Abstract
The precise two-terminal reliability calculation becomes more difficult when the numeral of components of the complex system increases. The accuracy of approximation methods is often adequate for expansive coverage of practical applications, while the algorithms and computation time are typically simplified. As a result, the reliability bounds of two-terminal systems and estimation methods have been established. Our method for determining a complex system's reliability lower and upper bounds employs a set of minimal paths and cuts. This paper aims to present a modern assessment of reliability bounds for coherent binary systems and a comparison of various reliability bounds in terms of subjective, mathematical, and efficiency factors. We performed the suggested methods in Mathematica and approximated their interpretation with existing ones. The observed results illustrate that the proposed Linear and Quadratic bounds (LQb) constraint is superior to Esary-Proschan (EPb), Spross (Sb), and Edge-Packing (EDb) bounds in the lower bond, and the EDb bound is preferable to other methods above in the upper bond. This modification is attributed to sidestepping certain duplicative estimations that are part of the current methods. Given component test data, the new measure supplies close point bounds for the system reliability estimation. The Safety–Critical-System (SCS) uses an illustrative model to show the reliability designer when to implement certain constraints. The numerical results demonstrate that the proposed methods are computationally feasible, reasonably precise, and considerably speedier than the previous algorithm version. Extensive testing on real-world networks revealed that it is impossible to enumerate all minimal paths or cuts, allowing one to derive precise bounds.
Similar content being viewed by others
Avoid common mistakes on your manuscript.
1 Introduction
One of the main challenges in reliability theory is to establish a system's reliability by examining its independent components' reliability. In order to tackle this challenge, approximative techniques for the system's reliability that are both computationally efficient and effective have been created. It has been found that the bounding approach is a beneficial approximation method. To assess system reliability, it is important to determine both the minimum and maximum bounds. We conducted a thorough evaluation of these bounds for binary systems, taking into account various assumptions about the components' reliabilities. For mechanical systems, a common belief is that reliability systems can be characterized by combining parallel and series collections. However, more than this approach is needed to explain the reliability systems of many complex engineering systems. Therefore, a simple series or parallel arrangement is inadequate to describe such systems. We conducted detailed numerical comparisons to provide a comprehensive assessment of these constraints.
When computing system reliability, a more efficient algorithm is always necessary. The algorithm should be correct in theory, accurate mathematically, and easy to compute. The algorithm described can solve problems with current models and provide improved lower and upper bounds for estimating system reliability. It can be used to estimate the reliability of a two-terminal network by utilizing minimal path (cut) sets. Calculating system reliability accurately is usually an NP-hard problem. Fortunately, several standard methods are available to compute both the reliability lower and the reliability upper bounds of the system. Esary and Proschan (1963) presented a significant paper proving that the trivial bounds can be improved by utilizing the minimal path and cut description of the structure-function. The EPb method is a graph transformation method to assess two-terminal reliability. The upper bound graph is a combination of parallel minimal path sets. If a component appears on multiple minimal path sets, it will be duplicated to create a unique component for each minimal path sets. The lower bound is a collection of all possible combinations of minimal cut sets, duplicating components similarly. When tackling design problems that prioritise caution, it is essential to consider lower bounds for the most informed approach.
Beichelt and Sproß (1989) highlight the importance of clearly defined upper and lower reliability bounds. Simple system paths, cut sets, and disjoint sums can be used to make these bounds. The Sb method is critical because they recognize that many approximation methods rely on complicated mathematics. Instead, it emphasizes the value of having short upper and lower bounds for measuring system reliability. Creating these boundaries requires minimal paths and cuts within the system and generating disjoint sums.
Colbourn (1988) identifies the EDb approaches as one of the numerous effective and widely utilized approximation approaches for reliability that only necessitates discussing some minimal paths or cut sets. The EDb techniques calculate lower and upper bounds based on disjoint edge minimal-path (cut) sets to evaluate system reliability. To ensure accurate reliability calculations, it's important to revise edge-packing techniques. Currently, these techniques must consider the potential of considerable minimal path sets that contain only series and parallel structures, actually if they have joint components. A better way to increase accuracy while maintaining efficiency is by utilizing minimal path sets in parallel and series reduction techniques. This method is more effective than solely concentrating on edge-disjoint minimal path sets.
Jin and Coit (2003) calculated the minimum and maximum bounds of system reliability by adding up the LQb of unreliability for each minimal cut set or path set. The LQb method is used to compute replicated components' highly efficient reliability covariance. Hence LQb significantly enhances the precision and accuracy of the estimation model for network reliability in the two-terminal form.
More efficient approximation methods have been proposed to evaluate more complex networks' reliability. Kaushik and Banka (2015) propose an estimated manufactured neural system (AANN) technique for the network reliability problem when complex system design is required. Datta and Goyal (2017) proposed a "sum of disjoint products" approach to minimize repetitive calculations when determining precise reliability based on flow vectors. Zhu and Zhang (2019) present edge-packing approaches that approximate network reliability more precisely and effectively. In this study, we examine the available bounds from the literature. Xiao et al. (2021) present a new robust timing quality network (RTFN) for obtaining features in time series type. It is made up of a temporal feature network (TFN) and a long brief memory (LSTM)-based focus network (LSTMaN). Xing et al. (2022) presented the projection of a Timecut-expanded performance of the same sequence guided by a faintly augmented sequence. Self-distillation facilitates the transfer of knowledge from upper to lower levels, thereby facilitating the extraction of low-level semantic data.=. Datta and Goyal (2023) suggest three directions if duplicative and disjoint Lower Boundary Flow Vectors as well as to disjoint the non-disjointed Lower Boundary Flow Vectors and present some useful applications of the stochastic system reliability computation.
