Abstract
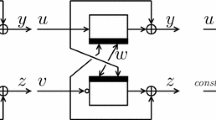
Methods to construct a hash function using an existing block cipher recently attract some interests as an approach to implement a hash function on constrained devices. It is often required to construct a hash function whose output length is larger than that of the underlying block cipher to provide sufficient level of collision resistance with the use of an existing block cipher. This article presents a new mode of double-block compression function, which is based on the mode proposed by Jonsson and Robshaw at PKC 2005. The mode can be instantiated with a block cipher whose key-length is larger than its block-length such as AES-192/256, PRESENT-128, etc. This article also provides provable security analyses to an iterated hash function using the proposed mode and the MDP domain extension. The security properties discussed are collision resistance, preimage resistance, pseudorandom-function property of the keyed-via-IV mode, and the indifferentiability from a random oracle.
Access provided by Autonomous University of Puebla. Download to read the full chapter text
Chapter PDF
Similar content being viewed by others
Keywords
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
Armknecht, F., Fleischmann, E., Krause, M., Lee, J., Stam, M., Steinberger, J.: The preimage security of double-block-length compression functions. In: Lee, D.H., Wang, X. (eds.) ASIACRYPT 2011. LNCS, vol. 7073, pp. 233–251. Springer, Heidelberg (2011)
Bellare, M., Kohno, T.: A theoretical treatment of related-key attacks: RKA-PRPs, RKA-PRFs, and applications. In: Biham, E. (ed.) EUROCRYPT 2003. LNCS, vol. 2656, pp. 491–506. Springer, Heidelberg (2003)
Black, J., Rogaway, P., Shrimpton, T., Stam, M.: An analysis of the blockcipher-based hash functions from PGV. Journal of Cryptology 23(4), 519–545 (2010)
Bogdanov, A., Leander, G., Paar, C., Poschmann, A., Robshaw, M.J.B., Seurin, Y.: Hash functions and RFID tags: Mind the gap. In: Oswald, E., Rohatgi, P. (eds.) CHES 2008. LNCS, vol. 5154, pp. 283–299. Springer, Heidelberg (2008)
Bos, J.W., Özen, O., Stam, M.: Efficient hashing using the AES instruction set. In: Preneel, B., Takagi, T. (eds.) CHES 2011. LNCS, vol. 6917, pp. 507–522. Springer, Heidelberg (2011)
Brachtl, B.O., Coppersmith, D., Hyden, M.M., Matyas Jr., S.M., Meyer, C.H.W., Oseas, J., Pilpel, S., Schilling, M.: Data authentication using modification detection codes based on a public one-way encryption function. U. S. Patent # 4,908,861 (March 1990)
Coron, J.-S., Dodis, Y., Malinaud, C., Puniya, P.: Merkle-Damgård revisited: How to construct a hash function. In: Shoup, V. (ed.) CRYPTO 2005. LNCS, vol. 3621, pp. 430–448. Springer, Heidelberg (2005)
FIPS PUB 180-4. Secure hash standard (SHS) (March 2012)
Fleischmann, E., Gorski, M., Lucks, S.: Security of cyclic double block length hash functions. In: Parker (ed.) [23], pp. 153–175
Gueron, S.: Intel advanced encryption standard (AES) instructions set (2010), http://software.intel.com/en-us/articles/intel-advanced-encryption-standard-aes-instructions-set/
Hirose, S.: Some plausible constructions of double-block-length hash functions. In: Robshaw, M.J.B. (ed.) FSE 2006. LNCS, vol. 4047, pp. 210–225. Springer, Heidelberg (2006)
