Abstract
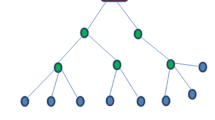
In-network data aggregation in Wireless Sensor Networks (WSNs) provides efficient bandwidth utilization and energy-efficient computing. Supporting efficient in-network data aggregation while preserving the privacy of the data of individual sensor nodes has emerged as an important requirement in numerous WSN applications. For privacy-preserving data aggregation in WSNs, He et al. (INFOCOM 2007) have proposed a Cluster-based Private Data Aggregation (CPDA) that uses a clustering protocol and a well-known key distribution scheme for computing an additive aggregation function in a privacy-preserving manner. In spite of the wide popularity of CPDA, it has been observed that the protocol is not secure and it is also possible to enhance its efficiency. In this paper, we first identify a security vulnerability in the existing CPDA scheme, wherein we show how a malicious participant node can launch an attack on the privacy protocol so as to get access to the private data of its neighboring sensor nodes. Next it is shown how the existing CPDA scheme can be made more efficient by suitable modification of the protocol. Further, suitable modifications in the existing protocol have been proposed so as to plug the vulnerability of the protocol.
Access provided by Autonomous University of Puebla. Download to read the full chapter text
Chapter PDF
Similar content being viewed by others
Keywords
References
Acharya, M., Girao, J., Westhoff, D.: Secure Comparison of Encrypted Data in Wireless Sensor Networks. In Proc. of the 3rd International Symposium on Modeling and Optimization in Mobile, Ad Hoc, and Wireless Networks (WIOPT), Washington, DC, USA, pp. 47–53 (2005)
Akyildiz, I.F., Su, W., Sankarasubramaniam, Y., Cayirci, E.: Wireless Sensor Networks: A Survey. Computer Networks 38(4), 393–422 (2002)
Armknecht, F., Westhoff, D., Girao, J., Hessler, A.: A Lifetime-Optimized End-to-End Encryption Scheme for Sensor Networks Allowing In-Network Processing. Computer Communications 31(4), 734–749 (2008)
Castelluccia, C., Chan, A.C-F., Mykletun, E., Tsudik, G.: Efficient and Provably Secure Aggregation of Encrypted Data in Wireless Sensor Networks. ACM Transactions on Sensor Networks 5(3) (2009)
Chaum, D.: The Dining Cryptographers Problem: Unconditional Sender and Recipient Untraceability. Journal of Cryptology 1(1), 65–75 (1988)
Eschenauer, L., Gligor, V.D.: A Key-Management Scheme for Distributed Sensor Networks. In: Proc. of the 9th ACM Conference on Computing and Communications Security, pp. 41–47 (2002)
Fontaine, C., Galand, F.: A Survey of Homomorphic Encryption for Nonspecialists. EURASIP Journal on Information Security 2007, Article ID 13801 (2007)
Girao, J., Westhoff, D., Schneider, M.: CDA: Concealed Data Aggregation for Reverse Multicast Traffic in Wireless Sensor Networks. In: Proc. of the 40th IEEE Conference on Communications (IEEE ICC), vol. 5, pp. 3044–3049 (2005)
He, W., Liu, X., Nguyen, H., Nahrstedt, K., Abdelzaher, T.: PDA: Privacy-Preserving Data Aggregation in Wireless Sensor Networks. In Proc. of the 26th IEEE International Conference on Computer Communications (IEEE INFOCOM), pp. 2045–2053 (2007)
Madden, S., Franklin, M.J., Hellerstein, J.M., Hong, W.: TAG: A Tiny Aggregation Service for Ad-Hoc Sensor Networks. In Proc. of the 5th Symposium on Operating Systems Design and Implementation (OSDI), vol. 36 (2002)
Peter, S., Westhoff, D., Castelluccia, C.: A Survey on the Encryption of Convergecast Traffic with In-Network Processing. IEEE Transactions on Dependable and Secure Computing 7(1), 20–34 (2010)
Sen, J.: A Survey on Wireless Sensor Network Security. International Journal of Communication Networks and Information Security (IJCNIS) 1(2), 59–82 (2009)
Westhoff, D., Girao, J., Acharya, M.: Concealed Data Aggregation for Reverse Multicast Traffic in Sensor Networks: Encryption, Key Distribution, and Routing Adaptation. IEEE Transactions on Mobile Computing 5(10), 1417–1431 (2006)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2012 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Sen, J., Maitra, S. (2012). An Attack on Privacy Preserving Data Aggregation Protocol for Wireless Sensor Networks. In: Laud, P. (eds) Information Security Technology for Applications. NordSec 2011. Lecture Notes in Computer Science, vol 7161. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-29615-4_15
Download citation
DOI: https://doi.org/10.1007/978-3-642-29615-4_15
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-29614-7
Online ISBN: 978-3-642-29615-4
eBook Packages: Computer ScienceComputer Science (R0)