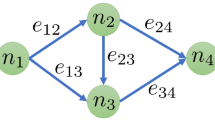
Graphs are typically used for system definition in engineering (Kuo and Zuo 2003; Mutar and Hassan 2017; Todinov 2013). A graph, denoted as G = (V, E), has a non-empty set V representing its vertices, and a non-empty set E represents a set of pairwise links (also called edges) between those nodes. The probability of the nodes and edges being functional is considered. (Beichelt 2012; Mutar 2022b, 2022c). The focus of this study is to highlight the importance of maintaining communication between source and sink nodes, even in the event of a node or edge failure. This study assumes that all nodes are reliable, so we will only explore techniques for dealing with edge failures. The probability of successful data transfer between two source and sink nodes referred to as two-terminal reliability, depends on the quality of the connecting paths. On the other hand, the reliability of the system is determined by the probability of these two nodes being connected by the most dependable and effective routes, referred to as minimal paths or cuts (Gertsbakh and Shpungin 2011; Mutar 2022d; Rausand 2014). In order to determine reliability bounds, it is essential first to compute and list all the minimal cut (path) sets. The underlying principle here is that every edge in a minimal path set must operate correctly to secure the linkage between two nodes. The connection cannot be guaranteed if any element in the set malfunctions. Minimal paths are the minor path sets without other path sets. A minimum path is set for two-terminal reliability, a process route between the terminals. It's crucial to understand that if all the edges in a minimal cut set fail, it could lead to disconnecting a pair of nodes. However, if some elements in the set are still functional, there's no guarantee of disconnection. To be considered minimal, a cut set must consist solely of a minimal set. (Rodionov and Rodionova 2013). Mutar (2020) described a technique to obtain the IM matrix by originating minimal cut sets from minimal path sets. Alternatively, the algebraic principles were employed to generate the minimal-cut sets for the complex system. One can create the system's matrix-based minimal cut arrangement by algebraically transposing an IM matrix with the truth matrix. This process is commonly used to establish the system's reliability boundaries.
Numerous engineering publications, books, and papers delve into hypothetical and experimental viewpoints about complex systems, networks, and reliability theory (Aggarwal 1993). For example, components in most communication systems have complex configurations, more than one technique (Hassan and Mutar, 2017; Hassan and Udriște 2015; Horváth 2013; Jula and Costin 2012; Malik et al. 2020; Mi et al. 2018; Mutar 2022d; Sharma 2014) was used. Mutar and Hassan (2022) show how mathematical detection tests can be involved in HPOSS to determine the reliability of complex systems. Xiao et al. (2022) proposal, the ETNEEG algorithm demonstrated superior performance compared to fourteen other algorithms on the given datasets.
This paper proposes a new technique to estimate the reliability of engineering design projects. The approach uses a matrix-based technique to compute the minimal paths and cuts of the SCS system with seven components. This system is complex, but the matrix-based deduction simplifies the network and reduces its complexity. After that, various techniques were attempted to bounds reliability, with some advancements based on more modular components. After that, several methods were used to achieve reliability in bounds, with some advancements based on minimal paths and cuts. Complete evaluation of reliability bounds for coherent binary systems. Considering qualitative, quantitative, and imposed on goods, compare these bounds. The structure of the dissertation is as tracks: In Section 1, we presented an overview of the relevant literature and reliability bounds for coherent binary systems. Section 2 provides the necessary theoretical foundations for coherent binary systems and a summary of the most significant reliability bounds identified in the literature. In Section 3, improved mathematical formulas for reliability-bound approaches are established. These formulas can then be applied to a real-world system. In Section 4, numerical comparisons of the reliability bounds are shown, and Sections 5 and 6 detail the results, discussion, and conclusion, respectively.
2 Some important concepts
2.1 Reliability function
A system (network) is considered coherent if its structural function is monotone and each element is essential (Important system components are those whose states are determined by the conditions of other components). The states of component \({x}_{i}\) are determined by whether it is functioning during a certain period (\({x}_{i}\)=1) or has failed (\({x}_{i}\)=0). The binary random variable of component x is represented in Eq. (1).
Therefore, each component's state is defined by the vector \({\varvec{X}} = \left({x}_{1},{x}_{2},\dots ,{x}_{n}\right)\). The system's requirements can be determined by the binary function φ(X), which performs as the structural function of the system. If \({x}_{1},{x}_{2},\dots ,{x}_{n}\) are i.i.d. random variables with each component having a probability of \(Pr\left({x}_{i}\right)={r}_{i}\), then the reliability of the system \({R}_{Exact}\) can be represented by the component reliabilities \({r}_{1},{r}_{2},\dots ,{r}_{n}\). Also, the system's unreliability \({Q}_{Exact}\) can be computed as:
where \({q}_{i} = 1- {r}_{i}\). Therefore, Eq. (2) shows that the system's unreliability increases with the number of components, which helps in identifying the components that are prone to failure.
2.2 Exact system reliability
This section will use powerful methods to accurately evaluate the reliability of systems that depend on minimal paths. This approach involves gathering all available minimal paths and creating an incidence matrix (Mutar 2020, 2022a, 2022c, 2022d). For the creation of an incidence matrix with k minimal paths (\({P}_{1}, {P}_{2},\dots , {P}_{k}\)), use the minimal paths as rows and the components as columns. This method ensures the matrix is accurate and efficient, allowing easy and effective analysis. Technically, using the proposed algorithm in MATHEMATICA software (Appendix), compute each minimal path as an incidence matrix (IM) as the following:
where \({e}_{ij}=1\) iff\({x}_{j}\in {P}_{i}\), otherwise \({e}_{ij}=0\) and\(i = 1, 2,\dots ,k , j = 1; 2,\dots , n\). Also, the proposed algorithm can be used to generate the minimal cut matrix (CM) to discover all minimal cut sets. In the CM matrix, the components are organized by column and the cuts by row (Mutar 2020). Hence, the failure conditions of components can be calculated using the proposed algorithm in MATHEMATICA software (Appendix) to compute a single matrix, given as
To find all possible minimal cuts
\({C}_{1}, {C}_{2},\dots , {C}_{m}\) in a complex system, the CM matrix is typically utilized, and Mathematica can be used to conduct a minimal cut deduction technique that will give all available minimal cuts (Kuo and Zuo 2003; Marichal 2016). With a parallel arrangement of each minimal path and each minimal cut contained in these rows, the \({R}_{Exact}\) can be determined utilizing the formula:
The random variables of Bernoulli (\({x}_{i}^{n}= {x}_{i}\)) imply that the system's structural function can only assume the importance of 1 or 0 (\({1}^{n} = 1\) and \({0}^{n} = 0\)). This connection can be expressed using a substitution rule (Hassan and Mutar, 2017; Hassan and Mutar, 2017; Pyzdek and Keller 2003; Todinov 2013).
