Abstract
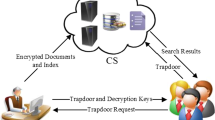
Searchable symmetric encryption is a good building block toward ensuring privacy preserving keyword searches in a cloud computing environment. This area has recently attracted a great deal of attention and a large quantity of research has been conducted. A security protocol generally faces a trade-off between security/privacy requirements and efficiency. Existing works aim to achieve the highest levels of security requirements, so they also come with high overhead. In this paper, we reconsider the security/privacy requirements for searchable symmetric encryption and relax the requirements for practical use. Then, we propose schemes suitable for the new requirements. We also show experimental results of our schemes and comparison to existing schemes. The results show that the index sizes of our proposals are only a few times of that of a Lucene (without encryption). In document update, our proposal requests additional index which depends only on the size of new document.
Access provided by Autonomous University of Puebla. Download to read the full chapter text
Chapter PDF
Similar content being viewed by others
Keywords
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
Abdalla, M., et al.: Searchable Encryption Revisited: Consistency Properties, Relation to Anonymous IBE, and Extensions. In: Shoup, V. (ed.) CRYPTO 2005. LNCS, vol. 3621, pp. 205–222. Springer, Heidelberg (2005)
Apache Lucene - Welcome to Apache Lucene, http://lucene.apache.org/
Announcing the ADVANCED ENCRYPTION STANDARD (AES). Federal Information Processing Standards Publication 197 (November 2001)
Bellare, M., Boldyreva, A., O’Neill, A.: Deterministic and Efficiently Searchable Encryption. In: Menezes, A. (ed.) CRYPTO 2007. LNCS, vol. 4622, pp. 535–552. Springer, Heidelberg (2007)
Boneh, D., Di Crescenzo, G., Ostrovsky, R., Persiano, G.: Public key encryption with keyword search. In: Cachin, C., Camenisch, J.L. (eds.) EUROCRYPT 2004. LNCS, vol. 3027, pp. 506–522. Springer, Heidelberg (2004)
Chang, Y.-C., Mitzenmacher, M.: Privacy Preserving Keyword Searches on Remote Encrypted Data. In: Ioannidis, J., Keromytis, A.D., Yung, M. (eds.) ACNS 2005. LNCS, vol. 3531, pp. 442–455. Springer, Heidelberg (2005)
Curtmola, R., Garay, J., Kamara, S., Ostrovsky, R.: Searchable Symmetric Encryption: Improved Definitions and Efficient constructions. In: ACM Conference on Computer and Communications Security (CCS 2006), pp. 79–88. ACM, New York (2006)
Goh, E.-J.: Secure indexes. Technical Report 2003/216, IACR ePrint Cryptography Archive (2003)
Goldreich, O., Ostrovsky, R.: Software protection and simulation on oblivious RAMs. J. of the ACM 43(3), 431–473 (1996)
Hirano, T., Mori, T., Hattori, M., Ito, T., Matsuda, N., Kawai, Y., Sakai, Y., Ohta, K.: Security Notions for Searchable Symmetric Encryption with Extra Multiple Documents. In: The 29th Symposium on Cryptography and Information Security, SCIS 2012, 2B3-1 (2012) (in Japanese)
Iwanami, J., Ogata, W.: Secure and Efficient Searchable Symmetric Encryption with Document Addition. In: The 30th Symposium on Cryptography and Information Security, SCIS 2013, 3A3-1 (2013) (in Japanese)
Kamara, S., Lauter, K.: Cryptographic Cloud Storage. In: Sion, R., Curtmola, R., Dietrich, S., Kiayias, A., Miret, J.M., Sako, K., Sebé, F. (eds.) FC 2010 Workshops. LNCS, vol. 6054, pp. 136–149. Springer, Heidelberg (2010)
Kamara, S., Papamanthou, C., Roeder, T.: CS2: A searchable cryptographic cloud storage system. MSR Tech Report no. MSR-TR-2011-58. Microsoft, Redmond (2011)
Kamara, S., Roeder, T.: Dynamic Searchable Symmetric Encryption. In: Proc. of the 2012 ACM Conference on Computer and Communications Security, pp. 965–976. ACM, New York (2012)
van Liesdonk, P., Sedghi, S., Doumen, J., Hartel, P., Jonker, W.: Computationally efficient searchable symmetric encryption. In: Jonker, W., Petković, M. (eds.) SDM 2010. LNCS, vol. 6358, pp. 87–100. Springer, Heidelberg (2010)
Moby Word Lists, The Institute for Language, Speech and Hearing, http://icon.shef.ac.uk/Moby/
Song, D., Wagner, D., Perrig, A.: Practical techniques for searching on encrypted data. In: Proc. of 2000 IEEE Symposium on Security and Privacy, pp. 44–55 (2000)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2013 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Ogata, W., Koiwa, K., Kanaoka, A., Matsuo, S. (2013). Toward Practical Searchable Symmetric Encryption. In: Sakiyama, K., Terada, M. (eds) Advances in Information and Computer Security. IWSEC 2013. Lecture Notes in Computer Science, vol 8231. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-41383-4_10
Download citation
DOI: https://doi.org/10.1007/978-3-642-41383-4_10
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-41382-7
Online ISBN: 978-3-642-41383-4
eBook Packages: Computer ScienceComputer Science (R0)