Abstract
In the Industry 4.0 paradigm, the cybersecurity is a key aim to obtain high levels of performance of the industries based on the use of the IoT technology and the Big Data analysis. To achieve this objective, the cyberphysical industrial plants must be equipped with cybersecurity systems for early detection and location of cyberattacks. This paper presents a robust approach of an industrial cybersecurity system by using non-standard Pythagorean membership grades. The proposed scheme was validated using the Two-Tanks benchmark with excellent results. The proposal was compared with other computational intelligence tools recently presented in the scientific literature, and the results showed the best performance of the proposed scheme.
Access provided by Autonomous University of Puebla. Download conference paper PDF
Similar content being viewed by others
Keywords
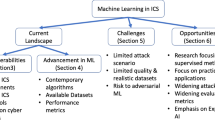
1 Introduction
At present, terms such as Smart Factory and Industry 4.0 are closely related to the automation of industrial plants characterized by increasingly connected physical systems and a stronger integration of digital technologies [4, 8]. This higher level of integration allows higher levels of productivity, more competitive final products, and excellent compliance of the industrial safety standards. However, despite these significant commercial benefits, the safety risk of these cyberindustrial environments is also increased. Therefore, there is an urgent need for increasing the cybersecurity in industrial processes [1, 2].
A major quality of the use of fuzzy sets is the insertion of membership degrees. With the aim of improving the ability of fuzzy sets to capture and model membership information, several researchers have begun to use non-standard fuzzy sets such as the intuitionistic [3], that allow to insert imprecision and uncertainty in the specification of the membership degrees.
The Pythagorean Fuzzy Sets (PFS) were presented in [10], where it is demonstrated that the space of Pythagorean membership degrees is larger than the space of intuitionistic membership degrees. This represents an important advantage in condition monitoring because it allows the insertion of uncertainty in the specification of membership degrees as result of noisy measurements.
The aim of this paper and its main contribution is to propose a cybersecurity scheme with a high performance in the detection and location of cyberattacks and with a robust behaviour versus noisy observations obtained from an industrial plant. The proposal is based on the modification of the Kernel Fuzzy C-Means algorithm by using the non standard Pythagorean membership grades. The modified algorithm, called Kernel Pythagorean Fuzzy C-Mean algorithm (KPyFCM), significantly reduces classification errors in the attack detection and location even in the presence of noisy observations. On the other hand, a performance comparison is developed with successful algorithms used in different applications [6, 12].
2 Materials and Methods
2.1 Main Characteristics of Pythagorean Fuzzy Sets
In [10], the PFS were introduced. The Pythagorean Membership Grades (PMG) associated with them are expressed as follow:
-
Two values, r(z) and d(z), are assigned for each \(z \in Z\).
-
If \(r(z)\, \in \,[0,1]\), it is labeled strength of commitment at z
-
If \(d(z)\, \in \, [0,1]\), it is labeled direction of commitment at z.
-
\(\mathcal {H}_{Y}(z)\) is a membership grade which indicates the support for membership of z in \(\mathcal {H}\).
-
\(\mathcal {H}_{N}(z)\) is a membership grade which indicates the support against membership of z in \(\mathcal {H}\).
-
\(\mathcal {H}_{Y}(z)\) and \(\mathcal {H}_{N}(z)\) are defined as
$$\begin{aligned} \mathcal {H}_{Y}(z) = r(z)cos(\varphi (z)) \end{aligned}$$(1)$$\begin{aligned} \mathcal {H}_{N}(z) = r(z)sin(\varphi (z)) \end{aligned}$$(2)where
$$\begin{aligned} \varphi (z) = (1-d(z))\frac{\pi }{2} \end{aligned}$$(3)and \(\varphi (z)\in [0, \frac{\pi }{2}]\) is expressed in radians.