3 Reliability bounds measurement approach
3.1 Spross bounds
Given that most approximation methodologies primarily depend on advanced mathematics, Spross highlights the significance of having a specific coverage for system reliability, with both the upper and lower bound. These bounds can be generated with minimal effort by using only a limited number of paths (\({P}_{1}, {P}_{2},\dots , {P}_{k}\)) of the system and by computing disjoint sums as follows:
1- For \({P}_{1}\) assume that \({A}_{\mathrm{0,1}}=\{{P}_{1}\}\) and \({\alpha }_{1}={A}_{\mathrm{0,1}}\).
2- Define the complement set \({P}_{j} -{A}_{s,i}\) of the path \({A}_{s,i}\) such that \({P}_{j} -{A}_{s,i}=\{{x}_{a}|{x}_{a}\in {P}_{j} and {x}_{a}\notin {A}_{s,i}\}\) for \(0\le s<j\le i\) and \(a=\mathrm{1,2},\dots ,n.\)
-
If \({P}_{j} -{A}_{s,i}=\varnothing \) then \({A}_{j,i}=\{{A}_{s,i}\}\) and \({\alpha }_{i}={A}_{s,i}.\)
-
If \({x}_{a}\in {P}_{j} and \overline{{x }_{a}}\in {A}_{s,i}\) where \(\overline{{x }_{a}}=1-{x}_{a}\) then \({P}_{j} -{A}_{s,i}=\varnothing \) and \({\alpha }_{i}={A}_{s,i}.\)
-
If \({P}_{j} -{A}_{s,i}=\{{x}_{a}\}\) then \({A}_{j,i}=\{\overline{{x }_{a}}{A}_{s,i}\}\) and \({\alpha }_{i}={A}_{j,i}\).
-
If \({P}_{j} -{A}_{s,i}=\{{x}_{a}{x}_{b}\}\) for a < b < n then \({B}_{j,r}=\{\overline{{x }_{a}}{A}_{s,i}\}\) and \({B}_{j,r+1}=\{{x}_{a}\overline{{x }_{b}}{A}_{s,i}\}\) then \({A}_{j,i}=\{{B}_{j,r}, {B}_{j,r+1}\}\) and \({\alpha }_{i}=\sum_{r=1}^{r+1}{B}_{j,r}\) \(\forall {B}_{j,r}\in {A}_{j,i}\).
Consequently, every \({\alpha }_{i}\) is determined as a disjoint sum form. The characteristics of the structure–function of a coherent system are as follows:
Likewise, minimal cut sets \({C}_{1}, {C}_{2},\dots , {C}_{m}\) can be used in the above algorithm to obtain disjoint products. Then
Hence \({\beta }_{j}\) are disjoint Boolean functions. For many decades, scientists have been trying to find a solution to this issue (see (Rai et al. 1995), and (Soh and Rai 1993)). Reliability is calculated for a system using the disjoint sum form of \(\varphi \left(x\right)\) as follows:
By assume that \({P}_{1}, {P}_{2},\dots , {P}_{k}\) and \({C}_{1}, {C}_{2},\dots , {C}_{m}\) are the provided commonly known as the minimal path and cut sets, respectively, where \(1 \le g \le k\) and \(1 \le h \le m\), the lower reliability bound (\({R}_{LB}\)) as follows:
And the upper reliability bound (\({R}_{UB}\)) is computed as
For a repaired degree of precision, the calculations of \(\mu \left(g\right)\) and \(\gamma \left(h\right)\) is stopped when \(d\left(g, h\right)\le \epsilon \), where \(d\left(g, h\right)=\mu \left(g\right)-\gamma \left(h\right)\). In that case, g and h would need to be increased in size. Using benchmark networks from the literature, we compared the interpretation of the suggested technique with that of current methods, which are implemented in WOLFRAM MATHEMATICA.
3.2 Esary-proschan bound
The EPb method, which determines the reliability of two-terminal systems, involves transforming a graph. The graph represents the maximum possible reliability by combining parallel minimal cut sets \(({C}_{1}, {C}_{2},\dots , {C}_{m})\). Each component that appears on multiple minimal cut sets is duplicated to create a unique component on each minimal cut sets. The lower bound (\({R}_{LB}\)) is calculated as
where \({r}_{t}\) is the component type \(t\) reliability in the minimum possible cut set \({C}_{i}\). Alternatively, assuming that all components of the complete structure have failure paths \(({P}_{1}, {P}_{2},\dots , {P}_{k})\), the upper bound (\({R}_{UB}\)) is the probability of the union of all failure paths.
Here \({r}_{t}\) is the component type \(t\) reliability in the minimal path set \({P}_{i}\). In this case, one must count both the minimal cut sets and the minimal path sets to obtain upper and lower bounds. Lower bounds provide more information for those averse to risk problems with the design (Sebastio et al. 2014; Yang and Frangopol 2020).
3.3 Edge-packing bound
To illustrate the fundamental idea of EDb techniques, consider \({\varvec{P}}=({P}_{1}, {P}_{2},\dots , {P}_{k})\) to define the vector of all minimal path sets and \({\varvec{D}}{\varvec{P}}=\{{P}_{i}|{P}_{i}-{P}_{j}=\varnothing \forall {P}_{i},{P}_{j}\in {\varvec{P}}\}\) to represent the vector of only disjoint minimal path sets. The vector \({\varvec{D}}{\varvec{P}}\) can be used to estimate the lower reliability bound as follows:
where u is defined as the total number of disjoint minimal path sets. Then a second justification for identifying disjoint edge minimal cut sets is their value in defining the network reliability upper bound. Alternatively, consider \({\varvec{C}}=({C}_{1}, {C}_{2},\dots , {C}_{m})\) to define the vector of all minimal cut sets and \({\varvec{D}}{\varvec{C}}=\{{C}_{i}|{C}_{i}-{C}_{j}=\varnothing \forall {C}_{i},{C}_{j}\in {\varvec{C}}\}\) be the vector of disjoint edge minimal cut sets. Then \({\varvec{D}}{\varvec{C}}\) can be used to estimate the upper reliability bound.
Hence, w is the total number of disjoint minimal cut sets (Jin and Coit 2003; Zhu and Zhang 2019).
