Abstract
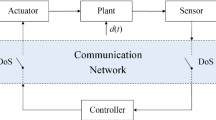
We consider the problem of security constrained optimal control for discrete-time, linear dynamical systems in which control and measurement packets are transmitted over a communication network. The packets may be jammed or compromised by a malicious adversary. For a class of denial-of-service (DoS) attack models, the goal is to find an (optimal) causal feedback controller that minimizes a given objective function subject to safety and power constraints. We present a semi-definite programming based solution for solving this problem. Our analysis also presents insights on the effect of attack models on solution of the optimal control problem.
Access provided by Autonomous University of Puebla. Download to read the full chapter text
Chapter PDF
Similar content being viewed by others
Keywords
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
Amin, S., Abate, A., Prandini, M., Lygeros, J., Sastry, S.: Reachability Analysis for Controlled Discrete Time Stochastic Hybrid Systems. In: Hespanha, J.P., Tiwari, A. (eds.) HSCC 2006. LNCS, vol. 3927, pp. 49–63. Springer, Heidelberg (2006)
Amin, S., Bayen, A.M., El Ghaoui, L., Sastry, S.S.: Robust feasibility for control of water flow in a reservoir canal system. In: Proceedings of the 46th IEEE Conference on Decision and Control, pp. 1571–1577 (2007)
Ben-Tal, A., Boyd, S., Nemirovski, A.: Control of uncertainty-affected discrete time linear systems via convex programming. Technical Report, Minerva Optimization Center, Technion, Haifa, Israel (2005)
Byres, E., Lowe, J.: The myths and facts behind cyber security risks for industrial control systems. In: Proceedings of the VDE Congress, VDE Association for Electrical Electronic & Information Technologies (2004)
Calafiore, G.C., El Ghaoui, L.: Linear programming with probability constraints. In: Proceedings of the 2007 American Control Conference, New York, USA (2007)
Chatterjee, K., de Alfaro, L., Henzinger, T.A.: Termination criteria for solving concurrent Safety and reachability games (2008), http://arxiv.org/abs/0809.4017
Cárdenas, A.A., Amin, S., Sastry, S.: Research Challenges for the Security of Control Systems. In: 3rd USENIX workshop on Hot Topics in Security (HotSec 2008). Associated with the 17th USENIX Security Symposium, San Jose, CA (2008)
Downs, J.J., Vogel, E.F.: A plant-wide industrial process control problem. Computers & Chemical Engineering 17(3), 245–255 (1993)
Gattami, A.: Optimal decision with limited information. PhD thesis, Department of Automatic Control, Lund University (2007)
Goulart, P.J., Kerrigan, E.C., Maciejowski, J.M.: Optimization over state feedback policies for robust control with constraints. Automatica 42(2), 523–533 (2006)
Mayne, D.Q., Rawlings, J.B., Rao, C.V., Scokaert, P.O.M.: Constrained model predictive control: stability and optimality. Automatica 36(6), 789–814 (2000)
Nguyen, K.C., Alpcan, T., Basar, T.: A decentralized Bayesian attack detection algorithm for network security. In: Proc. of 23rd Intl. Information Security Conf., Milan, pp. 413–428 (2008)
Pinar, A., Meza, J., Donde, V., Lesieutre, B.: Optimization strategies for the vulnerability analysis of the power grid. Submitted to SIAM Journal on Optimization (2008)
Primbs, J., Sung, C.: Stochastic receding horizon control of constrained linear systems with state and control multiplicative noise. Submitted to IEEE Transactions on Automatic Control (2007)
Salmeron, J., Wood, K., Baldick, B.: Analysis of electric grid security under terrorist threat. IEEE Transactions on power systems 19, 905–912 (2004)
Schenato, L., Sinopoli, B., Franceschetti, M., Poolla, K., Sastry, S.: Foundations of control and estimation over lossy networks. Proceedings of the IEEE, Special issue on networked control systems 95(1), 163–187 (2007)
Skaf, J., Boyd, S.: Design of affine controllers via convex optimization. Submitted to the IEEE Transactions on Automatic Control (2008)
Turk, R.J.: Cyber Incidents Involving Control Systems. Technical Report, Idaho National Laboratory (2005)
van Hessem, D., Bosgra, O.: A full solution to the constrained stochastic closed-loop MPC problem via state and innovations feedback and its receding horizon implementation. In: Proceedings of the 2003 Conference on Decision and Control, Maui, Hawaii, USA (2003)
Wang, Y., Boyd, S.: Fast model predictive control using online optimization. Submitted to IEEE Transactions on Control Systems Technology (2008)
Yu, Z.H., Li, W., Lee, J.H., Morari, M.: State estimation based model predictive control applied to shell control problem: a case study. Chemical engineering science 49(3), 285–301 (1994)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2009 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Amin, S., Cárdenas, A.A., Sastry, S.S. (2009). Safe and Secure Networked Control Systems under Denial-of-Service Attacks. In: Majumdar, R., Tabuada, P. (eds) Hybrid Systems: Computation and Control. HSCC 2009. Lecture Notes in Computer Science, vol 5469. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-00602-9_3
Download citation
DOI: https://doi.org/10.1007/978-3-642-00602-9_3
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-00601-2
Online ISBN: 978-3-642-00602-9
eBook Packages: Computer ScienceComputer Science (R0)