Abstract
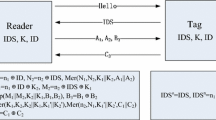
One of the most important challenges related to RFID systems is the verification of security proprieties in RFID authentication protocols. Among the important attacks in RFID systems, we speak about the Algebraic Replay Attack on Authentication (ARA). Common characteristic between the verified protocols cannot resist algebraic replay attacks. Our work is articulated on the formal automatic verification of RFID protocols by two different tools, firstly, the Open-source Fixedpoint Model Checker (OFMC) tool, secondary, the Constraint Logic based Attack Searcher (Cl-Atse) tool. These tools sufficient for detecting the attach of type ARA.
Access provided by Autonomous University of Puebla. Download to read the full chapter text
Chapter PDF
Similar content being viewed by others
Keywords
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
Basin, D., Mödersheim, S., Viganò, L.: OFMC: A symbolic model checker for security protocols. International Journal of Information Security 4(3), 181–208 (2005)
Modersheim, S., Vigano, L.: The open-source Fixed-point model checker for symbolic analysis of security protocols. In: Aldini, A., Barthe, G., Gorrieri, R. (eds.) FOSAD 2007/2008/2009. LNCS, vol. 5705, pp. 166–194. Springer, Heidelberg (2009)
Turuani, M.: The CL-Atse Protocol Analyser. In: Pfenning, F. (ed.) RTA 2006. LNCS, vol. 4098, pp. 277–286. Springer, Heidelberg (2006)
HLPSL Tutorial: A Beginner’s Guide to Modelling and Analysing Internet Security Protocols (2005), http://www.avispa-project.org/
Mödersheim, S.: Algebraic Properties in Alice and Bob Notation. In: Proceedings of Ares 2009, pp. 433–440. IEEE Xplore (2009); Extended version: Technical Report RZ3709, IBM Zurich Research Lab (2008)
Dolev, D., Yao, A.: On the security of public key protocols. IEEE Transactions on Information Theory IT-29(2), 198–208 (1983)
Lee, S., Asano, T., Kim, K.: RFID mutual authentication scheme based on synchronized secret information. In: Symposium on Cryptography and Information Security (2006)
Chien, H.-Y., Huang, C.-W.: A lightweight RFID Protocol Using Substring. In: Embedded Ubiquitous Computing (EUC), pp. 422–431 (2007)
Liu, Y.: An Efficient RFID Authentication Protocol for Low-Cost Tags. In: Proceedings of IEEE/IFIP International Conference on Embedded and Ubiquitous Computing, Shanghai, China, pp. 706–711 (2008)
Qingling, C., Yiju, Z., Yonghua, W.: A minimalist mutual authentication protocol for RFID system & BAN logic analysis. In: Proc. of CCCM 2008, pp. 449–453. IEEE Computer Society, Los Alamitos (2008)
Wei, C.-H., Hwang, M.-S., Chin, A.-Y.: A Mutual Authentication Protocol for RFID. IT Professional 3, 20–24 (2011)
van Deursen, T., Radomirović, S.: Algebraic Attacks on RFID Protocols. In: Markowitch, O., Bilas, A., Hoepman, J.-H., Mitchell, C.J., Quisquater, J.-J. (eds.) WISTP 2009. LNCS, vol. 5746, pp. 38–51. Springer, Heidelberg (2009)
Cao, T., Shen, P.: Cryptanalysis of Two RFID Authentication Protocols. International Journal of Network Security 9(1), 95–100 (2009)
Jannati, H., Falahati, A.: Cryptanalysis and Enhanced of Two Low Cost RFID Authentication protocols. International Journal of UbiComp 3(1), 1–9 (2012)
van Deursen, T., Radomirovic, S.: Attacks on RFID Protocols. Report 2008/310, Cryptology ePrint Archive (2008)
Chen, X., van Deursen, T., Pang, J.: Improving Automatic Verification of Security Protocols with XOR. In: Breitman, K., Cavalcanti, A. (eds.) ICFEM 2009. LNCS, vol. 5885, pp. 107–126. Springer, Heidelberg (2009)
Mihailescu, M.I.: Resreach on Solutions for Preventing Algebraic Attacks Against Biometric and RFID Protocols. ACTA Universitatis Apulensis (Special Issue), 371–386 (2011)
Chikouche, N., Cherif, F., Benmohammed, M.: Vulnerabilities of two Recently RFID Authentication Protocols. In: International Conference on Complex Systems, Agadir, Morocco (2012)
Hancke, G.P.: Practical Attacks on Proximity Identification Systems. In: Proceedings of IEEE Symposium on Security and Privacy, pp. 328–333 (May 2006) (short paper)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2013 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Chikouche, N., Cherif, F., Benmohammed, M. (2013). Algebraic Replay Attacks on Authentication in RFID Protocols. In: Awad, A.I., Hassanien, A.E., Baba, K. (eds) Advances in Security of Information and Communication Networks. SecNet 2013. Communications in Computer and Information Science, vol 381. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-40597-6_13
Download citation
DOI: https://doi.org/10.1007/978-3-642-40597-6_13
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-40596-9
Online ISBN: 978-3-642-40597-6
eBook Packages: Computer ScienceComputer Science (R0)