Abstract
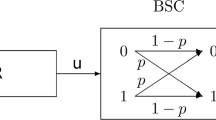
In this paper we present new and more accurate estimates of the biases of the linear approximation of the FSM of the stream cipher SNOW 2.0. Based on improved bias estimates we also find a new linear distinguisher with bias 2− − 86.9 that is significantly stronger than the previously found ones by Watanabe et al. (2003) and makes it possible to distinguish the output keystream of SNOW 2.0 of length 2174 words from a truly random sequence with workload 2174. This attack is also stronger than the recent distinguishing attack by Maximov and Johansson (2005). We also investigate the diffusion properties of the MixColumn transformation used in the FSM of SNOW 2.0 and present some evidence why much more efficient distinguishers may not exist.
Chapter PDF
Similar content being viewed by others
References
Billet, O., Gilbert, H.: Resistance of SNOW 2.0 against algebraic attacks. In: Menezes, A. (ed.) CT-RSA 2005. LNCS, vol. 3376, pp. 19–28. Springer, Heidelberg (2005)
Coppersmith, D., Halevi, S., Jutla, C.: Cryptanalysis of stream ciphers with linear masking. In: Yung, M. (ed.) CRYPTO 2002. LNCS, vol. 2442, pp. 515–532. Springer, Heidelberg (2002)
Ekdahl, P., Johansson, T.: A new version of the stream cipher SNOW. In: Nyberg, K., Heys, H.M. (eds.) SAC 2002. LNCS, vol. 2595, pp. 47–61. Springer, Heidelberg (2003)
ETSI/SAGE. Specification of the 3GPP confidentiality and integrity algorithms UEA2 & UIA2. Document 2: SNOW 3G specification, draft version 0.5 (August 2005), http://www.3gpp.org/ftp/tsg_sa/WG3_Security/TSGS3_40_Slovenia/Docs/S3050579%20.zip
ETSI/SAGE. Specification of the 3GPP confidentiality and integrity algorithms UEA2 & UIA2. Document 5: Design and evaluation report, version: 1.0, http://www.3gpp.org/ftp/tsg_sa/WG3_Security/TSGS3_42_Bangalore/Docs/S3060180.zip
Matsui, M.: Linear Cryptanalysis Method for DES Cipher. In: Helleseth, T. (ed.) EUROCRYPT 1993. LNCS, vol. 765, pp. 386–397. Springer, Heidelberg (1994)
Maximov, A., Johansson, T.: Fast Computation of Large Distributions and Its Cryptographic Applications. In: Roy, B. (ed.) ASIACRYPT 2005. LNCS, vol. 3788, pp. 313–332. Springer, Heidelberg (2005)
ECRYPT NoE. eSTREAM, the ECRYPT stream cipher project (2005), http://www.ecrypt.eu.org/stream/
Nyberg, K.: Correlation theorems in cryptanalysis. Discrete Applied Mathematics 111, 177–188 (2001)
Wallén, J.: Linear Approximations of Addition Modulo 2n. In: Johansson, T. (ed.) FSE 2003. LNCS, vol. 2887, pp. 261–273. Springer, Heidelberg (2003)
Watanabe, D., Biryukov, A., De Cannière, C.: A Distiguishing Attack of SNOW 2.0 with Linear Masking Method. In: Matsui, M., Zuccherato, R.J. (eds.) SAC 2003. LNCS, vol. 3006, pp. 222–233. Springer, Heidelberg (2004)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2006 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Nyberg, K., Wallén, J. (2006). Improved Linear Distinguishers for SNOW 2.0. In: Robshaw, M. (eds) Fast Software Encryption. FSE 2006. Lecture Notes in Computer Science, vol 4047. Springer, Berlin, Heidelberg. https://doi.org/10.1007/11799313_10
Download citation
DOI: https://doi.org/10.1007/11799313_10
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-36597-6
Online ISBN: 978-3-540-36598-3
eBook Packages: Computer ScienceComputer Science (R0)