3.4 Linear and quadratic bound
The LQb method can be utilized to find the terminal-pair reliability bound of a system, given minimal cut sets \(({C}_{1}, {C}_{2},\dots , {C}_{m})\) for that system. The lower bound is calculated as
Hence \(\mathrm{Pr}\left(\overline{{x }_{t}}\right)=1-{r}_{t}, \forall \overline{{x }_{t}}\in {C}_{i}\). Similar components or hardware can be used in various network applications across the system, and an unmarried reliability assessment is applied universally. This causes the reliability assessments of the components to be statistically interdependent. Equation (17) occurs as the first three outcome terms of Eq. (13) when the system structure is parallel-series. However, Eq. (17) is not limited to parallel-series arrangements. Two-terminal arrangements are usually not in parallel series. Consequently, it is essential to recognize that Eqs. (13), (14), and (17) represent three distinct approximations of the two-terminal reliability.
Finally, a reliability upper bound can be received from the collection of all minimal path sets by using the formula:
When \(\mathrm{Pr}\left({x}_{t}\right)=1-{r}_{t}, \forall {x}_{t}\in {P}_{i}\). For each given reliability value, the LQb approach can be used to determine lower and upper bounds. When the reliability values of certain network components are low (Babaei and Rashidi-baqhi 2022; Mutar and Hassan 2022; Romero 2021; Wang et al. 2021).
4 Structure with modules
4.1 Logic diagram of SCS
The diagram in Fig. 1 displays the SCS that uses four sensors (\({M}_{1}, {M}_{2}, {M}_{3}\) and \({M}_{4}\)) to approximate the temperatures and stresses of zones A and B. The CD in the comparator detects a temperature or pressure difference more significant than a necessary value, which activates a system shutdown sign. The SCS is designed to increase resilience by implementing dual comparators and sensor pairs. Signal cables \({C}_{1}\) and \({C}_{2}\) transmit the sensor data to the comparators. Actually, if sensors \({M}_{1}\) and \({M}_{2}\) drop, the SCS will resume functioning. The remaining sensors \({M}_{3}\) and \({M}_{4}\) will send recorded temperature or pressure data through the signal cables \({C}_{1}\) and \({C}_{2}\) to the comparator CD (Jula and Costin 2012; Todinov 2013).
The system will only function when there is a direct path between two terminals in the network shown in Fig. 2, using operational components. The reliability of complex systems, like communication and electronic management systems, cannot be determined by simply using a series, parallel, or series-parallel configuration. These systems can exhibit high reliability that cannot be achieved through series-parallel arrangements (Hassan and Udriște 2015; Jula and Costin 2012; Todinov 2013).
To describe the reliability function of the SCS system depicted in Fig. 2, graph G = (V, E) consists of vertices V={a,b,…,e} and edges E={1,2,…,7} can be used. The graph G is a two-terminal, simple, and connected graph with edges that go in the same direction. By examining Fig. 3, the structural function can be determined between the source and sink nodes.
4.2 Calculate all minimal paths and minimal cuts of SCS
In order to represent all potential states of a system, the IM matrix is used. This matrix contains information about whether each component is in good or faulty condition. Additionally, it is essential to note that the IM matrix includes all possible minimal paths. The proposed algorithm in the Appendix can be used to calculate the IM matrix for a complex system illustrated in Fig. 3. The equation for this is provided as Equation (3). The following is its structure:
Consequently, the system has an n-component with a f\(\varphi :{\left\{0, 1\right\}}^{n} \to \left\{0, 1\right\}\), which represents the order of the system (in this special case,\({2}^{8}=256\)). Only the minimal paths were evaluated, as they indicate the current state of the system's function and the lack of significance. All minimal path sets of the CSC system are:
In this manner, the SCS system depicted in Fig. 3 can be represented utilizing all minimal paths in a series–parallel topology form with repeating subsystem components, as shown in Fig. 4.
Also, the CM matrix provides a comprehensive overview of the failure states of all components. The rows contain all the minimal cuts, while the columns sequence the components accordingly. Consequently, to generate Equation (4) of Fig. 3 by applying the proposed algorithm in Appendix, the CM matrix can be the following structure:
Therefore, six minimal cuts can be obtained.
All minimal cut sets of the complex system in Fig. 3 can be used to rearrange the system in a series–parallel topology with repeating subsystem components, as seen in Fig. 5.
The reliability estimates of the resultant components are statistically reliant on one another, regardless of whether they are in the same or other cut sets or path sets since minimal paths and minimal cuts can sometimes split a single system component into two or more components. Most existent models consider these redundant components are statistically independent to find system reliability's lower and upper bounds.
4.3 The reliability of SCS
To assess the multivariate polynomial reliability of SCS, one can utilize all minimal path sets that extend from a starting node to a destination node. This can be done by applying the Path Tracing Method (Gertsbakh and Shpungin 2011; Kuo and Zuo 2003; Todinov 2013). By using Equation (19) in conjunction with all minimal path sets, the reliability function of SCS can be obtained in the following form:
Consequently, the reliability of the system can be computed as:
The reliability of the SCS system with i.i.d. components (\({r}_{i}=r\)) can be calculated using Eq. (22) as follows:
4.4 Spross bound of SCS
In order to generate the disjoint sum form for the vector of minimal path sets in Equation (19) for the SCS system depicted in Fig. 3, one can utilize the Spross algorithm. The following steps should be taken:
-
If \({\varvec{i}}=1:\) \({P}_{1}={x}_{2}{x}_{6}\), then, \({A}_{\mathrm{0,1}}=\{{x}_{2}{x}_{6}\}\), As a result \({\alpha }_{1}={x}_{2}{x}_{6}\).
-
If \({\varvec{i}}=2:\) \({P}_{2}={x}_{2}{x}_{5}{x}_{7}\), then, \({A}_{\mathrm{0,2}}=\{{x}_{2}{x}_{5}{x}_{7}\}\). Since \({P}_{1}-{A}_{\mathrm{0,2}}=\{{x}_{6}\}\) as a result \({A}_{\mathrm{1,2}}=\{\overline{{x }_{6}}{P}_{2}\}\). Therefore \({\alpha }_{2}={x}_{2}{x}_{5}\overline{{x }_{6}}{x}_{7}\).
