Abstract
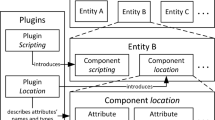
In virtual reality systems which are collaborative and dynamic, i.e. where at run-time mutually interactive objects can be added or removed in different contexts and where their behavior can be modified, the problem of data security and privacy protection is renewed. In such virtual worlds operations on objects should or should not be allowed to users playing particular roles with respect to inter-object interactions. In this paper a method called VR-PR is presented, where privileges are represented by pairs: object – semantic operations induced from object interactions. Semantic operations are generated using automatic analysis of the object method call graphs. Then they are used in the privilege creation and modification process. Privileges based on semantic operations are expressive, flexible and consistent with permanently evolving set of objects composing the virtual world, interactions between the objects, and a set of users.
Chapter PDF
Similar content being viewed by others
References
Qiu, Z.M., Kok, K.F., Wong, Y.S., Fuh, J.Y.: Role-based 3D visualisation for asynchronous PLM collaboration. Comput. Ind. 58(8-9), 747–755 (2007)
Wang, Y., Ajoku, P., Brustoloni, J., Nnaji, B.J.: Intellectual Property Protection in Collaborative Design through Lean Information Modeling and Sharing. Comput. Inf. Sci. Eng. 6, 149 (2006)
Cera, D.D., Kim, T., Han, J., Regli, W.C.: Role-based viewing envelopes for information protection in collaborative modeling. Computer-Aided Design 36(1), 873–886 (2004)
Fang, C., Peng, W., Ye, X., Zhang, S.: Multi-level access control for collaborative CAD. In: Proceedings of the Ninth International Conference on Computer Supported Cooperative Work in Design, vol. 1, pp. 643–648 (2005)
Pettifer, S., Marsh, J.: A Collaborative Access Model for Shared Virtual Environments. In: Proceedings of the 10th IEEE international Workshops on Enabling Technologies: infrastructure For Collaborative Enterprises. WETICE, pp. 257–262. IEEE Computer Society, Washington (2001)
Bullock, A., Benford, S.: An access control framework for multi-user collaborative environments. In: Proceedings of the international ACM SIGGROUP Conference on Supporting Group Work, pp. 140–149. ACM, NY (1999)
Walczak, K.: Structured Design of Interactive VR Applications. In: The 13th International Symposium on 3D Web Technology Web3D, Los Angeles, California, USA, pp. 105–113. ACM Press, NY (2008)
Latoschik, M.E., Biermann, P., Wachsmuth, I.: Knowledge in the Loop: Semantics Representation for Multimodal Simulative Environments. In: Butz, A., Fisher, B., Krüger, A., Olivier, P. (eds.) SG 2005. LNCS, vol. 3638, pp. 25–39. Springer, Heidelberg (2005)
Lugrin, J., Cavazza, M.: Making sense of virtual environments: action representation, grounding and common sense. In: Proceedings of the 12th international Conference on intelligent User interfaces, IUI 2007, pp. 225–234. ACM, NY (2007)
Pittarello, F., De Faveri, A.: Semantic description of 3D environments: a proposal based on web standards. In: Proceedings of the Eleventh international Conference on 3D Web Technology. Web3D 2006, pp. 85–95. ACM, NY (2006)
Gutierrez, M., Vexo, F., Thalmann, D.: Semantics-based representation of virtual environments. IJCAT 23, 229–238 (2005)
Sallés, E.J., Michael, J.B., Capps, M., McGregor, D., Kapolka, A.: Security of runtime extensible virtual environments. In: Proceedings of the 4th International Conference on Collaborative Virtual Environments, CVE 2002, pp. 97–104. ACM, NY (2002)
Tolone, W., Ahn, G., Pai, T., Hong, S.: Access control in collaborative systems. ACM Comput. Surv. 37(1), 29–41 (2005)
Izaki, K., Tanaka, K., Takizawa, M.: Authorization model based on object-oriented concept. In: Proceedings of the the 15th international Conference on information Networking. ICOIN, pp. 72–77. IEEE Computer Society, Washington (2001)
Wong, R.K.: RBAC support in object-oriented role databases. In: Proceedings of the Second ACM Workshop on Role-Based Access Control, Fairfax, Virginia, United States, RBAC 1997, pp. 109–120. ACM, New York (1997)
Sandhu, R., Ferraiolo, D., Kuhn, R.: The NIST model for role-based access control: towards a unified standard. In: Proceedings of the Fifth ACM Workshop on Role-Based Access Control, RBAC 2000, pp. 47–63. ACM, NY (2000)
Priebe, T., Dobmeier, W., Schläger, C., Kamprath, N.: Supporting Attribute-based Access Control in Authentication and Authorization Infrastructures with Ontologies. Journal of software: JSW 2(1), 27–38 (2007)
Wang, X., Demartini, T., Wragg, B., Paramasivam, M., Barlas, C.: The mpeg-21 rights expression language and rights data dictionary. IEEE Transactions on Multimedia 7(3), 408–417 (2005)
Moses, T. (ed.): eXtensible Access Control Markup Language (XACML) Version 2.0., http://docs.oasis-open.org/xacml/2.0/access_control-xacml-2.0-core-spec-os.pdf
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2010 IFIP International Federation for Information Processing
About this paper
Cite this paper
Wójtowicz, A., Cellary, W. (2010). Representing User Privileges in Object-Oriented Virtual Reality Systems. In: Camarinha-Matos, L.M., Pereira, P., Ribeiro, L. (eds) Emerging Trends in Technological Innovation. DoCEIS 2010. IFIP Advances in Information and Communication Technology, vol 314. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-11628-5_6
Download citation
DOI: https://doi.org/10.1007/978-3-642-11628-5_6
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-11627-8
Online ISBN: 978-3-642-11628-5
eBook Packages: Computer ScienceComputer Science (R0)