Abstract
In this work, we study the security of sponge-based authenticated encryption schemes against quantum attackers. In particular, we analyse the sponge-based authenticated encryption scheme \({ \textsc {Slae}}\) as put forward by Degabriele et al. (ASIACRYPT’19) due to its modularity. We show that the scheme achieves security in the post-quantum (QS1) setting in the quantum random oracle model by using the one-way to hiding lemma. Furthermore, we analyse the scheme in a fully-quantum (QS2) setting. There we provide a set of attacks showing that \({ \textsc {Slae}}\) does not achieve ciphertext indistinguishability and hence overall does not provide the desired level of security.
Access provided by Autonomous University of Puebla. Download conference paper PDF
Similar content being viewed by others
1 Introduction
Authenticated encryption schemes with associated data (AEAD) [47] are the main employed cryptographic scheme when it comes to securing the communication between two parties who already share a secret key by ensuring both confidentiality and authenticity of the exchanged messages. Several works show that AEAD schemes can be constructed purely from sponges [21,22,23,24, 35], which were initially introduced as a tool to construct cryptographic hash functions. Recent examples of such sponge-based AEAD schemes are \({ \textsc {Isap}}\) [22, 23] and \({ \textsc {Slae}}\) [21]. Observe that these schemes are already analysed showing that they are even secure against side-channel leakage, however, their security against quantum adversaries has yet to be studied.
Unlike public key cryptography that is based on number theoretic problems, which is completely broken by Shor’s algorithm [49], AEAD schemes are often assumed to be only mildly affected by Grover’s algorithm [31], although this assumption turns out to be delusive in some cases [13]. To compensate this, usually one simply doubles the key length. This approach indeed works for many symmetric schemes in the standard model, namely those where their security proofs can be easily translated to one against quantum adversaries [50]. However, schemes that rely on random oracles [7] cannot be translated in a straightforward manner and hence require more attention. In particular, translating their security to hold against quantum adversaries requires a proof in the quantum random oracle model (QROM) [10], and it has recently been shown that proofs cannot always be translated from the ROM to the QROM [56]. In particular, this will also apply to sponge-based AEAD schemes where we typically model the block function that underlies the sponge construction as a random oracle and includes the schemes in [21,22,23].
The security of cryptographic primitives against quantum adversaries can nowadays be divided into two cases [27, 37]. The first case corresponds to the setting of post-quantum security (usually abbreviated as QS1) where the adversary only has quantum computing power. This setting covers the scenario once the first large-scale quantum computer exists and corresponds to the setting described above which typically requires switching from the ROM to the QROM. The second case deals with the setting of quantum security (usually referred to as QS2) where protocol participants also have quantum computing power. This covers a scenario where quantum computers are ubiquitous but also earlier scenarios using more sophisticated attacks such as the frozen smart-card attack [28].
Observe that security in the QS2 setting is more involved since the adversary gets superposition access to the primitive, e.g., it can encrypt/sign messages in a superposition. Many schemes that are secure in the QS1 setting are however completely broken in the QS2 setting as is shown by a series of works [2, 4, 33, 36, 41, 42, 48]. Yet another difficulty in the QS2 setting is that there are many different security notions [1, 12, 14, 15, 25, 28,29,30, 43]. These notions use different approaches to formalise the idea of allowing the adversary to “encrypt/sign messages in a superposition” in order to obtain a security notion that translates the classical intuition of the corresponding security notion to the QS2 setting.
Our Contribution. In this work, we study the security of sponge-based authenticated encryption schemes against quantum attackers which has so far only received very little attention. In particular, we scrutinize the scheme \({ \textsc {Slae}}\) as put forward by Degabriele et al. [21] in both settings, namely in the QS1 and QS2 setting. Observe that the beauty of \({ \textsc {Slae}}\) is its simplicity in terms of their construction, i.e., \({ \textsc {Slae}}\) is a N2-composition [44] of a symmetric key encryption scheme and a message authentication code. In particular, Degabriele et al. show that \({ \textsc {Slae}}\) can be viewed in terms of smaller components (with slight improvements by [39]), i.e., the encryption scheme consists of a sponge-based pseudorandom function (PRF) and a sponge-based pseudorandom generator (PRG) while the MAC consists of the combination of a sponge-based hash function and a sponge-based PRF (a more detailed description can be found in Sect. 3). Note that our analysis does not only contribute towards the study of \({ \textsc {Slae}}\) but rather also provides a QS1 and QS2 analysis of the core primitives themselves which is of independent interest. Note that \({ \textsc {Slae}}\) is a leakage-resilient AEAD scheme. However, in this work we do not consider the leakage setting but rather use the scheme \({ \textsc {Slae}}\) due to its simplicity in order to provide a thorough security analysis of sponge-based AEAD schemes and the employed core primitives in the QS1 and QS2 setting closing this gap in the literature.
In the QS1 setting, we are able to establish security for \({ \textsc {Slae}}\). In particular, by using the one-way to hiding lemma [3, 53], we can show that the underlying building blocks, namely the sponge-based PRF and PRG are secure with respect to quantum adversaries. For the sponge-based hash function, we show that we can leverage existing results [18] to the construction specifics of \({ \textsc {Slae}}\). Finally, being equipped with the established results, we can overall establish security of \({ \textsc {Slae}}\) in the QS1 setting.
In the QS2 setting, we analyse the ciphertext indistinguishability of \({ \textsc {Slae}}\). Unlike the QS1 setting, there are different notions for ciphertext indistinguishability in the QS2 setting which do not form a strict hierarchy. We consider the two strongest, incomparable notions by Gagliardoni et al. [28] and Mossayebi and Schack [43]. We extend these notions to the nonce-based setting and show that \({ \textsc {Slae}}\) achieves neither of these notions by showing attacks. Finally, we argue that one may establish QS2 security in the sense of [12] of the generic construction that underlies \({ \textsc {Slae}}\). However, the security when studying the sponge-based construction is left as an open problem.
As mentioned above, we chose to analyse \({ \textsc {Slae}}\) rather than other relevant sponge-based schemes due to its modularity. Since \({ \textsc {Slae}}\) is based on a random transformation, we can leverage techniques for the QROM, whereas other sponge-based primitives are typically based on a random permutation. Our results yield post-quantum secure pseudorandom functions, pseudorandom generators, and hash functions all constructed entirely from sponges. Since these are fundamental cryptographic building blocks our contribution is more than just a post-quantum security proof for an AEAD scheme and can be applied elsewhere. In particular, it provides a starting point for proving post-quantum security of more practical schemes.
Related Work. Sponges were introduced by Bertoni et al. [8] as a tool to construct cryptographic hash functions which resulted in the hash function SHA-3. Since then, sponges were shown to be a versatile tool allowing not only the construction of hash functions but also primitives including authenticated encryption schemes [21,22,23,24, 35].
Research in the realm of QS1 security of sponges mainly targets the security of hash functions. The first result addresses sponge-based hash functions based on random transformations or non-invertible random permutations [18]. The ultimate goal is a post-quantum proof for SHA-3 which is targeted both by Unruh [55]Footnote 1 and Czajkowski [16] using Zhandry’s compressed oracle technique [58]. Apart from that we are not aware of other works considering the QS1 security of sponge-based constructions.
In the QS2 setting, [20] studies the quantum indifferentiability of sponges and [19] analyses the quantum indistinguishability of sponge-based pseudorandom functions. The analysis in [19] uses keyed functions for the underlying block function which allow the adversary only classical access to these block functions while it has superposition access to the resulting pseudorandom function.
Soukharev et al. [51] study the generic composition paradigms for authenticated encryption in the QS2 setting according to the security notions put forth by Boneh and Zhandry [12]. However, their proof implicitly assumes that superposition queries by the adversary can be recorded which, at this point, was unclear how to do as was pointed out Chevalier et al. [15].
Structure of the Paper. In Sect. 2 and Appendix A, we provide the necessary notation and background. The general sponge construction and the particular instantiation \({ \textsc {Slae}}\) is provided in Sect. 3. In Sect. 4, we provide a security analysis in the QS1 setting while in Sect. 5, we provide an analysis in the QS2 setting. We conclude the paper in Sect. 6 and provide proof details in Appendices B and C.
2 Preliminaries
2.1 Notation
For any positive integer \(n \in \mathbb {N}\), we use [n] to denote the set \(\{1, \dots , n\}\). For any two bit strings x and y of length n, |x| denotes the size of x, \(x \parallel y\) denotes their concatenation and by \(x \cdot y = x_1y_1 \oplus x_2y_2 \oplus \dots \oplus x_ny_n\) we denote their inner product. Furthermore, for a positive integer \(k \le |x|\), we use the notation \(\left\lfloor x \right\rfloor _{k}\) to denote the string when truncated to its k least significant bits while \(\left\lceil x \right\rceil ^{k}\) denotes the string when truncated to its k most significant bits. We denote the set of bit strings of size n by \(\{0,1\}^{n} \), and we denote by \(\{0,1\}^{*} \) the set of all bit strings of finite length. By writing
 , we denote the process of sampling at random a value from a finite set \({\mathcal {X}} \) and assigning it to x. We simply denote by \(\textsf{par}(x)\) the parity of x. Furthermore, we denote by \({\mathcal {Y}}^{{\mathcal {X}}}\) the set of all functions from \({\mathcal {X}}\) to \({\mathcal {Y}}\). We assume familiarity with the basics of quantum computation such as bra-ket notion for quantum states, e.g., \(\mathinner {|{x}\rangle }\), Hadamard operators, and measurements. For an in-depth discussion we refer to [46].
