Abstract
Stream cipher is an important branch of symmetric cryptosystems, which takes obvious advantages in speed and scale of hardware implementation. It is suitable for using in the cases of massive data transfer or resource constraints, and has always been a hot and central research topic in cryptography. With the rapid development of network and communication technology, cipher algorithms play more and more crucial role in information security. Simultaneously, the application environment of cipher algorithms is increasingly complex, which challenges the existing cipher algorithms and calls for novel suitable designs. To accommodate new strict requirements and provide systematic scientific basis for future designs, this paper reviews the development history of stream ciphers, classifies and summarizes the design principles of typical stream ciphers in groups, briefly discusses the advantages and weakness of various stream ciphers in terms of security and implementation. Finally, it tries to foresee the prospective design directions of stream ciphers.
Article PDF
Similar content being viewed by others
Avoid common mistakes on your manuscript.
References
Rivest R. The RC4 encryption algorithm. Rsa Data Secur Inc Doc No, 1992, 20: 86–96
Anderson D P, Herrtwich R G. Internet communication with end-to-end performance guarantees. In: Telekommunikation und multimediale Anwendungen der Informatik. Berlin: Springer, 1991
ETSI/SAGE. Specification of the 3GPP confidentiality and integrity algorithms UEA2&UIA2. Document 2: SNOW 3G Specification, Version 1.1, 2006. http://www.gsmworld.com/using/algorithms/docs/etsi_sage_06_09_06.pdf
Feng X T. ZUC algorithm: 3GPP LTE international encryption standard. China Inform Secur, 2011, 19: 45–46
Bluetooth. Specification of the Bluetooth system. 2005. https://www.bluetooth.com/specifications/adoptedspecifications
Ekdahl P, Johansson T. A new version of the stream cipher SNOW. In: Proceedings of International Workshop on Selected Areas in Cryptography, 2002. 47–61
Ekdahl P, Johansson T. SNOW-a new stream cipher. 2007. https://pdfs.semanticscholar.org/900e/081fa7ba0d0b45e36185e327e1081bf55d28.pdf
European Commission. First open NESSIE workshop. 2000. https://www.cosic.esat.kuleuven.be/nessie/workshop/
Hawkes P, Rose G G. Guess-and-determine attacks on SNOW. In: Proceedings of International Workshop on Selected Areas in Cryptography, 2002. 37–46
Markku-Juhani O S. A time-memory tradeoff attack against LILI-128. In: Proceedings of International Workshop on Fast Software Encryption, 2002
Tsunoo Y, Saito T, Shigeri M, et al. Shorter bit sequence is enough to break stream cipher LILI-128. IEEE Trans Inform Theory, 2005, 51: 4312–4319
Imai H, Yamagishi A. CRYPTREC project — cryptographic evaluation project for the japanese electronic government. In: Proceedings of International Conference on the Theory and Application of Cryptology and Information Security: Advances in Cryptology, 2000. 399–400
Watanabe D, Furuya S, Yoshida H, et al. A new keystream generator MUGI. In: Proceedings of International Workshop on Fast Software Encryption, 2002. 179–194
van Tilborg H C A, Jajodia S. ECRYPT Stream Cipher Project. Berlin: Springer. 2011
Robshaw M. The eSTREAM project. In: New Stream Cipher Designs. Berlin: Springer, 2008
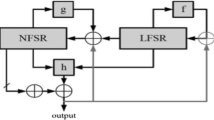
Hell M, Johansson T, Meier W. Grain: a stream cipher for constrained environments. Int J Wirel Mobile Comput, 2007, 2: 86–93
