Abstract
Secret sharing schemes protect secrets by distributing them over different locations (share holders). In particular, in k out of n threshold schemes, security is assured if throughout the entire life-time of the secret the adversary is restricted to compromise less than k of the n locations. For long-lived and sensitive secrets this protection may be insufficient.
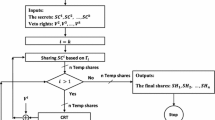
We propose an efficient proactive secret sharing scheme, where shares are periodically renewed (without changing the secret) in such a way that information gained by the adversary in one time period is useless for attacking the secret after the shares are renewed. Hence, the adversary willing to learn the secret needs to break to all k locations during the same time period (e.g., one day, a week, etc.). Furthermore, in order to guarantee the availability and integrity of the secret, we provide mechanisms to detect maliciously (or accidentally) corrupted shares, as well as mechanisms to secretly recover the correct shares when modification is detected.
Chapter PDF
Similar content being viewed by others
Keywords
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
M. Bellare and P. Rogaway, Optimal Asymmetric Encryption, Eurocrypt’ 94.
G.R. Blakley, Safeguarding Cryptographic Keys, AFIPS Con. Proc (v. 48), 1979, pp 313–317.
R. Canetti and A. Herzberg, Maintaining Security in the Presence of Transient Faults, Proc. Crypto’94 (LNCS 839), pp. 425–438.
R. Canetti and A. Herzberg, Proactive Maintenance of Authenticated Communication, manuscript, 1995.
B. Chor, S. Goldwasser, S. Micali and B. Awerbuch, Verifiable Secret Sharing and Achieving Simultaneous Broadcast, Proc. of IEEE Focs 1985, pp. 335–344.
M. Blum and S. Micali, How to Construct Cryptographically Strong Sequences of Pseudorandom Bits. SIAM J. Comp. 13, 1984.
A. De Santis, Y. Desmedt, Y. Frankel, and M. Yung, How to Share a Function Securely, ACM STOC 94.
Y. Desmedt and Y. Frankel, Threshold cryptosystems, In G. Brassard, editor, Advances in Cryptology, Proc. of Crypto’ 89 (Lecture Notes in Computer Science 435), pages 307–315. Springer-Verlag, 1990.
D. Dolev, C. Dwork, O. Waarts, and M. Yung, Perfectly Secure Message Transmission, Proc. 31st Annual Symposium on the Foundations of Computer Science, 1990, (also JACM).
T. El Gamal, A Public key cryptosystem and a signature scheme based on discrete logarithm, IEEE Trans. on Information Theory 31, 465–472, 1985.
P. Feldman, A Practical Scheme for Non-Interactive Verifiable Secret Sharing, Proc. of the 28th IEEE Symposium on the Foundations of Computer Science, 1987, 427–437
S. Goldwasser and S. Micali, Probabilistic Encryption, J. Com. Sys. Sci. 28 (1984), pp 270–299.
S. Goldwasser, S. Micali and R. Rivest, A Secure Digital Signature Scheme, Siam Journal of Computing, Vol. 17,2 (1988), pp. 281–308.
A. Herzberg, M. Jakobsson, S. Jarecki, H. Krawczyk and M. Yung, Proactive Public Key and Signatures Systems, draft.
D.L. Long and A. Wigderson, The Discrete Log. Problem Hides O(Log N) Bits. SIAM J. Comp. 17, 1988, pp. 363–372.
T. P. Pedersen, Distributed Provers with Applications to Undeniable Signature, Proc. Eurocrypt’ 91 (LNCS 547), pp. 221–242.
T. P. Pedersen, Non-Interactive and Information-Theoretic Secure Verifiable Secret Sharing, Proc. Crypto’91 (LNCS 576), pp. 129–140.
R. Ostrovsky and M. Yung, How to withstand mobile virus attacks, Proc. of the 10th ACM Symp. on the Princ. of Distr. Comp., 1991, pp. 51–61.
A. Shamir. How to share a secret, Commun. ACM, 22 (1979), pp 612–613.
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 1995 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Herzberg, A., Jarecki, S., Krawczyk, H., Yung, M. (1995). Proactive Secret Sharing Or: How to Cope With Perpetual Leakage. In: Coppersmith, D. (eds) Advances in Cryptology — CRYPT0’ 95. CRYPTO 1995. Lecture Notes in Computer Science, vol 963. Springer, Berlin, Heidelberg. https://doi.org/10.1007/3-540-44750-4_27
Download citation
DOI: https://doi.org/10.1007/3-540-44750-4_27
Published:
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-60221-7
Online ISBN: 978-3-540-44750-4
eBook Packages: Springer Book Archive