, we denote the process of sampling at random a value from a finite set \({\mathcal {X}} \) and assigning it to x. We simply denote by \(\textsf{par}(x)\) the parity of x. Furthermore, we denote by \({\mathcal {Y}}^{{\mathcal {X}}}\) the set of all functions from \({\mathcal {X}}\) to \({\mathcal {Y}}\). We assume familiarity with the basics of quantum computation such as bra-ket notion for quantum states, e.g., \(\mathinner {|{x}\rangle }\), Hadamard operators, and measurements. For an in-depth discussion we refer to [46].
2.2 Definitions
Due to space restrictions, we provide basic definitions about authenticated encryption with associated data (AEAD) and message authentication codes (MAC) in Appendix A.
Pseudorandom Function. Next we define pseudorandom functions and their respective security.
Definition 1
Let \(\mathcal {F} :{\mathcal {K}} \times {\mathcal {X}} \rightarrow {\mathcal {Y}}\) be a deterministic function. We define the PRF advantage of an adversary \(\mathcal {A}\) against \(\mathcal {F}\) as

Pseudorandom Generator. Next we define a pseudorandom generator and its security. Observe that we specify a PRG with variable output length, where the length is specified as part of the input.
Definition 2
Let \(\mathcal {G} :\mathcal {S} \times \mathbb {N}\rightarrow \{0,1\}^{*} \) be a pseudorandom generator with associated seed space \(\mathcal {S}\) and let \(\ell \in \mathbb {N}\) define the PRG’s output length. We define the PRG advantage of an adversary \(\mathcal {A}\) against \(\mathcal {G}\) as

Hash Function. Hash functions are a versatile cryptographic primitive that are efficiently computable functions that compress bit strings of arbitrary length to bit strings of fixed length. Hash functions do enjoy a variety of security properties and next we define collision resistance over a domain \({\mathcal {X}} =\{0,1\}^{*} \).
Definition 3
Let \(\mathcal {H} :{\mathcal {X}} \rightarrow \{0,1\}^{w} \) be a hash function constructed from a random transformation \( \rho \). We define the collision-resistance advantage of an adversary \(\mathcal {A}\) against \(\mathcal {H}\) where the adversary has (quantum) oracle access to \( \rho \) as

Since we consider hash functions in the QS1 and QS2 setting in this work, we require two additional properties when arguing about the security of a hash function, namely collapsing hash functions and zero-preimage resistance.
The collapsing property of hash functions is due to Unruh [54], who observed that collision resistance is not sufficient to construct commitment schemes secure against quantum adversaries.Footnote 2 Intuitively, a hash function is collapsing if an adversary can not distinguish between a measurement of the output (the hash value) and a measurement of the input. In [52, Lemma 25], Unruh shows that collapsing hash functions are also collision resistant. We present the formal definition of collapsing security in Appendix A.3.
Zero-preimage resistance states that it is infeasible for the adversary to output an element from the function’s domain which evaluates to the zero string.
Definition 4
Let \(f^{ \rho } :\{0,1\}^{x} \rightarrow \{0,1\}^{y} \) be a function. We define the zero-preimage resistance advantage of an adversary \(\mathcal {A}\) against \(f^{ \rho }\) where the adversary has (quantum) oracle access to \( \rho \) as

Quantum Random Oracle Model and One-way to Hiding Lemma. The quantum random oracle model (QROM) was formalised by Boneh et al. [10] extending the random oracle model (ROM) [7] to the quantum setting. The QROM has become the de-facto standard for analysing primitives which rely on random oracles. Boneh et al. [10] gave a separation between the ROM and the QROM, yet under non-standard assumptions. Recently, Yamakawa and Zhandry [56] provided a separation under standard assumptions. More precisely, let \({\textsf{H}} :\{0,1\}^{ n } \rightarrow \{0,1\}^{ n } \),Footnote 3 then the QROM allows a quantum adversary access to the unitary \(U_{{\textsf{H}}}\) that does the following
We write \(\mathcal {A} ^{{\textsf{H}}}\) to denote that \(\mathcal {A}\) has oracle access to \({\textsf{H}}\) which means having access to an oracle performing the unitary above.
The one-way to hiding (O2H) lemma is a fundamental tool for proofs in the quantum random oracle model (QROM). It provides an upper bound on the distinguishing advantage of a quantum adversary between different random oracles when having superposition access to it. The first variant was given by Unruh [53]. Subsequently, variants achieving tighter bounds were given in [3, 9, 40], yet at the cost of a more restricted applicability.
Below we recall the O2H lemma by Unruh [53], albeit in the formulation put forth by Ambainis et al. [3].
Lemma 5
(One-way to hiding (O2H) [3]). Let \({\textsf{G}}\), \({\textsf{H}} :{\mathcal {X}} \rightarrow {\mathcal {Y}}\) be random functions, let z be a random bitstring, and let \({\mathcal {S}} \subset {\mathcal {X}}\) be a random set such that \(\forall x \notin {\mathcal {S}}\), \({\textsf{G}}(x) = {\textsf{H}}(x)\). \(({\textsf{G}},{\textsf{H}},{\mathcal {S}},z)\) may have arbitrary joint distribution. Furthermore, let \(\mathcal {A} ^{{\textsf{H}}}\) be a quantum oracle algorithm which queries \({\textsf{H}}\) at most \( q \) times. Define an oracle algorithm \(\mathcal {B} ^{{\textsf{H}}}\) as follows: Pick
 . Run \(\mathcal {A}_{ q } ^{{\textsf{H}}}(z)\) until just before its i-th query to \({\textsf{H}}\). Measure the query in the computational basis, and output the measurement outcome. Then it holds that
. Run \(\mathcal {A}_{ q } ^{{\textsf{H}}}(z)\) until just before its i-th query to \({\textsf{H}}\). Measure the query in the computational basis, and output the measurement outcome. Then it holds that
3 The Sponge Construction and Slae
In this section, we provide the basic syntax about the sponge construction. Being equipped with the required syntax, we review \({ \textsc {Slae}}\) which is a N2-based authenticated encryption scheme [44] based on the sponge construction. Recall that a N2-construction follows the Encrypt-then-MAC paradigm and \({ \textsc {Slae}}\) is a refinement that builds a nonce-based AEAD scheme from a nonce-based symmetric key encryption scheme and a vector MAC.
3.1 Sponge Construction
The sponge construction has been introduced by Bertoni et al. [8] and has been used to build various cryptographic primitives. In Fig. 1, we provide an illustration of the plain sponge construction.
The sponge construction consists of a so-called absorbing phase and a squeezing phase that is built upon a transformation \( \rho \) that is iteratively called on its input. This transformation basically maps strings of length \( n \) to strings of the same length, and in particular one can decompose \( n \) into two values \( r + c \) where \( r \) is called the rate and \( c \) is called the capacity. After each iteration of the transformation we refer to its output as the state \( S \). Furthermore, we usually refer to the leftmost \( r \) bits of the state as the outer part \( \bar{ S } \), which is equivalent to \(\left\lceil S \right\rceil ^{ r }\), and we refer to the remaining \( c \) bits as the inner part \( \hat{ S } \), which is equivalent to \(\left\lfloor S \right\rfloor _{ c }\). In order to input some element \( N \), this input is first padded to a non-zero multiple of the rate \( r \). For this, we use an injective padding function \(\texttt{pad} \) to get \( l \ge 1\) input blocks \( N _{1} \parallel N _{2} \parallel \dots \parallel N _{ l } = \texttt{pad} ( N )\). At the ith iteration, \( N _{i}\) is XORed with the outer part \( \bar{ S } \) before being inputted to the transformation, i.e., more formally \( Y _{i} \leftarrow ( N _{i} \oplus \bar{ S }_{i})\parallel \hat{ S }_{i} \) and evaluating \( S _{i+1} \leftarrow \rho ( Y _{i})\). In the squeezing phase, one can produce an output in one or more iterations obtaining \( r \) bits of output per iteration, i.e., more formally at the jth iteration the output \( Z _{j}\) is produced by \( Z _{j} \leftarrow \bar{ S }_{j} \).
3.2 The FGHF’ Construction and Slae
Degabriele et al. [21] provide a generic N2-construction [44] of a leakage-resilient authenticated encryption scheme with associated data called the FGHF’ construction. In particular, they show that the encryption component can be constructed from a fixed-input length function family that retains pseudorandomness in the presence of leakage (F) combined with a (standard) pseudorandom generator (G) while the authentication component is built from a collision-resistant hash function (H) and a fixed-input length function family that retains both pseudorandomness and unpredictability in the presence of leakage (\(F'\)). Overall this yields a leakage-resilient AEAD scheme. Observe that Krämer and Struck [39] showed that leakage-resilient pseudorandom functions suffice to build the scheme of Degabriele et al. [21] dropping the unpredictability requirement.
Furthermore, Degabriele et al. [21] show that the generic construction FGHF’ can be instantiated entirely from the sponge construction using a random transformation. Their particular sponge construction is called \({ \textsc {Slae}} \) which is composed of a symmetric key encryption scheme \({ \textsc {SlEnc}} \) and a MAC \({ \textsc {SlMac}} \) according to the N2-construction. In particular, viewing each of the schemes in terms of their smaller components, Degabriele et al. build \({ \textsc {SlEnc}} \) from a leakage-resilient function \({ \textsc {SlFunc}}\) and a pseudorandom generator \({ \textsc {SPrg}}\) while \({ \textsc {SlMac}} \) can be built from a collision-resistant hash function \({ \textsc {SvHash}}\) and a leakage-resilient function \({ \textsc {SlFunc}}\), and a formal description is given in Fig. 2. Regarding the security of \({ \textsc {Slae}}\), they prove the security via a composition theorem for the N2-construction in the leakage setting as established by Barwell et al. [5].
However, the quantum resistance of \({ \textsc {Slae}}\) has not been considered yet. In the following, we will scrutinize the \({ \textsc {Slae}}\) construction in this regard and we set the respective leakage sets to be empty. Therefore, we analyse the construction in the standard setting without leakage.