Canniere C D, Preneel B. TRIVIUM specifications. eSTREAM, ECRYPT Stream Cipher Project, 2006. http://www.ecrypt.eu.org/stream/
Babbage S, Dodd M. The stream cipher MICKEY 2.0. eSTREAM, ECRYPT Stream Cipher Project, 2006. http://www.ecrypt.eu.org/stream/
Robshaw M, Billet O. New Stream Cipher Designs. Berlin: Springer, 2008
Berbain C, Billet O, Canteaut A, et al. SOSEMANUK, a fast software-oriented stream cipher. In: New Stream Cipher Designs. Berlin: Springer, 2008. 98–118
Boesgaard M, Vesterager M, Pedersen T, et al. Rabbit: a new high-performance stream cipher. In: Proceedings of International Workshop on Fast Software Encryption, 2003. 307–329
Wu H J. The stream cipher HC-128. In: New Stream Cipher Designs. Berlin: Springer, 2008. 39–47
Cruz J R C. Keccak: the new SHA-3 encryption standard. 2014
Chakraborti A, Chattopadhyay A, Hassan M, et al. TriviA: a fast and secure authenticated encryption scheme. In: Proceedings of International Workshop on Cryptographic Hardware and Embedded Systems, 2015. 330–353
Wu H J. ACORN: a lightweight authenticated cipher (v3). CAESAR Submission, 2016. http://competitions.cr.yp.to/caesar-submissions.html
Shannon C E. A mathematical theory of communication. Bell Syst Technical J, 1948, 27: 379–423
Fontaine C. Synchronous stream cipher. In: Encyclopedia of Cryptography and Security. Beilin: Springer, 2005. 1274–1275
Millan W, Dawson E. On the security of self-synchronous ciphers. In: Proceedings of Australasian Conference on Information Security and Privacy, 1997. 159–170
Massey J. Shift-register synthesis and BCH decoding. IEEE Trans Inform Theory, 1969, 15: 122–127
Ere C D, Johansson T, Preneel B. Cryptanalysis of the Bluetooth Stream Cipher. Cosic Internal Report, 2001
Lu Y, Vaudenay S. Cryptanalysis of an E0-like combiner with memory. J Cryptol, 2008, 21: 430–457
Armknecht F, Mikhalev V. On lightweight stream ciphers with shorter internal states. In: Proceedings of International Workshop on Fast Software Encryption, 2015. 451–470
Ghafari V A, Hu H G, Chen Y. Fruit-v2: ultra-lightweight stream cipher with shorter internal state. 2016. https://eprint.iacr.org/2016/355
Ghafari V A, Hu H G. Fruit-80: a secure ultra-lightweight stream cipher for constrained environments. Entropy, 2018, 20: 180
Mikhalev V, Armknecht F, M¨uller C. On ciphers that continuously access the non-volatile key. IACR Trans Symmetric Cryptol, 2016, 2016: 52–79
Zhang B, Gong X X. Another tradeoff attack on Sprout-like stream ciphers. In: Proceedings of International Conference on the Theory and Application of Cryptology and Information Security, 2014. 561–585
Lallemand V, Naya-Plasencia M. Cryptanalysis of full Sprout. In: Proceedings of Annual Cryptology Conference, 2015. 663–682
Esgin M F, Kara O. Practical cryptanalysis of full Sprout with TMD tradeoff attacks. In: Proceedings of International Conference on Selected Areas in Cryptography, 2015. 67–85
M´eaux P, Journault A, Standaert F X, et al. Towards stream ciphers for efficient FHE with low-noise ciphertexts. In: Proceedings of Annual International Conference on the Theory and Applications of Cryptographic Techniques, 2016. 311–343
Duval S, Lallemand V, Rotella Y. Cryptanalysis of the FLIP family of stream ciphers. In: Proceedings of Annual International Cryptology Conference, 2016. 457–475
Yu Y, Pereira O, Yung M. Practical leakage-resilient pseudorandom generators. In: Proceedings of the 17th ACM Conference on Computer and Communications Security, 2010. 141–151
Faust S, Pietrzak K, Schipper J. Practical leakage-resilient symmetric cryptography. In: Proceedings of International Conference on Cryptographic Hardware and Embedded Systems, 2012. 213–232
