Abstract
The last years have seen the definition of many languages, models and standards tailored to specify and enforce access control policies, but such frameworks do not provide methodological support during the policy specification process. In particular, they do not provide facilities for the analysis of the social context where the system operates.
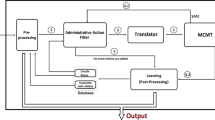
In this paper we propose a model-driven approach for the specification and analysis of access control policies. We build this framework on top of SI*, a modeling language tailored to capture and analyze functional and security requirements of socio-technical systems. The framework also provides formal mechanisms to assist policy writers and system administrators in the verification of access control policies and of the actual user-permission assignment.
This work has been partially funded by the EU-IST-IP SERENITY and SENSORIA projects, and by the Canada’s NSERC Hyperion project.
Access provided by Autonomous University of Puebla. Download to read the full chapter text
Chapter PDF
Similar content being viewed by others
References
Ahn, G.-J., Sandhu, R.: The RSL99 language for role-based separation of duty constraints. In: Proc. of RBAC 1999, pp. 43–54. ACM Press, New York (1999)
Antón, A.I., Potts, C.: The use of goals to surface requirements for evolving systems. In: Proc. of ICSE 1998, pp. 157–166. IEEE Press, Los Alamitos (1998)
Association of Certified Fraud Examiners. The 2006 report to the nation (2006)
Basin, D., Doser, J., Lodderstedt, T.: Model Driven Security: from UML Models to Access Control Infrastructures. TOSEM 15(1), 39–91 (2006)
Becker, M.Y., Sewell, P.: Cassandra: flexible trust management, applied to electronic health records. In: Proc. of CSFW 2004, pp. 139–154. IEEE Press, Los Alamitos (2004)
Bell, D.E., LaPadula, L.J.: Secure Computer System: Unified Exposition and MULTICS Interpretation. Technical Report MTR-2997 Rev. 1, The MITRE Corporation, Bedford, MA (1976)
Bertino, E., Ferrari, E., Atluri, V.: The specification and enforcement of authorization constraints in workflow management systems. TISSEC 2(1), 65–104 (1999)
Breu, R., Popp, G., Alam, M.: Model based development of access policies. STTT 9, 457–470 (2007)
Calimeri, F., Ianni, G.: External Sources of Computation for Answer Set Solvers. In: Baral, C., Greco, G., Leone, N., Terracina, G. (eds.) LPNMR 2005. LNCS (LNAI), vol. 3662, pp. 105–118. Springer, Heidelberg (2005)
Coyne, E.J.: Role engineering. In: Proc. of RBAC 1995, pp. 15–16. ACM Press, New York (1995)
Crook, R., Ince, D., Nuseibeh, B.: On Modelling Access Policies: Relating Roles to their Organisational Context. In: Proc. of RE 2005, pp. 157–166 (2005)
Damianou, N., Dulay, N., Lupu, E., Sloman, M.: The Ponder Policy Specification Language. In: Sloman, M., Lobo, J., Lupu, E.C. (eds.) POLICY 2001. LNCS, vol. 1995, pp. 18–39. Springer, Heidelberg (2001)
Dardenne, A., van Lamsweerde, A., Fickas, S.: Goal-directed Requirements Acquisition. Sci. of Comp. Prog. 20, 3–50 (1993)
Doan, T., Demurjian, S., Ting, T.C., Ketterl, A.: MAC and UML for secure software design. In: Proc. of FMSE 2004, pp. 75–85. ACM Press, New York (2004)
Dobson, J.E., McDermid, J.A.: A framework for expressing models of security policy. In: Proc. of Symp. on Sec. and Privacy, pp. 229–239. IEEE Press, Los Alamitos (1989)
Ferraiolo, D.F., Barkley, J.F., Kuhn, D.R.: A role-based access control model and reference implementation within a corporate intranet. TISSEC 2(1), 34–64 (1999)
Fontaine, P.-J.: Goal-Oriented Elaboration of Security Requirements. Ph.D thesis, Université Catholique de Louvain (2001)
Giorgini, P., Massacci, F., Zannone, N.: Security and Trust Requirements Engineering. In: Aldini, A., Gorrieri, R., Martinelli, F. (eds.) FOSAD 2005. LNCS, vol. 3655, pp. 237–272. Springer, Heidelberg (2005)
Gligor, V.D., Gavrila, S.I., Ferraiolo, D.: On the formal definition of separation-of-duty policies and their composition. In: Proc. of Symp. on Sec. and Privacy, pp. 172–183. IEEE Press, Los Alamitos (1998)
