Abstract
In this paper, we present a new design of cryptosystem characterized by an optimized substitution box (S-box) and random permutation. Our proposed S-box is generated using a modified genetic algorithm. The crossover process is performed with sophisticated research using the best previous population. We use randomness and ergodicity of the logistic map to add complexity and robustness to our proposed method. Many tests proving the nonlinearity of our S-box have been carried out to demonstrate the efficiency of our algorithm. In the second part, we offer a new permutation algorithm based on a chaotic sequence generated from the logistic map. To show the performance of our proposition, we compare our results with previous algorithms. The results of its statistical analysis, like entropy value and correlation between adjacent pixels, show that the proposed image encryption scheme provides security for image encryption. The time speed of the proposed algorithm confirms the possibility of real-time implementation.
Similar content being viewed by others
Explore related subjects
Discover the latest articles, news and stories from top researchers in related subjects.Avoid common mistakes on your manuscript.
1 Introduction
1.1 Research background
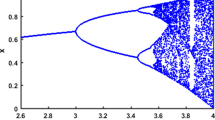
In the last decade, new technologies have known considerable development and thus, have had a significant impact on society. Technology has changed the communication world. Different means of communication have been developed, such as facebook, twitter, Instagram...These social media have facilitated communication and the share of information at high speed. One can say that technology and communication are interdependent. In this way, the more communication is established, the more we care about creating new solutions to privacy threats. Secure communication is essential to protect one’s privacy. In general, two entities need to communicate without an interception and in a safe way. Several methods were used to ensure the security and confidentiality of transmitted information through the internet. Encryption is one of the essential measures to provide security. It is true that it is a crucial tool but it cannot provide a high level of protection on its own. Security researchers are thus busy developing new technologies and fixing out the flaws in existing ones. In this context, the chaotic system properties such as randomness, sensitivity to the initial condition, and ergodicity give promising results in building robust cryptosystems.
1.2 Review of the previous chaotic cryptosystems
Due to the importance of images and video transmission in our life, many encryption algorithms have been proposed, we can classify these algorithms in two classes. The first one includes those classical encryption schemes like RSA, AES, DES... [8, 32], while the second one contains algorithms exploiting the chaotic properties of nonlinear functions [6, 7, 37]. These maps have been used in the masking and confusion/diffusion steps. The most important point of this category is the exploitation of the ergodicity and randomness proprieties of chaotic functions. Indeed, many recent studies have focused on demonstrating the randomness effect of chaotic functions (NIST test) [23]. Currently, the challenge in encryption scheme is to find a secure algorithm with an excellent complexity performance. The last encryption schemes proposed in the previous few years were based on the twin study of performance/complexity in order to demonstrate the possibility of using chaotic functions in secured networks and web services. The techniques that we have used to demonstrate the robustness and complexity of the algorithms can be classified as follows: firstly, we should use an excellent dataset to generalize the use of our solution. Secondly, we study the histogram behavior of encrypted images to demonstrate the unpredictability process with statistical study like entropy values and correlation between two adjacent pixels. Finally, a speed study and a complexity discussion were conducted to evaluate the real-time implementation.
Most of the chaotic encryption schemes are based on confusion/diffusion Shannon properties [39, 40]. Recently, many algorithms used S-box (Substitution-box) to enhance the confusion phase [15, 25]. The advantages of using this technique are the simple implementation and incorporation in the cryptosystem and the nonlinearity effect on the encryption algorithms. AES and DES algorithms were the first to use S-boxes. Eventhough S-boxes have contributed to strengthening these algorithms, their major inconvenience remains their statistic behaviors. In our solution, we used chaotic systems to draw S-boxes in order to produce dynamicity. Jakimoski and Kocarev used tow chaotic logistic maps [18]: exponential and logistic. They demonstrated that both can be implemented in various processors and be robust to several attacks. In [33], they proposed a solution using 2D chaotic map to obtain random and bijective S-boxes. Among the advantages of this method are low complexity, obvious parametrization, and large key space. Chen et al. [12] improved this method by using Backer map. Fatih et al. [30] proposed S-boxes using chaotic Lorenz system as a source of randomness. Authors in [26] proposed S-boxes based on complex chaotic system and random noise. Three S-Boxes are generated by a complex Chen system, and each S-box is used to encrypt one of the color components.
