Abstract
Very recently, Carlet, Méaux and Rotella have studied the main cryptographic features of Boolean functions when, for a given number n of variables, the input to these functions is restricted to some subset E of \(\mathbb {F}_{2}^{n}\). Their study includes the particular case when E equals the set of vectors of fixed Hamming weight, which is important in the robustness of the Boolean function involved in the FLIP stream cipher. In this paper we focus on the nonlinearity of Boolean functions with restricted input and present new results related to the analysis of this nonlinearity improving the upper bound given by Carlet et al.
Similar content being viewed by others
Avoid common mistakes on your manuscript.
1 Introduction
The cryptographic criterion of interest in this manuscript is that of nonlinearity which characterizes the distance between a Boolean function and the set of affine functions (i.e. those of algebraic degree 0 or 1) and is naturally defined using the Hamming distance. More precisely, the nonlinearity of f is the minimum distance to affine functions (in terms of Reed-Muller codes, it is equal to the minimum distance of the linear code Reed-Muller code RM(1, n) ∪ (f + RM(1, n)) where RM(1, n) denotes the Reed-Muller code of order 1 and length 2n). It can be shown that the nonlinearity of a Boolean function in n variables is upper bounded by 2n− 1 − 2n/2 − 1. In order to provide confusion, cryptographic functions must lie at large Hamming distance (in the sense, close to the maximum value 2n− 1 − 2n/2 − 1) to all affine functions, equivalently must be of a large nonlinearity (in the sense, close to the upper bound 2n− 1 − 2n/2 − 1). Boolean functions achieving maximal nonlinearity are called bent functions introduced by Rothaus [8] in 1976 but already studied by Dillon [5] since 1974. For of their own sake as interesting combinatorial objects, but also for their relations to coding theory (Reed-Muller codes), combinatorics (difference sets) and applications in cryptography (design of stream ciphers), they have attracted a lot of research for more than four decades. Two references devoted especially to bent functions and containing a complete survey on bent functions are [3, 7]. It is important to point out that bent functions can not be directly used in the filter and combiner models; in particular, they are not balanced and their algebraic degree does not exceed \(\frac {n}{2}\), which make them weak against fast algebraic attacks [9] even after modifying a number of values small enough to keep good nonlinearity.
In 2016, Méaux, Journault, Standaert and Carlet [6] introduced the cipher FLIP in the context of homomorphic encryption. FLIP is one of the encryption schemes specifically designed to be combined with an homomorphic encryption scheme to improve the efficiency of somewhat homomorphic encryption frameworks. It has been shown that in the context of the FLIP cipher, the important criteria of Boolean functions are the classical ones (balancedness, nonlinearity, algebraic immunity) when, for a given number n of variables, the input to these functions is restricted to some subset E of \(\mathbb {F}_{2}^{n}\). In 2017, Carlet, Méaux and Rotella [4] studied Boolean functions with restricted input and their robustness in the framework of FLIP cipher. In this manuscript, we focus on one parameter of Boolean functions: the nonlinearity with restricted input. We derive new results on the analysis of the nonlinearity with restricted input improving the upper bound given by Carlet, Méaux and Rotella. The paper is organized as follows. In Section 2, we recall some background related to Boolean functions as well as some preliminaries on the nonlinearity of Boolean functions. In Section 3, we focus ourselves on the nonlinearity of Boolean functions with restricted input. Using the moments of the Walsh transform, we first derive in Section 3.1 an upper bound on that nonlinearity (Theorem 7). Next, we push further the analysis of the power sums involved in Theorem 7 and establish a new upper bound on the nonlinearity of Boolean functions with constant weight inputs improving the results of Carlet et al. (Theorem 16).