Lemma:
\(\mathcal {H}_{Y}\)(z) and \(\mathcal {H}_{N}\)(z) are Pythagorean complements with respect to r(z)
Proof:
See [11]
In general, a PMG is formalized by using a pair of values (e, f) such that \(e,f \in [0,1]\) and \(e^{2}\) + \(f^{2}\) \(\le \) 1.
Intuitionistic membership grades are also represented by a pair (e, f) which satisfies \(e,f \in [0,1]\) and \(e + f \le 1\) [3].
Theorem:
The set of Pythagorean Membership Grades is greater than the set of intuitionistics membership grades
Proof:
See [11]
This result indicates the possibility of using PFS in more situations than intuitionistics fuzzy sets. For cybersecurity systems this characteristic of the PFS is very important for improving their performance.
2.2 Kernel Pythagorean Fuzzy C-Means Algorithm
Using the PFS theory, the objective function of the Pythagorean FCM (PyFCM) algorithm can be obtained in the similar form to the Intuitionistic Fuzzy C-Means algorithm (IFCM) [3] according to the equation
where \(m > 1\) is the fuzziness regulation factor of the partition [9], l is the quantity of classes, N is the quantity of observations.
\(u_{ik}^{*} = u_{ik}^{m} + \pi _{ik}\). \(u_{ik}^{*}\) represents the pythagorean fuzzy membership, \(u_{ik}\) denotes the typical fuzzy membership of the kth observation in the ith class, and \(\pi _{ik}\) is the hesitation degree, formalized as:
and
Kernel functions permit to map non-linear observation of the input space into a higher-dimensional space. This is very useful in classification tasks because allow for greater separability among classes. With this aim, the Kernel Pythagorean Fuzzy C Mean algorithm (KPyFCM) is designed. In this algorithm, the following objective function is minimized:
where, \(\left\| \mathbf {\Psi (z_{k})}-\mathbf {\Psi (q_{i})}\right\| ^{2}\) denotes the square of the distance between \(\mathbf {\Psi (z_{k})}\) and \(\mathbf {\Psi (q_{i})}\). In the feature space, the distance is computed by using the kernel function as follows:
There exist many kernel functions and the choice of the most appropriate depends on the application [5]. Nonetheless, the most used is the Gaussian Kernel function (GKF).
If the GKF is used, then \(\mathbf {K(z,z) = 1}\) and \(\left\| \mathbf {\Psi (z_{k})}-\mathbf {\Psi (q_{i})}\right\| ^{2} = \mathbf {2\left( 1-K(z_{k},q_{i})\right) }\). So, Eq. (7) can be expressed as:
where,
where \(\delta \) is the bandwidth which indicates the smoothness degree of the GKF [9]. Minimizing Eq. (9), yields:
KPyFCM algorithm is displayed in Algorithm 1.

2.3 Proposal of Scheme for Detection and Localization of Cyberattacks
The proposal of scheme for Detection and Location of Cyberattacks is shown in Fig. 1. It is formed for two phases: a training phase executed offline and a recognition phase developed online. In the first phase, the data obtained from the process allow to train offline the Cyberattack Detection and Location (CADL) algorithm. After training, the CADL algorithm is used online to analyze each new observation taken from the process. Training is the most important stage, since the center of the different classes that represent the process operation states are determined (normal operation class and the classes that represent the different cyberattacks).
Offline Training Stage. In this stage, the CADL system is trained with a set of historical data which contain the necessary information of each known operating state or class of the industrial plant (normal operation condition (NOC) and states of attack). The main aim of the training process is to determine the center of the known classes \(\textbf{Q}=\left\{ \textbf{q}_{1},\textbf{q}_{2},...,\textbf{q}_{c}\right\} \) to be used in the on-line recognition stage.
On-Line Recognition Stage. In this stage, each observation (\(O_k\)) obtained from the process is assigned to a known class based on the distance between the observation and the centers of the different classes. Subsequently, the membership degree of the observation k for each class is obtained. The observation is assigned to the class with the highest membership degree such as is showed in Eq. (13). (See Algorithm ).