Now, researchers utilize meta-heuristic algorithms in different software applications such as image processing, cloud computing, big data and encryption mask phase. They use the following optimization techniques: the so-called PSO (Particle Swarm Optimization) or ACO (Ant Colony Optimization) [4, 5, 16, 20, 21, 27, 28].
In our previous work presented in [9], we proposed novel S-boxes based on crossover and mutation; we generated seven S-boxes with acceptable nonlinearity parameter. We have profited from the chaotic Properties and genetic algorithms. Development of the algorithm steps showed some weaknesses due to the randomness caused by the chaotic function. This resulted in a weak solution domain.
In the last five years, many researchers tried to include natural phenomena in the encryption algorithms to add more unpredictability in the confusion phase. Tests of these attempts have given encouraging results. For example, in [17], authors use DNA concept in the encryption algorithm and they generate a mask using 1D and 2D chaotic maps to obtain ciphered image. In [10], we used DNA sequences and hash algorithm to conceptualize a new cryptosystem. In [11], we proposed a new cryptosystem based on hash function key generator, in order to increase the robustness of our cryptosystem. Now, the main objective of security researches is to find a robust symmetric chaotic encryption algorithm for specific applications. The challenge is to demonstrate that chaotic encryption can be applied for real-time communication. For example, the author in [24] proposed a chaotic dynamic key cryptosystem based on a neural network so as to secure wireless communication. Another solution was proposed in [31]. Authors used a chaotic encryption algorithm to secure medical images. Authors in [13] proposed an application of chaotic cryptosystem in IoT E-healthcare. They used a 2D chaotic function to generate pseudo-random numbers used as keys of their scheme. Therefore, any proposed encryption algorithm must meet the robustness and speed criteria, so that it could be applied in several applications.
1.3 Our contribution
In this paper, we present a new design of a chaotic S-box based on modified genetic algorithm techniques. The selection of population is a fundamental part to optimize the algorithm. So, we develop a new intelligent crossover that explores individuals found in our work [9]. We also divided the research domain into sub-regions to facilitate population construction. The enhanced algorithm selects individuals according to the quality of the last operation in our algoriyhm in order to find the best population. The second originality of our work lies in creating an interdependency between the input image and the round number utilized by the encryption algorithm. This relation enhances security and gives more unpredictability to the proposed algorithm. In our work, we present an algorithm based on a chaotic sequence generated by the logistic map. This sequence allows us to change the order of sub-blocks randomly and add more security to the encryption algorithm. The results of statistical analysis and security analysis show that the proposed image encryption scheme guarantees efficiency and robustness for image encryption.
1.4 Structure of the paper
The remainder of the paper is organized as follows. In section 2, we proposed a new method to draw an S-box using intelligent crossover and the best exploitation of the chaotic range function; a statistical test was elaborated and showed thealgorithm’s performances. In section 3 we developed a new cryptosystem based on Shannon confusion/diffusion properties. In section 4, we carried out statistical tests and security analysis to demonstrate the robustness and the efficiency of the proposed encryption algorithm. Finally, a conclusion is presented in section 5.
2 The proposed S-boxes approach
An S-box (Substitution box) is used in an encryption algorithm to satisfy the Shannon confusion property. To evaluate an S-box, we determine the nonlinearity parameter (Eq. (1)), which measures the degree of confusion. Generally, this parameter contributes to the robustness of the encryption algorithm (An important step when we propose a secure cryptosystem). So, it’s taken as an objective function in our optimization algorithm.
The nonlinearity criteria are defined by
Mathematically, the nonlinearity of a Boolean function f(x) can be represented by the Walsh Spectrum.
The Walsh Spectrum of f(x) is given by
and
To generate a highly nonlinear S-box, we studied the steps of the algorithm proposed in [9], and we make improvements after revealing some weaknesses. The main weakness in the algorithm is that all the process depends on the initial S-box (Step 1) (Fig. 1) If the initial S-box does not show excellent properties, neither will the final one. To overcome this weakness, we propose to generatea dynamic initial S-box (Fig. 2). Each time we obtain weak results, we regenerate another one until we get an S-box with excellent cryptographic properties. Analyzing the mentioned algorithm, we remark that the initial S-box depends heavily on the initial value of x0. On the other hand, we enhance the construction of population size of the optimization algorithm to explore all the research domain of the solution. We start by dividing the range of chaotic map initial conditions; this segmentation is essential and allowsthe excellent exploration of the solution domain (Table 1).
Thereby, our contribution is summarized as follows:
-
1.