-
If \({\varvec{i}}=3:{P}_{3}={x}_{1}{x}_{3}{x}_{6}\), then, \({A}_{\mathrm{0,3}}=\left\{{x}_{1}{x}_{3}{x}_{6}\right\}.\) So \({P}_{1}-{A}_{\mathrm{0,3}}=\{{x}_{2}\}\) as a result\({A}_{\mathrm{1,3}}=\{\overline{{x }_{2}}{P}_{3}\}\). Therefore\({A}_{\mathrm{1,3}}={x}_{1}\overline{{x }_{2}}{x}_{3}{x}_{6}\), and \({P}_{2}-{A}_{\mathrm{1,3}}=\varnothing \). As a result,\({\alpha }_{3}={x}_{1}\overline{{x }_{2}}{x}_{3}{x}_{6}\).
-
If \({\varvec{i}}=4:{P}_{4}={x}_{1}{x}_{4}{x}_{7}\), then, \({A}_{\mathrm{0,4}}=\{{x}_{1}{x}_{4}{x}_{7}\}\) So \({P}_{1}-{A}_{\mathrm{0,4}}=\{{x}_{2}{x}_{6}\}\) by of above algorithm, we get \({A}_{\mathrm{1,4}}=\{{B}_{\mathrm{1,1}}={x}_{1}\overline{{x }_{2}}{x}_{4}{x}_{7}\), \({B}_{\mathrm{1,2}}={x}_{1}{x}_{2}{x}_{4}\overline{{x }_{6}}{x}_{7}\}\) then \({P}_{2}-{A}_{\mathrm{1,4}}\) lead \({P}_{2}-{B}_{\mathrm{1,1}}=\varnothing \) Then \({B}_{\mathrm{2,1}}={x}_{1}\overline{{x }_{2}}{x}_{4}{x}_{7}\) and \({P}_{2}-{B}_{\mathrm{1,2}}=\{{x}_{5}\}\) Hence \({B}_{\mathrm{2,2}}={x}_{1}{x}_{2}{x}_{4}\overline{{x }_{5}} \overline{{x }_{6}}{x}_{7}\). So\({A}_{\mathrm{2,4}}=\{{B}_{\mathrm{2,1}}={x}_{1}\overline{{x }_{2}}{x}_{4}{x}_{7},{B}_{\mathrm{2,2}}={x}_{1}{x}_{2}{x}_{4}\overline{{x }_{5}} \overline{{x }_{6}}{x}_{7}\}\). Also \({P}_{3}-{A}_{\mathrm{2,4}}\) lead\({P}_{3}-{B}_{\mathrm{2,1}}=\{{x}_{3}{x}_{6}\}\), as a result \({B}_{\mathrm{3,1}}={x}_{1}\overline{{x }_{2}} \overline{{x }_{3}}{x}_{4}{x}_{7}\) and \({B}_{\mathrm{3,2}}={x}_{1}\overline{{x }_{2}}{x}_{3}{x}_{4}\overline{{x }_{6}}{x}_{7}\) on other hand \({P}_{3}-{B}_{\mathrm{2,2}}=\varnothing \) so \({B}_{\mathrm{3,3}}={x}_{1}{x}_{2}{x}_{4}\overline{{x }_{5}} \overline{{x }_{6}}{x}_{7}\) then\({A}_{\mathrm{3,4}}=\{{B}_{\mathrm{3,1}}={x}_{1}\overline{{x }_{2}}\overline{{x }_{3}}{x}_{4}{x}_{7}\), \({B}_{\mathrm{3,2}}={x}_{1}\overline{{x }_{2}}{x}_{3}{x}_{4}\overline{{x }_{6}}{x}_{7},{B}_{\mathrm{3,3}}={x}_{1}{x}_{4}{x}_{7}{x}_{2}\overline{{x }_{6}}\overline{{x }_{5}}\}.\)
Hence
Based on the system's structure, if \(i=5\), the lower bound of system reliability cannot be achieved due to the accuracy measure \(d\left(g, h\right)=\mu \left(g\right)-\gamma \left(h\right)\) such that \(d\left(g, h\right)\le \epsilon \). If not, \(g\) and \(h\) must be increased (see (Beichelt and Sproß, 1989)). From Eq. (11) the reliability lower bound of the SCS system is given as
For i. i. d. reliability of components, Equation (24) becomes as follows:
In the same way, to obtain the disjoint sum form for the system in Fig. 3, use the Spross algorithm and the vector of all minimal cut sets in Eq. (20). Follow these steps:
-
If \({\varvec{i}}=1:\) \({C}_{1}=\overline{{x }_{6}} \overline{{x }_{7}}\), then, \({A}_{\mathrm{0,1}}=\{\overline{{x }_{6}} \overline{{x }_{7}}\}\), As a result \({\beta }_{1}=\overline{{x }_{6}} \overline{{x }_{7}}\).
-
If \({\varvec{i}}=2:\) \({C}_{2}=\overline{{x }_{4}} \overline{{x }_{5}} \overline{{x }_{6}}\), then, \({A}_{\mathrm{0,2}}=\{\overline{{x }_{4}} \overline{{x }_{5}} \overline{{x }_{6}}\}\). Since \({C}_{1}-{A}_{\mathrm{0,2}}=\{ \overline{{x }_{7}}\}\) as a result \({A}_{\mathrm{1,2}}=\{ {x}_{7}{C}_{2}\}\). Therefore \({\beta }_{2}=\overline{{x }_{4}} \overline{{x }_{5}} \overline{{x }_{6}} {x}_{7}\).
-
If \({\varvec{i}}=3:{C}_{3}=\overline{{x }_{2}} \overline{{x }_{3}} \overline{{x }_{5}} \overline{{x }_{7}}\), then, \({A}_{\mathrm{0,3}}=\left\{\overline{{x }_{2}} \overline{{x }_{3}} \overline{{x }_{5}} \overline{{x }_{7}}\right\},\) So \({C}_{1}-{A}_{\mathrm{0,3}}=\{\overline{{x }_{6}}\}\) as a result\({A}_{\mathrm{1,3}}=\{{x}_{6}{C}_{3}\}\). Therefore\({A}_{\mathrm{1,3}}=\overline{{x }_{2}} \overline{{x }_{3}} \overline{{x }_{5}} {x}_{6} \overline{{x }_{7}}\), and \({C}_{2}-{A}_{\mathrm{1,3}}=\varnothing \). As a result,\({\beta }_{3}=\overline{{x }_{2}} \overline{{x }_{3}} \overline{{x }_{5}} {x}_{6} \overline{{x }_{7}}\).