2.4 Case Study: Two-Tanks
The test system consists of two tanks (\(T_1, T_2\)) interconnected through a pipe with a valve \(V_{b}\) which is actuated by an ON-OFF controller (see Fig. 2) [7]. Tank \(T_{1}\) is fed by the pump \(P_{1}\) controlled by a proportional integral (PI) controller. Tank \(T_{2}\), is equipped with the manual outlet valve \(V_{0}\). The variables of the process are: Inflow to \(T_{1}\) (\(Q_{p}\)), Water level in \(T_{1}\) (\(h_{1}\)), Water level in \(T_{2}\) (\(h_2\)), Pump control signal on \(T_{1}\) (\(U_{p}\), Outflow to consumers (\(Q_{0}\)), Outflow at \(T_{1}\) (\(Q_{f1}\)) and Outflow at \(T_{2}\) (\(Q_{f2}\)).
In dependence of the type of cyberattack, different scenarios can be obtained. In this paper, the following five scenarios were simulated:
-
Scenario 1 (NOC): Normal Operation Condition.
-
Scenario 2 (A1): Scenario corresponding to Attack 1 due to a water leak in Tank 1 (\(T_{1}\)) at a constant flow \(Q_{f1}\) = \(10^{-4}\) \(m^{3}\)/s in the period of time from t = 40 s to t = 80 s.
-
Scenario 3 (A2): Short-term water theft from \(T_{1}\) with hidden signal added to the \(h_{1}^{m}\) level measurement (Deception attack). The attacker extracts a constant flow \(Q_{f1}\) = \(10^{-4}\) \(m^{3}\)/s through the pump between t = 40 s and 80 s. In this period of time a signal is added to the level sensor output at \(T_{1}\) to hide the theft. For the PI controller the level at \(T_{1}\) seems to remain constant and its output does not change.
-
Scenario 4 (A3): This scenario corresponds to Attack 3 due to a water leak in Tank 2 (\(T_{2}\)) at a constant flow \(Q_{f2}\) = \(10^{-4}\) \(m^{3}\)/s in the time period \(t=40\,\text {s}\, - \, t=80\,\text {s}\).
-
Scenario 5 (A4): The attacker steals water when the system has reached the steady state. Before doing so, the attacker saves several measurements of the level sensors before the water is stolen from the tanks. In the attack phase, the attacker steals water and replacing the real data with the saved ones (Replay attack). Specifically, water is stolen in the period of time between t = 100 s and t = 200 s and the controller is fooled by using the measurements saved in the 50 s prior to the attack.
2.5 Design of Experiments
For building the training database, simulations were carried out to obtain 160 observations of each class (NOC and Attacks). For validating the behavior of the CADL system in the online stage were used another set of 40 observations of each class. Figures 3 and 4 shows a comparison between the water levels in the tanks with scenario 1 (NOC) and the different attacks scenarios (2, 3, 4 and 5). The values of the parameters used in the KPyFCM algorithm were: \(\epsilon \) = \(10^{-5}\), m = 2, \(\sigma \) = 10. The value of \(\sigma \) was selected after the development of 10 experiments (\(\sigma \) = 10,20,30,40,...,100). Three experiments were developed to evaluate the robustness of the cyberattack detection and location system against noise:
-
1.
Without noise in the measurements.
-
2.
Measurements with 2% of noise level.
-
3.
Measurements With 5% of noise level.
3 Analysis and Discussion of Results
For the performance analysis of the proposed CADL system the Confusion Matrix (CM) was used. The values \(CM_{rs}\) for \( r \ne s\) in the CM show the number of observations of the operation mode r that the CADL system misclassifies in the operation modes.
