Abstract
After a disaster occurs, effective communication between the people and the institutions of disaster or emergency management is vital. Device to device (D2D) discovery and communication provides communication services in such difficult situations without the requirement of network infrastructure and by reducing call traffic in cellular communication networks. Considering the fact that almost everyone uses a smart mobile device (UE-User Equipment), the D2D communication method seems the most suitable solution for a post-disaster situation. In particular, this method plays important role in fifth generation 5G communication networks. The device discovery or UE discovery is fundamental strategy in D2D communication. In this study, a Throughput-based Discovery Algorithm (TDA) is proposed to find D2D peers among devices on Public Security Network (PSN) in a post-disaster situation. A sample scenario was created to test the performance of the proposed TDA, and the TDA was compared to some discovery algorithms, such as Shortest Distance Algorithm (SDA), Maximum SINR with No limit on the distance of discovery Algorithm (MSNA), and Maximum SINR with Limit on the distance of discovery Algorithm (MSLA). In terms of the outage SINR and average pair SINR metrics, the proposed TDA showed better performance than the other discovery (MSNA, SDA, and MSLA) algorithms for D2D discovery in the disaster area.
Graphic Abstract

Similar content being viewed by others
Avoid common mistakes on your manuscript.
1 Introduction
Disasters such as earthquakes, landslides, and tornadoes are among the most notable events that damage the infrastructure-worldwide [1, 2]. Communication is vital for post-disaster, between people and disaster management organizations [3,4,5]. Effective disaster management which is crucial for governments can be achieved by obtaining fast and accurate information from the disaster area [6, 7]. During or after a disaster, communication can collapse due to damages to the communication infrastructure or of overloading users keeping in contact with friends and relatives. As a consequence, disaster victims are unable to communicate with those outside the affected area and cannot be monitored by rescue teams [8, 9].
D2D communication technology provides communication services in disaster situations without the help of network infrastructure by reducing the call traffic in the cellular communication network [10,11,12]. In next-generation 5G communication networks, D2D communication technology is thought to play a critical role as smart mobile devices (UE-User Equipment) will be used by everyone [13, 14]. The D2D communication method stands out in the field of post-disaster search, rescue, and communication. Current studies in D2D can be divided into coverage area and out of coverage area according to the base station’s (BS) signal coverage [15, 16]. The UEs can communicate with central BSs as well as to other UEs in the coverage area.
D2D communication can be classified into two main elements: device discovery and communication. D2D discovery is the process of finding nearby devices to establish a direct communication link (direct mode). Device discovery is divided into two types [17]: direct discovery and Evolved Packet Core (EPC) level discovery. In the case of direct discovery, the UE autonomously searches for nearby UE devices; this process requires UE devices to participate in the device discovery in order to transmit/receive discovery signals seamlessly. The subjects of D2D discovery on Public Security Network (PSN) studies can be summarized as schema design [18], routing (multihop) [19,20,21,22], clustering [23, 24], energy-spectrum efficiency [25, 26], performance evaluation [27,28,29] and UE discovery [30, 31].
The SINR (Signal to Interference plus Noise Ratio) metric is a significant parameter for peer to peer (P2P) discovery. In the study of Osman [31], some D2D discovery algorithms are proposed according to the SINR metrics and distances between UEs. These are Short Distance Algorithm (SDA), Maximum SINR with No limit on the distance of discovery Algorithm (MSNA), and Maximum SINR with Limit on the distance of discovery Algorithm (MSLA). SDA discovers the D2D pairs according to the shortest distance and therefore selects only the two closest pairs. MSNA is a discovery algorithm that finds D2D pairs according to the maximum SINR without limit distance between UEs. MSLA is a discovery algorithm that searches D2D pairs according to high SINR values under limit distance. However, there are some shortcomings and weak points in these discovery algorithms.
The communication probability of UEs increases if there are many matching D2D pairs in the post-disaster area. In D2D communication, the improvements in reducing energy consumption and increasing throughput play a critical role. Therefore, we focused on the throughput metric in the device discovery algorithm. We proposed a Throughput-based Discovery Algorithm (TDA) which finds D2D pairs according to the throughput metric between UEs. The results show that TDA provides more D2D pairs for the disaster area compared to the discovery algorithms that use the distance and SINR value between UEs. The outage SINR (inability to serve-percentage) obtained by the proposed TDA is lower in the disaster area, so it provides better service quality than others. UEs with the low outage SINR and with multiple matching UE pairs will ensure uninterrupted communication. The focus of our study and motivation is to find the most matching UEs with the lowest outage SINR among D2D peers on the PSN in the out-of-disaster area.