4 Post-Quantum (QS1) Security
In this section we analyse the security of \({ \textsc {Slae}}\) against quantum adversaries in the QS1 setting. The respective proofs of this Section can be found in Appendix B.
4.1 Security of SlFunc
The sponge-based pseudorandom function \({ \textsc {SlFunc}}\) is illustrated in Fig. 3 while the pseudocode can be found in Fig. 2. The function initialises the state of the sponge with the key and then absorbs the input, in case of \({ \textsc {Slae}}\) the nonce \( N \), \( r \) bits at a time. After the nonce has been absorbed, the output is obtained by applying the transformation \( \rho \) a final time and outputting the state. Note that the function outputs the full state rather than squeezing it over several rounds. That is also the reason why \( \rho \) is required to be a random transformation rather than a random permutation. Otherwise, an adversary could simply undo the transformation from the output by applying the inverse permutation. The theorem below gives a bound on distinguishing \({ \textsc {SlFunc}}\) from a random function when having superposition access to the underlying random oracle \( \rho \). The proof utilises the O2H lemma (cf. Lemma 5).
Theorem 6
Let \(\mathcal {F} = { \textsc {SlFunc}} \) be the function displayed in Fig. 3. Then for any quantum adversary \(\mathcal {A}\), making \( q _{\mathcal {F}}\) (classical) queries to \({ \textsc {SlFunc}}\) and \( q _{ \rho }\) (quantum) queries to \( \rho \), it holds that
Proof
Let \( l = \left\lceil \tfrac{ \nu }{ r } \right\rceil \) be the number of absorption steps and we assume for simplicity that \( \nu \) is a multiple of the rate. We further recursively define sets \({\mathcal {Y}}_i\) as
for all \(i\in \{1,\dots , l \}\), i.e., \({\mathcal {Y}}_i\) is the set of all possible values that can occur as input to \( \rho \) while evaluating \(\mathcal {F} ( \textsf{K},\cdot )\). It follows that \(|{\mathcal {Y}}_{i}| \le 2^{i r }\) and, in particular, \(|{\mathcal {Y}}_{ l }| \le 2^{ l r } = 2^{ \nu }\). Note that every input \( N \) defines a sequence of states \( Y _{0}, Y _{1},\dots , Y _{ l } \) that occur while evaluating the sponge. For an input \( N \), let \( Y _{i} [ N ]\) denote the state \( Y _{i}\) for this particular input, e.g., \( Y _{1} [ N ] = \left( \left\lceil \rho ( \textsf{K}) \right\rceil ^{ r } \oplus N _{1} \right) \parallel \left\lfloor \rho ( \textsf{K}) \right\rfloor _{ c }\), where \( N = N _{1} \parallel \dots \parallel N _{ l } \). In particular, for every input \( N \) it holds that \( Y _{0} [ N ] = \textsf{K} \).
We want to bound the following difference

In order to do this, we define the oracle \(\rho _{*}\), where \(\rho _{*} ( Y _{ l } [ N ]) = \overline{\mathcal {F}} ( N )\) for all \( Y _{ l } [ N ] \in {\mathcal {Y}}_{ l }\). That is, oracle \(\rho _{*}\) is reprogrammed on all final input states \( Y _{ l } [ N ]\) to output the output of a random function \(\overline{\mathcal {F}}\) on the input \( N \). Then it holds that

For the first difference on the right-hand side, the oracles are consistent in both cases. However, if the adversary finds a collision on the final input to \( \rho \) for \({ \textsc {SlFunc}} ( \textsf{K},\cdot )\), more precisely, two inputs \( N \) and \( N '\) such that \(\lceil N \rceil ^{ \nu - r } \ne \lceil N ' \rceil ^{ \nu - r } \) and \( Y _{ l } [ N ] = Y _{ l } [ N ' ]\), then these two inputs will result in the same output for \(\mathcal {F}\) and (most likely) different outputs for \(\overline{\mathcal {F}}\). Finding such a collision is a counting argument over the number of queries to the function and an application of Gaussian summation. Hence, it follows that

For the second difference, we can apply the O2H lemma (cf. Lemma 5) which yields

Recall that \(\mathcal {B} ^{\overline{\mathcal {F}} (\cdot ), \rho }\) simply runs \(\mathcal {A} ^{\overline{\mathcal {F}} (\cdot ), \rho }\) and outputs the measurement outcome of a randomly chosen query to \( \rho \). However, \(\mathcal {A}\) has no information about the set \({\mathcal {Y}}_{ l }\), hence we conclude with
Collecting everything yields

\(\square \)
We would like to point out the following. The length of the nonce \( \nu \) is typically of fixed size, e.g., in case of the NIST lightweight cryptography standardization process [45] the nonce is assumed to be 12 bytes long. In particular, \( \nu \) will be much smaller than the size of the sponge \( n \).
4.2 Security of SPrg
In this section we show that the sponge-based pseudorandom generator \({ \textsc {SPrg}}\) is secure against adversaries having superposition access to the underlying random oracle \( \rho \). The PRG \({ \textsc {SPrg}}\) is displayed in Fig. 4 and the respective pseudocode is given in Fig. 2. The construction deviates from more common constructions for pseudorandom generators since it initialises the state of the sponge with the seed rather than absorbing it. The output is then generated by squeezing \( r \) bits at each iteration of the sponge. Similar to the previous section, the proof relies on the O2H lemma.
Theorem 7
Let \({ \textsc {SPrg}}\) be the pseudorandom generator displayed in Fig. 4. Then for any quantum adversary \(\mathcal {A}\), making \( q \) (quantum) queries to \( \rho \), and receiving an input of length \( \mu \) it holds that
where \( l = \left\lceil \tfrac{ \mu }{ r } \right\rceil \) is the number of squeezing steps to obtain the required output length \( \mu \).
Proof
Let \( l = \left\lceil \tfrac{ \mu }{ r } \right\rceil \) be the number of squeezing steps. We assume, for sake of simplicity, that \( \mu \) is a multiple of \( r \). For a seed \( z \), let \( S _{1}, S _{2},\dots , S _{ l } \) denote the sequence of states that occur during evaluation of the sponge, i.e., \( S _{i} = \rho ^{i-1}( z )\), where \( \rho ^{i}\) corresponds to i consecutive evaluations of \( \rho \). We want to bound the following difference

where \( Z = Z _{1} \parallel \dots \parallel Z _{ l } = { \textsc {SPrg}} ( z , l r )\), i.e., obtaining an output of length \( l r \) using \({ \textsc {SPrg}}\) on seed \( z \) and \(R = R_1 \parallel \dots \parallel R_{ l }\), such that \(| Z _{i} | = |R_i| = r \). We write \(R_{[i,j]}\) for \(R_i \parallel \dots \parallel R_j\), the same for \( Z \). In particular, \(R_{[i,j]}\) for \(i > j\) equals the empty string. In the following we leave out the probability spaces for readability. We obtain
We start with the first difference, that, after simple rewriting, is,
where \(\rho _{1} (R_1 \parallel [ S _{1} ]_{ c }) = S _{2} \). Then it holds that the first difference above is 0, as the relation between \(R_1\) and \(\rho _{1}\) is the same as between \( Z _{1} \) and \( \rho \), and we merely need to bound the second difference, which only differs in the random oracle (\( \rho \) and \(\rho _{1}\)) at input \(R_1 \parallel [ S _{1} ]_{ c }\). Let \({\mathcal {S}}_1 = \{ R_1 \parallel [ S _{1} ]_{ c } \}\), then we can apply the O2H lemma (cf. Lemma 5) to obtain
While \(\mathcal {A}\) knows \(R_1\), it has no information about \([ S _{1} ]_{ c }\) (note that \( Z _{i}\), for \(i > 1\) provides no information about \({\mathcal {S}}_1\) due to \( \rho \) being one-way in the random oracle model). This yields
The same argument applies to the other differences, where more and more \( r \) bit blocks of \(\mathcal {A}\) ’s input are replaced with \(R_i\). More precisely, we obtain
where \({\mathcal {S}}_i = \{ R_i \parallel [ S _{i} ]_{ c } \}\). Collecting everything then yields
\(\square \)
4.3 Security of SvHash
In this section we analyse the QS1 security of \({ \textsc {SvHash}} \) which we display in Fig. 5 and its respective pseudocode can be found in Fig. 2. Observe that in order to compute a hash digest, the internal state is initialised to an evaluation of the random transformation of a zero bit string of length \( n \) XORed with the passed nonce. Afterwards the padded associated data and padded ciphertext are absorbed blockwise. Degabriele et al. chose to employ a domain separation to separate the boundary between associated data and ciphertext consisting of XORing the string \(1\parallel 0^{ c -1}\) to the inner state \( \hat{ S } \) as soon as the associated data has been absorbed. Observe that the domain separation can be viewed as a sponge construction with a rate increased by one bit. In this sense, an adversary \(\mathcal {A}\) against \({ \textsc {SvHash}}\) with rate \( r \) and capacity \( c \) can be viewed as an adversary against the plain sponge-based hash function with rate \( r +1\) and capacity \( c -1\), where \(\mathcal {A}\) guarantees that the \(( r +1)\)th bit of each input block is 0 except for the block which corresponds to absorbing the first ciphertext block. Hence a bound for the plain sponge-based hash function directly yields a bound for \({ \textsc {SvHash}}\) by accounting for the one bit loss in the capacity. The proof can be found in Appendix B.
Theorem 8
Let \({ \textsc {SvHash}}\) be the hash function as displayed in Fig. 5. Then for any quantum adversary \(\mathcal {A} \) making \( q \) (quantum) queries to \( \rho \), it holds that
where \(\varepsilon _1 \le ( q +1)^2 2^{- c +4}\), \(\varepsilon _2 \le q ^3 \left( \frac{\delta '+324}{2^{ c -1}}\right) +7\delta \sqrt{\frac{3( q +4)^3}{2^{ c }}}\) and \(\varepsilon _3 \le q ^3 \left( \frac{\delta '+324}{2^{ w +1}}\right) +7\delta \sqrt{\frac{3( q +4)^3}{2^{ w +2}}}\) with non-zero constants \(\delta \) and \(\delta '\) as well as \( l = \left\lceil \tfrac{ \mu }{ r } \right\rceil \) where \( \mu \) is the length of the (padded) message.