2 Preliminaries
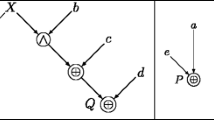
We denote by |I| the cardinality of a finite set I. Let n be any positive integer. In this paper, we shall denote by \(\mathcal {B}_{n}\) the set of all n-variable Boolean functions over \(\mathbb {F}_{2}^{n}\) [1]. Any n-variable Boolean function f (that is, a mapping from \(\mathbb {F}_{2}^{n}\) to \(\mathbb {F}_{2}\)) admits a unique algebraic normal form (ANF), that is, a representation as a multivariate polynomial over \(\mathbb {F}_{2}\):
where the aI’s are in \(\mathbb {F}_{2}\). The terms \({\prod }_{i\in I} {x_{i}}\) are called monomials. The algebraic degree deg(f) of a Boolean function f equals the maximum degree of those monomials whose coefficients are nonzero in its algebraic normal form. A slightly different form for the algebraic normal form is \(f(x)=\bigoplus _{u\in \mathbb {F}_{2}^{n}}a_{u}x^{u}\), where \(a_{u}\in \mathbb {F}_{2}\) and where \(x^{u}={\prod }_{i = 1}^{n}x_{i}^{u_{i}}\). Then deg(f) equals \(\displaystyle \max _{a_{u}\neq 0}\text {wt}(u)\), where wt(u) denotes the Hamming weight of u, that is, wt(u) = |{i = 1,…, n∣ui = 1}|. Given a positive integer r, we make an abuse of notation and denote by RM(r, n) the set of all n-variable Boolean functions of algebraic degrees at most r, that is, the so-called r-th order Reed-Muller code of length 2n. We recall that RM(r, n) is a vector subspace over \(\mathbb {F}_{2}\) of dimension \({\sum }_{i = 0}^{r}{\left (\begin {array}{c} n \\ i \end {array}\right )}\).
The Hamming weight wt(f) of a Boolean function is the size of its support \(\{x\in \mathbb {F}_{2}^{n}\mid f(x)= 1\}\) that we denote by supp(f). The Hamming distance between two n-variable Boolean functions is the Hamming weight of f ⊕ g, that is \(\text {dist}(f,g)=|{\{x\in \mathbb {F}_{2}^{n}\mid f(x)\neq g(x)\}}|\).
Definition 1 (rth-order nonlinearity)
Let f be an n-variable Boolean function. Let r be a positive integer such that r ≤ n. The r-th order nonlinearity of f is the minimum Hamming distance between f and all n-variable Boolean functions from RM(r, n). We shall denote the r-th order nonlinearity of f by nlr(f).
We have
The first-order nonlinearity of f is simply called the nonlinearity of f and is denoted by nl(f) (instead of nl1(f)). Clearly we have nlr(f) = 0 if and only if f has degree at most r. So, the knowledge of the nonlinearity profile (i.e. of all the nonlinearities of orders r ≥ 1) of a Boolean function includes the knowledge of its algebraic degree. It is in fact a much more complete cryptographic parameter than the single (first-order) nonlinearity and the algebraic degree. The best known upper bound on nlr(f) has an asymptotic version [2]:
for every n-variable Boolean function f.
3 Results on the nonlinearity with restricted input
3.1 An upper bound derived from power sums of Walsh transform
Let n be a positive integer. Let E be any subset of \(\mathbb {F}_{2}^{n}\) and let f be any Boolean function defined over E. We define
where “⋅” denotes the standard inner product in \(\mathbb {F}_{2}^{n}\). In [4], the authors have introduced the following definition of the nonlinearity of a Boolean function with restricted input:
Clearly, NLE is invariant under the addition by a Boolean function g whose restriction to E is affine, that is, g(x) = γ ⋅ x + β. Indeed,
Thus, we have the following.
Lemma 2
Let \(g:\mathbb {F}_{2}^{n}\to \mathbb {F}_{2}\) such that g(x) = γ ⋅ x + βfor every x ∈ Ewhere \(\gamma \in \mathbb {F}_{2}^{n}\) and \(\beta \in \mathbb {F}_{2}\). Then NLE(f + g) = NLE(f).
In [4], it is established the following upper bound on this nonlinearity.
Theorem 3 ([4, Proposition 6])
We have
where
Herein \(\mathcal F\) is a family of vector spaces F for each of which there exists \(v\in \mathbb {F}_{2}^{n}\) such that v ⋅ (x + y) = 1for all (x, y) ∈ E2 such that x + y ∈ F⊥∖{0}. Herein and hereafter, F⊥ denotes the dual space of the vector space F.
