Abstract
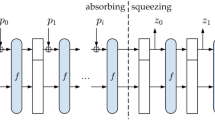
In recent years, many hardware implementations of the SHA-3 have been proposed to improve throughput, frequency, efficiency, or area. However, the increasing demand for hashing larger data requires other improved implementations of this function in terms of throughput. In this work, two different implementations of the Secure Hash Algorithm SHA-3 are proposed, the designs are based on the pipeline technique. Our main focus was to maximize the throughput of this function, also to analyze the impact of the use of the pipelining technique on this function The proposed designs are coded using VHDL language and implemented on two different devices Virtex 5 and 6 FPGA. The designs reach a maximum Throughput almost double 16.24 Gbps in the 2 stages external pipelining, and 17.01 Gbps in the internal pipelining. In contrast, it’s worth 8.12 Gbps on Virtex 5 for 512 bits output length in the case of one stage. However, this increase in the throughput will negatively affect the Area needed to implement the design.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Rao, M., Newe, T., Grout, I.: Secure Hash Algorithm-3(SHA-3) implementation on Xilinx FPGAs, suitable for IoT applications. Int. J. Smart Sens. Intell. Syst. 7(5), 1–6 (2020). https://doi.org/10.21307/ijssis-2019-018
Velmurugadass, P., Dhanasekaran, S., Anand, S.S., Vasudevan, V.: Enhancing Blockchain security in cloud computing with IoT environment using ECIES and cryptography hash algorithm. Materials Today: Proceedings, p. S2214785320364014 (2020). https://doi.org/10.1016/j.matpr.2020.08.519
Yang, Y., He, D., Kumar, N., Zeadally, S.: Compact hardware implementation of a SHA-3 core for wireless body sensor networks. IEEE Access 6, 40128–40136 (2018). https://doi.org/10.1109/ACCESS.2018.2855408
Li, X., Ibrahim, M.H., Kumari, S., Sangaiah, A.K., Gupta, V., Choo, K.-K.R.: Anonymous mutual authentication and key agreement scheme for wearable sensors in wireless body area networks. Comput. Netw. 129(2), 429–443 (2017). https://doi.org/10.1016/j.comnet.2017.03.013
Dworkin, M.J.: SHA-3 standard: permutation-based hash and extendable-output functions. Nat. Inst. Stand. Technol. NIST FIPS 202 (2015). https://doi.org/10.6028/NIST.FIPS.202
Rivest, R.: The MD5 Message-Digest Algorithm (1991). http://altronic-srl.com.ar/md5%20algoritmo.pdf
SHA-1 Standard, National Institute of Standards and Technology (NIST), Secure Hash Standard, FIPS PUB 180–1 (1995)
NIST: Federal information processing standard 180–2, secure hash standard. https://csrc.nist.gov/csrc/media/publications/fips/180/2/archive/2002-08-01/documents/fips180-2.pdf
Wong, M.M., Haj-Yahya, J., Sau, S., Chattopadhyay, A.: A new high throughput and area efficient SHA-3 implementation. In: 2018 IEEE International Symposium on Circuits and Systems (ISCAS), Florence, May 2018, pp. 1–5 (2018). https://doi.org/10.1109/ISCAS.2018.8351649
Neelima, S., Brindha, R.: 512 bit-SHA3 design approach and implementation on field programmable gate arrays. IJRES 8(3), 169 (2019). https://doi.org/10.11591/ijres.v8.i3.pp169-174
Sideris, A., Sanida, T., Dasygenis, M.: High throughput implementation of the keccak hash function using the Nios-II processor. Technologies 8(1), 15 (2020). https://doi.org/10.3390/technologies8010015
Mestiri, H., Kahri, F., Bouallegue, B., Machhout, M.: An efficient hardware implementation of KECCAK algorithm. 3(12), 5 (2017)
