Abstract
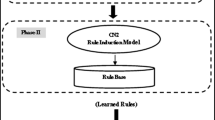
The inhuman cause of behavior in computer users, lack of coding skills pursue a malfunctioning of applications creating security breaches and vulnerable to every use of online transaction today. The anomaly detection is in-sighted into security of information in early stage of 1980, but still we have potential abnormalities in real time critical applications and unable to model online, real world behavior. The anomalies are pinpointed by conventional algorithms was very poor and false positive rate (FPR) is increased. So, in this context better use the adorned machine learning techniques to improve the performance of an anomaly detection system (ADS). In this paper we have given a new classifier called rule based decision tree (RBDT), it is a cascading of C4.5 and Naïve Bayes use the conjunction of C4.5 and Naïve Bayes rules towards a new machine learning classifier to ensure that to improve in results. Here two case studies used in experimental work, one taken from UCI machine learning repository and other one is real bank dataset, finally comparison analysis is given by applying datasets to the decision trees ( ID3, CHAID, C4.5, Improved C4.5, C4.5 Rule), Neural Networks, Naïve Bayes and RBDT.
Access provided by Autonomous University of Puebla. Download to read the full chapter text
Chapter PDF
Similar content being viewed by others
References
Denning, D.E.: An intrusion detection model. IEEE Transactions on Software Engineering (1987)
Axelsson, S.: Intrusion Detection Systems: A Survey and Taxonomy, Chalmers University. Technical Report 99-15 (March 2000)
Feng, H.H., Kolesnikov, O.M., Fogla, P., Lee, W., Gong, W.: Anomaly Detection Using Call Stack Information. In: IEEE Symposium on Security and Privacy 2003, CA, Issue Date: May 11-14, pp. 62–75 (2003) ISSN: 1081-6011 Print ISBN
Lee, W., Stolfo, S.J.: Data mining approaches for intrusion detection. In: 7th USENIX Security Symposium, Berkeley, CA, USA, pp. 79–94 (1998)
Lane, T., Brodley, C.E.: An Application of Machine Learning to Anomaly Detection. In: Proceedings of the 20th National Information Systems Security Conference, pp. 366–377 (October 1997)
Breiman, L.: Random Forests. Machine Learning 45, 5–32 (2001)
Jidiga, G.R., Sammulal, P.: Foundations of Intrusion Detection Systems: Focus on Role of Anomaly Detection using Machine Learning. In: ICACM - 2013 Elsevier 2nd International Conference (August 2013) ISBN No: 9789351071495
Jidiga, G.R., Sammulal, P.: The Need of Awareness in Cyber Security with a Case Study. In: Proceedings of the 4th IEEE Conference (ICCCNT), Thiruchengode, TN, India, July 4-6 (2013)
Kass, G.V.: An Exploratory Technique for Investigating Large Quantities of Categorical Data. Applied Statistics 29(2), 119–127 (1980)
Quinlan, J.R.: Induction of decision trees, Machine Learning 1, pp. 81–106. Kluwer Publishers (1986)
Quinlan, J.R.: Simplifying decision trees. International Journal of Man Machine Studies 27, 221–234 (1987)
Quinlan, J.R.: Decision Trees and Multivalued Attributes. In: Richards, J. (ed.) Machine Intelligence, vol. 11, pp. 305–318. Oxford Univ. Press, Oxford (1988)
Quinlan, J.R.: Unknown attribute values in induction. In: Proceedings of the Sixth International Machine Learning Workshop Cornell. Morgan Kaufmann, New York (1989)
Quinlan, J.R.: C4.5: Programs for Machine Learning. Morgan Kaufmann, Los Altos (1993)
Quinlan, J.R., Rivest, R.L.: Inferring Decision Trees Using The Minimum Description Length Principle. Information and Computation 80, 227–248 (1989)
Breiman, L., Friedman, J., Olshen, R., Stone, C.: Classification and Regression Trees. Wadsworth Int. Group (1984)
Russell, S., Norvig, P.: Artificial Intelligence: A Modern Approach, 3rd edn. Prentice-Hall (2009)
Polat, K., Güne, S.: A novel hybrid intelligent method based on C4. 5 decision tree classifier and one against all approach for multi-class classification problems. Expert Systems with Applications 36, 1587–1592 (2009)
Jiang, S., Yu, W.: A Combination Classification Algorithm Based on Outlier Detection and C4. 5. Springer Publications (2009)
Cohen, W.W.: Fast effective rule induction. In: Proceedings of the Twelfth International Conference on Machine Learning Chambery, France, pp. 115–123 (1993)
