Abstract
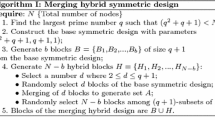
As typical wireless sensor networks (WSNs) have resource limitations, predistribution of secret keys is possibly the most practical approach for secure network communications. In this paper, we propose a key management scheme based on random key predistribution for heterogeneous wireless sensor networks (HSNs). As large-scale homogeneous networks suffer from high costs of communication, computation, and storage requirements, the HSNs are preferred because they provide better performance and security solutions for scalable applications in dynamic environments. We consider hierarchical HSN consisting of a small number high-end sensors and a large number of low-end sensors. To address storage overhead problem in the constraint sensor nodes, we incorporate a key generation process, where instead of generating a large pool of random keys, a key pool is represented by a small number of generation keys. For a given generation key and a publicly known seed value, a keyed-hash function generates a key chain; these key chains collectively make a key pool. As dynamic network topology is native to WSNs, the proposed scheme allows dynamic addition and removal of nodes. This paper also reports the implementation and the performance of the proposed scheme on Crossbow’s MicaZ motes running TinyOS. The results indicate that the proposed scheme can be applied efficiently in resource-constrained sensor networks. We evaluate the computation and storage costs of two keyed-hash algorithms for key chain generation, HMAC-SHA1 and HMAC-MD5.
Article PDF
Similar content being viewed by others
Avoid common mistakes on your manuscript.
References
Blom R (1982) Non-public key distribution. In: Advances in cryptology—CRYPTO 82, pp 231–236
Blundo C, De Santis A, Herzberg A, Kutten S, Vaccaro U, Yung M (1993) Perfectly-secure key distribution for dynamic conferences. In: CRYPTO ’92: proceedings of the 12th annual international cryptology conference on advances in cryptology, London, UK, 1993. Springer, New York, pp 471–486. ISBN 3-540-57340-2
Bulusu V, Durresi A, Paruchuri V, Durresi M, Jain R (2006) Key distribution in mobile heterogeneous sensor networks. In: Global telecommunications conference, 2006. GLOBECOM ’06. IEEE, New York, pp 1–5. ISBN 1-4244-0356-1
Chan H, Perrig A (2005) Pike: peer intermediaries for key establishment in sensor networks. In: INFOCOM 2005. 24th annual joint conference of the IEEE computer and communications societies, pp 524–535. ISBN 0-7803-8968-9
Chan H, Perrig A, Song D (2003) Random key pre-distribution schemes for sensor networks. In: IEEE symposium on security and privacy, May 2003, pp 197–213
Chan H, Perrig A, Song D (2003) Random key pre-distribution schemes for sensor networks. In: IEEE symposium on research in security and privacy, 2003
Cheng P, Glenn R (1997) Test cases for HMAC-MD5 and HMAC-SHA-1. In: RFC 2202, 1997
Cheng Y, Agrawal DP (2005) Efficient pairwise key establishment and management in static wireless sensor networks. In: Second IEEE international conference on mobile ad hoc and sensor systems, 2005
Di Pietro R, Mancini LV, Mei A (2003) Random key assignment secure wireless sensor networks. In: 1st ACM workshop on security of ad hoc and sensor networks, 2003
Du X, Lin F (2005) Maintaining differentiated coverage in heterogeneous sensor networks. EURASIP J Wirel Commun Netw (4):565–572
Du X, Xiao Y (2006) Energy efficient chessboard clustering and routing in heterogeneous sensor network. Int J Wirel Mobile Comput 1(2):121–130
Du X, Xiao Y, Guizani M, Chen H-H (2007) An effective key management scheme for heterogeneous sensor networks. Ad Hoc Netw 5(1):24–34
Duarte-Melo EJ, Liu M (2002) Analysis of energy consumption and lifetime of heterogeneous wireless sensor networks. In: Proceedings of IEEE GLOBECOM, 2002
Eschenauer L, Gligor VD (2002) A key management scheme for distributed sensor networks. In: ACM CCS, 2002
Gay D, Levis P, von Behren R, Welsh M, Brewer E, Culler D (2003) The nesc language: a holistic approach to networked embedded systems. SIGPLAN Not 38(5):1–11. ISSN 0362-1340. doi:http://doi.acm.org/10.1145/780822.781133