4.4 Security of Slae
In this section we show that the \(\mathrm {IND{\text{- }}CPA}\) and \(\mathrm {INT{\text{- }}CTXT}\) security of the authenticated encryption scheme \({ \textsc {Slae}}\) in the QS1 follows from the QS1 security of the underlying primitives \({ \textsc {SlFunc}}\), \({ \textsc {SPrg}}\), and \({ \textsc {SvHash}}\). The proofs can be found in Appendix B.
\(\mathrm {IND{\text{- }}CPA}\) Security of \({ \textsc {Slae}}\). \(\mathrm {IND{\text{- }}CPA}\) security follows from \({ \textsc {SlFunc}}\) and \({ \textsc {SPrg}}\) being a secure PRF and PRG, respectively. Theorem 9 first shows that \({ \textsc {SlFunc}}\) and \({ \textsc {SPrg}}\) yield \({ \textsc {SlEnc}}\) being \(\mathrm {IND{\text{- }}CPA}\)-secure while Theorem 10 then establishes the \(\mathrm {IND{\text{- }}CPA}\) security of \({ \textsc {Slae}}\).
Theorem 9
Let \({ \textsc {SlFunc}}\) be a pseudorandom function and \({ \textsc {SPrg}}\) a pseudorandom generator. Let further \({ \textsc {SlEnc}}\) be the symmetric key encryption scheme constructed from \({ \textsc {SlFunc}}\) and \({ \textsc {SPrg}}\) as shown in Fig. 2. For any quantum adversary \(\mathcal {A}\), making \( q _{{\textsf{Enc}}}\) queries to its encryption oracle, against the \(\mathrm {IND{\text{- }}CPA}\) security there exist adversaries \(\mathcal {A}_{ prf }\) and \(\mathcal {A}_{ prg }\) against \({ \textsc {SlFunc}}\) and \({ \textsc {SPrg}}\), respectively, such that
Theorem 10
Let \({ \textsc {SlEnc}}\) be the symmetric key encryption scheme and \({ \textsc {SlMac}}\) be a MAC. Let further \({ \textsc {Slae}}\) be the authenticated encryption scheme constructed from \({ \textsc {SlEnc}}\) and \({ \textsc {SlMac}}\) as shown in Fig. 2. For any quantum adversary \(\mathcal {A}\), making \( q _{{\textsf{Enc}}}\) queries to its encryption oracle, against the \(\mathrm {IND{\text{- }}CPA}\) security there exists an adversary \(\mathcal {A}_{ se }\), such that
\(\mathrm {INT{\text{- }}CTXT}\) Security of \({ \textsc {Slae}}\). The \(\mathrm {INT{\text{- }}CTXT}\) security follows from \({ \textsc {SlFunc}}\) being a secure PRF and \({ \textsc {SvHash}}\) being a collision-resistant hash function. In Theorem 11, we show that both yield a \(\mathrm {SUF{\text{- }}CMA}\)-secure MAC \({ \textsc {SlMac}}\). Subsequently, Theorem 12 shows that the \(\mathrm {SUF{\text{- }}CMA}\) security of \({ \textsc {SlMac}}\) ensures \(\mathrm {INT{\text{- }}CTXT}\) security of \({ \textsc {Slae}}\).
Theorem 11
Let \({ \textsc {SlFunc}}\) be a function and \({ \textsc {SvHash}}\) a hash function. Let further \({ \textsc {SlMac}}\) be the MAC constructed from \({ \textsc {SlFunc}}\) and \({ \textsc {SvHash}}\) as shown in Fig. 2. For any quantum adversary \(\mathcal {A}\), making \( q _{T}\) queries to its tagging oracle and \( q _{F}\) to its forge oracle, against the \(\mathrm {SUF{\text{- }}CMA}\) security there exist adversaries \(\mathcal {A}_{ prf }\) and \(\mathcal {A}_{ hash }\) against \({ \textsc {SlFunc}}\) and \({ \textsc {SvHash}}\), respectively, such that
Theorem 12
Let \({ \textsc {SlEnc}}\) be the symmetric key encryption scheme and \({ \textsc {SlMac}}\) be a MAC. Let further \({ \textsc {Slae}}\) be the authenticated encryption scheme constructed from \({ \textsc {SlEnc}}\) and \({ \textsc {SlMac}}\) as shown in Fig. 2. For any quantum adversary \(\mathcal {A}\), making \( q _{E}\) queries to its encryption oracle and \( q _{F}\) queries to its forge oracle, against the \(\mathrm {INT{\text{- }}CTXT}\) security there exists an adversary \(\mathcal {A}_{ mac }\), such that
5 Quantum (QS2) Security
In this section we study the security of \({ \textsc {Slae}}\) in the QS2 setting, where both the adversary and the challenger are quantum. Unlike the QS1 setting, the QS2 setting comes with several security notions. We analyse \({ \textsc {Slae}}\), or even more precisely its encryption component \({ \textsc {SlEnc}}\), with respect to the quantum security notions put forward in [12, 28, 43] providing positive and negative results.
5.1 QS2 Security Notions for SKE
Unlike the QS1 setting, there are several notions in the QS2 setting for encryption schemes. The first notion, called \(\mathrm {IND{\text{- }}qCPA}\), was presented by Boneh and Zhandry [12]. This notion allows the adversary superposition queries in the learning (qCPA) phase, while its challenge (IND) phase is restricted to classical queries. They further showed that simply allowing a quantum indistinguishability phase results in an unachievable security notion, called \(\mathrm {fqIND{\text{- }}CPA}\). More precisely, they consider a left-or-right oracle which performs the following
This operator entangles the ciphertext register with one of the message registers. Boneh and Zhandry show how this entanglement can be exploited to determine the bit b, irrespectively of the underlying encryption scheme.
Later, Gagliardoni et al. [28] and Mossayebi and Schack [43] provided security notions which allow the challenge (IND) phase to be quantum while not suffering from the impossibility result from [12].
An exhaustive study of QS2 security notions for encryption schemes is given by Carstens et al. [14]. Their study includes the aforementioned notions, along with many variants differing in the number of queries during challenge resp. learning phase. They show, surprisingly, that the notions do not form a strict hierarchy. Instead, the notions by Gagliardoni et al. [28] and Mossayebi and Schack [43] are incomparable but, together, imply all other notions. To ensure security in the QS2 setting, schemes have to be analysed with respect to both of these notions.
Nonce-Respecting Adversaries in the QS2 Setting. Another question that arises for the security of \({ \textsc {Slae}}\), deals with the nonce selection. Typically, adversaries are assumed to be nonce-respecting, meaning that they never repeat a nonce. While this is well defined in both the classical as well as QS1 setting, there is no definition for such adversaries in the QS2 setting. Kaplan et al. [36] mention this problem and sidestep it by letting the game pick the nonce at random. Thus, they essentially switch to the weaker IV setting which is well-studied in the classical setting. In our adapted security notions, we let the adversary submit a nonce register along with its message(s). We observe that it is not necessary to observe nonces in superposition since all QS2 notions for encryption schemes [12, 15, 28, 29, 43] consider the randomness (in case of \({ \textsc {Slae}}\) the nonce) to be classical.Footnote 4 To comply with this, we let the challenger measure the nonce register, thus ensuring a classical nonce, and reject a query if a nonce repeats.
5.2 Left-or-Right Security of SlEnc
The notion by Gagliardoni et al. [28] follows a left-or-right approach, similar to the one by Boneh and Zhandry [12], in which the adversary submits two messages (possibly in superposition) and receives the encryption of one of the two. The main difference is that Gagliardoni et al. use type-2 operators which operate directly on the register (instead of XORing the output to a separate output register). These operators are more powerful than the corresponding type-1 operator and they can only be realised for functions that are reversible. Type-2 operators were first studied by Kashefi et al. [38] and have further been studied by Carstens et al. [14] for symmetric key encryption and by Gagliardoni et al. [29] for public key encryption.
More formally those operators can be formalised as follows. Let \(\mathcal {F} :\{0,1\}^{n} \rightarrow \{0,1\}^{n} \) be a function. The type-1 operator for \(\mathcal {F}\) is the unitary \(U_{\mathcal {F}}^{(1)}\) that does the following
Observe that the realisation of \(U_{\mathcal {F}}^{(1)}\) is efficient if \(\mathcal {F}\) can be realised efficiently [46]. The type-2 operator for \(\mathcal {F}\) is the unitary \(U_{\mathcal {F}}^{(2)}\) that does the following
A realisation of a type-2 operator is, unlike for type-1 operators, not straightforward. Kashefi et al. [38] show that they can be realised using type-1 operators for both \(\mathcal {F}\) and \(\mathcal {F} ^{-1}\). Gagliardoni et al. [28] use this to show that type-2 operators for symmetric key encryption schemes can be realised using type-1 operators for encryption and decryption (cf. Fig. 6).
Using type-2 operators, Gagliardoni et al. [28] bypass the impossibility result by Boneh and Zhandry [12]. Since the adversary only receives a ciphertext register, it can not exploit the entanglement between registers as was the case for \(\mathrm {fqIND{\text{- }}CPA}\).