The rest of the paper is organized as follows: D2D standardization, studies about D2D discovery on LTE and PSN in the literature are given in Sect. 2. Modeling of the proposed D2D discovery algorithm (TDA) is defined in Sect. 3. The general structure of the system, a sample scenario, and simulation results are presented in Sect. 4. In Sect. 5, we present conclusion and future works.
2 Preliminary
2.1 D2D Standardization
D2D communication benefits both 3GPP (Third Generation Partnership Project) and LTE (Long Term Evolution) cellular networks in terms of both cost-effectiveness and network performance. In particular, D2D communication improves network efficiency, end-to-end latency, resource utilization, and energy efficiency. At the same time, D2D supports many applications such as social networks, data sharing and games. Therefore, enabling D2D communication over LTE greatly improves the performance of the network. For D2D communication, a customized system architecture and channel models are utilized as ProSe (Proximity Service) in 3GPP, LTE version 12 [7, 32, 33]. Figure 1 shows device pairs for D2D ProSe communication.
In Fig. 1, blue solid lines indicate the connection between UEs, and orange dashed lines represent the control signal between the UEs and the BSs. One of the devices sends the discovery signal, and the other receives this signal. For instance, while the UE2 is in receiver mode, the UE1 sends a discovery signal in transmit mode. Likewise, when the UE2 acts as a sender, the UE1 remains the receiver mode.
Table 1 summarizes the coverage area according to the D2D scenarios shown in Fig. 1. Scenario 1-A represents the D2D discovery and communication mode (direct mode) in cases that the base station is damaged or the base station signal is not received (out of range). Scenario 1-B signifies the partial coverage situation that one of the devices is within the coverage area and the other is outside the coverage area. Scenario 1-C shows the status of the devices within the coverage area in a single cellular structure. Scenario 1-D represents the state of the multi-cellular structure of devices within range.
D2D discovery and communication are vital functions that support the service of ProSe D2D. The architecture of the D2D system, which assists the ProSe service, consisting of D2D discovery and communication, was studied by 3GPP. In LTE version 13, the use of D2D/ProSe and mission-critical communications including 3GPP, small cells, resource efficiency, spectrum bands and heterogeneous network (HetNet) were improved. In particular, public safety functions in version 12, which consist of D2D discovery based on LTE and D2D communications, public security requirements, were also maintained by version 13. In addition, D2D communication has been enhanced in terms of partial coverage and extension coverage for out-of-coverage [7, 16].
2.2 D2D Discovery and LTE
In the study of Doppler and his colleagues, D2D communication, which forms the basis of the 3GPP LTE-Advanced (LTE-A) cellular network, was considered as a facilitator of regional services with restricted interference effect on the primary cellular network [34]. The novel mechanisms for the management of D2D communication procedures and their session setup in the LTE network were proposed. In another paper presented by Doppler and his friends, a novel beaconing scheme was proposed for a service and device discovery radio. This scheme is based on the Orthogonal Frequency-Division Multiple Access (OFDMA) principle and the LTE beacon structure. The devices like smartphones can create a background network using the recommended marking scheme without significantly decrease standby operating time in accordance with energy consumption analysis [35].
In the study of Tang and her colleagues, the problem of neighbour discovery was addressed to enable D2D communication in standard LTE cellular networks. The performances of the proposed methods for neighbour discovery were evaluated in terms of various system parameters in LTE deployment [36]. Simsek and her friends propose a system-level simulator based on 3GPP and compare the performances of three discovery resources selection algorithms (the greedy, the random, and coordinated algorithms) [37]. The results show that the random approach is worse than the other algorithms.
In the study of Vasudevan and his colleagues, the algorithm was proposed and analyzed for the discovery of neighbouring nodes in wireless networks. In the same study, an ALOHA-like neighbour discovery algorithm was presented with a single-hop wireless node network [38]. Sun and his friends present a friend neighbour discovery protocol scheme. This scheme, proposed by adding front handshaking subsets in front of conventional slots [39].
Yang and his colleagues presented a distributed mapping protocol for LTE-A networks. In this study, a resource allocation algorithm was recommended to minimize resource consumption in the discovery which is similar to the adaptive FlashLinqQ structure based on the number of D2D UEs requesting. In the same study, peer to peer (P2P) UE discovery times were compared [40]. In the study of Zou and her colleagues, a discovery signal was proposed as the activator of P2P communication inside the physical layer level in the OFDMA cellular system. The proposed signal has high power efficiency, high noise tolerance, and minimum overhead [41]. In another paper presented by Zou and her friends, a signature-based discovery scheme was presented as a notional instance for cellular networks [42].
