Abstract
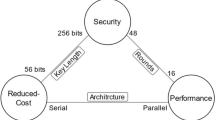
In recent years more and more security sensitive applications use passive smart devices such as contactless smart cards and RFID tags. Cost constraints imply a small hardware footprint of all components of a smart device. One particular problem of all passive smart devices such as RFID tags and contactless smart cards are the harsh power constraints. On the other hand, active smart devices have to minimize energy consumption. Recently, many lightweight block ciphers have been published. In this paper we present three different architecture of the ultra-lightweight algorithm present and highlight their suitability for both active and passive smart devices. Our implementation results of the serialized architecture require only 1000 GE. To the best of our knowledge this is the smallest hardware implementation of a cryptographic algorithm with a moderate security level.
Chapter PDF
Similar content being viewed by others
Keywords
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
Keeloq algorithm (November 2006), http://en.wikipedia.org/wiki/KeeLoq
Bogdanov, A.: Attacks on the KeeLoq Block Cipher and Authentication Systems. In: 3rd Conference on RFID Security 2007 (RFIDSec 2007) (2007)
Bogdanov, A., Leander, G., Knudsen, L.R., Paar, C., Poschmann, A., Robshaw, M.J., Seurin, Y., Vikkelsoe, C.: PRESENT - An Ultra-Lightweight Block Cipher. In: Paillier, P., Verbauwhede, I. (eds.) CHES 2007. LNCS, vol. 4727 Springer, Heidelberg (2007)
Cast Inc. Cast aes32-c, http://www.cast-inc.com
Hong, S., Lim, J., Lee, S., Koo, B.-S., Lee, C., Chang, D., Lee, J., Jeong, K., Kim, H., Kim, J., Hong, D., Sung, J., Chee, S.: HIGHT: A New Block Cipher Suitable for Low-Resource Device. In: Goubin, L., Matsui, M. (eds.) CHES 2006. LNCS, vol. 4249, pp. 46–59. Springer, Heidelberg (2006)
Feldhofer, M., Wolkerstorfer, J., Rijmen, V.: AES implementation on a grain of sand. In: Information Security, IEE Proceedings, vol. 152, pp. 13–20 (October 2005)
Feldhofer, M., Dominikus, S., Wolkerstorfer, J.: Strong Authentication for RFID Systems Using the AES Algorithm (2004)
Finkenzeller, K.: RFID Handbook - Fundamentals and Applications in Contactless Smart Cards and Identification, 2nd edn. John Wiley and Sons. Ltd., Chichester (2003)
Good, T., Benaissa, M.: Hardware Results for selected Stream Cipher Candidates. In: State of the Art of Stream Ciphers 2007 (SASC 2007), Workshop Record (February 2007)
Hämäläinen, P., Alho, T., Hännikäinen, M., Hämäläinen, T.D.: Design and implementation of low-area and low-power aes encryption hardware core. In: DSD, pp. 577–583 (2006)
Hong, D., Sung, J., Hong, S., Lim, J., Lee, S., Koo, B.-S., Lee, C., Chang, D., Lee, J., Jeong, K., Kim, H., Kim, J., Chee, S.: HIGHT: A New Block Cipher Suitable for Low-Resource Device (2006)
Kerckhoff, A.: La cryptographie militaire. Journal des sciences militaires IX, 5–38 (1883)
Leander, G., Paar, C., Poschmann, A., Schramm, K.: New Lighweight DES Variants. In: Biryukov, A. (ed.) FSE 2007. LNCS, vol. 4593, pp. 196–210. Springer, Heidelberg (2007)
Lim, C., Korkishko, T.: mcrypton - a lightweight block cipher for security of low-cost rfid tags and sensors. In: Kwon, T., Song, J., Yung, M. (eds.) WISA 2005. LNCS, vol. 3786, pp. 243–258. Springer, Heidelberg (2006)
Mace, F., Standaert, F.-X., Quisquater, J.-J.: ASIC Implementations of the Block Cipher SEA for Constrained Applications. In: Proceedings of the Third International Conference on RFID Security - RFIDSec 2007, Malaga, Spain, pp. 103–114 (2007)
N.A. Contactless Specifications for Payment Systems - EMV Contactless Communication Protocol Specification. Version 2.0, EMV (August 2007), http://www.emvco.com/specifications.asp
N.A. Contactless Specifications for Payment Systems - Entry Point Specification. Draft 1.0, EMV (October 2007), http://www.emvco.com/specifications.asp
Nohl, K., Ploetz, H.: Mifare - little security, despite obscurity. Talk at the 24th Chaos Communication Congress (December 2007)
Pramstaller, N., Mangard, S., Dominikus, S., Wolkerstorfe, J.: Efficient aes implementations on asics and fpgas. In: Dobbertin, H., Rijmen, V., Sowa, A. (eds.) AES 2005. LNCS, vol. 3373, pp. 98–112. Springer, Heidelberg (2005)
Satoh, A., Morioka, S., Takano, K., Munetoh, S.: A compact rijndael hardware architecture with s-box optimization. In: Boyd, C. (ed.) ASIACRYPT 2001. LNCS, vol. 2248, pp. 239–254. Springer, Heidelberg (2001)
Standaert, F.-X., Piret, G., Gershenfeld, N., Quisquater, J.-J.: Sea: A scalable encryption algorithm for small embedded applications. In: Domingo-Ferrer, J., Posegga, J., Schreckling, D. (eds.) CARDIS 2006. LNCS, vol. 3928, pp. 222–236. Springer, Heidelberg (2006)
Visa. Visa payWave FAQ (accessed on 15.02.2008), www.visa.com
Author information
Authors and Affiliations
Editor information
Rights and permissions
Copyright information
© 2008 IFIP International Federation for Information Processing
About this paper
Cite this paper
Rolfes, C., Poschmann, A., Leander, G., Paar, C. (2008). Ultra-Lightweight Implementations for Smart Devices – Security for 1000 Gate Equivalents. In: Grimaud, G., Standaert, FX. (eds) Smart Card Research and Advanced Applications. CARDIS 2008. Lecture Notes in Computer Science, vol 5189. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-540-85893-5_7
Download citation
DOI: https://doi.org/10.1007/978-3-540-85893-5_7
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-85892-8
Online ISBN: 978-3-540-85893-5
eBook Packages: Computer ScienceComputer Science (R0)