Below we define \(\mathrm {LoR{\text{- }}qIND}\) security. This is the notion given in [28] restricted to a single challenge and no learning queries. The difference is that our notion allows the adversary to specify a register containing the nonce used for encryption. To ensure the usage of classical randomness, we let the challenger measure this register. We restrict ourselves to the weaker \(\mathrm {LoR{\text{- }}qIND}\) notion, since we show below that \({ \textsc {Slae}}\) does not even achieve this notion. Extension to the stronger \(\mathrm {LoR{\text{- }}qINDqCPA}\) (allowing multiple challenges and learning queries) is straightforward by giving the adversary oracle access to a left-or-right oracle and a learning oracle implementing the type-2 encryption operator. The nonce-respecting property is ensured by letting the challenger reject queries for which the measurement of the nonce register yields an already measured nonce.
Definition 13
Let \(\varSigma = ( \texttt{Enc}, \texttt{Dec})\) be symmetric key encryption scheme and the security game \(\mathrm {LoR{\text{- }}qIND}\) be defined as in Fig. 7. For any adversary \(\mathcal {A}\) we define its \(\mathrm {LoR{\text{- }}qIND}\) advantage as
Security notion \(\mathrm {LoR{\text{- }}qIND}\) following [28].
The following theorem shows that the sponge-based encryption scheme \({ \textsc {SlEnc}}\) is not \(\mathrm {LoR{\text{- }}qIND}\)-secure. The attack uses a Hadamard distinguisher, following the one given in [28], that exploits the quantum insecurity of the one-time pad approach. The proof details can be found in Appendix C.
Theorem 14
Let \({ \textsc {SlEnc}}\) be the sponge-based encryption scheme displayed in Fig. 2 with message space \(\{0,1\}^{ \mu }\). Then there exist an adversary \(\mathcal {A}\) such that
Observe that there is no security notion for AEAD schemes using type-2 operators. Both [28] and [29] only focus on encryption schemes. The obvious question is whether the MAC can be implemented using a type-2 operator. Regardless of this, we point out that the attack does not necessarily extend to \({ \textsc {Slae}}\). The reason is that the register containing the tag will be entangled which thwarts an attack by simply discarding the tag.
Note that the same attack applies to the encryption scheme underlying the sponge-based AEAD schemes ISAP [23] and its successor ISAP v2.0 [22].
5.3 Real-or-Random Security of SlEnc
The notion by Mossayebi and Schack [43] follows a real-or-random approach, where the adversary submits only a single message (possibly in superposition) and receives back the message along with a ciphertext. The ciphertext is either the encryption of the submitted message or of the permuted message using a permutation picked at random. Usage of the permutation ensures that the number of messages in superposition is the same for both the submitted and permuted message. Mossayebi and Schack [43] also defined the corresponding security with respect to chosen ciphertext attacks. The relevance of this notion is questionable, as it assumes non-cheating adversaries, that do not try to decrypt the challenge ciphertext with its decryption oracle.
In this notion, there is only a single message register that will always be entangled with the ciphertext register. This bypasses the impossibility result by Boneh and Zhandry [12].
Security notion \(\mathrm {RoR{\text{- }}qIND}\) following [43].
Below we define \(\mathrm {RoR{\text{- }}qIND}\) security, where the adversary is restricted to a single challenge query and no learning query, again, extended by letting the adversary send a register with the nonce that is measured by the challenger. Extension to \(\mathrm {RoR{\text{- }}qINDqCPA}\) security works by providing the adversary a real-or-random challenge oracle and a learning oracle and reject queries where (measured) nonces repeat (Fig. 9).
Definition 15
Let \(\varSigma = ( \texttt{Enc}, \texttt{Dec})\) be a symmetric key encryption scheme and the security game \(\mathrm {RoR{\text{- }}qIND}\) be defined as in Fig. 8. For any adversary \(\mathcal {A}\) we define its \(\mathrm {RoR{\text{- }}qIND}\) advantage as
The following theorem shows that the sponge-based encryption scheme \({ \textsc {SlEnc}}\) is not \(\mathrm {RoR{\text{- }}qIND}\)-secure. The attack follows [15] exploiting the outcome of a measurement in the Hadamard basis on two entangled registers. The full proof details can be found in the full version of the paper [34].
Theorem 16
Let \({ \textsc {SlEnc}}\) be the sponge-based encryption scheme displayed in Fig. 2. Then there exist an adversary \(\mathcal {A}\) such that
5.4 \(\mathrm {IND{\text{- }}qCPA}\) Security of Slae and FGHF’
In Sect. 5.1, we have discussed various different security notions for symmetric key encryption schemes in the QS2 setting. So far we have shown that \({ \textsc {SlEnc}}\) is neither \(\mathrm {LoR{\text{- }}qIND}\) nor \(\mathrm {RoR{\text{- }}qIND}\) secure. Observe that the attacks also apply to the generic construction FGHF’, as the weakness lies in the one-time pad (OTP) approach exploiting an inherent insecurity of the OTP against quantum attackers.
Observe that both the generic FGHF’ construction as well as \({ \textsc {Slae}}\) are stream ciphers. Following the results by Anand et al. [4], we obtain that both constructions are \(\mathrm {IND{\text{- }}qCPA}\) secure which is a direct consequence from the established \(\mathrm {IND{\text{- }}CPA}\) security in the QS1 sense.
6 Conclusion
In this work we have given both positive and negative results for the security of the sponge-based AEAD scheme \({ \textsc {Slae}}\). On the one hand, we have shown that \({ \textsc {Slae}}\) as well as the underlying core primitives are post-quantum secure. On the other hand, we have shown that their quantum security is not fully clear yet. While \({ \textsc {Slae}}\), as well as the generic FGHF’ construction, are easily seen to be not quantum secure for notions that allow challenge queries by the adversary to be in superposition, its quantum security with respect to \(\mathrm {IND{\text{- }}qCPA}\) is still open. More precisely, we argued that its \(\mathrm {IND{\text{- }}qCPA}\) security reduces to the quantum security of the underlying function \({ \textsc {SlFunc}}\) via the generic FGHF’ construction.
In the realm of quantum security, it is open to analyse the quantum security of the sponge-based function \({ \textsc {SlFunc}}\) as well as addressing the quantum unforgeability of \({ \textsc {Slae}}\) and its underlying MAC \({ \textsc {SlMac}}\). The reason is that the landscape of quantum unforgeability notions is still unclear as the existing notions [1, 12, 25, 30] suffer from some drawbacks that allow for intuitive forgeries that are not covered by the notions.
Regarding the post-quantum security of \({ \textsc {Slae}}\), one can investigate whether tighter bounds can be achieved. Generally, our bounds establish for the first time post-quantum security for the AEAD scheme and the underlying primitives but they are rather conservative and there might be room for improvements. For example, for \({ \textsc {SlFunc}}\) one may be able to use the semi-classical variant of the O2H lemma developed by Ambainis et al. [3] and for \({ \textsc {SPrg}}\) one may get tighter bounds by using the doubled-sided O2H lemma by Bindel et al. [9]. One can also consider an adaptive version, where the random oracle is reprogrammed only on the points that the adversary queries to its classical oracle.
Notes
- 1.
Observe that the current version of the paper is flawed.
- 2.
In a nutshell, a quantum adversary can open a commitment to an arbitrary message but not to two different messages. Thus it breaks the binding property without finding a collision.
- 3.
We assume that domain and co-domain are of the same size as it is the only case we are considering in this work.
- 4.