Remark 4
If \(E=\mathbb {F}_{2}^{n}\), Theorem 3 is the classical “covering radius bound” \(2^{n-1}-2^{\frac {n}{2}-1}\) (since F⊥ = {0}).
Remark 5
Without giving the calculation, we indicate that the theorem above is a direct consequence of the following identity where F is a vector space:
The most important feature is that Theorem 3 does not relies on any property on E but only on the fact that we sum over a vector space.
Considering the case where F is a hyperplane (in that case, the condition of Theorem 3 is satisfied), we have the following most simple bound established in [4]:
Corollary 6
We have
where
and D a f is the derivative of f in the direction of a whose expression is given as follows:
We are going to show that Theorem 3 is a particular case of a more general result. To this end, set
Observe that Sℓ(f, E, F) = 0 if and only if \(\widehat {\chi _{f,E}}\) vanishes on F when ℓ is even. Next,
Thus we arrive at
A direct generalization of Theorem 3 is therefore the following upper bound.
Theorem 7
Let f be a Boolean function over \(\mathbb {F}_{2}^{n}\). Let F be a vectorspace of \(\mathbb {F}_{2}^{n}\) such that \(\widehat {\chi _{f,E}}\) does not vanish on F. Then, every positive integer ℓ,
Remark 8
With our framework, the approach of [4] corresponds to take ℓ = 0 in (2) and to consider particular subspaces F. Indeed, if ℓ = 0, one has
To get the absolute value, it suffices to use Lemma 2 with fv(x) = f(x) + v ⋅ x. According to Lemma 2, one has NLE(f) = NLE(fv) On the other hand,
Now, if v is chosen such that v ⋅ (x + y) = 1 for every (x, y) ∈ E2 such that x + y ∈ F⊥, then
Remark 9
Another approach would have been to use the following naive upper bound:
But it will not give a better upper bound. Indeed, using the Hölder inequality (that is, \({\sum }_{a\in F} \vert u_{a}v_{a}\vert \leq \left ({\sum }_{a\in F} \vert u_{a}\vert ^{p}\right )^{\frac {1}{p}} \left ({\sum }_{a\in F} \vert u_{a}\vert ^{q}\right )^{\frac {1}{q}}\), where \(\frac {1}{p}+\frac {1}{q}= 1\)) with \(p=\frac {\ell + 1}{\ell }\) and q = ℓ + 1, we get
That implies that
that is,
Remark 10
An important feature of Theorem 7 is that the right-hand side is a decreasing sequence. Indeed, by the Cauchy-Schwarz inequality,
which implies that the sequence \(\left (\frac {S_{2\ell + 2}(f,E,F)}{S_{2\ell }(f,E,F)}\right )_{\ell \in {\mathbb N}^{\star }}\) is an increasing sequence. Since Theorem 3 corresponds to the case where ℓ = 0, that says that (3) may be a better upper bound than Theorem 3 for every positive integers ℓ and the particular subspaces F considered in that Theorem.
But above, it is known that \(\frac {{\sum }_{i}\lambda _{i}^{k + 1}}{{\sum }_{i}{\lambda _{i}^{k}}}\) tends to maxiλi as k tends to infinity for any finite sequence of positive numbers λi. That says that, the right-hand side of (4) is a decreasing sequence which tends to \(\frac {|E|}{2}-\frac {1}{2}\max _{a\in F}\vert \widehat {\chi _{f,E}}(a)\vert \) as ℓ tends to infinity.
At this stage, Theorem 7 does not give enough insight on NLE because it does not rely on the structure of E. To understand more deeply what restricting inputs implies on the nonlinearity of a Boolean function, we shall consider particular subsets E in the sequel. But before doing this, we shall push further a bit more the analysis of the power sums S2ℓ(f, E, F) involved in Theorem 7 in the next subsection.