Table 1 shows the CM (without noise in the measurements) where NOC: Normal Operation Condition, A1: Attack 1, A2: Attack 2, A3: Attack 3 and A4: Attack 4. The main diagonal presents the number of observations successfully classified. The accuracy TA for each class was computed as TA = correctly classified observations of the class/total observations of the class. The last row shows the average (AVE) of TA. Figure 5 show the classification results for the different scenarios by using the proposed CADL system for Two-Tank benchmark.
3.1 Comparison with Other Algorithms
For improving the classification process, the Density-Based Weighted FCM (DBFCM) algorithm [6], the Maximum-Entropy-Regularized Weighted FCM (EWFCM) algorithm [12], and the Kernel based EWFCM (KEWFCM) algorithm [12], all of them with excellent performance in different applications, have been presented in the scientific literature. Follow a comparison with these algorithms.
Density-Based Weighted Fuzzy C-Means Algorithm. In this algorithm, the weight of an object is decided by the density of the objects around this object. There are two stages of the density-based weighted FCM. The first stage is designed to calculate the weights of every object, the second stage is the clustering stage.
Maximum-Entropy-Regularized Weighted Fuzzy C-Means and Kernel Maximum-Entropy-Regularized Weighted Fuzzy C-Means Algorithms. A maximum-entropy-regularized weighted fuzzy c-means (EWFCM) algorithm is proposed to extract the important features and improve the clustering. In EWFCM algorithm, the attribute-weight entropy regularization is defined in the new objective function to achieve the optimal distribution of the attribute weights. The kernel based EWFCM (KEWFCM) clustering algorithm is developed for clustering the data with non-spherical shaped clusters.
Table 2 show the results of the CM (without noise) corresponding to the algorithms used in the comparison.
Figure 6 shows the classification results by using the mentioned algorithms and the KPyFCM algorithm for the observations without noise, with 2% and 5% of noise level.
All experiments were performed on a computer with the following characteristics: Intel Core i7-6600U 2.6–2.81 GHz, memory RAM: 16 GB. The average computational time of each algorithm to perform an execution was: DBFCM (0.5520 s), EWFCM (0.4962 s), KEWFCM (0.6315 s), and KPyFCM (0.6035 s). When comparing these times with the time constant of the process, it can be seen that they are very small and, therefore, show the feasibility of their application to the proposed scheme.
The Friedman was applied, and its results confirmed that at least, the performance of one algorithm is significantly different to the performances of the other algorithms.
The Wilcoxon test was applied to compare the algorithms in pairs where 1: DBWFCM, 2: EWFCM, 3: KEWFCM, 4: KPyFCM. Table 3 displays the results. The first row contains the values of the sum of the positive rank (\(R^{+}\)) and the second row presents the sum of the negative rank (\(R^{-}\)) for each comparison. The third row shows the statistical values T, and the fourth row, the critical value of T for a significance level \(\alpha =0.05\). The last row displays number the winner algorithm in each comparison. Table 4 shows the times that each algorithm was the winner. This results demonstrate the proper performance of the CADL scheme proposed.
4 Conclusions
To achieve the successful implementation of the Industry 4.0 paradigm in industrial plants, cybersecurity must be guaranteed. In this paper, an attack detection and location system with a high performance and robustness versus noisy measurements was presented. The CADL system was implemented by using a KPyFCM algorithm which significantly improves the performance in the detection and location process based on two key characteristics of the elements that make it up. The first is related with the fact that the Pythagorean membership grades permit to use a larger set of numeric values for assigning the membership degree to an observation than the standard and intuitionistic membership grades. The second is related with use of kernel functions which allow to achieve greater separability among the classes. The high performance of the proposal of CADL scheme was confirmed using the Two-Tank process benchmark. The results obtained by the proposed CADL system were compared with the results of three algorithms of high performance recently presented in the scientific literature demonstrating the superiority of the proposal for detection and location of cyberattacks. For future research, an interesting idea will be designing a monitoring scheme that integrally addresses fault diagnosis and cyberattacks in industrial plants.