References
Alagic, G., Majenz, C., Russell, A., Song, F.: Quantum-access-secure message authentication via blind-unforgeability. In: Canteaut, A., Ishai, Y. (eds.) EUROCRYPT 2020, Part III. LNCS, vol. 12107, pp. 788–817. Springer, Cham (2020). https://doi.org/10.1007/978-3-030-45727-3_27
Alagic, G., Russell, A.: Quantum-secure symmetric-key cryptography based on hidden shifts. In: Coron, J.-S., Nielsen, J.B. (eds.) EUROCRYPT 2017, Part III. LNCS, vol. 10212, pp. 65–93. Springer, Cham (2017). https://doi.org/10.1007/978-3-319-56617-7_3
Ambainis, A., Hamburg, M., Unruh, D.: Quantum security proofs using semi-classical oracles. In: Boldyreva, A., Micciancio, D. (eds.) CRYPTO 2019, Part II. LNCS, vol. 11693, pp. 269–295. Springer, Cham (2019). https://doi.org/10.1007/978-3-030-26951-7_10
Anand, M.V., Targhi, E.E., Tabia, G.N., Unruh, D.: Post-quantum security of the CBC, CFB, OFB, CTR, and XTS modes of operation. In: Takagi, T. (ed.) PQCrypto 2016. LNCS, vol. 9606, pp. 44–63. Springer, Cham (2016). https://doi.org/10.1007/978-3-319-29360-8_4
Barwell, G., Martin, D.P., Oswald, E., Stam, M.: Authenticated encryption in the face of protocol and side channel leakage. In: Takagi, T., Peyrin, T. (eds.) ASIACRYPT 2017, Part I. LNCS, vol. 10624, pp. 693–723. Springer, Cham (2017). https://doi.org/10.1007/978-3-319-70694-8_24
Bellare, M., Namprempre, C.: Authenticated encryption: relations among notions and analysis of the generic composition paradigm. In: Okamoto, T. (ed.) ASIACRYPT 2000. LNCS, vol. 1976, pp. 531–545. Springer, Heidelberg (2000). https://doi.org/10.1007/3-540-44448-3_41
Bellare, M., Rogaway, P.: Random oracles are practical: a paradigm for designing efficient protocols. In: Denning, D.E., Pyle, R., Ganesan, R., Sandhu, R.S., Ashby, V. (eds.) ACM CCS 1993, pp. 62–73. ACM Press, November 1993
Bertoni, G., Daemen, J., Peeters, M., Van Assche, G.: Sponge functions. In: ECRYPT Hash Workshop (2007)
Bindel, N., Hamburg, M., Hövelmanns, K., Hülsing, A., Persichetti, E.: Tighter proofs of CCA security in the quantum random oracle model. In: Hofheinz, D., Rosen, A. (eds.) TCC 2019, Part II. LNCS, vol. 11892, pp. 61–90. Springer, Cham (2019). https://doi.org/10.1007/978-3-030-36033-7_3
Boneh, D., Dagdelen, Ö., Fischlin, M., Lehmann, A., Schaffner, C., Zhandry, M.: Random oracles in a quantum world. In: Lee, D.H., Wang, X. (eds.) ASIACRYPT 2011. LNCS, vol. 7073, pp. 41–69. Springer, Heidelberg (2011). https://doi.org/10.1007/978-3-642-25385-0_3
Boneh, D., Zhandry, M.: Quantum-secure message authentication codes. In: Johansson, T., Nguyen, P.Q. (eds.) EUROCRYPT 2013. LNCS, vol. 7881, pp. 592–608. Springer, Heidelberg (2013). https://doi.org/10.1007/978-3-642-38348-9_35
Boneh, D., Zhandry, M.: Secure signatures and chosen ciphertext security in a quantum computing world. In: Canetti, R., Garay, J.A. (eds.) CRYPTO 2013, Part II. LNCS, vol. 8043, pp. 361–379. Springer, Heidelberg (2013). https://doi.org/10.1007/978-3-642-40084-1_21
Bonnetain, X., Hosoyamada, A., Naya-Plasencia, M., Sasaki, Yu., Schrottenloher, A.: Quantum attacks without superposition queries: the offline Simon’s algorithm. In: Galbraith, S.D., Moriai, S. (eds.) ASIACRYPT 2019, Part I. LNCS, vol. 11921, pp. 552–583. Springer, Cham (2019). https://doi.org/10.1007/978-3-030-34578-5_20
Carstens, T.V., Ebrahimi, E., Tabia, G.N., Unruh, D.: On quantum indistinguishability under chosen plaintext attack. Cryptology ePrint Archive, Report 2020/596 (2020). https://eprint.iacr.org/2020/596
Chevalier, C., Ebrahimi, E., Vu, Q.-H.: On security notions for encryption in a quantum world. Cryptology ePrint Archive, Report 2020/237 (2020). https://eprint.iacr.org/2020/237
Czajkowski, J.: Quantum indifferentiability of SHA-3. IACR Cryptology ePrint Archive 2021/192 (2021)
Czajkowski, J., Groot Bruinderink, L., Hülsing, A., Schaffner, C., Unruh, D.: Post-quantum security of the sponge construction. Cryptology ePrint Archive, Report 2017/771 (2017). https://eprint.iacr.org/2017/771
Czajkowski, J., Groot Bruinderink, L., Hülsing, A., Schaffner, C., Unruh, D.: Post-quantum security of the sponge construction. In: Lange, T., Steinwandt, R. (eds.) PQCrypto 2018. LNCS, vol. 10786, pp. 185–204. Springer, Cham (2018). https://doi.org/10.1007/978-3-319-79063-3_9
Czajkowski, J., Hülsing, A., Schaffner, C.: Quantum indistinguishability of random sponges. In: Boldyreva, A., Micciancio, D. (eds.) CRYPTO 2019, Part II. LNCS, vol. 11693, pp. 296–325. Springer, Cham (2019). https://doi.org/10.1007/978-3-030-26951-7_11
Czajkowski, J., Majenz, C., Schaffner, C., Zur, S.: Quantum lazy sampling and game-playing proofs for quantum indifferentiability. Cryptology ePrint Archive, Report 2019/428 (2019). https://eprint.iacr.org/2019/428
Degabriele, J.P., Janson, C., Struck, P.: Sponges resist leakage: the case of authenticated encryption. In: Galbraith, S.D., Moriai, S. (eds.) ASIACRYPT 2019, Part II. LNCS, vol. 11922, pp. 209–240. Springer, Cham (2019). https://doi.org/10.1007/978-3-030-34621-8_8
Dobraunig, C., et al.: ISAP v2.0. IACR Trans. Symm. Cryptol. 2020(S1), 390–416 (2020)
Dobraunig, C., Eichlseder, M., Mangard, S., Mendel, F., Unterluggauer, T.: ISAP - towards side-channel secure authenticated encryption. IACR Trans. Symm. Cryptol. 2017(1), 80–105 (2017)
Dobraunig, C., Eichlseder, M., Mendel, F., Schläffer, M.: Ascon v1. 2. Submission to the CAESAR Competition (2016)
Doosti, M., Delavar, M., Kashefi, E., Arapinis, M.: A unified framework for quantum unforgeability. CoRR, abs/2103.13994 (2021)
Fischlin, M., Mittelbach, A.: An overview of the hybrid argument. Cryptology ePrint Archive, Report 2021/088 (2021). https://eprint.iacr.org/2021/088
Gagliardoni, T.: Quantum security of cryptographic primitives. Ph.D. thesis, Darmstadt University of Technology, Germany (2017)
Gagliardoni, T., Hülsing, A., Schaffner, C.: Semantic security and indistinguishability in the quantum world. In: Robshaw, M., Katz, J. (eds.) CRYPTO 2016, Part III. LNCS, vol. 9816, pp. 60–89. Springer, Heidelberg (2016). https://doi.org/10.1007/978-3-662-53015-3_3
Gagliardoni, T., Krämer, J., Struck, P.: Quantum indistinguishability for public key encryption. In: Cheon, J.H., Tillich, J.-P. (eds.) PQCrypto 2021 2021. LNCS, vol. 12841, pp. 463–482. Springer, Cham (2021). https://doi.org/10.1007/978-3-030-81293-5_24
Garg, S., Yuen, H., Zhandry, M.: New security notions and feasibility results for authentication of quantum data. In: Katz, J., Shacham, H. (eds.) CRYPTO 2017, Part III. LNCS, vol. 10402, pp. 342–371. Springer, Cham (2017). https://doi.org/10.1007/978-3-319-63715-0_12
Grover, L.K.: A fast quantum mechanical algorithm for database search. In: 28th ACM STOC, pp. 212–219. ACM Press, May 1996
Hosoyamada, A., Sasaki, Yu.: Quantum Demiric-Selçuk meet-in-the-middle attacks: applications to 6-round generic feistel constructions. In: Catalano, D., De Prisco, R. (eds.) SCN 2018. LNCS, vol. 11035, pp. 386–403. Springer, Cham (2018). https://doi.org/10.1007/978-3-319-98113-0_21
Ito, G., Hosoyamada, A., Matsumoto, R., Sasaki, Yu., Iwata, T.: Quantum chosen-ciphertext attacks against feistel ciphers. In: Matsui, M. (ed.) CT-RSA 2019. LNCS, vol. 11405, pp. 391–411. Springer, Cham (2019). https://doi.org/10.1007/978-3-030-12612-4_20
Janson, C., Struck, P.: Sponge-based authenticated encryption: security against quantum attackers. Cryptology ePrint Archive, Report 2022/139 (2022). https://eprint.iacr.org/2022/139
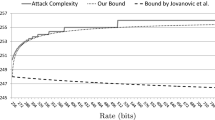
Jovanovic, P., Luykx, A., Mennink, B.: Beyond 2c/2 security in sponge-based authenticated encryption modes. In: Sarkar, P., Iwata, T. (eds.) ASIACRYPT 2014, Part I. LNCS, vol. 8873, pp. 85–104. Springer, Heidelberg (2014). https://doi.org/10.1007/978-3-662-45611-8_5
Kaplan, M., Leurent, G., Leverrier, A., Naya-Plasencia, M.: Breaking symmetric cryptosystems using quantum period finding. In: Robshaw, M., Katz, J. (eds.) CRYPTO 2016, Part II. LNCS, vol. 9815, pp. 207–237. Springer, Heidelberg (2016). https://doi.org/10.1007/978-3-662-53008-5_8
Kaplan, M., Leurent, G., Leverrier, A., Naya-Plasencia, M.: Quantum differential and linear cryptanalysis. IACR Trans. Symm. Cryptol. 2016(1), 71–94 (2016). https://tosc.iacr.org/index.php/ToSC/article/view/536
Kashefi, E., Kent, A., Vedral, V., Banaszek, K.: Comparison of quantum oracles. Phys. Rev. A 65(5), 050304 (2002)
Krämer, J., Struck, P.: Leakage-resilient authenticated encryption from leakage-resilient pseudorandom functions. In: Bertoni, G.M., Regazzoni, F. (eds.) COSADE 2020. LNCS, vol. 12244, pp. 315–337. Springer, Cham (2021). https://doi.org/10.1007/978-3-030-68773-1_15
Kuchta, V., Sakzad, A., Stehlé, D., Steinfeld, R., Sun, S.-F.: Measure-rewind-measure: tighter quantum random oracle model proofs for one-way to hiding and CCA security. In: Canteaut, A., Ishai, Y. (eds.) EUROCRYPT 2020, Part III. LNCS, vol. 12107, pp. 703–728. Springer, Cham (2020). https://doi.org/10.1007/978-3-030-45727-3_24
Kuwakado, H., Morii, M.: Quantum distinguisher between the 3-round feistel cipher and the random permutation. In: ISIT 2010 (2010)
Kuwakado, H., Morii, M.: Security on the quantum-type even-mansour cipher. In: ISITA 2012 (2012)
Mossayebi, S., Schack, R.: Concrete security against adversaries with quantum superposition access to encryption and decryption oracles. CoRR, abs/1609.03780 (2016)
Namprempre, C., Rogaway, P., Shrimpton, T.: Reconsidering generic composition. In: Nguyen, P.Q., Oswald, E. (eds.) EUROCRYPT 2014. LNCS, vol. 8441, pp. 257–274. Springer, Heidelberg (2014). https://doi.org/10.1007/978-3-642-55220-5_15
National Institute of Standards and Technology. Lightweight cryptography standardization process (2015)
Nielsen, M.A., Chuang, I.L.: Quantum Computation and Quantum Information: 10th Anniversary Edition, 10th edn. Cambridge University Press, New York (2011)
Rogaway, P.: Authenticated-encryption with associated-data. In: Atluri, V. (ed.) ACM CCS 2002, pp. 98–107. ACM Press, November 2002
Rötteler, M., Steinwandt, R.: A note on quantum related-key attacks. Inf. Process. Lett. 115(1), 40–44 (2015)
Shor, P.W.: Algorithms for quantum computation: discrete logarithms and factoring. In: 35th FOCS, pp. 124–134. IEEE Computer Society Press, November 1994
Song, F.: A note on quantum security for post-quantum cryptography. In: Mosca, M. (ed.) PQCrypto 2014. LNCS, vol. 8772, pp. 246–265. Springer, Cham (2014). https://doi.org/10.1007/978-3-319-11659-4_15
Soukharev, V., Jao, D., Seshadri, S.: Post-quantum security models for authenticated encryption. In: Takagi, T. (ed.) PQCrypto 2016. LNCS, vol. 9606, pp. 64–78. Springer, Cham (2016). https://doi.org/10.1007/978-3-319-29360-8_5
Unruh, D.: Computationally binding quantum commitments. Cryptology ePrint Archive, Report 2015/361 (2015). https://eprint.iacr.org/2015/361
Unruh, D.: Revocable quantum timed-release encryption. J. ACM 62(6), 1–76 (2015)
Unruh, D.: Computationally binding quantum commitments. In: Fischlin, M., Coron, J.-S. (eds.) EUROCRYPT 2016, Part II. LNCS, vol. 9666, pp. 497–527. Springer, Heidelberg (2016). https://doi.org/10.1007/978-3-662-49896-5_18
Unruh, D.: Compressed permutation oracles (and the collision-resistance of sponge/SHA3). Cryptology ePrint Archive, Report 2021/062 (2021). https://eprint.iacr.org/2021/062
Yamakawa, T., Zhandry, M.: Classical vs quantum random oracles. In: Canteaut, A., Standaert, F.-X. (eds.) EUROCRYPT 2021, Part II. LNCS, vol. 12697, pp. 568–597. Springer, Cham (2021). https://doi.org/10.1007/978-3-030-77886-6_20
Zhandry, M.: How to construct quantum random functions. In: 53rd FOCS, pp. 679–687. IEEE Computer Society Press, October 2012
Zhandry, M.: How to record quantum queries, and applications to quantum indifferentiability. In: Boldyreva, A., Micciancio, D. (eds.) CRYPTO 2019, Part II. LNCS, vol. 11693, pp. 239–268. Springer, Cham (2019). https://doi.org/10.1007/978-3-030-26951-7_9
Acknowledgements
We thank anonymous reviewers for their valuable comments on an earlier draft of this work. This work was funded by the Deutsche Forschungsgemeinschaft (DFG) – SFB 1119 – 236615297.
