Abstract
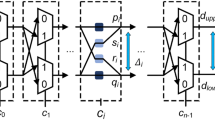
A lightweight and secure key storage scheme using silicon Physical Unclonable Functions (PUFs) is described. To derive stable PUF bits from chip manufacturing variations, a lightweight error correction code (ECC) encoder / decoder is used. With a register count of 69, this codec core does not use any traditional error correction techniques and is 75% smaller than a previous provably secure implementation, and yet achieves robust environmental performance in 65nm FPGA and 0.13μ ASIC implementations. The security of the syndrome bits uses a new security argument that relies on what cannot be learned from a machine learning perspective. The number of Leaked Bits is determined for each Syndrome Word, reducible using Syndrome Distribution Shaping. The design is secure from a min-entropy standpoint against a machine-learning-equipped adversary that, given a ceiling of leaked bits, has a classification error bounded by ε. Numerical examples are given using latest machine learning results.
Chapter PDF
Similar content being viewed by others
Keywords
References
Bösch, C., Guajardo, J., Sadeghi, A.-R., Shokrollahi, J., Tuyls, P.: Efficient Helper Data Key Extractor on FPGAs. In: Oswald, E., Rohatgi, P. (eds.) CHES 2008. LNCS, vol. 5154, pp. 181–197. Springer, Heidelberg (2008)
Cover, T., Thomas, J.: Elements of Information Theory, 2nd edn. (2006)
Devadas, S., Suh, E., Paral, S., Sowell, R., Ziola, T., Khandelwal, V.: Design and Implementation of PUF-Based ’Unclonable’ RFID ICs for Anti-Counterfeiting and Security Applications. In: Proc. RFID 2008, pp. 58–64 (May 2008)
Dodis, Y., Ostrovsky, R., Reyzin, L., Smith, A.: Fuzzy Extractors: How to Generate Strong Keys from Biometrics and Other Noisy Data (2008)
Gassend, B.: Physical Random Functions, Master’s Thesis, EECS, MIT (2003)
Gassend, B., Clarke, D., van Dijk, M., Devadas, S.: Silicon Physical Random Functions. In: Proc. ACM CCS, pp. 148–160. ACM Press, New York (2002)
Guajardo, J., Kumar, S., Schrijen, G., Tuyls, P.: FPGA intrinsic pUFs and their use for IP protection. In: Paillier, P., Verbauwhede, I. (eds.) CHES 2007. LNCS, vol. 4727, pp. 63–80. Springer, Heidelberg (2007)
Holcomb, D., Burleson, W., Fu, K.: Initial SRAM State as a Fingerprint and Source of True Random Numbers for RFID Tags. In: Conf. RFID Security (2007)
Kocher, P., Jaffe, J., Jun, B.: Differential power analysis. In: Wiener, M. (ed.) CRYPTO 1999. LNCS, vol. 1666, pp. 388–397. Springer, Heidelberg (1999)
Krawczyk, H.: LFSR-based hashing and authentication. In: Desmedt, Y.G. (ed.) CRYPTO 1994. LNCS, vol. 839, pp. 129–139. Springer, Heidelberg (1994)
Lim, D.: Extracting Secret Keys from Integrated Circuits, MS Thesis, MIT (2004)
Maes, R., Tuyls, P., Verbauwhede, I.: A Soft Decision Helper Data Algorithm for SRAM PUFs. In: IEEE ISIT 2009. IEEE Press, Los Alamitos (2009)
Ruhrmair, U.: On the Foundations of Physical Unclonable Functions (2009)
Ruhrmair, U., Sehnke, F., Solter, J., Dror, G., Devadas, S., Schmidhuber, J.: Modeling Attacks on Physical Unclonable Functions. In: Proc. ACM CCS (October 2010)
Sehnke, F., Osendorfer, C., Sölter, J., Schmidhuber, J., Rührmair, U.: Policy gradients for cryptanalysis. In: Diamantaras, K., Duch, W., Iliadis, L.S. (eds.) ICANN 2010. LNCS, vol. 6354, pp. 168–177. Springer, Heidelberg (2010)
Skorobogatov, S.P.: Semi-Invasive Attacks: A New Approach to Hardware Security Analysis. Univ. Cambridge, Computer Lab.: Tech. Report (April 2005)
Su, Y., Holleman, J., Otis, B.: A 1.6pJ/bit 96 (percent) Stable Chip ID Generating Circuit Using Process Variations. In: ISSCC 2007, pp. 200–201 (2007)
Suh, G.: AEGIS: A Single-Chip Secure Processor, PhD thesis, EECS, MIT (2005)
Suh, G., Devadas, S.: Physical Unclonable Functions for Device Authentication and Secret Key Generation. In: DAC 2007, pp. 9–14 (2007)
Vapnik, V., Chervonenkis, A.: On the uniform convergence of relative frequencies of events to their probabilities. Theory of Prob. and its App. (1971)
Yu, M., Devadas, S.: Secure and Robust Error Correction for Physical Unclonable Functions. IEEE D&T 27(1), 48–65 (2010)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2011 International Association for Cryptologic Research
About this paper
Cite this paper
Yu, MD.(., M’Raihi, D., Sowell, R., Devadas, S. (2011). Lightweight and Secure PUF Key Storage Using Limits of Machine Learning. In: Preneel, B., Takagi, T. (eds) Cryptographic Hardware and Embedded Systems – CHES 2011. CHES 2011. Lecture Notes in Computer Science, vol 6917. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-23951-9_24
Download citation
DOI: https://doi.org/10.1007/978-3-642-23951-9_24
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-23950-2
Online ISBN: 978-3-642-23951-9
eBook Packages: Computer ScienceComputer Science (R0)