Yu, M., Ai, T.H.: Study of RS data classification based on rough sets and C4. 5 algorithms. In: Proceedings of the Society of Photo-Optical Instrumentation Engineers (SPIE) Conference Series (2009)
Yang, X.Y.: Decision tree induction with constrained number of leaf node. Master’s Thesis, National Central University (NCU-T), Taiwan (2009)
Michael, J.A., Gordon, S.L.: Data mining technique for marketing, sales and customer support. Wiley, New York (1997)
Loh, W.Y., Shih, Y.S.: Split selection methods for classification trees. Statistica Sinica 7, 815–840 (1997)
Clark, P., Niblett, T.: The CN2 induction algorithm. Machine Learning 3, 261–283 (1989)
Clark, P., Boswell, R.: Rule induction with CN2: Some recent improvements. In: Kodratoff, Y. (ed.) EWSL 1991. LNCS, vol. 482, Springer, Heidelberg (1991)
Rakotomalala, R., Lallich, S.: Handling noise with generalized entropy of type beta in induction graphs algorithm. In: Proceedings of International Conference on Computer Science and Informatics, pp. 25–27 (1998)
Chauchat, J.H., Rakotomalala, R., Carloz, M., Pelletier, C.: Targeting customer groups using gain and cost matrix: a marketing application. In: Proceedings of Data Mining for Marketing Applications Workshop (PKDD), pp. 1–13 (2001)
Rakotomalala, R., Lallich, S., Di Palma, S.: Studying the behavior of generalized entropy in induction trees using a m-of-n concept. In: Żytkow, J.M., Rauch, J. (eds.) PKDD 1999. LNCS (LNAI), vol. 1704, pp. 510–517. Springer, Heidelberg (1999)
Rajeswari, P., Kannan, A.: An active rule approach for network intrusion detection with enhanced C4.5 Algorithm. International Journal of Communications Network and System Sciences, 285–385 (2008)
Ghosh, A., Schwartzbard, A.: A study using NN for anomaly detection and misuse detection. Reliable Software Technologies, http://www.docshow.net/ids/useni
Benferhat, A.S., Elouedi, Z.: Naive Bayes vs Decision Trees in Intrusion Detection Systems. In: Proc. ACM Symp. Applied Computing (SAC 2004), pp. 420–424 (2004)
Rokach, L., Maimon, O.: Decision Trees
Bache, K., Lichman, M.: UCI Machine Learning Repository. University of California, School of Information and Computer Science, CA (2013), http://archive.ics.uci.edu/ml
Usta, I., Kantar, Y.M.: Mean-Variance-Skewness-Entropy Measures: A Multi-Objective Approach for Portfolio Selection. Entropy 13, 117–133 (2011), doi:10.3390/e13010117
Abdelhalim, A., Traore, I.: Converting Declarative Rules into Decision Trees. In: Proceedings of the World Congress on Engineering and Computer Science, Vol-I WCECS 2009, San Francisco, USA, October 20-22 (2009)
Abdelhalim, A.: Issa Traore, The RBDT-1 method for rule-based decision tree generation. Technical report (ECE-09-1), University of Victoria, STN CSC, Victoria, BC, Canada (July 2009)
Siva, S., Sindhu, S., Geetha, S., Kannan, A.: Decision tree based light weight intrusion detection using a wrapper approach. Elsevier-Expert Systems with Applications 39, 129–141 (2011), doi:10.1016/j.eswa.2011.06.013
Lowd, D., Davis, J.: Improving Markov Network Structure Learning Using Decision Trees. Journal of Machine Learning Research 15, 501–532 (2014)
Zaidi, N.A., Cerquides, J., Carman, M.J.: Alleviating Naive Bayes Attribute Independence Assumption by Attribute Weighting. Journal of Machine Learning Research 14 (2013)
Anchiang, D., Chen, W., Fanwang, Y., Jinnhwang, A.: Rules Generation from the Decision Tree. Journal of Information Science and Engineering 17, 325–339 (2001)
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2015 Springer International Publishing Switzerland
About this paper
Cite this paper
Jidiga, G.R., Sammulal, P. (2015). RBDT: The Cascading of Machine Learning Classifiers for Anomaly Detection with Case Study of Two Datasets. In: El-Alfy, ES., Thampi, S., Takagi, H., Piramuthu, S., Hanne, T. (eds) Advances in Intelligent Informatics. Advances in Intelligent Systems and Computing, vol 320. Springer, Cham. https://doi.org/10.1007/978-3-319-11218-3_29
Download citation
DOI: https://doi.org/10.1007/978-3-319-11218-3_29
Publisher Name: Springer, Cham
Print ISBN: 978-3-319-11217-6
Online ISBN: 978-3-319-11218-3
eBook Packages: EngineeringEngineering (R0)