In the study of Yang and his colleagues, a device discovery scheme was proposed similar to the FlashLinqQ structure using a marker in conjunction with the conventional packet-based scheme suitable for LTE cellular network architecture [43]. Hayat and his friends presented a discovery algorithm called Sphere Decoder Like (SDL) within a lattice area with radius R to ensure D2D communication [44].
2.3 D2D Discovery and PSN
D2D communication can be used to provide Public Protection and Disaster Relief (PPDR) and National Security and Public Safety (NSPS) services. For example, the spectrum is allocated in the 700 MHz frequency band for an LTE-based Public Safety Network (PSN). PPDR and NSPS-enabled systems ensure access to cellular network services even if the infrastructure becomes dysfunctional due to disaster or emergency. A literature brief in this area is presented below:
In the study of Fodor and his colleagues, a procedure-based clustering was proposed to the design of a system integrating cellular and specific modes of operation. This system was improved to depend on the presence of substructure nodes of LTE networks, and in particular D2D communication. The proposed approach is recognized as a technology component of the 5G which is developed by mobile and wireless communications enablers for 2020 information society (METIS) that is the European 5G research project [24]. Gomez and her colleagues introduced a hybrid base station (HyeNB) scheme to reduce the dependency between UE, eNBs, and EPC for virtual and distributed architectures in the LTE mobile network [18].
Yuan and his colleagues presented dynamically select multi-path routes together in a fully loaded cellular network for D2D communication. In their study, as a modeling scenario, in case of a terrorist act for Ottawa city, communication infrastructure is damaged. It has been shown that Interference Aware Routing (IAR) provides better results than the Broadcast Routing (BR) and Shortest Path Routing (SPR) [45]. In the study of Lin and his colleagues was presented an overview of 3GPP ProSE. LTE devices with D2D support were reported that PSN was more conducive than commercial networks in the absence of cellular networks [17]. In the study of Babun and his colleagues, D2D communication has was discussed to extend the coverage of active BSs in the case of partial coverage in the PSN. A system-level simulator was presented for HetNet and D2D technologies in consideration of PSN scenarios 3GPP standard-compliant. The simulator was used to show the performance of D2D multi-hop communication under cellular networks according to partial coverage [22].
The study of Kamran and his colleagues was focussed on relay-supported transmission architecture performance which can increase the capacity and power savings of the PSN. At the same time, a distance-based strategy was proposed to decrease power transmission and computational complexity [46]. In another work, Kamran and his friends were proposed an approach with clustering procedure to a system structure integrating D2D and cellular operating modes. This approach was depended on the presence of substructure nodes to enable PSN, and especially D2D communication [10]. In another paper presented by Kamran and his friends, it was focused on reuse mode in terms of spectrum efficiency. The simultaneous wireless information, power transmission (SWIPT), and energy harvesting (EH) in the relay (R) were used to extend the life of the energy-constrained network. The communication services can be sustained by integrating the cluster building technique with D2D communication into cellular networks when the cellular infrastructure has partly dysfunctional [23].
Wang and his colleagues were focussed to rebuild capacity the post-disaster network, based on the award-winning Steiner Tree. It was aimed to recover the network from the BS which is still operational to the out of service evacuation places by using a multi-hop technique. The proposed plan was evaluated to present the assessment results more accurately, using the BS data and actual evacuation site in the Tokyo city and using big data analysis based on the post-disaster service model [47].
In the study of Osman, D2D communication and discovery methods were examined in 5G communication systems. In this study, randomly distributed D2D devices were calculated output D2D was found percentages and was made comparisons of MSNA, SDA, MSLA algorithms for single and multiple cells within the determined area [31].
In the study of Marttin and his colleagues, it was investigated the capacity, bandwidth, spectrum, and energy efficiency calculations in the LTE network standard for an example scenario. In this study, it was shown that the energy efficiency of the UE with a large bandwidth reduces quickly according to the UE with a small bandwidth, when the communication distance between the D2D increases [26].
In the study of Hossain and his colleagues, a novel method named SmartDR was proposed which helps post-disaster recovery using smartphones.This method includes multihop routing and neighbour discovery for D2D [48]. Hayat and his colleagues presented SSA named device discovery-based scanning algorithm on the cell sector. This algorithm includes a random walk and velocity scenarios according to received signal strength (RSS) in a special area [30].
