Abstract
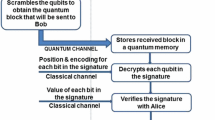
We employ physical properties of the real world to design a protocol for secure information transmission where one of the parties is able to transmit secret information to another party over an insecure channel, without any prior secret arrangements between the parties. The distinctive feature of this protocol, compared to all known public-key cryptographic protocols, is that neither party uses a one-way function. In particular, our protocol is secure against (passive) computationally unbounded adversary.
Access provided by Autonomous University of Puebla. Download to read the full chapter text
Chapter PDF
Similar content being viewed by others
Keywords
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
Bennett, C.H., Brassard, G.: Quantum Cryptography: Public key distribution and coin tossing. In: Proceedings of the IEEE International Conference on Computers, Systems, and Signal Processing, Bangalore, p. 175 (1984)
Garey, M., Johnson, J.: Computers and Intractability, A Guide to NP-Completeness. W. H. Freeman (1979)
Grigoriev, D., Shpilrain, V.: Secrecy without one-way functions. Groups, Complexity, Cryptology 5 (2013)
Impagliazzo, R., Luby, M.: One-way functions are essential for information based cryptography. In: Proc. 30th IEEE Sympos. on Found. of Comput. Sci., pp. 230–235. IEEE, New York (1989)
Kahrobaei, D., Habeeb, M., Shpilrain, V.: A secret sharing scheme based on group presentations and the word problem. Contemp. Math., Amer. Math. Soc. 582, 143–150 (2012)
Shamir, A.: How to share a secret. Comm. ACM 22, 612–613 (1979)
Yao, A.C.: Protocols for secure computations (Extended Abstract). In: 23rd Annual Symposium on Foundations of Computer Science (Chicago, Ill., 1982), pp. 160–164. IEEE, New York (1982)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2013 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Grigoriev, D., Shpilrain, V. (2013). Secure Information Transmission Based on Physical Principles. In: Mauri, G., Dennunzio, A., Manzoni, L., Porreca, A.E. (eds) Unconventional Computation and Natural Computation. UCNC 2013. Lecture Notes in Computer Science, vol 7956. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-39074-6_12
Download citation
DOI: https://doi.org/10.1007/978-3-642-39074-6_12
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-39073-9
Online ISBN: 978-3-642-39074-6
eBook Packages: Computer ScienceComputer Science (R0)