Segmentation of the initial condition range
-
2.
Generate a pseudo-random sequence of initial values using the first range n0
-
3.
Generate the first initial S-Box using the initial value taken from the chaotic generator.
-
4.
Mutation process.
-
5.
Intelligent crossover of S-box elements: The selection of population is according to the last objective values.
-
6.
If nonlinearity of the obtained S-Box is less than 107.5, regenerate another initial S-box by using another value of the initial condition.
-
7.
Stop condition: Nonlinearity >107.5
The proposed algorithm is performed in three steps and presented briefly in the following flowchart (Fig. 3).
2.1 Description
Step 1 (Generating the initial dynamic S-box)
The selection of an initial S-box is an essential step in our algorithm, and it’s the step that leads us to an excellent S-box with better performances. In our proposal, we choose to modify the initial S-box to maximize the exploration of the solution domain. In the flowing, we explain the necessary steps to determine an initial S-box.
-
1.
Define S as a sequence, which is empty at the beginning.
-
2.
Given the initial value x0, iterate Eq. (4) for 100 times to get rid of the transient effect.
-
3.
Continue to iterate, one time, the Eq. (4), and denote the current state value as x′. Then an integer value X is obtained as below:
where floor(X) rounds the elements of X to the nearest integers towards minus infinity.
-
4.
If X is not in sequence S, append it to S. Otherwise, go to item 3.
-
5.
If the number of elements in S is not bigger than 256, go to item 3. Otherwise, output S.
-
6.
Construct the initial (8 × 8) S-box from the sequence S using the algorithm 1. This S-box is used as the initial population.
-
7.
After K iterations, if the final condition is not satisfied, take another value ∈ ni as initial condition and repeat previous steps to determine another initial S-box (Fig. 3) (Alg. 2, Alg. 3)
Algorithm 1 Optimization Process.

Algorithm 2 Gen_init_S Box(x0).

Step 2 (Generating the control parameters of mutation and crossover)
The logistic map system defined in Eq. (4) is used to generate the control parameters of the genetic algorithm. This step is presented briefly.
Algorithm 3 S2Sbox(S).

-
1.
Given the initial values x0, iterate Eq. (4) for 100 times to get rid of the transient effect.
-
2.
Iterate it 16 × 3 times to generate three sequences, S1i = xi, S2i = yi and S3i = zi, i = 1, 2, …, 16. The flowing table explain the exploitation process of the genetic algorithm in order to generate the S-box.
Step 3 (Intelligent crossover)
The intelligent crossover part of the algorithm is described in Fig. 4. If the output of the algorithm is ∈ [Nf1,Nf2], we change the initial condition slightly to find the best one, and else we repeat all the process. In our simulation we choose Nf1 = 105.5 and Nf2 = 107.
Finaly, to select the best S-box solution to the problem, we adopt the following points:
-
1.
Determining the nonlinearity of the first S-box calculated
-
2.
Applying the crossover/mutation process (Fig. 4): Intelligent crossover
-
3.
Calculating the new nonlinearity score
-
4.
Evaluating the nonlinearty value
-
5.
Taking a decision
-
6.
Repeating previous steps with new initial S-box if condition is not satisfied
-
7.
Evaluating the final solution
2.2 S-box evaluation
We take the simulation parameters when we execute our algorithm:
-
x0 = 0.17888888888887; μ = 3.57777777777777;
-
D is number of sub-regions = 12;
-
Population number for each sub-region = 50;
-
Nf1=105; Nf2=107;
The Tables 2 and 3 represent the proposed S-Box. we remark these points:
-
1.
The bijective propriety is verified
-
2.
The nonlinearity score of the optimized S-box (Nonlinearity = 108) is better than those proposed in previous work (Including our recent proposition in [9])
-
3.
The mean value of the S-box dependence matrix (SAC), and we founded as average value 0.4988
-
4.
The output bits independence criterion (BIC) means that all the avalanche variables must be pair-wise independent, in our case BIC − SAC = 0.4969 and BIC − nonlinearity = 102.8571.
-
5.
The maximum input/output Xor is 12
3 The proposed cryptosystem
The process of encryption is presented in the following steps (Fig. 6):
-
Step 1. Inputting the original image P(S,M), S and M represent the dimension of row and column respectively.