Table 2 summarizes the PSN-related studies given briefly in this paper in terms of some keywords. These keywords are device discovery, schema design, and multihop for routing, clustering, throughput, energy-spectrum efficiency, and performance evaluation.
3 D2D Discovery System Model
3.1 D2D Discovery and Problem Formulation
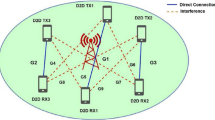
In this section, the D2D discovery system model is presented as a short brief by using model equations. In D2D communication, successful device discovery enables among UEs to intercommunicate immediately. Figure 2 shows the D2D system model for device discovery in a single cell as a scenario example. In this figure, the blue solid lines denote the direct connection between UE pairs; the orange dashed lines represent the interferences between D2D receivers and D2D transmitter.
D2D discovery system model in a single cell [34]
The calculation of the SINR metric (\({\upgamma }\)) is given below:
where S denotes the incoming signal power, I stands for the interference power of the other signals in the network, and N represents the noise. The power of the incoming signal S is calculated as given in Eq. (2):
where \({S}^{(i,j)}\) is the signal power between ith UE and jth UE, \({P}_{T}^{(i,j)}\) represents transmit power, \({G}_{T}^{(i,j)}\) stands for transmitter antenna gain, \({G}_{R}^{(i,j)}\) is receiver antenna gain, \(PL\) stands for path loss, \({d}_{i,j}\) denotes the distance between ith UE and jth UE, \({h}_{i}\) represents the fading coefficient. The formula used for interference calculation between ith and jth UEs is given in Eq. (3):
where \(I^{{\left( {i,j} \right)}}\) denotes interference between ith UE (transmitter) and jth UE (receiver). The noise used in the calculation of the SINR metric is Additive White Gaussian Noise (AWGN). According to the D2D system model in Fig. 2, for example, the calculation of SINR (\({\upgamma }_{RX1}\)) is presented below for D2D communication between TX1 and RX1 UEs.
where \(P_{TX1}\), \(P_{TX2}\), \(P_{TX3}\) represent the transmit powers of TX1, TX2, TX3, \({N}_{0}\) denotes the Additive White Gaussian Noise, \({G}_{T}^{(TX\_,RX1)}\) stands for transmitter antenna gains between RX1 and other transmitter UEs (TX1-3), \({G}_{R}^{(TX\_,RX1)}\) is receiver antenna gains between RX1 and other transmitter UEs (TX1-3), \(PL\) is the path loss, \({d}_{TX\_,RX}\) denotes the distances between RX1 and other transmitter UEs (TX1-3), \({h}_{TX\_}\) represents the fading coefficients of the transmitters. The path loss model, constant propagation loss [49] and Log-Normal Shadowing models [50] are given below:
where n denotes the path loss exponent, \({d}_{0}\) represents the reference distance, \({X}_{\sigma }\) stands for the random shadowing effect. \(\stackrel{-}{PL}\left({d}_{0}\right)\) denotes the path loss at the reference distance (\({d}_{0}\)) and it is given in Eq. (9).
\({f}_{c}\) stands for the transmission frequency. The distances for each D2D point are considered separately. For the distance of two nodes in the coordinate plane, the Euclidean distance relation is used as below:
where \(\left({x}_{T},{y}_{T}\right)\) represents the location of the UE transmitter, \(\left({x}_{R},{y}_{R}\right)\) represents the location of the UE receiver. The throughput (\({R}^{(i,j)}\)) for each D2D uplink scenario is calculated as given below:
where, \(B\) denotes the bandwitdh and \({S}^{(i,j)}\) stands for the signal power between ith UE and jth UE, and \({N}^{(i,j)}\) represents the noise between ith UE and jth UE. In Eq. (12), the energy efficiency (\(EE\)) is calculated for a single hope (node-to-node) according to the bandwidth and the noise ratio.
Here, \({\upzeta }^{\left(i,j\right)}\) denotes signal to noise ratio and \({\mathrm{log}}_{2}(e)\) represents the natural logarithm.