References
Alanazi, M., Mahmood, A., Morshed, M.: Scada vulnerabilities and attacks: a review of the state of the art and open issues. Comput. Secur. 125, 1–29 (2023)
Alladi, T., Chamola, V., Zeadally, S.: Industrial control systems: cyberattack trends and countermeasures. Comput. Commun. 155, 1–8 (2020)
Atanassov, K.: On Intuitionistic Fuzzy Sets Theory. Springer, Heidelberg (2012). https://doi.org/10.1007/978-3-642-29127-2
Bashendy, M., Tantawy, A., Erradi, A.: Intrusion response systems for cyber-physical systems: a comprehensive survey. Comput. Secur. 124, 1–27 (2023)
Bernal de Lázaro, J., Cruz Corona, C., Silva Neto, A., Llanes-Santiago, O.: Criteria for optimizing kernel methods in fault monitoring process: a survey. ISA Trans. 127, 259–272 (2022)
Li, Y., Yang, G., He, H., Jiao, L., Shang, R.: A study of large-scale data clustering based on fuzzy clustering. Soft Comput. 20, 3231–3242 (2016)
Quevedo, J., Sánchez, H., Rotondo, D., Escobet, T., Puig, V.: A two-tank benchmark for detection and isolation of cyber-attacks. IFAC Paper OnLIne 51, 770–775 (2018)
Rodríguez-Ramos, A., Bernal-de Lázaro, J., Prieto-Moreno, A., Silva Neto, A., Llanes-Santiago, O.: An approach to robust fault diagnosis in mechanical systems using computational intelligence. J. Intell. Manuf. 30, 1601–1615 (2019)
Rodríguez-Ramos, A., Silva-Neto, A.J., Llanes-Santiago, O.: An approach to fault diagnosis with online detection of novel faults using fuzzy clustering tools. Expert Syst. Appl. 113, 200–212 (2018)
Yager, R.R.: Pythagorean membership grades in multicriteria decision making. IEEE Trans. Fuzzy Syst. 22, 958–965 (2014)
Yager, R.R.: Properties and applications of Pythagorean fuzzy sets. In: Angelov, P., Sotirov, S. (eds.) Imprecision and Uncertainty in Information Representation and Processing. SFSC, vol. 332, pp. 119–136. Springer, Cham (2016). https://doi.org/10.1007/978-3-319-26302-1_9
Zhou, J., Chen, L., Chen, C.P., Zhang, Y., Li, H.: Fuzzy clustering with the entropy of attribute weights. Neurocomputing 198, 125–134 (2016)
Acknowledgements
The authors acknowledge the financial support provided by FAPERJ, Fundacão Carlos Chagas Filho de Amparo à Pesquisa do Estado do Rio de Janeiro; CNPq, Consehlo Nacional de Desenvolvimento Científico e Tecnológico; CAPES, Coordenação de Aperfeiçoamento de Pessoal de Nível Superior, research supporting agencies from Brazil and the project PN223LH004-23 from the Science and Technology National Program in Automation, Robotic and Artificial Intelligence (ARIA) of the Ministry of Science, Technology and Environment (CITMA) of Cuba.
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2024 The Author(s), under exclusive license to Springer Nature Switzerland AG
About this paper
Cite this paper
Rodríguez-Ramos, A., Irigoyen, E., da Silva Neto, A.J., Llanes-Santiago, O. (2024). A New Proposal for Detection and Location of Cyberattacks in Industrial Processes. In: Hernández Heredia, Y., Milián Núñez, V., Ruiz Shulcloper, J. (eds) Progress in Artificial Intelligence and Pattern Recognition. IWAIPR 2023. Lecture Notes in Computer Science, vol 14335. Springer, Cham. https://doi.org/10.1007/978-3-031-49552-6_9
Download citation
DOI: https://doi.org/10.1007/978-3-031-49552-6_9
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-031-49551-9
Online ISBN: 978-3-031-49552-6
eBook Packages: Computer ScienceComputer Science (R0)