-
Step 2. Using the proposed SBox, we start the substitution phase, after that we divide the matrix into 4*4 blocks
-
Step 3. We itirate N times the logistic map and we construct a vector according to
-
Step 4. We permuted the blocks, this operation is made randomly according to the final vector presented in step 3. We repeated this operation N times. In our case we took N = 10,000. Algorithm 2 described the permutation process, we started by iterating logistic map N times, after that we completed the matrix permutation (Matrixp)by the following instruction. We present in (Fig. 5) an example to explain the operation:
-
Step 5. In this step we used Xor operation between the permuted Matrix and chaotic sequence generated from logistic map. Finally, we obtain the encrypted image (first round).
-
Step 6. By updating the key of the algorithm according to the folowing equation, we repeat all steps described (Fig. 6).
Algorithm 4 Permutation Process

The number of the rounds in our proposed algorithm is defined by
We notice a relation between the algorithm output in the first encryption round and the number of rounds executed. This operation enhances the security of the proposed encryption scheme by increasing the possibility of encryption rounds (the maximum value is 8). We have chosen eight encryption rounds as maximum value to keep an acceptable algorithm speed.
4 Simulation results
In our simulation, we used the optimized S-box detailed in section 2 and these simulations parameters:
-
1.
For permutation vector: x0 = 0.278888888888879; μ = 3.67777777777779;
-
2.
For mask vector(xor): x0 = 0.37888888888887; μ = 3.77777777777779;
In the case of the IEEE floating-point standard, the double precession number is 2−52. Therefore, the proposed encryption algorithm has a keyspace calculated as fellow:
4.1 Histogram analysis
The histogram of images is a statistical analysis that determines the distribution of pixels values. Histogram of the uniform distribution formed by the encrypted image indicates the unpredictability of the encryption algorithm. To validate this test, we take different images from USC-SIPI ‘Miscellaneous’ image data set with many textures. We remark that the histogram of encrypted images is different from the original images. Simulation results indicates that the proposed algorithm passes with success the histogram test. (Table 4)
4.2 Correlation analysis of two adjacent pixels
Let, x and y the gray values of two adjacent pixels, and N is the number of pixels selected from the plain image. We take E(x) and E(y) as the mean values of xi and yi. The correlation coefficients of two adjacent pixels is given by
where
with
and
In Table 5, the correlation values of the encrypted image are close to 0, and the uniform distribution of adjacent pixels indicate an excellent evaluation of the algorithm.
The resistance to statistical attacks is confirmed in our proposition.
We selected 3000 adjacent pixels (vertical, horizontal, and diagonal directions) from the original image and encrypted image.
Simulation results presented in Table 6 indicate the correlation of two adjacent pixels for original images taken from USC-SIPI ‘Miscellaneous’ data-set and encrypted images (Airplane, Airport and chemical plant).
4.3 Information entropy analysis
Let ‘m’ is the source of information and ‘p’ is the probability of symbol ‘m’.
The entropy is a parameter that measure the degree of randomness, calculated by
Table 7 calculate the information entropy of the ciphered different images. Compared to other previous algorithms, we can confirm that the proposed method give us an acceptable average value close to 8.
4.4 Differential attack
To test and examine the performance of an encryption algorithm we calculate NPCR (Number of pixel change rate) and UACI (Unified average changing intensity, the following formulas indicate how to determine these parameters. The ideal image encryption algorithm is when UACI is in the range [33.38 33.70] and NPCR >99.50. Simulation results presented in Table 8 indicate the robustness of our proposition.
and
where L is the total number of pixels in the image. C and C′ are respectively the ciphered images before and after one pixel of the plain image is changed. D(i, j) can be defined by
4.5 Randomness Nist 800–22 tests
Nist 800–22 tests, presented in [23] evaluate the randomness property for encryption algorithms. For test, we select different encrypted images, after that we calculate its P values (The formula of each P value for different tests is indicated in [23]), which should be in the interval [0 1]. To validate the randomness test we choose three different images (Airport, Airplane and Chemical plant). (Table 9)
4.6 The speed performance
The speed of encryption algorithm is an important parameter to evaluate the possibility of real-time implementation. Table 10 we present a comparison between our proposition and previous work. We can confirm that our proposition has excellent performance.
Our experiments were realized using Lena image with a 256 × 256 size, microprocessor 2.53 GHz, and ram 3GB. We took the average value of 20 encryption test.