-
If\({\varvec{i}}=4:{C}_{4}=\overline{{x }_{2}} \overline{{x }_{3}} \overline{{x }_{4}}\), then, \({A}_{\mathrm{0,4}}=\left\{\overline{{x }_{2}} \overline{{x }_{3}} \overline{{x }_{4}}\right\}\) So \({C}_{1}-{A}_{\mathrm{0,4}}=\left\{\overline{{x }_{6}} \overline{{x }_{7}}\right\}\) by of above algorithm, we get\({A}_{\mathrm{1,4}}=\{{B}_{\mathrm{1,1}}=\overline{{x }_{2}} \overline{{x }_{3}} \overline{{x }_{4}} {x}_{6}\), \({B}_{\mathrm{1,2}}=\overline{{x }_{2}} \overline{{x }_{3}} \overline{{x }_{4}} \overline{{x }_{6}} {x}_{7}\}\) then \({C}_{2}-{A}_{\mathrm{1,4}}\) lead \({C}_{2}-{B}_{\mathrm{1,1}}=\varnothing \) Then \({B}_{\mathrm{2,1}}=\overline{{x }_{2}} \overline{{x }_{3}} \overline{{x }_{4}} {x}_{6}\) and \({C}_{2}-{B}_{\mathrm{1,2}}=\left\{\overline{{x }_{5}}\right\}\) Hence\({B}_{\mathrm{2,2}}=\overline{{x }_{2}} \overline{{x }_{3}} \overline{{x }_{4}} {x}_{5} \overline{{x }_{6}} {x}_{7}\). So.\({A}_{\mathrm{2,4}}=\left\{{B}_{\mathrm{2,1}}=\overline{{x }_{2}} \overline{{x }_{3}} \overline{{x }_{4}} {x}_{6},{B}_{\mathrm{2,2}}=\overline{{x }_{2}} \overline{{x }_{3}} \overline{{x }_{4}} {x}_{5} \overline{{x }_{6}} {x}_{7}\right\}\). Also \({C}_{3}-{A}_{\mathrm{2,4}}\) lead\({C}_{3}-{B}_{\mathrm{2,1}}=\left\{\overline{{x }_{5}} \overline{{x }_{7}}\right\}\), as a result \({B}_{\mathrm{3,1}}=\overline{{x }_{2}} \overline{{x }_{3}} \overline{{x }_{4}} {x}_{5} {x}_{6}\) and \({B}_{\mathrm{3,2}}=\overline{{x }_{2}} \overline{{x }_{3}} \overline{{x }_{4}} \overline{{x }_{5}} {x}_{6} {x}_{7}\) On other hand \({C}_{3}-{B}_{\mathrm{2,2}}=\varnothing \) so \({B}_{\mathrm{3,3}}=\overline{{x }_{2}} \overline{{x }_{3}} \overline{{x }_{4}} {x}_{5} \overline{{x }_{6}} {x}_{7}\) then \({A}_{\mathrm{3,4}}=\{{B}_{\mathrm{3,1}}=\overline{{x }_{2}} \overline{{x }_{3}} \overline{{x }_{4}} {x}_{5} {x}_{6}\) , \({B}_{\mathrm{3,2}}=\overline{{x }_{2}} \overline{{x }_{3}} \overline{{x }_{4}} \overline{{x }_{5}} {x}_{6} {x}_{7},{B}_{\mathrm{3,3}}=\overline{{x }_{2}} \overline{{x }_{3}} \overline{{x }_{4}} {x}_{5} \overline{{x }_{6}} {x}_{7}\}\)
Hence
The reliability upper bound of a system can be found using Eq. (12).
When the reliability of components is i.i.d., Equation (26) grows as follows:
The tabular representations of the numerical values of bounds can be seen further n Tables 1 and 2.
4.5 Esary-proschan bound of SCS
The minimal cut sets of Equation (20) are utilized to get the lower bound for the system shown in Fig. 3, Therefore, use Equation (13) to find
Therefore, assuming components have i.i.d. reliability, Equation (28) grows as follows:
To compute the reliability upper bound for the system, first take the minimal path sets of Eq. (19), and then by use Eq. (14) to obtain
Consequently, if Equation (30) have i.i.d. component reliability, then get
The data of the bounds are provided in Tables 1 and 2.
4.6 Edge-packing bound of SCS
In order to establish the reliability lower bound of the SCS system, as displayed in Fig. 3, the disjoint minimal path sets can be employed, identified in Eq. (19). It follows that the sets of disjoint minimal paths are \({DP}_{1}=\{{x}_{2}{x}_{6}\}\) and \({DP}_{2}=\{{x}_{1}{x}_{4}{x}_{7}\}\). Then use Eq. (15) to obtain
Consequently, if equation (32) has i.i.d. component reliability, it must be as follows:
Also, to determine the upper bound for the system, we must first identify the disjoint edge minimal cut sets of Eq. (20). Therefore, the disjoint edge minimal cut sets are \(D{C}_{1}=\left\{\overline{{\mathrm{x} }_{6}} \overline{{\mathrm{x} }_{7}}\right\}\) and \(D{C}_{2}=\left\{\overline{{\mathrm{x} }_{1}} \overline{{\mathrm{x} }_{2}}\right\}\), then use Eq. (14) to derive the upper bound.
Therefore, if equation (34) has i.i.d. component reliability, then it can be expressed as follows:
Tables 1 and 2 list the exact values used for the bounds.
4.7 Linear and quadratic bound of SCS
In order to determine the lower bound for the system shown in Fig. 3, it is essential to insert the minimal cut sets derived from Equation (20) into Equation (17) as follows:
Representing \({R}_{LB}\) can be achieved by simplifying Eq. (36) for \(Pr\left(\overline{{x }_{i}}\right)=1-{r}_{i}, \forall \overline{{x }_{i}}\in {C}_{i}\) and assuming that the component reliability is i.i.d. This representation follows:
The upper bound for the system can be computed by taking the minimal path sets from Equation (19) and putting them into Equation (18).
Express \({R}_{UB}\) by simplifying Eq. (38) for \(Pr\left({x}_{i}\right)=1-{r}_{i} , \forall {x}_{i}\in {P}_{i}\) and assuming the component reliability is i.i.d. Then
The exact values used for the bounds are shown in Tables 1 and 2.
