Abstract
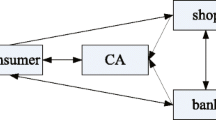
Recently, some blind quantum signature (BQS) protocols have been proposed. But the previous schemes have security and efficiency problems. Based on the entangled Greenberger-Horne-Zeilinger (GHZ) states, a new weak BQS protocol is proposed. Compared with some existing schemes, our protocol has 100% efficiency. Besides, the protocol is simple and easy to implement. The security of the protocol is guaranteed by the correlation of the GHZ particles held by each participant. In our protocol, the signatory is kept blind from the content of the message. According to the security analysis, the signatory cannot disavowal his/her signature while the signature cannot be forged by others.
Article PDF
Similar content being viewed by others
Avoid common mistakes on your manuscript.
References
Diffie W, Hellman M. New directions in cryptography. IEEE Trans Inf Theory, 1976, 22: 644–654
Merkle R. Secrecy, Authentication, and Public Key Systems. Dissertation for Doctoral Degree. Stanford: Stanford University, 1979
Shor P W. Polynomial-time algorithms for prime factorization and discrete logarithms on a quantum computer. SIAM J Sci Statist Comput, 1997, 26: 1484–1509
Bennett C H, Brassard G. Quantum cryptography: Public key distribution and coin tossing. In: Proceedings of IEEE International Conference on Computer Systems and Signal Processing, Bangalore, 1984. 175–179
Ekert A K. Quantum cryptography based on Bell’s theorem. Phys Rev Lett, 1991, 67: 661–663
Bennett C H. Quantum cryptography using any two nonorthogonal states. Phys Rev Lett, 1992, 68: 3121–3124
Bostrom K, Felbinger T. Deterministic secure direct communication using entanglement. Phys Rev Lett, 2002, 89: 187902
Deng F G, Long G L, Liu X S. Two-step quantum direct communication protocol using the Einstein-Podolsky-Rosen pair block. Phys Rev A, 2003, 68: 042317
Chen X B, Wang T Y, Du J Z, et al. Controlled quantum secure direct communication with quantum encryption. Int J Quantum Inf, 2008, 6: 543–551
Chen X B, Wen Q Y, Guo F Z, et al. Controlled quantum secure direct communication with W state. Int J Quantum Inf, 2008, 6: 899–906
Hillery M, Buzek V, Berthiaume A. Quantum secret sharing. Phys Rev A, 1999, 59: 1829–1834
Gottesman D. Theory of quantum secret sharing. Phys Rev A, 2000, 61: 042311
Chen X B, Niu X X, Zhou X J, et al. Multi-party quantum secret sharing with the single-particle quantum state to encode the information. Quantum Inf Process, 2013, 12: 365–380
Gottesman D, Chuang I. Quantum digital signatures. arXiv: quantph/0105032, 2001
Zeng G H, Keitel C H. Arbitrated quantum-signature scheme. Phys Rev A, 2002, 65: 042312
Curty M, Lutkenhaus N. Comment on “Arbitrated quantum-signature scheme”. Phys Rev A, 2008, 77: 046301
Zeng G H. Reply to “Comment on ‘Arbitrated quantum-signature scheme’ ”. Phys Rev A, 2008, 78: 016301
Li Q, Chan W H, Long D Y. Arbitrated quantum signature scheme using Bell states. Phys Rev A, 2009, 79: 054307
Zou X F, Qiu D W. Security analysis and improvements of arbitrated quantum signature schemes. Phys Rev A, 2010, 82: 042325
Gao F, Qin S J, Guo F Z, et al. Cryptanalysis of the arbitrated quantum signature protocols. Phys Rev A, 2011, 84: 022344
Lee H, Hong C, Kim H, et al. Arbitrated quantum signature scheme with message recovery. Phys Lett A, 2004, 321: 295–300
Yang Y G, Zhou Z, Teng YW, et al. Arbitrated quantum signature with an untrusted arbitrator. Eur Phys J D, 2011, 61: 773–778
Chaum D. Blind signatures for untraceable payments. In: Proceedings of CRYPTO’82. New York: Plenum Publishing, 1982. 199–203
Benaloh J C, Yung M. Distributing the power of a government to enhance the privacy of voters. In: Proceedings of the 5th Annual ACM Symposium on Principles of Distributed Computing, Calgary, 1986. 52–62
Wen X J, Niu X M, Ji L P, et al. A weak blind signature scheme based on quantum cryptography. Opt Commun, 2009, 282: 666–669
Naseri M. A weak blind signature based on quantum cryptography. Int J Phys Sci, 2011, 6: 5051–5053
Su Q, Huang Z, Wen Q Y, et al. Quantum blind signature based on two-state vector formalism. Opt Commun, 2010, 283: 4408–4410
Yang C W, Hwang T, Luo Y P. Enhancement on “quantum blind signature based on two-state vector formalism”. Quantum Inf Process, 2013, 12: 109–117
Xu R, Huang L S, Yang W, et al. Quantum group blind signature scheme without entanglement. Opt Commun, 2011, 284: 3654–3658
Yin X R, Ma W P, Liu W Y. A blind quantum signature scheme with X-type entangled states. Int J Theor Phys, 2012, 51: 455–461
Karlsson A, Koashi M, Imoto N. Quantum entanglement for secret sharing and secret splitting. Phys Rev A, 1999, 59: 162–168
Qin S J, Gao F, Wen Q Y, et al. Cryptanalysis of the Hillery-Buzcaronek-Berthiaume quantum secret-sharing protocol. Phys Rev A, 2007, 76: 062324
Deng F G, Li X H, Zhou H Y, et al. Improving the security of multiparty quantum secret sharing against Trojan horse attack. Phys Rev A, 2005, 72: 044302
Gisin N, Fasel S, Kraus B, et al. Trojan-horse attacks on quantum-keydistribution systems. Phys Rev A, 2006, 73: 022320
Huttner B, Imoto N, Gisin N, et al. Quantum cryptography with coherent states. Phys Rev A, 1995, 51: 1863–1869
Brassard G, Lutkenhaus N, Mor T, et al. Limitations on practical quantum cryptography. Phys Rev Lett, 2000, 85: 1330–1333
Tittel W, Zbinden H, Gisin N. Experimental demonstration of quantum secret sharing. Phys Rev A, 2001, 63: 042301
Chen Y A, Zhang A N, Zhao Z, et al. Experimental quantum secret sharing and third-man quantum cryptography. Phys Rev Lett, 2005, 95: 200502
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Wang, M., Chen, X. & Yang, Y. A blind quantum signature protocol using the GHZ states. Sci. China Phys. Mech. Astron. 56, 1636–1641 (2013). https://doi.org/10.1007/s11433-013-5170-x
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11433-013-5170-x