3.2 Analysis of the power sums involved in Theorem 7
3.2.1 A decomposition formula
We begin with a classical calculation:
Let us now split the latter sum as follows
We then deduce from the above calculation
Proposition 11
Let f be a Boolean function over \(\mathbb {F}_{2}^{n}\). Let F be a vectorspace of \(\mathbb {F}_{2}^{n}\) such that \(\widehat {\chi _{f,E}}\) does not vanish on F. Let ℓ be a positive integer. Then
where
and
Proof
Let ℓ be a positive integer. Equation (6) implies that
Decomposition (7) follows then from (5) and
where \(T_{2}(f,E,u)= {\sum }_{\underset {x_{1}+x_{2}=u}{x_{1},x_{2}\in E}} (-1)^{f(x_{1})+f(x_{2})}\). Now, according to Remark 10, \(\frac {S_{2\ell + 2}(f,E,F)}{S_{2\ell }(f,E,F)}\geq \frac {S_{2}(f,E,F)}{S_{0}(f,E,F)}={\sum }_{\underset {x_{1}+x_{2}\in F^{\perp }}{x_{1},x_{2}\in E}} (-1)^{f(x_{1})+f(x_{2})}\) which implies that Rℓ(f, E, F)≥ 0. □
Remark 12
Remark 10 implies also that the sequence \((R_{\ell }(f,E,F))_{\ell \in {\mathbb N}}\) is a non-decreasing sequence. Note that the sum \({\sum }_{\underset {u, v\not \in F^{\perp }}{u+v\in F^{\perp }}}T_{2}(f,E,u)T_{2\ell }(f,E,v)\) is also nonnegative because \({\sum }_{u\in F^{\perp }}T_{2\ell }(f,E,u)=\frac {1}{\vert F\vert }S_{2\ell }(f,E,F)>0\) when \(\widehat {\chi _{f,E}}\) does not vanish on F. Furthermore, if \({\sum }_{\underset {u, v\not \in F^{\perp }}{u+v\in F^{\perp }}}T_{2}(f,E,u)T_{2\ell }(f,E,v) = 0\), then we have \(\frac {S_{2\ell + 2}(f,E,F)}{S_{2\ell }(f,E,F)}=\frac {S_{2}(f,E,F)}{S_{0}(f,E,F)}\). Thus, according to Remark 10, the preceding equality implies that \(\frac {S_{4}(f,E,F)}{S_{2}(f,E,F)}=\frac {S_{2}(f,E,F)}{S_{0}(f,E,F)}\). Next, since equality is achieved in Cauchy-Schwarz inequality if and only the two sequences involved in the inequality are proportional, \((\widehat {\chi _{f,E}})^{2}\) is therefore constant on F. The converse is also true. Hence,
3.2.2 The case ℓ = 1
We are now going to turn our attention to the case where ℓ = 1. As in Section 3.2.1, in the sequel, F denotes a vectorspace of \(\mathbb {F}_{2}^{n}\) such that \(\widehat {\chi _{f,E}}\) does not vanish on F. In that case, Proposition 11 says that:
where
Observe next that
Note that this term is involved in the upper bound stated by Theorem 3. At this stage, we observe that one should deduce from Equation (8) an upper bound on NLE and this upper bound should be better than Theorem 3 provided that the second-term at the right-hand side is positive. Thus, we are now going to study when this term vanishes, that is, when
We have restricted ourselves to suppose that \(\widehat {\chi _{f,E}}\) does not vanish on F. We therefore indicate that (11) is always true when F is a vectorspace such that \(\widehat {\chi _{f,E}}\) vanishes on F according to Remark 12. We have
Proposition 13
Let n > 1 be a positive integer. Let F be a vector space of \(\mathbb {F}_{2}^{n}\) and E be a subset of \(\mathbb {F}_{2}^{n}\) . Let R1(f, E, F) be defined in Proposition 11. Then R1(f, E, F) = 0 for every hyperplane F if and only if T2(f, E, u) = 0 for every u ≠ 0.
Proof
Clearly, if T2(f, E, u) = 0 for every u ≠ 0, (11) holds. Suppose now that (11) holds. Every hyperplane F can be written as F = {0, γ}⊥. Therefore, (11) rewrites as
Now
Suppose that (12) holds for every γ ≠ 0. Then
Hence, \({\sum }_{u\not = 0}\left (T_{2}(f,E,u)\right )^{2}= 0\) implying that T2(f, E, u) = 0 for every u ≠ 0. □
We immediately deduce the following corollary.