Yu Y, Standaert F X. Practical leakage-resilient pseudorandom objects with minimum public randomness. In: Proceedings of Cryptographers’ Track at the RSA Conference, 2013
Qu L J, Feng K Q, Liu F, et al. Constructing symmetric boolean functions with maximum algebraic immunity. IEEE Trans Inform Theory, 2009, 55: 2406–2412
Peng J, Wu Q S, Kan H B. On symmetric Boolean functions with high algebraic immunity on even number of variables. IEEE Trans Inform Theory, 2011, 57: 7205–7220
Wang H, Peng J, Li Y, et al. On 2k-variable symmetric Boolean functions with maximum algebraic immunity k. IEEE Trans Inform Theory, 2012, 58: 5612–5624
Li N, Qi W F. Symmetric Boolean function with maximum algebraic immunity on odd number of variables. 2005. arXiv:cs/0511099
Rueppel R A. Analysis and Design of Stream Ciphers. Berlin: Springer, 1986
Simpson L R, Dawson E, Golic J D, et al. LILI keystream generator. In: Proceedings of International Workshop on Selected Areas in Cryptography, 2000. 248–261
Ekdahl P, Johansson T, Maximov A, et al. A new SNOW stream cipher called SNOW-V. 2018. https://eprint.iacr.org/2018/1143.pdf
Hell M, Johansson T, Maximov A, et al. A stream cipher proposal: Grain-128. In: Proceedings of IEEE International Symposium on Information Theory, 2006. 1614–1618
°Agren M, Hell M, Johansson T, et al. Grain-128a: a new version of Grain-128 with optional authentication. Int J Wirel Mobile Comput, 2011, 5: 48–59
Hamann M, Krause M, Meier W. LIZARD — a lightweight stream cipher for power-constrained devices. IACR Trans Symmetric Cryptol, 2017, 2017: 45–79
Hamann M, Krause M. On stream ciphers with provable beyond-the-birthday-bound security against time-memorydata tradeoff attacks. Cryptogr Commun, 2018, 10: 959–1012
Canteaut A, Carpov S, Fontaine C, et al. Stream ciphers: a practical solution for efficient homomorphic-ciphertext compression. In: Proceedings of International Conference on Fast Software Encryption, 2016
Arnault F, Berger T P. F-FCSR: design of a new class of stream ciphers. In: Proceedings of International Workshop on Fast Software Encryption, 2005. 83–97
Hell M, Johansson T. Breaking the F-FCSR-H stream cipher in real time. In: Proceedings of the 14th International Conference on the Theory and Application of Cryptology and Information Security, Melbourne, 2008. 557–569
Daemen J, Clapp C. Fast hashing and stream encryption with PANAMA. In: Proceedings of the 5th International Workshop on Fast Software Encryption, Paris, 1998. 60–74
Rivest R L, Schuldt J C N. Spritz — a spongy RC4-like stream cipher and hash function. 2016. https://eprint.iacr.org/2016/856
Banik S, Isobe T, Morii M. Analysis and improvements of the full spritz stream cipher. IEICE Trans Fund, 2017, 100: 1296–1305
Wu H J. A new stream cipher HC-256. In: Proceedigns of International Workshop on Fast Software Encryption, 2004. 226–244
Bernstein D J. ChaCha, a variant of Salsa20. 2009. http://cr.yp.to/chacha/chacha-20080120.pdf
Mileva A, Dimitrova V, Velichkov V. Analysis of the authenticated cipher MORUS (v1). In: Proceedings of International Conference on Cryptography and Information Security in the Balkans, 2016. 45–59
Dobraunig C, Eichlseder M, Mendel F, et al. Ascon — submission to the CAESAR competition. 2016
Wu H J, Preneel B. AEGIS: a fast authenticated encryption algorithm. In: Proceedings of International Conference on Selected Areas in Cryptography, 2013. 185–201
