 2007 Springer Berlin Heidelberg
About this paper
Cite this paper
Chang, D., Yung, M., Sung, J., Hong, S., Lee, S. (2007). Preimage Attack on the Parallel FFT-Hashing Function. In: Pieprzyk, J., Ghodosi, H., Dawson, E. (eds) Information Security and Privacy. ACISP 2007. Lecture Notes in Computer Science, vol 4586. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-540-73458-1_5
Download citation
DOI: https://doi.org/10.1007/978-3-540-73458-1_5
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-73457-4
Online ISBN: 978-3-540-73458-1
eBook Packages: Computer ScienceComputer Science (R0)