Corollary 14
Let n > 1 be a positive integer. Let F be a vector space of \(\mathbb {F}_{2}^{n}\) and E be a subset of \(\mathbb {F}_{2}^{n}\). Let Rℓ(f, E, F) be defined in Proposition 11. Then Rℓ(f, E, F) = 0for every hyperplane F if and only if T2(f, E, u) = 0 for every u ≠ 0.
Proof
Clearly, if T2(f, E, u) = 0 for every u ≠ 0 , then Rℓ(f, E, F) = 0 for any hyperplane F. Conversely, suppose that Rℓ(f, E, F) = 0 for every hyperplane F. According to Remark 12, we have 0 ≤ R1(f, E, F) ≤ Rℓ(f, E, F) = 0. We then conclude thanks to Proposition 13 that T2(f, E, u) = 0 for every u ≠ 0. □
4 Boolean functions with constant weight inputs
In this subsection, we shall consider the subsets \(E=\{x\in \mathbb {F}_{2}^{n}\mid \text {wt}(x)=k\}\) for 0 ≤ k ≤ n. In the sequel, when x and y are in \(\mathbb {F}_{2}^{n}\), we shall denote by z = xy the element of \(\mathbb {F}_{2}^{n}\) such that zi = xiyi for every 1 ≤ i ≤ n. Set E + E = {x + y, (x, y) ∈ E2}.
Let us investigate the particular cases where k ∈{0, 1, n − 1, n}. If k = 0, \( \widehat {\chi _{f,E}}(a) = (-1)^{f(0)}\) while, if k = n, \(\widehat {\chi _{f,E}}(a) = (-1)^{f(1)+\text {wt}(a)}\). In both cases, it implies that NLE(f) = 0. On the other hand, denote ei the element of \(\mathbb {F}_{2}^{n}\) whose all coordinates are equal to 0 except the i th coordinate. Then, if k = 1, \(\widehat {\chi _{f,E}}(a) = {\sum }_{i = 1}^{n}(-1)^{a_{i} + f(e_{i})}\) where ai stands for the i th-coordinate of a. Now, if ai = f(ei) for every 1 ≤ i ≤ n, then \(\widehat {\chi _{f,E}}(a) = n\) and thus \(NL_{E}(f) = \frac {n}{2} - \frac {1}{2}\max _{a\in \mathbb {F}_{2}^{n}}\vert \widehat {\chi _{f,E}}(a)\vert \leq 0\). If k = n − 1, given \(x\in \mathbb {F}_{2}^{n}\), we denote \(\bar x\) the element of \(\mathbb {F}_{2}^{n}\) such that \(\bar x_{i}= 1+x_{i}\). Then, \(\widehat {\chi _{f,E}}(a) = {\sum }_{i = 1}^{n}(-1)^{a_{i} + \text {wt}(a) + f(\bar e_{i})}\). Hence, if \(a_{i}=f(\bar {e_{i}})+\text {wt}(a)\mod 2\) for every 1 ≤ i ≤ n then, we can conclude as precedingly that NLE(f) = 0. In the sequel, we shall therefore suppose that 2 ≤ k ≤ n − 2.
Let us now prove the following.
Lemma 15
\(E+E=\{x+y,\,(x,y)\in E^{2}\}=\{a\in \mathbb {F}_{2}^{n}\mid \text {wt}(a)\leq \min (2k,n),\, \text {wt}(a)= 0\mod 2\}\). Furthermore, for every \(a\in \mathbb {F}_{2}^{n}\), x and x + a are both in E if and only if wt(x) = k and \(\text {wt}(ax)=\frac {\text {wt}(a)}{2}\).
Proof
Recall that wt(x + y) = wt(x) + wt(y) − 2wt(xy). Now the latter equation in x has a solution in E for every a of even hamming weight at most 2k. □
According to the above proposition, if u is of even Hamming weight at most 2k,
while T2(f, E, u) = 0 if wt(u) is odd or greater than 2k. Note, that if u = 0 then T2(f, E,0) = |E|.