Ivica N. Tiaoxin-346, version 2.1. CAESAR Submission, 2016
Biryukov A. A New 128-bit Key Stream Cipher LEX. Estream Ecrypt Stream Cipher Project Report, 2008
Halevi S, Coppersmith D, Jutla C S. Scream: a software-efficient stream cipher. In: Proceedings of International Workshop on Fast Software Encryption, 2002. 195–209
Jean J, Nikoli´c I, Peyrin T, et al. Deoxys v1.41. 2016. http://competitions.cr.yp.to/round3/deoxysv141.pdf
Krovetz T, Rogaway P. OCB (v1.1). 2016. https://competitions.cr.yp.to/round3/ocbv11.pdf
Andreea E, Bogdanov A, Datta N, et al. COLM v1. 2016. http://competitions.cr.yp.to/caesar-submissions.html
Wu H J, Huang T. The JAMBU lightweight authentication encryption mode (v2.1). 2016. http://competitions.cr.yp.to/caesar-submissions.html
Albrecht M R, Rechberger C, Schneider T, et al. Ciphers for MPC and FHE. In: Proceedings of Annual International Conference on the Theory and Applications of Cryptographic Techniques, 2015
Shamir A. The generation of cryptographically strong pseudo-random sequences. In: Proceedings of IEEE Workshop on Communications Security, Santa Barbara, 1981
Blum M, Micali S. How to generate cryptographically strong sequences of pseudo-random bits. SIAM J Comput, 1984, 13: 850–864
Yao A C. Theory and applications of trapdoor functions (extended abstract). In: Proceedings of the 23rd Annual Symposium on Foundations of Computer Science, Chicago, 1982. 80–91
Goldreich O, Levin L A. A hard-core predicate for all one-way functions. In: Proceedings of the 21st Annual ACM Symposium on Theory of Computing, Seattle, 1989. 25–32
Berbain C, Gilbert H, Patarin J. QUAD: a multivariate stream cipher with provable security. J Symb Comput, 2009, 44: 1703–1723
Biryukov A, Shamir A. Cryptanalytic time/memory/data tradeoffs for stream ciphers. In: Proceedigns of International Conference on the Theory and Application of Cryptology and Information Security, 2000
Courtois N T, Meier W. Algebraic attacks on stream ciphers with linear feedback. In: Proceedings of International Conference on the Theory and Applications of Cryptographic Techniques, 2003. 345–359
Courtois N T. Fast algebraic attacks on stream ciphers with linear feedback. In: Proceedings of Annual International Cryptology Conference, 2003. 176–194
Meier W, Staffelbach O. Fast correlation attacks on certain stream ciphers. J Cryptology, 1989, 1: 159–176
Berbain C, Gilbert H, Maximov A. Cryptanalysis of grain. In: Proceedings of International Workshop on Fast Software Encryption, 2006
Biham E, Dunkelman O. Differential Cryptanalysis in Stream Ciphers. Technical Report CS-2007-10, 2007
Biryukov A, Wagner D. Slide attacks. In: Proceedings of International Workshop on Fast Software Encryption, 1999. 245–259
Dinur I, Shamir A. Cube attacks on tweakable black box polynomials. In: Proceedigns of Annual International Conference on the Theory and Applications of Cryptographic Techniques, 2009. 278–299
Barenghi A, Breveglieri L, Koren I, et al. Fault injection attacks on cryptographic devices: theory, practice, and countermeasures. Proc IEEE, 2012, 100: 3056–3076
Acknowledgements
This work was supported by National Natural Science Foundation of China (Grant No. 61902030).
Author information
Authors and Affiliations
Corresponding authors
Rights and permissions
About this article
Cite this article
Jiao, L., Hao, Y. & Feng, D. Stream cipher designs: a review. Sci. China Inf. Sci. 63, 131101 (2020). https://doi.org/10.1007/s11432-018-9929-x
Received:
Accepted:
Published:
DOI: https://doi.org/10.1007/s11432-018-9929-x