Girod L, Stathopoulos T, Ramanathan N, Elson J, Estrin D, Osterweil E, Schoellhammer T (2004) A system for simulation, emulation, and deployment of heterogeneous sensor networks. In: 2nd international conference on embedded networked sensor systems, 2004
Goldreich O (2000) Foundations of cryptography: basic tools. Cambridge University Press, New York. ISBN 0521791723
Heinzelman WR, Chandrakasan A, Balakrishnan H (2000) Energy-efficient communication protocol for wireless microsensor networks. In: IEEE Hawaii int conf on system sciences, pp 4–7
Karlof C, Sastry N, Wagner D (2004) Tinysec: a link layer security architecture for wireless sensor networks. In: SenSys ’04: proceedings of the 2nd international conference on embedded networked sensor systems. ACM Press, New York, pp 162–175. ISBN 1-58113-879-2. doi:http://doi.acm.org/10.1145/1031495.1031515
Lazos L, Poovendran R (2006) Stochastic coverage in heterogeneous sensor networks. ACM Trans Sensor Netw (TOSN) 2(3):325–358
Liu D, Ning P (2003) Location-based pairwise key establishments for static sensor networks. In: SASN ’03: proceedings of the 1st ACM workshop on security of ad hoc and sensor networks. ACM, Press, New York, pp 72–82. ISBN 1-58113-783-4. doi:http://doi.acm.org/10.1145/986858.986869
Liu D, Ning P, Li R (2005) Establishing pairwise keys in distributed sensor networks. ACM Trans Inf Syst Secur 8(1):41–77. ISSN 1094-9224. doi:http://doi.acm.org/10.1145/1053283.1053287
Lu K, Qian Y, Hu J (2006) A framework for distributed key management schemes in heterogeneous wireless sensor networks. In: IEEE international performance computing and communications conference, pp 513–519
Ma Y, Dalal S, Alwan M, Aylor J (2003) Rop: a resource oriented protocol for heterogeneous sensor networks. In: Virginia tech symposium on wireless personal communications, 2003
Menezes AJ, van Oorschot PC, Vanstone SA (1996) Handbook of applied cryptography. CRC Press, New York. ISBN 08493-8523-7
Oliveira LB, Wong HC, Bern M, Dahab R, Loureiro AAF (2006) Sec leach: a random key distribution solution for securing clustered sensor networks. In: 5th IEEE international symposium on network computing and applications, pp 145–154
Perrig A, Szewczyk R, Tygar JD, Victorwen, Culler DE (2001) Spins: security protocols for sensor networks. In: Seventh annual int’l conf on mobile computing and networks, July 2001
Ren K, Zeng K, Lou W (2006) A new approach for random key predistribution in large-scale wireless sensor networks. Wirel Commun Mobile Comput 6(3):307–318
Traynor P, Kumar R, Bin Saad H, Cao G, La Porta T (2006) Establishing pair-wise keys in heterogeneous sensor networks. In: INFOCOM 2006. 25th IEEE international conference on computer communications. Proceedings, pp 1–12. ISBN 1-4244-0221-2
Traynor P, Kumar R, Bin Saad H, Cao G, La Porta T (2007) Efficient hybrid security mechanisms for heterogeneous sensor networks. IEEE Trans Mobile Comput 6(6):663–677. ISSN 1536-1233
Wadaa A, Olariu S, Wilson L, Eltoweissy M (2004) Scalable cryptographic key management in wireless sensor networks. In: Proceedings of the 24th international conference on distributed computing systems workshops—W7: EC (ICDCSW’04), Washington, DC, USA. IEEE Computer Society, Silver Spring, pp 796–802. ISBN 0-7695-2087-1
Woo A, Culler DE (2001) A transmission control scheme for media access in sensor networks. In: MobiCom ’01: proceedings of the 7th annual international conference on mobile computing and networking. ACM Press, New York, pp 221–235. ISBN 1-58113-422-3. doi:http://doi.acm.org/10.1145/381677.381699
Zhu S, Xu S, Setia S, Jajodia S (2003) Establishing pairwise keys for secure communication in ad hoc networks: a probabilistic approach. In: 11th IEEE international conference on network protocols (ICNP’03)
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Kausar, F., Hussain, S., Yang, L.T. et al. Scalable and efficient key management for heterogeneous sensor networks. J Supercomput 45, 44–65 (2008). https://doi.org/10.1007/s11227-008-0184-2
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11227-008-0184-2