Abstract
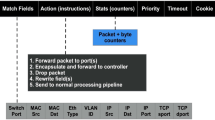
Software Defined Networks (SDN) aim to deconstruct current routers into a small number of controllers, which are general purpose machines, and a large number of switches that contain programmable forwarding engines. The vision is that, instead of the ad-hoc mechanisms used in current routers, we can build programmable networks using proper computer science abstractions. This technology is now at the startup stage, and is being deployed in the data centres of large web service firms.
We are interested in protecting a future SDN. The current designs follow traditional security assumptions and do not consider many likely deployment scenarios. We discuss how SDN architecture can be structured to offer more security, the auxiliary services that such a network will require and the advantages that it can offer.
Access provided by Autonomous University of Puebla. Download to read the full chapter text
Chapter PDF
Similar content being viewed by others
Keywords
- Virtual Network
- Access Control Policy
- Monitoring Service
- Threat Model
- Defense Advance Research Project Agency
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
Arends, R., Austein, R., Larson, M., Massey, D., Rose, S.: DNS Security Introduction and Requirements. RFC 4033 (Proposed Standard) (March 2005), http://www.ietf.org/rfc/rfc4033.txt
Foster, N., Guha, A., Reitblatt, M., Story, A., Freedman, M.J., Katta, N.P., Monsanto, C., Reich, J., Rexford, J., Schlesinger, C., Story, A., Walker, D.: Languages for software-defined networks. IEEE Communications Magazine 51(2), 128–134 (2013)
Gutz, S., Story, A., Schlesinger, C., Foster, N.: Splendid isolation: a slice abstraction for software-defined networks. In: Proceedings of the First Workshop on Hot Topics in Software Defined Networks, HotSDN 2012, pp. 79–84. ACM (2012)
Hoelzle, U.: OpenFlow @ Google, keynote address at the Open Network Summit (2012)
Lepinski, M. (ed.): BGPSEC Protocol Specification (February 2013), http://www.ietf.org/id/draft-ietf-sidr-bgpsec-protocol-07.txt
Porras, P., Shin, S., Yegneswaran, V., Fong, M., Tyson, M., Gu, G.: A security enforcement kernel for OpenFlow networks. In: Proceedings of the First Workshop on Hot Topics in Software Defined Networks, HotSDN 2012, pp. 121–126. ACM (2012)
Reitblatt, M., Foster, N., Rexford, J., Schlesinger, C., Walker, D.: Abstractions for network update. In: Proceedings of the ACM SIGCOMM 2012 Conference on Applications, Technologies, Architectures, and Protocols for Computer Communication, SIGCOMM 2012, pp. 323–334. ACM (2012)
Shin, S., Porras, P., Yegneswaran, V., Fong, M., Gu, G., Tyson, M.: Fresco: Modular composable security services for software-defined networks. Internet Society NDSS (to appear, February 2013)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2013 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Yu, D., Moore, A.W., Hall, C., Anderson, R. (2013). Authentication for Resilience: The Case of SDN. In: Christianson, B., Malcolm, J., Stajano, F., Anderson, J., Bonneau, J. (eds) Security Protocols XXI. Security Protocols 2013. Lecture Notes in Computer Science, vol 8263. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-41717-7_6
Download citation
DOI: https://doi.org/10.1007/978-3-642-41717-7_6
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-41716-0
Online ISBN: 978-3-642-41717-7
eBook Packages: Computer ScienceComputer Science (R0)