We then establish the following new upper bound on NLE.
Theorem 16
Let 2 ≤ k ≤ n − 2. Set \(E=\{x\in \mathbb {F}_{2}^{n}\mid \text {wt}(x)=k\}\). Let f be a Boolean function over \(\mathbb {F}_{2}^{n}\). Then,
where
and
Proof
Let γ ≠ 0 be such that |T2(f, E, γ)| = λ. According to Equation (8), when F = {0, γ}⊥:
We have to distinguish two cases depending on the sign of T2(f, E, γ):
If T2(f, E, γ) is nonnegative, then
$$\begin{array}{@{}rcl@{}} \frac{S_{4}(f,E,F)}{S_{2}(f,E,F)} = |E| + \lambda + \frac{{\sum}_{\underset{u, v\not\in\{0,\gamma\}}{u+v\in\{0,\gamma\}}} T_{2}(f,E,u)T_{2}(f,E,v)}{|E| + \lambda} \end{array} $$Now
$$\begin{array}{@{}rcl@{}} \underset{u, v\not\in\{0,\gamma\}}{\sum\limits_{u+v\in\{0,\gamma\}}} T_{2}(f,E,u)T_{2}(f,E,v) \,=\, \sum\limits_{u\not\in\{0,\gamma\}} \left( T_{2}(f,E,u)\right)^{2} \,+\, \sum\limits_{u\not\in\{0,\gamma\}} T_{2}(f,E,u)T_{2}(f,E,u\,+\,\gamma) \end{array} $$and therefore
$$\begin{array}{@{}rcl@{}} \frac{S_{4}(f,E,F)}{S_{2}(f,E,F)} = |E| + \lambda + \frac{ {\sum}_{u\not\in\{0,\gamma\}} \left( T_{2}(f,E,u)\right)^{2} + {\sum}_{u\not\in\{0,\gamma\}} T_{2}(f,E,u)T_{2}(f,E,u+\gamma)}{|E| + \lambda} \end{array} $$If T2(f, E, γ) is negative, that is, T2(f, E, γ) = −λ. Set fv(x) = f(x) + v ⋅ x with v ≠ 0. Observe that \(T_{2}(f_{v},E,u)=\underset {x+y=u}{\sum \limits _{x,y\in E}} (-1)^{f_{v}(x)+f_{v}(y)}=(-1)^{v\cdot u}T_{2}(f,E,u)\) for every \(u\in \mathbb {F}_{2}^{n}\). If we choose v such that v ⋅ γ = 1 (such v exists since γ ≠ 0), then we have T2(fv, E, γ) = −T2(f, E, γ) = λ. Furthermore,
$$\begin{array}{@{}rcl@{}} \frac{S_{4}(f_{v},E,F)}{S_{2}(f_{v},E,F)} \,=\, |E| + \lambda + \frac{ {\sum}_{u\not\in\{0,\gamma\}} \left( T_{2}(f,E,u)\right)^{2} - {\sum}_{u\not\in\{0,\gamma\}} T_{2}(f,E,u)T_{2}(f,E,u\!+\gamma)}{|E| + \lambda} \end{array} $$
Now
and, according to Lemma 2, NLE(fv) = NLE(f). Thus
We therefore conclude from the two above decompositions of \(\frac {S_{4}(f,E,F)}{S_{2}(f,E,F)}\) and \(\frac {S_{4}(f_{v},E,F)}{S_{2}(f_{v},E,F)}\) that:
proving
Next, according to (10), when F = {0, γ}⊥ with γ of odd weight,
since T2(f, E, γ) = 0. Now, if γ is of odd weight, then, for every u∉{0, γ}, the weights of u and u + γ are of different parity since wt(u + γ) = wt(u) + wt(γ) − 2wt(uγ). Thus T2(f, E, u)T2(f, E, u + γ) = 0 for every u∉{0, γ} according to Lemma 15. Then, we simply get in that case (since T2(f, E, γ) = 0)
yielding that
Proposition 16 follows then from (18) and (19). □
Remark 17
Observe that
Thus
We indicate that, if \(\gamma > {\left (\begin {array}{c} n \\ k \end {array}\right )}^{2}\) then \( \frac {1}{{\left (\begin {array}{c} n \\ k \end {array}\right )}}\gamma -\lambda >{\left (\begin {array}{c} n \\ k \end {array}\right )}-\lambda \geq 0\).