4.7 Noise and data loss attacks
Firstly, in the encrypted image, we added 1% salt and pepper nose; after that, we decrypt the resulted image . Secondly, we replaced a part of the encrypted image (40 × 40, in our case) by black pixels, and we study the decrypted image. The simulations results presented in Fig. 7 indicate that we have received the image even we apply nose or information loss attacks.
5 Conclusion
In this paper, we present a new proposition of cryptosystem based on S-box in the substitution process and a permutation algorithm based on a chaotic map. An optimization algorithm contains intelligent crossover, generates optimal S-box. The height nonlinearity score founded, demonstrate the unpredictability of the encryption algorithm. The presented S-box shows excellent randomness characteristics compared with others presented in previous papers. The permutation process is based on the chaotic sequence results of the logistic map, many statistical and security tests are carried out to show the performance of our proposition.
Our algorithm can be improved by studying the impact of changing the chaotic function in robustness and security. Also, we can enhance our scheme by adding an intelligent selective algorithm to become suitable for video sequences and multimedia information.
References
Artiles JAP, Chaves DPB, Pimentel C (2019) Image encryption using block cipher and chaotic sequences. Signal Process Image Commun 79:24–31
Asgari-Chenaghlu M, Balafar M-A, Feizi-Derakhshi M-R (2019) A novel image encryption algorithm based on polynomial combination of chaotic maps and dynamic function generation. Signal Process 157:1–13
Belazi A, Abd El-Latif AA, Belghith S (2016) A novel image encryption scheme based on substitution-permutation network and chaos. Signal Process 128:155–170
Chidambaram N, Raj P, Thenmozhi K, Rajagopalan S, Amirtharajan R (2019) A cloud compatible dna coded security solution for multimedia file sharing & storage. Multimedia Tools and Applications, pages 1–27
Farah A, Belazi A (2018) A novel chaotic jaya algorithm for unconstrained numerical optimization. Nonlinear Dynamics 93(3):1451–1480
Farah MAB, Guesmi R, Kachouri A, Samet M (2020) A novel chaos based optical image encryption using fractional fourier transform and dna sequence operation. Opt Laser Technol 121:105777
Fridrich J (1998) Symmetric ciphers based on two-dimensional chaotic maps. International Journal of Bifurcation and chaos 8(06):1259–1284
Gueron S, Feghali WK, Gopal V, Makaram R, Dixon MG, Chennupaty S, and Kounavis ME (2019) Flexible architecture and instruction for advanced encryption standard (aes), January 1 2019. US Patent 10,171,232
Guesmi R, Farah MAB, Kachouri A, and Samet M (2014) A novel design of chaos based s-boxes using genetic algorithm techniques. In 2014 IEEE/ACS 11th International Conference on Computer Systems and Applications (AICCSA), pages 678–684. IEEE
Guesmi R, Farah MAB, Kachouri A, Samet M (2016) A novel chaos-based image encryption using dna sequence operation and secure hash algorithm sha-2. Nonlinear Dynamics 83(3):1123–1136
Guesmi R, Farah MAB, Kachouri A, Samet M (2016) Hash key-based image encryption using crossover operator and chaos. Multimed Tools Appl 75(8):4753–4769
Guo C, Chen Y, Liao X (2007) An extended method for obtaining s-boxes based on three-dimensional chaotic baker maps. Chaos, Solitons Fractals 31(3):571–579
Hamza R, Yan Z, Muhammad K, Bellavista P, and Titouna F (2019) A privacy-preserving cryptosystem for iot e-healthcare. Information Sciences
Hayat U, Azam NA (2019) A novel image encryption scheme based on an elliptic curve. Signal Process 155:391–402
Hussain I, Shah T, Gondal MA (2013) Application of s-box and chaotic map for image encryption. Math Comput Model 57(9–10):2576–2579
Hussien AG, Hassanien AE, Houssein EH, Bhattacharyya S, and Amin M (2019) S-shaped binary whale optimization algorithm for feature selection. In Recent trends in signal and image processing, pages 79–87. Springer
Jain A, Rajpal N (2016) A robust image encryption algorithm resistant to attacks using dna and chaotic logistic maps. Multimed Tools Appl 75(10):5455–5472
Jakimoski G, Kocarev L (2001) Chaos and cryptography: block encryption ciphers based on chaotic maps. Ieee transactions on circuits and systems i: fundamental theory and applications 48(2):163–169