He, Q., Antón, A.I.: A Framework for Modeling Privacy Requirements in Role Engineering. In: Proc. of REFSQ 2003, pp. 137–146 (2003)
House of Lords. Prince Jefri Bolkiah vs KPMG. 1 All ER 517 (1999)
Hu, H., Ahn, G.: Enabling verification and conformance testing for access control model. In: Proc. of SACMAT 2008, pp. 195–204. ACM Press, New York (2008)
Jajodia, S., Samarati, P., Sapino, M.L., Subrahmanian, V.S.: Flexible support for multiple access control policies. TODS 26(2), 214–260 (2001)
Jürjens, J.: Secure Systems Development with UML. Springer, Heidelberg (2004)
Kang, M.H., Park, J.S., Froscher, J.N.: Access control mechanisms for inter-organizational workflow. In: Proc. of SACMAT 2001, pp. 66–74. ACM Press, New York (2001)
Leone, N., Pfeifer, G., Faber, W., Eiter, T., Gottlob, G., Perri, S., Scarcello, F.: The DLV System for Knowledge Representation and Reasoning. TOCL 7(3), 499–562 (2006)
Li, N., Mitchell, J.C.: RT: A Role-based Trust-management Framework. In: Proc. of DISCEX 2003, vol. 1, pp. 201–212. IEEE Press, Los Alamitos (2003)
Liu, L., Yu, E.S.K., Mylopoulos, J.: Security and Privacy Requirements Analysis within a Social Setting. In: Proc. of RE 2003, pp. 151–161. IEEE Press, Los Alamitos (2003)
Massacci, F., Mylopoulos, J., Zannone, N.: Computer-Aided Support for Secure Tropos. ASE 14(3), 341–364 (2007)
Massacci, F., Mylopoulos, J., Zannone, N.: An Ontology for Secure Socio-Technical Systems. In: Handbook of Ontologies for Business Interaction, ch. XI, p. 188. The IDEA Group (2008)
Massacci, F., Zannone, N.: Detecting Conflicts between Functional and Security Requirements with Secure Tropos: John Rusnak and the Allied Irish Bank. In: Social Modeling for Requirements Engineering. MIT Press, Cambridge (to appear, 2008)
Mellado, D., Fernández-Medina, E., Piattini, M.: Applying a Security Requirements Engineering Process. In: Gollmann, D., Meier, J., Sabelfeld, A. (eds.) ESORICS 2006. LNCS, vol. 4189, pp. 192–206. Springer, Heidelberg (2006)
OASIS. eXtensible Access Control Markup Language (XACML) Version 2.0. OASIS Standard (2005)
Promontory Financial Group, Wachtell, Lipton, Rosen, and Katz. Report to the Board and Directors of Allied Irish Bank P.L.C., Allfirst Financial Inc., and Allfirst Bank Concerning Currency Trading Losses (March 12, 2003)
Ray, I., Li, N., France, R., Kim, D.-K.: Using UML to visualize role-based access control constraints. In: Proc. of SACMAT 2004, pp. 115–124. ACM Press, New York (2004)
Room, S.: Data Protection & Compliance in Context. BCS (2007)
Saltzer, J.H., Schroeder, M.D.: The Protection of Information in Computer Systems. Proceedings of the IEEE 63(9), 1278–1308 (1975)
Samarati, P., di Vimercati, S.D.C.: Access Control: Policies, Models, and Mechanisms. In: Focardi, R., Gorrieri, R. (eds.) FOSAD 2001. LNCS, vol. 2946, pp. 137–196. Springer, Heidelberg (2004)
Sandhu, R.S., Coyne, E.J., Feinstein, H.L., Youman, C.E.: Role-Based Access Control Models. IEEE Comp. 29(2), 38–47 (1996)
Schaad, A., Lotz, V., Sohr, K.: A model-checking approach to analysing organisational controls in a loan origination process. In: Proc. of SACMAT 2006, pp. 139–149. ACM Press, New York (2006)
Simon, R., Zurko, M.E.: Separation of duty in role-based environments. In: Proc. of CSFW 1997, pp. 183–194. IEEE Press, Los Alamitos (1997)
Sohr, K., Drouineaud, M., Ahn, G.-J., Gogolla, M.: Analyzing and managing role-based access control policies. TKDE 20(7), 924–939 (2008)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2008 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Massacci, F., Zannone, N. (2008). A Model-Driven Approach for the Specification and Analysis of Access Control Policies. In: Meersman, R., Tari, Z. (eds) On the Move to Meaningful Internet Systems: OTM 2008. OTM 2008. Lecture Notes in Computer Science, vol 5332. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-540-88873-4_11
Download citation
DOI: https://doi.org/10.1007/978-3-540-88873-4_11
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-88872-7
Online ISBN: 978-3-540-88873-4
eBook Packages: Computer ScienceComputer Science (R0)