Athanasiou, G.S., Makkas, G.-P., Theodoridis, G.: High throughput pipelined FPGA implementation of the new SHA-3 cryptographic hash algorithm. In: 2014 6th International Symposium on Communications, Control and Signal Processing (ISCCSP), Athens, Greece, May 2014, pp. 538–541 (2014). https://doi.org/10.1109/ISCCSP.2014.6877931
Arshad, A., Kundi, D.-S., Aziz, A.: Compact implementation of SHA3–512 on FPGA. In: 2014 Conference on Information Assurance and Cyber Security (CIACS), Rawalpindi, Pakistan, June 2014, pp. 29–33 (2014). https://doi.org/10.1109/CIACS.2014.6861327
Honda, T., Guntur, H., Satoh, A.: FPGA implementation of new standard hash function Keccak. In: 2014 IEEE 3rd Global Conference on Consumer Electronics (GCCE), Tokyo, Japan, October 2014, pp. 275–279 (2014). https://doi.org/10.1109/GCCE.2014.7031105
Sundal, M., Chaves, R.: efficient FPGA implementation of the SHA-3 hash function. In: 2017 IEEE Computer Society Annual Symposium on VLSI (ISVLSI), Bochum, Germany, July 2017, pp. 86–91 (2017).https://doi.org/10.1109/ISVLSI.2017.24
Rao, M., Newe, T., Grout, I., Mathur, A.: High speed implementation of a SHA-3 core on Virtex-5 and Virtex-6 FPGAs. J. Circ. Syst. Comput. 25(07), 1650069 (2016). https://doi.org/10.1142/S0218126616500699
Mestiri, H., Kahri, F., Bedoui, M., Bouallegue, B., Machhout, M.: High throughput pipelined hardware implementation of the keccak hash function. In: 2016 International Symposium on Signal, Image, Video and Communications (ISIVC), pp. 282–286 (2016). https://doi.org/10.1109/ISIVC.2016.7894001
Michail, H.E., Ioannou, L., Voyiatzis, A.G.: Pipelined SHA-3 implementations on FPGA: architecture and Performance analysis. In: Proceedings of the Second Workshop on Cryptography and Security in Computing Systems - CS2 2015, Amsterdam, Netherlands, pp. 13–18 (2015). https://doi.org/10.1145/2694805.2694808
Keccak specifications.pdf
Paar, C., Pelzl, J.: Understanding Cryptography: A Textbook for Students and Practitioners. Springer, Berlin, Heidelberg (2010). https://doi.org/10.1007/978-3-642-04101-3
Kahri, F., Mestiri, H., Bouallegue, B., Machhout, M.: High speed FPGA implementation of cryptographic KECCAK hash function crypto-processor. J. Circ. Syst. Comput. 25(04), 1650026 (2016). https://doi.org/10.1142/S0218126616500262
Provelengios, G., Kitsos, P., Sklavos, N., Koulamas, C.: FPGA-based design approaches of keccak hash function. In: 2012 15th Euromicro Conference on Digital System Design, Cesme, Izmir, Turkey, September 2012, pp. 648–653 (2012). https://doi.org/10.1109/DSD.2012.63
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2022 The Author(s), under exclusive license to Springer Nature Switzerland AG
About this paper
Cite this paper
Assad, F., Fettach, M., Elotmani, F., Tragha, A. (2022). Two-Stage Pipelining Implementation of the Secure Hash Algorithm SHA-3 on Virtex-5 and Virtex-6 FPGAs. In: Maleh, Y., Alazab, M., Gherabi, N., Tawalbeh, L., Abd El-Latif, A.A. (eds) Advances in Information, Communication and Cybersecurity. ICI2C 2021. Lecture Notes in Networks and Systems, vol 357. Springer, Cham. https://doi.org/10.1007/978-3-030-91738-8_51
Download citation
DOI: https://doi.org/10.1007/978-3-030-91738-8_51
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-030-91737-1
Online ISBN: 978-3-030-91738-8
eBook Packages: Intelligent Technologies and RoboticsIntelligent Technologies and Robotics (R0)