Abstract
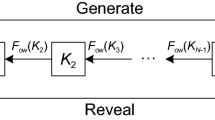
Existing navigation services, such as GPS, offer no signal-integrity (anti-spoof) protection for the general public, especially not with systems for remote attestation of location, where an attacker has easy access to the receiver antenna. With predictable broadcast signals, the antenna can be replaced with a signal generator that simulates a signal as it would be received elsewhere. With a symmetrically encrypted broadcast signal, anyone who can build or reverse engineer a receiver will know the secret key needed to spoof other receivers. Such encryption is only of use in closed user communities (e.g., military) or with highly tamper-resistant modules protecting the common key. In open user communities without common secret keys, integrity protection is needed instead, with properties similar to digital signatures. The ability to verify a navigation signal must be separate from the ability to generate a new one or to apply selective-delay attacks; but simply signing the broadcast signals will not protect their exact relative arrival times. This paper introduces a practical solution based on short-term information hiding.
Access provided by Autonomous University of Puebla. Download to read the full chapter text
Chapter PDF
Similar content being viewed by others
Keywords
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
Kallender, P.: Omron uses GPS to catch a car thief. EE Times, June 12 (2001), http://www.eetimes.com/at/news/OEG20010612S0059
Denning, D.E., MacDoran, P.F.: Location-based authentication: Grounding cyberspace for better security. Computer Fraud & Security, Elsevier, pp. 12–16 (February 1996), http://www.cosc.georgetown.edu/~denning/infosec/Grounding.txt
Electronic tagging: A virtual prison? BBC News Online, January 7 (2000), http://news.bbc.co.uk/1/hi/specialreport/1999/02/99/e-cyclopedia/594314.stm
Spilker Jr., J.J.: GPS signal structure and theoretical performance. In: Parkinson, B.W., Spilker Jr., J.J. (eds.) Global Positioning System: Theory and Applications, Washington DC. Progress in Astronautics and Aeronautics, American Institute of Aeronautics and Astronautics, vol. I, 163 (1996) ISBN 1-56347-106-X
Perrig, A., Canetti, R., Tygar, J.D., Song, D.: The TESLA broadcast authentication protocol. CryptoBytes, Vol. 5, No. 2, pp. 2–13, RSA Laboratories (Summer/Fall 2002)
Radio noise. Recommendation ITU-R P.372-7, International Telecommunication Union, Geneva (2001)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2004 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Kuhn, M.G. (2004). An Asymmetric Security Mechanism for Navigation Signals. In: Fridrich, J. (eds) Information Hiding. IH 2004. Lecture Notes in Computer Science, vol 3200. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-540-30114-1_17
Download citation
DOI: https://doi.org/10.1007/978-3-540-30114-1_17
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-24207-9
Online ISBN: 978-3-540-30114-1
eBook Packages: Computer ScienceComputer Science (R0)