Remark 18
Observe that, if there exists u1≠u2 such that |T2(f, E, u1)| = |T2(f, E, u2)| = λ, γ ≥ 2λ2 > λ2 yielding that 𝜃 > 0. Therefore, \(\max \left (\theta ,\frac {1}{{\left (\begin {array}{c} n \\ k \end {array}\right )}}\gamma -\lambda \right )= 0\) if and only if there exists a unique u ≠ 0 such that |T2(f, E, u)| = λ and 𝜃 = 0, that is, |T2(f, E, v)| = 0 for every v∉{0, u} (observe that γ = T2(f, E, u)2 = λ2 and \(\frac {1}{{\left (\begin {array}{c} n \\ k \end {array}\right )}}\gamma -\lambda =\frac {1}{{\left (\begin {array}{c} n \\ k \end {array}\right )}}\lambda (\lambda -{\left (\begin {array}{c} n \\ k \end {array}\right )})\leq 0\)). In other words, if we are not in this situation, \(\max \left (\theta ,\frac {1}{{\left (\begin {array}{c} n \\ k \end {array}\right )}}\gamma -\lambda \right )\) is positive.
5 Concluding remarks
In the line of the very recent work of Carlet, Méaux and Rotella, we provided a further study of Boolean functions with restricted input. Inspired by the work of Carlet and the first author on the covering radii of binary Reed-Muller codes, we firstly obtained upper bounds on the nonlinearity for Boolean functions with general restricted input. Next, we derived an upper bound in the particular case when the restricted input is the set of vectors of fixed Hamming weight. Our results improved the known upper bound given by Carlet et al. It would be interesting to construct Boolean functions approaching those developed bounds. But such construction would be a very hard work. The reader is kindly invited to join this adventure.
References
Carlet, C.: Boolean functions for cryptography and error correcting codes. In: Crama, Y., Hammer, P. L. (eds.) Boolean Models and Methods in Mathematics, Computer Science, and Engineering, pp 257–397. Cambridge University Press, Cambridge (2010)
Carlet, C., Mesnager, S.: Improving the upper bounds on the covering radii of binary Reed-Muller codes. IEEE Trans. Inf. Theory 53(1), 162–173 (2007)
Carlet, C., Mesnager, S.: Four decades of research on bent functions. Des. Codes Crypt. 78(1), 5–50 (2016)
Carlet, C., Méaux, P., Rotella, Y.: Boolean functions with restricted input and their robustness; application to the flip cipher. IACR Transactions on Symmetric Cryptology (3), 192–227. https://doi.org/10.13154/tosc.v2017.i3.192-227 (2017)
Dillon, J.: Elementary Hadamard difference sets. PhD Thesis, University of Maryland (1974)
Méaux, P., Journault, A., Standaert, F.-X., Carlet, C.: Towards stream ciphers for efficient FHE with low-noise ciphertexts. In: EUROCRYPT 2016, pp. 311–343 (2016)
Mesnager, S.: Binary Bent Functions: Fundamentals and Results. Springer, Switzerland (2016)
Rothaus, O.S.: On “bent” functions. Journal of Combinatorial Theory, Series A 20, 300–305 (1976)
Wang, Q., Johansson, T.: A note on fast algebraic attacks and higher order nonlinearities. In: International Conference on Information Security and Cryptology, Inscrypt 2010, pp. 404–414 (2010)
Author information
Authors and Affiliations
Corresponding author
Additional information
This article is part of the Topical Collection on Special Issue on Boolean Functions and Their Applications
Rights and permissions
About this article
Cite this article
Mesnager, S., Zhou, Z. & Ding, C. On the nonlinearity of Boolean functions with restricted input. Cryptogr. Commun. 11, 63–76 (2019). https://doi.org/10.1007/s12095-018-0293-6
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s12095-018-0293-6