Jakimoski G, Kocarev L (2002) Block encryption ciphers based on chaotic maps. IEEE Transaction on Circuits System-I 48:163–169
Kanmani M, Narasimhan V (2018) Swarm intelligent based contrast enhancement algorithm with improved visual perception for color images. Multimed Tools Appl 77(10):12701–12724
Kanmani M, Narasimhan V (2019) An optimal weighted averaging fusion strategy for remotely sensed images. Multidimensional Systems and Signal Processing, pages 1–25
Khan M, Shah T, Mahmood H, Gondal MA, Hussain I (2012) A novel technique for the construction of strong s-boxes based on chaotic lorenz systems. Nonlinear Dyn 70(3):2303–2311
Lawrence E Bassham III, Andrew L Rukhin JS, Nechvatal JR, Smid ME, Barker EB, Leigh SD, Levenson M, Vangel M, Banks DL et al. (2010) Sp 800–22 rev. 1a. a statistical test suite for random and pseudorandom number generators for cryptographic applications
Liang C, Zhang Q, Ma J, Li K (2019) Research on neural network chaotic encryption algorithm in wireless network security communication. EURASIP J Wirel Commun Netw 2019(1):151
Liu H, Kadir A, Niu Y (2014) Chaos-based color image block encryption scheme using s-box. AEU-international Journal of Electronics and Communications 68(7):676–686
Liu H, Kadir A, Gong P (2015) A fast color image encryption scheme using one-time s-boxes based on complex chaotic system and random noise. Opt Commun 338:340–347
Madheswari K, Venkateswaran N (2017) Swarm intelligence based optimisation in thermal image fusion using dual tree discrete wavelet transform. Quantitative Infrared Thermography Journal 14(1):24–43
Manoj RJ, Praveena MDA, Vijayakumar K (2019) An aco–ann based feature selection algorithm for big data. Clust Comput 22(2):3953–3960
Nesa N, Ghosh T, Banerjee I (2019) Design of a chaos-based encryption scheme for sensor data using a novel logarithmic chaotic map. Journal of Information Security and Applications 47:320–328
Özkaynak F, Özer AB (2010) A method for designing strong s-boxes based on chaotic lorenz system. Phys Lett A 374(36):3733–3738
Parvees MYM, Samath JA, Bose BP (2018) Providing confidentiality for medical image—an enhanced chaotic encryption approach. In: Advances in big data and cloud computing. Springer, Singapore, p 309–317
Singh G (2013) A study of encryption algorithms (rsa, des, 3des and aes) for information security. International Journal of Computer Applications, 67(19)
Tang G, Liao X, Chen Y (2005) A novel method for designing s-boxes based on chaotic maps. Chaos, Solitons Fractals 23(2):413–419
Wang X, Lin T, Xue Q (2012) A novel colour image encryption algorithm based on chaos. Signal Process 92(4):1101–1108
Wang X, Liu L, Zhang Y (2015) A novel chaotic block image encryption algorithm based on dynamic random growth technique. Opt Lasers Eng 66:10–18
Xu L, Li Z, Li J, Hua W (2016) A novel bit-level image encryption algorithm based on chaotic maps. Opt Lasers Eng 78:17–25
Yang J, He S, Lin Y, Lv Z (2017) Multimedia cloud transmission and storage system based on internet of things. Multimed Tools Appl 76(17):17735–17750
Ye G, Pan C, Huang X, Mei Q (2018) An efficient pixel-level chaotic image encryption algorithm. Nonlinear Dynamics 94(1):745–756
Zhang Y, Xiao D (2014) An image encryption scheme based on rotation matrix bit-level permutation and block diffusion. Commun Nonlinear Sci Numer Simul 19(1):74–82
Zhang W, Wong K-w, Yu H, Zhu Z-l (2013) An image encryption scheme using reverse 2-dimensional chaotic map and dependent diffusion. Commun Nonlinear Sci Numer Simul 18(8):2066–2080
Acknowledgements
The authors would like to thank the anonymous referees for their valuable comments and suggestions that enhanced the content and the form of this paper.
Author information
Authors and Affiliations
Corresponding author
Ethics declarations
Conflict of interest
The authors declare that they have no conflict of interest.
Additional information
Publisher’s note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
About this article
Cite this article
Farah, M.A.B., Guesmi, R., Kachouri, A. et al. A new design of cryptosystem based on S-box and chaotic permutation. Multimed Tools Appl 79, 19129–19150 (2020). https://doi.org/10.1007/s11042-020-08718-8
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11042-020-08718-8