Abstract
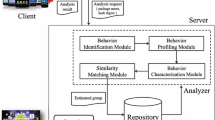
We present Andromaly - a behavioral-based detection framework for Android-powered mobile devices. The proposed framework realizes a Host-based Intrusion Detection System (HIDS) that continuously monitors various features and events obtained from the mobile device, and then applies Machine Learning methods to classify the collected data as normal (benign) or abnormal (malicious). Since no malicious applications are yet available for Android, we evaluated Andromaly’s ability to differentiate between game and tool applications. Successful differentiation between games and tools is expected to provide a positive indication about the ability of such methods to learn and model the behavior of an Android application and potentially detect malicious applications. Several combinations of classification algorithms, feature selections and the number of top features were evaluated. Empirical results suggest that the proposed detection framework is effective in detecting types of applications having similar behavior, which is an indication for the ability to detect unknown malware in the Android framework.
Access provided by Autonomous University of Puebla. Download to read the full chapter text
Chapter PDF
Similar content being viewed by others
References
Leavitt, N.: Mobile phones: the next frontier for hackers? Computer 38(4), 20–23 (2005)
Shih, D.H., Lin, B., Chiang, H.S., Shih, M.H.: Security aspects of mobile phone virus: a critical survey. Industrial Management & Data Systems 108(4), 478–494 (2008)
Piercy, M.: Embedded devices next on the virus target list. IEEE Electronics Systems and Software 2, 42–43 (2004)
Cheng, J., Wong, S.H., Yang, H., Lu, S.: SmartSiren: virus detection and alert for smartphones. In: Proceedings of the 5th International Conference on Mobile Systems, Applications and Services (2007)
Muthukumaran, D., et al.: Measuring integrity on mobile phone systems. In: Proceedings of the 13th ACM Symposium on Access Control Models and Technologies (2008)
Botha, R.A., Furnell, S.M., Clarke, N.L.: From desktop to mobile: Examining the security experience. Computer & Security 28, 130–137 (2009)
Dagon, C., Martin, T., Starner, T.: Mobile phones as computing devices the viruses are coming. Pervasive Computing, 11–15 (2004)
Emm, D.: Lasco: the hybrid threat. Computer Fraud and Security (2005)
Moreau, Y., Preneel, B., Burge, P., Shawe-Taylor, J., Stoermann, C., Cooke, C.: Novel techniques for fraud detection in mobile telecommunication networks. In: ACTS Mobile Summit (1997)
Samfat, D., Molva, R.: IDAMN: An intrusion detection architecture for mobile networks. IEEE Journal on Selected Areas in Communications 15(7), 1373–1380 (1997)
Yap, T.S., Ewe, H.T.: A mobile phone malicious software detection model with behavior checker. In: Shimojo, S., Ichii, S., Ling, T.-W., Song, K.-H. (eds.) HSI 2005. LNCS, vol. 3597, pp. 57–65. Springer, Heidelberg (2005)
Schmidt, A., Peters, F., Lamour, F., Albayrak, S.: Monitoring smartphones for anomaly detection. In: Proceedings of the 1st International Conference on Mobile Wireless Middleware,Operating Systems, and Applications (2008)
Bose, A., Hu, X., Shin, K.G., Park, T.: Behavioral detection of malware on mobile handsets. In: Proceeding of the 6th International Conference on Mobile Systems, Applications, and Services (2008)
Kim, H., Smith, J., Shin, K.G.: Detecting energy-greedy anomalies and mobile malware variants. In: Proceeding of the 6th International Conference on Mobile Systems, Applications, and Services (2008)
Buennemeyer, T.K., et al.: Mobile device profiling and intrusion detection using smart batteries. In: International Conference on System Sciences, pp. 296–296 (2008)
Nash, D.C., et al.: Towards an intrusion detection system for battery exhaustion attacks on mobile computing devices. In: Pervasive Computing and Communications Workshops (2005)
Jacoby, G.A., Davis, N.J.: Battery-based intrusion detection. In: Global Telecommunications Conference (2004)
Hwang, S.S., Cho, S., Park, S.: Keystroke dynamics-based authentication for mobile Devices Computer & Security 28, 85–93 (2009)
Jain, A.K., Murty, M.N., Flynn, P.J.: Data clustering. ACM Computing Surveys 31(3), 264–296 (1999)
Neter, J.K., Nachtsheim, M.H., Wasserman, W.: Applied Linear Statistical Models. McGraw-Hill, New York (1996)
Endler, D.: Intrusion detection: Applying machine learning to solaris audit data. In: Proceedings of the 14th Annual Computer Security Applications Conference (1998)
Quinlan, J.R.: C4.5: Programs for machine learning. Morgan Kaufmann Publishers, Inc., San Francisco (1993)
Pearl, J.: Probabilistic reasoning in intelligent systems: networks of plausible inference. Morgan Kauhmann, San Francisco (1988)
Russel, S., Norvig, P.: Artificial Intelligence: A modern approach. Prentice Hall, Englewood Cliffs (2002)
Imam, I.F., Michalski, R.S., Kerschberg, L.: Discovering Attribute Dependence in Databases by Integrating Symbolic Learning and Statistical Analysis Techniques. In: Proceeding of the AAAI 1993 Workshop on Knowledge Discovery in Databases (1993)
Golub, T., et al.: Molecular classification of cancer: Class discovery and class prediction by gene expression monitoring. Science 286, 531–537 (1999)
Shannon, C.E.: The mathematical theory of communication. The Bell system Technical Journal 27(3), 379–423 (1948)
Shabtai, A., Kanonov, U., Elovici, Y.: Intrusion Detection on Mobile Devices Using the Knowledge Based Temporal-Abstraction Method. Journal of Systems and Software, (2010) doi:10.1016/j.jss.2010.03.046
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2010 ICST Institute for Computer Science, Social Informatics and Telecommunications Engineering
About this paper
Cite this paper
Shabtai, A., Elovici, Y. (2010). Applying Behavioral Detection on Android-Based Devices. In: Cai, Y., Magedanz, T., Li, M., Xia, J., Giannelli, C. (eds) Mobile Wireless Middleware, Operating Systems, and Applications. MOBILWARE 2010. Lecture Notes of the Institute for Computer Sciences, Social Informatics and Telecommunications Engineering, vol 48. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-17758-3_17
Download citation
DOI: https://doi.org/10.1007/978-3-642-17758-3_17
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-17757-6
Online ISBN: 978-3-642-17758-3
eBook Packages: Computer ScienceComputer Science (R0)