Abstract
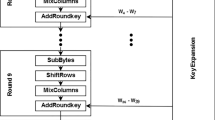
Security is a concern in the design of smartcards. It is possible to leak much side channel information related to secret key when cryptographic algorithm runs on smartcards. Power analysis attacks are a very strong cryptanalysis by monitoring and analyzing power consumption traces. In this paper, we experiment Exclusive OR operation. We also analyze the tendency of state-of-the-art regarding hardware countermeasures and experiments of Hamming-Weights on power attacks. It can be useful to evaluate a cryptosystem related with hardware security technology.
Access provided by Autonomous University of Puebla. Download to read the full chapter text
Chapter PDF
Similar content being viewed by others
References
Kocher, P., Jaffe, J., Jun, B.: Differential Power Analysis. In: Wiener, M. (ed.) CRYPTO 1999. LNCS, vol. 1666, pp. 388–397. Springer, Heidelberg (1999)
MaDaniel III, L.T.: An Investigation of Differential Power Analysis Attacks on FPGA-based encryption Systems, available to scholar.lib.vt.edu, Master of Science in Electrical Engineering (May 2003)
Ors, S.B., Oswald, E., Preneel, B.: Power-Analysis Attacks on an FPGA-First Experimental Results. In: Walter, C.D., Koç, Ç.K., Paar, C. (eds.) CHES 2003. LNCS, vol. 2779, pp. 35–50. Springer, Heidelberg (2003)
Wollinger, T., Paar, C.: How Secure Are FPGAs in Cryptographic Applications(Long version), Report 2003 /119, IACR (2003), available on http://eprint.iacr.org
Tiu, C.C.: A New Frequency-Based Side Channel Attack for Embedded Systems, A Master thesis, in the University of Waterloo (2005)
Junee, R.: POWER ANALYSIS ATTACKS: A Weakness in Cryptographic Smart Cards and Microprocessors. In: Bachelor of Computer Engineering & Bachelor of Commerce (November 2002)
Oswald, E.: On Side-Channel Attacks and the Application of Algorithmic Countermeasures, A PhD Thesis in Graz University of Technology, IAIK (May 2003)
Mangard, S.: Calculation and simulation of the Susceptibility of Cryptographic Devices to Power-Analysis Attacks, A Diploma Thesis, in Graz University of Technology, IAIK (2003)
KULRD & SCARD Consortium, Side Channel Analysis Resistant Design Flow, IST-2002-507270, SCARD-KULRD-D4.1 (2005), available on http://www.scard-project.org
den Hartog, J., et al.: PINPAS: a tool for power analysis of smartcards. In: SEC 2003, IFIP WG 11.2 Small Systems Security, pp. 447–451 (2003)
den Hartog, J.I., de Vink, E.P.: Virtual Analysis and Reduction of Side-Channel Vulnerabilities of Smartcards (2005), available on http://www.win.tue.nl/ecss
Mangard, S., Popp, T., Gammel, B.M.: Side-Channel Leakage of Masked CMOS Gates. In: Menezes, A. (ed.) CT-RSA 2005. LNCS, vol. 3376, pp. 351–365. Springer, Heidelberg (2005)
Tiri, K., Verbauwhede, I.: A Logic Level Design Methodology for a Secure DPA Resistant ASIC or FPGA Implementation. In: DATE 2004, pp. 246–251. IEEE Computer Society, Los Alamitos (2004)
Mangard, S.: Hardware Countermeasures against DPA. A Statistical Analysis of Their effectiveness. In: Okamoto, T. (ed.) CT-RSA 2004. LNCS, vol. 2964, pp. 222–235. Springer, Heidelberg (2004)
Tiri, K., Verbauwhede, I.: A VLSI Design Flow for Secure Side-Channel Attack Resistant ICs. In: Proceedings of the Design, Automation and Test in Europe Conference and Exhibition, DATE 2005 (2005)
Kris, T., Moonmoon, A., Ingrid, V.: A Dynamic and Differential CMOS Logic with Signal Independent Power Consumption to withstand Differential power Analysis on Smart Cards. In: 28th European Solid-State Circuits Conference (2002)
Kulikowski, K.J., Su, M., Smirnov, A., Taubin, A., Karpovsky, M.G., Daniel, M.: Delay Insensitive Encoding and Power Analysis: A Balancing Act. In: 11th IEEE International Symposium on Asynchronous Circuits and Systems: ASYNC 2005, pp. 116–125 (2005)
Moore, S., et al.: Improving SmartCard Security using Self-timed Circuits (2003), available on http://actes.sstic.org/SSTIC03/Rump_sessions
Moore, S., Anderson, R., Mullins, R., Taylor, G.: Balanced self-checking asynchronous logic for smart card applications. The Microprocessors and Microsystems Journal (2003)
Feyt.: Countermeasure method for a microcontroller based on a pipeline architecture, US PATENT 20030115478 A1 (2003)
Oswald, E., Mangard, S., Pramastaller, N., Rijmen, V.: A Side-Channel Analysis Resistant Description of the AES S-Box. In: Gilbert, H., Handschuh, H. (eds.) FSE 2005. LNCS, vol. 3557, pp. 413–423. Springer, Heidelberg (2005)
Tir, K., Verbauwhede, I.: Simulation Models for Side-Channel Information Leaks. In: ACM 1-59593-058-2/05/0006, DAC 2005 (2005)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2006 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Ahn, M., Lee, H. (2006). Experiments and Hardware Countermeasures on Power Analysis Attacks. In: Gavrilova, M., et al. Computational Science and Its Applications - ICCSA 2006. ICCSA 2006. Lecture Notes in Computer Science, vol 3982. Springer, Berlin, Heidelberg. https://doi.org/10.1007/11751595_6
Download citation
DOI: https://doi.org/10.1007/11751595_6
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-34075-1
Online ISBN: 978-3-540-34076-8
eBook Packages: Computer ScienceComputer Science (R0)