Abstract
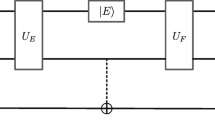
For the first time, a threshold quantum secure direct communication (TQSDC) scheme is presented. Similar to the classical Shamir’s secret sharing scheme, the sender makes n shares, S 1, ..., S n of secret key K and each receiver keeps a share secretly. If the sender wants to send a secret message M to the receivers, he encodes the information of K and M on a single photon sequence and sends it to one of the receivers. According to the secret shares, the t receivers sequentially perform the corresponding unitary operations on the single photon sequence and obtain the secret message M. The shared shares may be reusable if it can be judged that there is no eavesdropper in line. We discuss that our protocol is feasible with current technology.
Article PDF
Similar content being viewed by others
Avoid common mistakes on your manuscript.
References
Bennett C H, Brassard G. Quantum cryptography: Public-key distribution and coin tossing, Proc IEEE Int Conf on Computers, Systems and Signal Processing, Bangalore, India. New York: IEEE, 1984. 175–179
Ekert A. Quantum cryptography based on Bell’s theorem. Phys Rev Lett, 1991, 67: 661–664
Bennett C H. Quantum cryptography using any two nonorthogonal states. Phys Rev Lett, 1992, 68: 3121–3124
Deng F G, Long G L. Bidirectional quantum key distribution protocol with practical faint laser pulses. Phys Rev A, 2004, 70: 012311-1-4
Deng F G, Long G L. Controlled order rearrangement encryption for quantum key distribution. Phys Rev A, 2003, 68: 042315-1-5
Hillery M, Bužek V, Berthiaume A. Quantum secret sharing. Phys Rev A, 1999, 59: 1829–1834
Karlsson A, Koashi M, Imoto N. Quantum entanglement for secret sharing and secret splitting. Phys Rev A, 1999, 59: 162–168
Deng F G, Zhou H Y, Long G L. Bidirectional quantum secret sharing and secret splitting with polarized single photons. Phys Lett A, 2005, 337(4–6): 329–334
Guo G P, Guo G C. Quantum secret sharing without entanglement. Phys Lett A, 2003, 310(4): 247–251
Xiao L, Long G L, Deng F G, et al. Efficient multiparty quantum secret sharing schemes. Phys Rev A, 2004, 69: 052307-1-5
Beige A, Englert B G, Kurtsiefer C et al. Secure communication with single-photon two-qubit states. J Phys A: Math Gen, 2002, 35(28): L407–L413
Boström K, Felbinger T. Deterministic secure direct communication using entanglement. Phys Rev Lett, 2002, 89: 187902-1-4
Wójcik A. Eavesdropping on the “Ping-Pong” quantum communication protocol. Phys Rev Lett, 2003, 90: 157901-1-4
Zhang Z J, Man Z X, Li Y. Improving Wójcik’s eavesdropping attack on the ping-pong protocol. Phys Lett A, 2004, 333(1–2): 46–50
Cai Q Y. The “Ping-Pong” protocol can be attacked without eavesdropping. Phys Rev Lett, 2003, 91: 109801-1-1
Cai Q Y, Li B W. Deterministic secure communication without using entanglement. Chin Phys Lett, 2004, 21: 601–603
Deng F G, Long G L. Secure direct communication with a quantum one-time pad. Phys Rev A, 2004, 69: 052319-1-4
Cai Q Y, Li B W. Improving the capacity of the Boström-Felbinger protocol. Phys Rev A, 2004, 69: 054301-1-3
Wang C, Deng FG, Li Y S, et al. Quantum secure direct communication with high-dimension quantum superdense coding. Phys Rev A, 2005, 71: 044305-1-4
Zhu A D, Xia Y, Fan Q B, et al. Secure direct communication based on secret transmitting order of particles. Phys Rev A, 2006, 73: 022338-1-4
Wang J, Zhang Q, Tang C J. Quantum secure direct communication based on order rearrangement of single photons. Phys Lett A, 2006, 358(4): 256–258
Lucamarini M, Mancini S. Secure deterministic communication without entanglement. Phys Rev Lett, 2005, 94: 140501-1-4
Deng F G, Long G L, Liu X S. Two-step quantum direct communication protocol using the Einstein-Podolsky-Rosen pair block. Phys Rev A, 2003, 68: 042317-1-4
Cao H J, Song H S. Quantum secure direct communication with W State. Chin Phys Lett, 2006, 23: 290–292
Li X H, Zhou P, Liang Y-J, et al. Quantum secure direct communication network with two-step protocol. Chin Phys Lett, 2006, 23: 1080–1083
Bouwmeester D, Pan J W, Daniell M, et al. Observation of three-photon Greenberger-Horne-Zeilinger entanglement. Phys Rev Lett, 1999, 82: 1345–1349
Pan J W, Daniell M, Gasparoni S, et al. Experimental demonstration of four-photon entanglement and high-fidelity teleportation. Phys Rev Lett, 2001, 86: 4435–4438
Shamir A. How to share a secret. Commun ACM, 1979, 22(11): 612–613
Cai QY. Eavesdropping on the two-way quantum communication protocols with invisible photons. Phys Lett A, 2006, 351(1–2): 23–25
Deng F G, Li X H, Zhou H Y, et al. Improving the security of multiparty quantum secret sharing against Trojan horse attack. Phys Rev A, 2005, 72: 044302-044305
Qin S J, Gao F, Wen Q Y, et al. Improving the security of multiparty quantum secret sharing against an attack with a fake signal. Phys Lett A, 2006, 357(2): 101–103
Author information
Authors and Affiliations
Corresponding author
Additional information
Supported by the National Basic Research Program of China (973 Program) (Grant No. 2007CB311100), the National High Technology Research and Development Program of China (Grant Nos. 2006AA01Z419 and 20060101Z4015), the Major Research Plan of the National Natural Science Foundation of China (Grant No. 90604023), the 2008 Scientific Research Common Program of Beijing Municipal Commission of Education; the Scientific Research Foundation for the Youth of Beijing University of Technology (Grant No. 97007016200701), the National Research Foundation for the Doctoral Program of Higher Education of China (Grant No. 20040013007), the National Laboratory for Modern Communications Science Foundation of China (Grants No. 9140C1101010601), the Doctor Scientific Research Activation Foundation of Beijing University of Technology (No. 52007016200702), and the Open Foundation of State Key Laboratory of Information Security (Graduate School of the Chinese Academy of Sciences)
Rights and permissions
About this article
Cite this article
Yang, Y., QiaoYan, W. Threshold quantum secure direct communication without entanglement. Sci. China Ser. G-Phys. Mech. Astron. 51, 176–183 (2008). https://doi.org/10.1007/s11433-008-0028-3
Received:
Accepted:
Issue Date:
DOI: https://doi.org/10.1007/s11433-008-0028-3