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Appendices
A A Additional Preliminaries
1.1 A.1 A.1 Authenticated Encryption
We begin with a definition of authenticated encryption schemes with associated data [6, 47].
Definition 17
An authenticated encryption scheme with associated data (AEAD) \(\texttt{AEAD} =( \texttt{Enc}, \texttt{Dec})\) is a pair of efficient algorithms associated with key space \({\mathcal {K}}\), nonce space \({\mathcal {N}}\), associated-data space \({\mathcal {H}}\), message space \({\mathcal {M}}\), and ciphertext space \({\mathcal {C}}\) such that:
-
The deterministic encryption algorithm \( \texttt{Enc} :{\mathcal {K}} \times {\mathcal {N}} \times {\mathcal {H}} \times {\mathcal {M}} \rightarrow {\mathcal {C}} \) takes as input a secret key \( \textsf{K}\), a nonce \( N \), associated data \( A \), and a message \( M \). It outputs a ciphertext \( C \).
-
The deterministic decryption algorithm \( \texttt{Dec} :{\mathcal {K}} \times {\mathcal {N}} \times {\mathcal {H}} \times {\mathcal {C}} \rightarrow {\mathcal {M}} \cup \{\bot \}\) takes as input a secret key \( \textsf{K}\), a nonce \( N \), associated data \( A \), and a ciphertext \( C \). It outputs a message \( M \) or \(\bot \) indicating an invalid ciphertext.
We say that an AEAD scheme is correct, if for all \( \textsf{K} \in {\mathcal {K}} \), \( N \in {\mathcal {N}} \), \( A \in {\mathcal {H}} \) and \( M \in {\mathcal {M}} \), it holds that \( \texttt{Dec} ( \textsf{K}, N , A , \texttt{Enc} ( \textsf{K}, N , A , M )) = M \).
Throughout this work, we consider \({\mathcal {K}} = \{0,1\}^{ k } \), \({\mathcal {N}} = \{0,1\}^{ \nu } \), \({\mathcal {H}} = \{0,1\}^{ \alpha } \), \({\mathcal {M}} = \{0,1\}^{ \mu } \), and \({\mathcal {C}} = \{0,1\}^{ \gamma } \).
Security of an AEAD scheme now demands that an adversary cannot distinguish encryptions of equal-length messages which corresponds to the usual CPA-security notion of encryption schemes. The formal description of the game can be found on the left side of Fig. 10. Additionally, security also demands that the adversary is not able to forge further valid ciphertexts which corresponds to an integrity notion on the ciphertext level. The formal description of the games can be found on the right side of Fig. 10.
Definition 18
Let \(\texttt{AEAD}\) be an authenticated encryption scheme with associated data.
-
For an adversary \(\mathcal {A}\), making \( q _{E}\) queries to its encryption oracle, we define its \(\mathrm {IND{\text{- }}CPA}\) advantage as
$$\begin{aligned} \textbf{Adv}_{\texttt{AEAD}}^{{\mathsf {IND{\text{- }}CPA}}}(\mathcal {A}) = 2\,\Pr [\mathrm {IND{\text{- }}CPA} ^{\mathcal {A}} \rightarrow 1] - 1 \,. \end{aligned}$$ -
For an adversary \(\mathcal {A}\), making \( q _{E}\) and \( q _{F}\) queries to its encryption oracle and forge oracle, respectively, we define its \(\mathrm {INT{\text{- }}CTXT}\) advantage as
$$\begin{aligned} \textbf{Adv}_{\texttt{AEAD}}^{{\mathsf {INT{\text{- }}CTXT}}}(\mathcal {A}) = \Pr [\mathrm {INT{\text{- }}CTXT} ^{\mathcal {A}} \rightarrow 1] \,. \end{aligned}$$
Symmetric Key Encryption. Observe that the definition of a symmetric key encryption (SKE) scheme is very close to the given about AEAD. Note that one can obtain a SKE scheme by analogously defining an encryption scheme which does not admit associated data as a part of its input in comparison to Definition 17.
Usually one defines CPA-security of a SKE scheme. Here the formalisation is again very close to the description in Fig. 10 with the modification of not including the associated data as an input to the encryption oracle.
1.2 B.2 A.2 Message Authentication Code
Next we will provide the basic definition of a message authentication code.
Definition 19
A message authentication code (MAC) \(\texttt{MAC} =( \texttt{Tag}, \texttt{Vfy})\) is a pair of efficient algorithms associated with key space \({\mathcal {K}}\) and domain space \({\mathcal {X}}\) such that:
-
The deterministic tagging algorithm \( \texttt{Tag} :{\mathcal {K}} \times {\mathcal {X}} \rightarrow \{0,1\}^{ \tau } \) takes as input a key \( \textsf{K}\) and an element \( X \). It returns a tag \( T \) of size \(\{0,1\}^{ \tau } \).
-
The deterministic verification algorithm \( \texttt{Vfy} :{\mathcal {K}} \times {\mathcal {X}} \times \{0,1\}^{ \tau } \rightarrow \{0,1\}\) takes as input a key \( \textsf{K}\), an element \( X \), and a tag \( T \) and outputs 1 indicating that the input is valid, or otherwise 0.
We say that a MAC scheme is correct, if for all \( \textsf{K} \in {\mathcal {K}} \) and any admissible input \( X \in {\mathcal {X}} \), it holds that \( \texttt{Vfy} ( \textsf{K}, X , \texttt{Tag} ( \textsf{K}, X )) = 1\).
Definition 20
Let \(\texttt{MAC}\) be a message authentication code. We define the \(\mathrm {SUF{\text{- }}CMA}\) advantage of an adversary \(\mathcal {A}\) making at most \( q _{T}\) queries to its tag oracle and \( q _{F}\) many queries to its forge oracle as
where the respective game is depicted in Fig. 11.
1.3 C.3 A.3 Hash Function
In this section, we simply review the collapsing property of hash functions [54] in the formalisation of [18].
Definition 21
For algorithms \(\mathcal {A} \) and \(\mathcal {B} \), consider the following games given in Fig. 12. There are quantum registers S and M, and \(\mathcal {M}(M)\) is a measurement of M in the computational basis.
For a set \(\textbf{m}\), we call an adversary \((\mathcal {A}, \mathcal {B})\) valid on \(\textbf{m}\) for \(H^{ {\textsf{O}}}\) if and only if \(\Pr [H^{ {\textsf{O}}}(m) = h \wedge m \in \textbf{m}]\) when we run \((S,M,h) \leftarrow \mathcal {A} ^{ {\textsf{O}}}()\) and measure M in the computational basis as m.
A function H is collapsing on \(\textbf{m}\) if and only if for any quantum-polynomial-time adversary \((\mathcal {A}, \mathcal {B})\) that is valid for \(H^{ {\textsf{O}}}\) on \(\textbf{m}\) and \(|\Pr [b=1 :\mathsf {Game_1}]-\Pr [b=1 :\mathsf {Game_2}]|\) is negligible.