5 Result and discussion
The computation reliability of a complex system in the binary case is an NP-hard problem; thus, effective analysis techniques and well-implemented solutions are crucial for practical use. Comparing the four models, Sb, EPb, EDb and LQb, can be challenging due to their differing network structures. Section 4 presents the results achieved for the SCS network. The analysis was conducted from two perspectives computational measures and result quality. Fig. 3 displays these effects. This analysis aims to explain and demonstrate when bound-based approaches are a better choice than analytical approximation formulas. On the theoretical and computational front, some of the applicable properties can be identified:
-
The Sb technique gives a helpful approach to estimating the upper and lower reliability constraints, as in Fig. 7. However, this estimation requires more computational effort as the number of system components increases.
-
The EPb method is advantageous as it offers highly accurate reliability function importance established on the selected components, as shown in Fig. 7. It is a simple mathematical process that relies on minimal cut sets and paths.
-
Based on the selected components, the EDb method offers the most minimal values for the reliability function, as depicted in Fig. 6. However, it cannot be used for systems that do not have disjoint sets.
-
The LQb method is efficient for estimating the lower bound reliability of a system. However, it may not be accurate for estimating the reliability upper bound of the system, as indicated in Fig. 6.
In order to evaluate the significance of the suggested technique in estimating network reliability, small-scale test networks (as illustrated in Fig. 3) were utilized; in this network, all edges are considered undirected, and their reliability gradually increases from 0.7 to 0.95. To determine the network's reliability, we implemented the four approaches described in Sect. 2 to calculate the lower and upper bounds. To prove the effectiveness of the suggested approach, Table 1–2 and Fig. 6–7, four different methods were used to obtain lower and upper bounds, and a comparison of these bounds is presented, along with the Exact reliability. In Table 1, the proposed LQb approach consistently shows a lower bound than the Sb, EPb, and EDb methods for all network components. This approach provides a more accurate estimation of the exact reliability. However, it does not improve network performance.
On the other hand, the EDb approach produces the lowest reliability function values based on selected components. Table 2 shows that the proposed EPb approach consistently yields a higher upper bound than the LQb, EPb, and EDb methods for all network components. This approach gives the best possible reliability function values based on selected components. The EDb approach provides a more accurate estimation of the exact reliability, but the network's performance needs to improve.
6 Conclusions
The exact methods for calculating system reliability in polynomial time are restricted to elementary systems, such as series and parallel-connected systems. This study examines the primary techniques for utilizing minimal paths and cuts to determine the reliability bounds of the system. These bounds are evaluated qualitatively and contrasted quantitatively by numerically analyzing example systems. The matrix-based method is offered to simplify the analysis of safety–critical systems with seven components. This approach helps to calculate the system's minimal path and minimal cuts (see Fig. 6 and Fig. 7). The lower and upper-reliability bounds discussed in this study assist the relationship of information on the reliability of systems that are more complex than those tractable with exact methods because it takes only polynomial time to calculate reliability bounds using the provided minimal paths and cuts. Tables 1 and 2 show the results of our numerical comparison of the bounds obtained using the extended SCS structure (Fig. 3). Also, select the optimal approach according to theoretical generalizations addressing the bounds, which hold across the range for component reliability (see Table 1–2).
Abbreviations
- Sb:
-
Spross bound
- EPb:
-
Esary-proschan bound
- EDb:
-
Edge-packing bound
- LQb:
-
Linear and quadratic bound
- SCS:
-
Safety–critical system
- i. i. d.:
-
Independent and identically distributed
- \({x}_{i}\) :
-
A system component
- \(\overline{{x }_{i}}\) :
-
The complement of component \({x}_{i}\) such that \(\overline{{x }_{i}}=1-{x}_{i}\)
- \(Pr({x}_{i})\) :
-
The Probability of component \({x}_{i}\) such that \(Pr\left({x}_{i}\right)={r}_{i}\)
- \({r}_{i}\) :
-
The reliability of component \({x}_{i}\)
- \({q}_{i}\) :
-
The unreliability of component \({x}_{i}\)
- \({\varvec{X}}\) :
-
The vector of all component \({x}_{i}\) of the system
- \({\varvec{P}}\) :
-
The vector of all minimal path \({P}_{i}\) of the system
- \({\varvec{D}}{\varvec{P}}\) :
-
The vector of all disjoint minimal path \(D{P}_{i}\) of the system
- \({\varvec{C}}\) :
-
The vector of all minimal cut \({C}_{i}\) of the system
- \({\varvec{D}}{\varvec{C}}\) :
-
The vector of all disjoint minimal cut \(D{C}_{i}\) of the system
- \(IM\) :
-
Incidence matrix of the system
- \(CM\) :
-
Minimal cut matrix of the system
- \({R}_{Exact}\) :
-
The exact reliability of the system
- \({Q}_{Exact}\) :
-
The exact unreliability of the system
- \({R}_{LB}\) :
-
The reliability lower bound of the system
- \({R}_{UB}\) :
-
The reliability upper bound of the system
- \({B}_{j,r}\) :
-
The Boolean product of \({x}_{i}\) and \(\overline{{x }_{i}}\) for some \({P}_{i}\) or \({C}_{i}\)
- \({A}_{j,i}\) :
-
Sets {\({B}_{j,r}\)} of disjoint products derived from \({P}_{i}\) or \({C}_{i}\)
- \({\alpha }_{i}\) :
-
Portion that are obtained successively from
- \({A}_{j,i}\) :
-
For minimal path \({P}_{i}\)
- \({\beta }_{j}\) :
-
Portion that are obtained successively from
- \({A}_{j,i}\) :
-
For minimal cut \({C}_{j}\)
- \(\mu \left(g\right)\) :
-
A specified lower bound for a spross bound method
- \(\gamma \left(h\right)\) :
-
A specified upper bound for a spross bound method
References
Aggarwal K (1993) Reliability engineering (Vol 3). Springer Science and Business Media
Babaei M, Rashidi-baqhi A (2022) Universal generating function-based narrow reliability bounds to evaluate reliability of project completion time. Reliab Eng Syst Saf 218:108121
Beichelt F, Sproß L (1989) Bounds on the reliability of binary coherent systems. IEEE Trans Reliab 38(4):425–427