Hirose, S., Park, J.H., Yun, A.: A simple variant of the Merkle-Damgård scheme with a permutation. In: Kurosawa, K. (ed.) ASIACRYPT 2007. LNCS, vol. 4833, pp. 113–129. Springer, Heidelberg (2007)
Jonsson, J., Robshaw, M.J.B.: Securing RSA-KEM via the AES. In: Vaudenay, S. (ed.) PKC 2005. LNCS, vol. 3386, pp. 29–46. Springer, Heidelberg (2005)
Kuwakado, H., Hirose, S.: Hashing mode using a lightweight blockcipher. In: Stam, M. (ed.) IMACC 2013. LNCS, vol. 8308, pp. 213–231. Springer, Heidelberg (2013)
Lai, X., Massey, J.L.: Hash functions based on block ciphers. In: Rueppel, R.A. (ed.) EUROCRYPT 1992. LNCS, vol. 658, pp. 55–70. Springer, Heidelberg (1993)
Lee, J., Kwon, D.: The security of Abreast-DM in the ideal cipher model. IEICE Transactions 94-A(1), 104–109 (2011)
Lee, J., Stam, M.: MJH: A faster alternative to MDC-2. In: Kiayias, A. (ed.) CT-RSA 2011. LNCS, vol. 6558, pp. 213–236. Springer, Heidelberg (2011)
Lee, J., Stam, M.: MJH: A faster alternative to MDC-2. Cryptology ePrint Archive, Report 2014/108 (2014), http://eprint.iacr.org/
Lee, J., Stam, M., Steinberger, J.: The collision security of Tandem-DM in the ideal cipher model. In: Rogaway, P. (ed.) CRYPTO 2011. LNCS, vol. 6841, pp. 561–577. Springer, Heidelberg (2011)
Maurer, U.M., Renner, R., Holenstein, C.: Indifferentiability, impossibility results on reductions, and applications to the random oracle methodology. In: Naor, M. (ed.) TCC 2004. LNCS, vol. 2951, pp. 21–39. Springer, Heidelberg (2004)
Naito, Y.: Blockcipher-based double-length hash functions for pseudorandom oracles. In: Miri, A., Vaudenay, S. (eds.) SAC 2011. LNCS, vol. 7118, pp. 338–355. Springer, Heidelberg (2012)
Özen, O., Stam, M.: Another glance at double-length hashing. In: Parker (ed.) [23], pp. 176–201
Parker, M.G. (ed.): Cryptography and Coding 2009. LNCS, vol. 5921. Springer, Heidelberg (2009)
Rijmen, V., Barreto, P.S.L.M.: The Whirlpool hash function (2000), http://www.larc.usp.br/~pbarreto/WhirlpoolPage.html
Rivest, R.: The MD4 message-digest algorithm. Request for Comments 1320 (RFC 1320), The Internet Engineering Task Force (1992)
Rivest, R.: The MD5 message-digest algorithm. Request for Comments 1321 (RFC 1321), The Internet Engineering Task Force (1992)
Rohde, S., Eisenbarth, T., Dahmen, E., Buchmann, J., Paar, C.: Fast hash-based signatures on constrained devices. In: Grimaud, G., Standaert, F.-X. (eds.) CARDIS 2008. LNCS, vol. 5189, pp. 104–117. Springer, Heidelberg (2008)
Steinberger, J.P.: The collision intractability of MDC-2 in the ideal-cipher model. In: Naor, M. (ed.) EUROCRYPT 2007. LNCS, vol. 4515, pp. 34–51. Springer, Heidelberg (2007)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2014 Springer International Publishing Switzerland
About this paper
Cite this paper
Hirose, S., Kuwakado, H. (2014). A Block-Cipher-Based Hash Function Using an MMO-Type Double-Block Compression Function. In: Chow, S.S.M., Liu, J.K., Hui, L.C.K., Yiu, S.M. (eds) Provable Security. ProvSec 2014. Lecture Notes in Computer Science, vol 8782. Springer, Cham. https://doi.org/10.1007/978-3-319-12475-9_6
Download citation
DOI: https://doi.org/10.1007/978-3-319-12475-9_6
Publisher Name: Springer, Cham
Print ISBN: 978-3-319-12474-2
Online ISBN: 978-3-319-12475-9
eBook Packages: Computer ScienceComputer Science (R0)