B B QS1 Proofs
1.1 D.4 B.1 Proof of Theorem 8
Proof
The above collision resistance bound can be obtained from a combination of results from Czajkowski et al. [17] and Unruh [52] with a slight modification that stems from the way \({ \textsc {SvHash}} \) is constructed. Observe that the small modification is due to the interpretation that we consider a sponge-based hash function with the capacity being reduced by one bit and hence the rate being increased by one bit. We take care of this one bit loss when applying the following results.
A crucial property in the realm of hash functions in the post-quantum setting is called the collapsing property which is a strengthening of collision resistance and Unruh has showed in [52, 54] that if a hash function is collapsing then this also implies that it is quantum collision resistant. Additionally, Czajkowski et al. [17, 18] showed that if the underlying function of the sponge construction is a random transformation then the sponge construction is collapsing. Being equipped with their result, we can derive the required bound for our setting.
We will follow the proof strategy put forward by Czajkowski et al. [17, Theorem 33] to show that the sponge construction is collapsing. This requires to show that the inner state \( \hat{ S } \) is collapsing in the absorbing phase while the outer state \( \bar{ S } \) is collapsing in the squeezing phase and that there are no zero-preimages in the inner state \( \hat{ S } \). Then using [52, Lemma 25] provides us with the implication that the sponge construction is then also collision resistant. It now remains to apply the above strategy appropriately to derive the bound.
We have that \( l = \left\lceil \tfrac{ \mu }{ r } \right\rceil \) and by [17, Theorem 33], we know that the collapsing advantage is bounded by \(\sqrt{\varepsilon _1}+ l \cdot \varepsilon _2 + \varepsilon _3\), where \(\varepsilon _1\) corresponds to the probability of finding zero-preimages, \(\varepsilon _2\) corresponds to the collapsing advantage of the inner state and \(\varepsilon _3\) corresponds to the collapsing advantage of the outer state, respectively. By applying [17, Lemma 19], we obtain that \(\varepsilon _1 \le ( q +1)^2 2^{- c +4}\). By a simple combination of [17, Lemma 32] and [52, Theorem 38], we can derive \(\varepsilon _2 \le q ^3 \left( \frac{\delta '+324}{2^{ c -1}}\right) +7\delta \sqrt{\frac{3( q +4)^3}{2^{ c }}}\) and \(\varepsilon _3 \le q ^3 \left( \frac{\delta '+324}{2^{ w +1}}\right) +7\delta \sqrt{\frac{3( q +4)^3}{2^{ w +2}}}\) where both \(\delta \) and \(\delta '\) are non-zero constants. Then by [52, Lemma 25], we have a tight reduction from collapsing to collision resistance and hence the same bound holds for the collision resistance of the sponge construction. \(\square \)
1.2 E.5 B.2 Proof of Theorem 9
Proof
The proof can be obtained from [21] by dropping everything related to the leakage setting. It proceeds in two game hops. The first game hop replaces the function \({ \textsc {SlFunc}}\) by a random function which can be straightforwardly bound by the PRF advantage of \({ \textsc {SlFunc}}\). More precisely, \(\mathcal {A}_{ prf }\) uses its own oracle for everything related to \({ \textsc {SlFunc}}\) while simulating \({ \textsc {SPrg}}\) using (classical) queries to the random oracle \( \rho \). All (quantum) queries by \(\mathcal {A}\) to \( \rho \) are simply forwarded by \(\mathcal {A}_{ prf }\), as are the responses back to \(\mathcal {A}\).
The second game hop replaces the output of \({ \textsc {SPrg}}\) by a random output. A standard hybrid argument [26] shows that this can be bound by the security of \({ \textsc {SPrg}}\). The reduction \(\mathcal {A}_{ prg }\) picks a random query of \(\mathcal {A}\) to its encryption oracle, where it uses its own input (either the output of \({ \textsc {SPrg}}\) or a random bit string) to encrypt the message. Prior queries are answered by XORing random bit string to the message while subsequent queries are answered by simulating \({ \textsc {SPrg}}\) using (classical) queries to \( \rho \). All (quantum) queries by \(\mathcal {A}\) to \( \rho \) are simply forwarded by \(\mathcal {A}_{ prg }\), as are the responses back to \(\mathcal {A}\).
The resulting game yields identically distributed ciphertexts, irrespectively of the message. The factor 2 accounts for doing the game hops for both cases \(b=0\) and \(b=1\). \(\square \)
1.3 F.6 B.3 Proof of Theorem 10
Proof
The proof proceeds by a simple reduction. In more detail, the reduction \(\mathcal {A}_{ se }\) picks a key for the MAC \({ \textsc {SlMac}}\). For every query to the encryption oracle by \(\mathcal {A}\), \(\mathcal {A}_{ se }\) invokes its own encryption oracle and locally computes the tag of the ciphertext using (classical) queries to \( \rho \) before sending the ciphertext and the tag back to \(\mathcal {A}\). Every (quantum) query by \(\mathcal {A}\) to \( \rho \) is simply forwarded by \(\mathcal {A}_{ se }\). \(\square \)
1.4 G.7 B.4 Proof of Theorem 11
Proof
We assume that all messages queried by \(\mathcal {A}\) result in different hash values, otherwise, we obtain a simple reduction \(\mathcal {A}_{ hash }\) from the collision resistance of \({ \textsc {SvHash}}\).
Then the proof proceeds by a game hop in which \({ \textsc {SlFunc}}\) is replaced by a random function. The reduction \(\mathcal {A}_{ prf }\) will invoke its own function to simulate the tagging and verification of \({ \textsc {SlMac}}\) and (classical) queries to \( \rho \) to evaluate \({ \textsc {SvHash}}\). Every (quantum) query to \( \rho \) by \(\mathcal {A}\) is simply forwarded by \(\mathcal {A}_{ prf }\).
The resulting game is bound by a simple counting argument that \(\mathcal {A}\) predicts the output of a random function. \(\square \)
1.5 H.8 B.5 Proof of Theorem 12
Proof
The reduction \(\mathcal {A}_{ mac }\) picks a key for the symmetric key encryption scheme \({ \textsc {SlEnc}}\). For every query to the encryption oracle by \(\mathcal {A}\), \(\mathcal {A}_{ mac }\) locally computes the ciphertext using (classical) queries to \( \rho \) and obtains the tag using its own tagging oracle. It then sends the ciphertext and the tag back to \(\mathcal {A}\). For every forgery attempt by \(\mathcal {A}\), \(\mathcal {A}_{ mac }\) queries the ciphertext and the tag as its own forgery attempt. If the tag verifies correctly, \(\mathcal {A}_{ mac }\) locally decrypts the ciphertext using the sampled key and (classical) queries to \( \rho \) and sends the message back to \(\mathcal {A}\), otherwise, i.e., if the tag was invalid, \(\mathcal {A}_{ mac }\) simply returns \(\bot \) to \(\mathcal {A}\). Every (quantum) query by \(\mathcal {A}\) to \( \rho \) is simply forwarded by \(\mathcal {A}_{ se }\). \(\square \)
C C QS2 Proofs
1.1 I.9 C.1 Proof of Theorem 14
Proof
We construct the following adversary \(\mathcal {A} = (\mathcal {A}_{ 1 },\mathcal {A}_{ 2 })\). It picks a nonce
 and prepares the states \(\mathinner {|{\varphi _{0}}\rangle } = H\mathinner {|{0^{ \mu }}\rangle } = \mathinner {|{+}\rangle }^{\otimes \mu }\) and \(\mathinner {|{\varphi _{1}}\rangle } = \mathinner {|{0^{ \mu }}\rangle }\). It outputs the state
and prepares the states \(\mathinner {|{\varphi _{0}}\rangle } = H\mathinner {|{0^{ \mu }}\rangle } = \mathinner {|{+}\rangle }^{\otimes \mu }\) and \(\mathinner {|{\varphi _{1}}\rangle } = \mathinner {|{0^{ \mu }}\rangle }\). It outputs the state
Upon receiving the state \(\mathinner {|{\psi }\rangle }\), \(\mathcal {A}_{ 2 }\) applies the Hadamard operator to it and measures the register. If the measurement output is \(0^{ \mu }\), \(\mathcal {A}_{ 0 }\) outputs 0, otherwise, it outputs 1.
Before analysing the different cases, note that measuring the nonce register as well as tracing out one of the message registers does not affect the other registers as they are all unentangled. Let us now start with the case distinctions.
If \(b=0\), the game encrypts the left message, i.e., the state
\(\mathcal {A}_{ 2 }\) receives the state
i.e., the state \(\mathinner {|{\varphi }\rangle }\) is left unchanged. Application of the Hadamard operator therefore yields the state \(\mathinner {|{0^{ \mu }}\rangle }\), for which the measurement outcome is \(0^{ \mu }\) with probability 1. Thus we get
If \(b=1\), \(\mathcal {A}_{ 2 }\) receives the state
Application of the Hadamard operator yields
Measurement yields a random \(x \in \{0,1\}^{ \mu } \). Since \(\mathcal {A}_{ 2 }\) outputs 0 if and only if the measurement yields \(0^{ \mu }\), we obtain
Collecting everything yields
\(\square \)
Rights and permissions
Copyright information
© 2022 The Author(s), under exclusive license to Springer Nature Switzerland AG
About this paper
Cite this paper
Janson, C., Struck, P. (2022). Sponge-Based Authenticated Encryption: Security Against Quantum Attackers. In: Cheon, J.H., Johansson, T. (eds) Post-Quantum Cryptography. PQCrypto 2022. Lecture Notes in Computer Science, vol 13512. Springer, Cham. https://doi.org/10.1007/978-3-031-17234-2_12
Download citation
DOI: https://doi.org/10.1007/978-3-031-17234-2_12
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-031-17233-5
Online ISBN: 978-3-031-17234-2
eBook Packages: Computer ScienceComputer Science (R0)