Beichelt F (2012) Reliability and maintenance: networks and systems. Chapman and Hall/CRC
Colbourn CJ (1988) Edge-packings of graphs and network reliability. In: Annals of Discrete Mathematics 38 pp 49–61, Elsevier
Datta E, Goyal N (2023) An efficient sum of disjoint product method for reliability evaluation of stochastic flow networks using d-MPs. Int J Syst Assur Eng Manage pp 1–19
Datta E, Goyal NK (2017) Sum of disjoint product approach for reliability evaluation of stochastic flow networks. Int J Syst Assur Eng Manage 8:1734–1749
Esary JD, Proschan F (1963) Coherent structures of non-identical components. Technometrics 5(2):191–209
Gertsbakh I, Shpungin Y (2011) Network reliability and resilience. Springer Science and Business Media
Hassan ZAH, Mutar EK (2017b) Geometry of reliability models of electrical system used inside spacecraft. 2017b Second Al-Sadiq International Conference on Multidisciplinary in IT and Communication Science and Applications (AIC-MITCSA)
Hassan ZA, Mutar EK (2017a) Evaluation the reliability of a high-pressure oxygen supply system for a spacecraft by using GPD method. Al-Mustansiriyah J Coll Educ 2(2):993–1004
Hassan ZAH, Udriște C (2015) Equivalent reliability polynomials modeling EAS and their geometries. Ann West Univ Timisoara-Math Comput Sci 53(1):177–195
Horváth Á (2013) The cxnet complex network analyser software. Acta Polytech Hungarica 10(6):43–58
Jin T, Coit DW (2003) Approximating network reliability estimates using linear and quadratic unreliability of minimal cuts. Reliab Eng Syst Saf 82(1):41–48
Jula N, Costin C (2012) Methods for analyzing the reliability of electrical systems used inside aircrafts. In: Recent Advances in Aircraft Technology. IntechOpen
Kaushik B, Banka H (2015) Performance evaluation of approximated artificial neural network (AANN) algorithm for reliability improvement. Appl Soft Comput 26:303–314
Kuo W, Zuo MJ (2003) Optimal reliability modeling: principles and applications. John Wiley and Sons
Malik S, Chauhan S, Ahlawat N (2020) Reliability analysis of a non series–parallel system of seven components with Weibull failure laws. Int J Syst Assur Eng Manage 11(3):577–582
Marichal J-L (2016) Structure functions and minimal path sets. IEEE Trans Reliab 65(2):763–768
Mi J, Li Y-F, Peng W, Huang H-Z (2018) Reliability analysis of complex multi-state system with common cause failure based on evidential networks. Reliab Eng Syst Saf 174:71–81
Mutar EK (2020) Matrix-based minimal cut method and applications to system reliability. Adv Sci Technol Eng Syst J 5(5):991–996
Mutar EK, Hassan Z (2017) On the geometry of the reliability polynomials. University of Babylon
Mutar EK, Hassan ZAH (2022) New properties of the equivalent reliability polynomial through the geometric representation. In: 2022 International Conference on Electrical, Computer and Energy Technologies (ICECET)
Mutar EK (2022a) Analytical method of calculating reliability sensitivity for space capsule life support systems. Math Probl Eng 2022a
Mutar EK (2022b) Path tracing method to evaluate the signature reliability function of a complex system. J Aerosp Technol Manage 14
Mutar EK (2022c) Reliability analysis of complex safety-critical system with exponential decay failure laws the 6th international conference on SRS
Mutar EK (2022d) Signature of electrical system reliability used inside aircraft IEEE 27th pacific rim international symposium on dependable computing (PRDC)
Pyzdek T, Keller PA (2003) Quality engineering handbook. CRC Press
Rai S, Veeraraghavan M, Trivedi KS (1995) A survey of efficient reliability computation using disjoint products approach. Networks 25(3):147–163
Rausand M (2014) Reliability of safety-critical systems: theory and applications. John Wiley and Sons
Rodionov A, Rodionova O (2013) Exact bounds for average pairwise network reliability. In: Proceedings of the 7th International Conference on Ubiquitous Information Management and Communication
Romero P (2021) Universal reliability bounds for sparse networks. IEEE Trans Reliab 71(1):359–369
Sebastio S, Trivedi KS, Wang D, Yin X (2014) Fast computation of bounds for two-terminal network reliability. Eur J Oper Res 238(3):810–823
Sharma M (2014) Reliability analysis of a non-series parallel network in fuzzy and possibility context. Int J Educ Sci Res Rev 1(2):40–46
Soh S, Rai S (1993) Experimental results on preprocessing of path/cut terms in sim of disjoint products technique. IEEE Trans Reliab 42(1):24–33
Todinov MT (2013) Flow networks: analysis and optimization of repairable flow networks, networks with disturbed flows, static flow networks and reliability networks. Newnes
Wang Z, Zhang J, Huang T (2021) Determining delay bounds for a chain of virtual network functions using network calculus. IEEE Commun Lett 25(8):2550–2553
Xiao Z, Xu X, Xing H, Luo S, Dai P, Zhan D (2021) RTFN: a robust temporal feature network for time series classification. Inf Sci 571:65–86
Xiao Z, Zhang H, Tong H, Xu X (2022) An efficient temporal network with dual self-distillation for electroencephalography signal classification. In: 2022 IEEE International Conference on Bioinformatics and Biomedicine (BIBM)
Xing H, Xiao Z, Zhan D, Luo S, Dai P, Li K (2022) SelfMatch: robust semisupervised time-series classification with self-distillation. Int J Intell Syst 37(11):8583–8610
Yang DY, Frangopol DM (2020) Life-cycle management of deteriorating bridge networks with network-level risk bounds and system reliability analysis. Struct Saf 83:101911
Zhu H, Zhang C (2019) Expanding a complex networked system for enhancing its reliability evaluated by a new efficient approach. Reliab Eng Syst Saf 188:205–220
Funding
No funding is required for the completion of this study.
Author information
Authors and Affiliations
Corresponding author
Ethics declarations
Conflict of interest
There are no conflicts of interest present that would affect the publication of this manuscript.
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
Springer Nature or its licensor (e.g. a society or other partner) holds exclusive rights to this article under a publishing agreement with the author(s) or other rightsholder(s); author self-archiving of the accepted manuscript version of this article is solely governed by the terms of such publishing agreement and applicable law.
About this article
Cite this article
Mutar, E.K. Estimating the reliability of complex systems using various bounds methods. Int J Syst Assur Eng Manag 14, 2546–2558 (2023). https://doi.org/10.1007/s13198-023-02108-7
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s13198-023-02108-7