Abstract
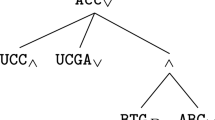
The BDMP (Boolean logic Driven Markov Processes) modeling formalism has recently been adapted from reliability engineering to security modeling. It constitutes an attractive trade-off in terms of readability, modeling power, scalability and quantification capabilities. This paper develops and completes the theoretical foundations of such an adaptation and presents new developments on defensive aspects. In particular, detection and reaction modeling are fully integrated in an augmented theoretical framework. Different use-cases and quantification examples illustrate the relevance of the overall approach.
Access provided by Autonomous University of Puebla. Download to read the full chapter text
Chapter PDF
Similar content being viewed by others
References
Amoroso, E.G.: Threat Trees. In: Fundamentals of computer security technology, ch. 2, pp. 15–29. Prentice-Hall Inc., Englewood Cliffs (1994)
Bouissou, M.: Automated dependability analysis of complex systems with the KB3 workbench: the experience of EDF R&D. In: Proc. International Conference on Energy and Environment (CIEM 2005), Bucharest, Romania (October 2005)
Bouissou, M., Bon, J.: A new formalism that combines advantages of fault-trees and Markov models: Boolean logic driven Markov processes. Reliability Engineering & System Safety 82(2), 149–163 (2003)
Bouissou, M., Lefebvre, Y.: A path-based algorithm to evaluate asymptotic unavailability for large Markov models. In: Proc. Reliability and Maintainability Annual Symposium (RAMS 2002), Seattle, USA, pp. 32–39 (2002)
Harrison, P.: Laplace transform inversion and passage time distributions in Markov processes. Journal of applied probability 27(1), 74–87 (1990)
Jonsson, E., Olovsson, T.: A quantitative model of the security intrusion process based on attacker behavior. IEEE Trans. Soft. Engineering 23(4), 235–245 (1997)
Kotenko, I., Stepashkin, M.: Analyzing network security using malefactor action graphs. Int. Journal of Comp. Science and Network Security 6(6), 226–236 (2006)
Lippmann, R., Ingols, K.: An annotated review of past papers on attack graphs. Project Report ESC-TR-2005-054, Massachusetts Institute of Technology (MIT), Lincoln Laboratory (March 2005)
Littlewood, B., Brocklehurst, S., Fenton, N., Mellor, P., Page, S., Wright, D., Dobson, J., McDermid, J., Gollmann, D.: Towards operational measures of computer security. Journal of Computer Security 2, 211–229 (1993)
Mauw, S., Oostdijk, M.: Foundations of attack trees. In: Won, D.H., Kim, S. (eds.) ICISC 2005. LNCS, vol. 3935, pp. 186–198. Springer, Heidelberg (2006)
McDermott, J.P.: Attack net penetration testing. In: Proceedings of the 2000 Workshop on New Security Paradigms, Ballycotton, Ireland, pp. 15–21 (2000)
Nicol, D.M., Sanders, W.H., Trivedi, K.S.: Model-based evaluation: From dependability to security. IEEE Trans. Dependable and Secure Comp. 1(1), 48–65 (2004)
Ou, Y., Dugan, J.B.: Approximate sensitivity analysis for acyclic Markov reliability models. IEEE Transactions on Reliability 52(2), 220–230 (2003)
Patel, S.C., Graham, J.H., Ralston, P.A.: Quantitatively assessing the vulnerability of critical information systems: A new method for evaluating security enhancements. Int. Journal of Information Management 28(6), 483–491 (2008)
Piètre-Cambacédès, L., Bouissou, M.: Attack and defense dynamic modeling with BDMP (extended version). Technical Report, Telecom ParisTech, Département INFRES (2010)
Piètre-Cambacédès, L., Bouissou, M.: Beyond attack trees: dynamic security modeling with Boolean logic Driven Markov Processes (BDMP). In: Proc. 8th European Dependable Computing Conference (EDCC), Valencia, Spain, pp. 119–208 (April 2010)
Piètre-Cambacédès, L., Chaudet, C.: Disentangling the relations between safety and security. In: Proc. of the 9th WSEAS Int. Conf. on Applied Informatics and Communications (AIC 2009), WSEAS, Moscow, Russia (August 2009)
Pudar, S., Manimaran, G., Liu, C.: PENET: a practical method and tool for integrated modeling of security attacks and countermeasures. Computers & Security In Press, Corrected Proof (May 2009)
Rausand, M., Høyland, A.: System Reliability Theory: Models and Statistical Methods, 2nd edn. Wiley, Chichester (2004)
Sallhammar, K.: Stochastic models for combined security and dependability evaluation. Ph.D. thesis, Norwegian University of Science and Technology NTNU (2007)
Schneier, B.: Attack trees: Modeling security threats. Dr. Dobb’s Journal 12(24), 21–29 (1999)
Sheyner, O., Haines, J., Jha, S., Lippmann, R., Wing, J.: Automated generation and analysis of attack graphs. In: Proc. IEEE Symposium on Security and Privacy (S&P 2002), Oakland, USA, pp. 273–284 (May 2002)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2010 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Piètre-Cambacédès, L., Bouissou, M. (2010). Attack and Defense Modeling with BDMP. In: Kotenko, I., Skormin, V. (eds) Computer Network Security. MMM-ACNS 2010. Lecture Notes in Computer Science, vol 6258. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-14706-7_7
Download citation
DOI: https://doi.org/10.1007/978-3-642-14706-7_7
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-14705-0
Online ISBN: 978-3-642-14706-7
eBook Packages: Computer ScienceComputer Science (R0)