3.2 Throughput Based Discovery Algorithm (TDA)
In this sub-section, the proposed Throughput based Discovery Algorithm (TDA) is presented to discover the UEs on PSN for post-disaster. This algorithm finds the UEs in the network according to the throughput metric. D2D pairs are determined when they exceed the minimum threshold of throughput and then the best pair with maximum throughput values is found. The proposed TDA aims to select pre-communication D2D pairs without SINR-based distance limit. The best D2D pair with TDA is calculated as follows:
where \({R}_{th}\) stands for the threshold of throughput, \({N}_{UE}\) represents the number of UEs. The first constraint ensures that the throughput value between ith UE and jth UE is greater than the threshold of throughput. The second constraint ensures that the selected users can not be out of the range between 1 and \({N}_{UE}\). The last constraint makes the selected users different from themselves. The pseudocode of the TDA is given in Algorithm 1, and the proposed algorithm's flowchart is shown in Fig. 3.

3.3 Shortest Distance Discovery Algorithm (SDA)
In this discovery algorithm, the selection procedure is based on the shortest distance between UEs. D2D pair with the minimum distance is selected and if this pair meets the minimum SINR threshold, it is determined as the best pair [31]. The best D2D pair is found by SDA as given below:
where \( d^{{\left( {i,j} \right)}} \) denotes the distance between ith UE and jth UE, \({\upgamma }_{th}\) represents the threshold of SINR. The 1st and 2nd constraints provide that the SINR values as bidirectional between ith UE and jth UE is bigger than the SINR threshold values. The 3rd constraint ensures that the selected users are in the range between 1 and \({N}_{UE}\).
3.4 Maximum SINR with No Limit on the Distance of Discovery Algorithm (MSNA)
MSNA discovers the D2D pairs according to the SINR values among the UEs, and the best pair with maximum SINR is determined. In this discovery algorithm, the distance among the UEs is insignificant [31]. The best D2D pair is determined by MSNA as follows:
\( 1 \le i,j \le N_{UE}\), \(i \ne j\).where \({\upgamma }^{\left(i,j\right)}\) stands for the SINR. The constraints of MSNA are the same as SDA. Firstly, UEs with SINR values greater than the threshold level are detected in the network, and then, the best D2D pair with maximum SINR values is found.
3.5 Maximum SINR with Limit on the Distance of Discovery Algorithm (MSLA)
MSLA finds the best D2D pair with maximum SINR value among the UEs in the network based on a distance constraint between UEs. In this algorithm, there is a distance threshold, unlike MSNA [31]. The best D2D pair is found by MSLA as given below:
where \({d}_{th}\) denotes the distance threshold. In MSLA, the devices are detected according to the distance values greater than the threshold value among UEs. Secondly, MSLA selects the devices with SINR values greater than the SINR threshold level among the detected devices. Finally, the best D2D pair is determined as the pair with the maximum SINR value. In this paper, five distance threshold values (50 m, 100 m, 150 m, 200 m, and 250 m) are used for D2D discovery by MSLA.
4 Results and Discussion
4.1 General Structure of the System and Sample Scenario
The example scenario in Fig. 4 deals with D2D communication in order to provide post-disaster communication. Indeed, the D2D scenarios proposed by 3GPP are taken as reference in this scenario. The disaster area is represented by the hexagons shown in red circles. UEs are randomly distributed to the disaster area in the simulation. It is assumed that device discoveries are successful so that only D2D pairs can be communicated when communication from other cellular and satellite networks is not possible. Table 3 summarizes the simulation parameters for the proposed TDA discovery method and the other discovery algorithms.
The D2D discovery simulations are made for eight different options according to the selected algorithm. The existing UEs are randomly placed in the sample scenario for the selected case during the iteration. For example, if case-1 is selected, MSNA runs and then the output values such as outage SINR, active pair1, active pair2, capacity and energy activity are calculated.
4.2 Simulation Results
The proposed TDA was examined in the sample scenario and then TDA was compared with SDA, MSNA, and MSLA versions to evaluate its performance. The distribution of UEs detected by the TDA in the disaster area is shown in Fig. 5. As can be seen from this figure, the primarily matching devices are determined among UEs placed randomly for post-disaster. In this figure, some UEs that are not selected by TDA are shown in a red dashed circle. Matching UE pairs are represented with green circle.
Figure 6 shows the performances of SINR, pair number, energy efficiency, capacity, and throughput obtained by TDA. These results are the outputs of the D2D discovery simulation using TDA under 100 iterations and 100 UEs. The first subfigure shows the SINR changes of the best D2D pair determined by TDA at the end of each iteration. The blue and red lines donate the SINR values of the best D2D pair discovered by TDA. According to the SINR result, the average SINR value of active pairs was calculated as 10.959 dB. In 2nd subfigure, the number of D2D pairs obtained by TDA among 100 UEs varies within the range of 31–39.
Table 4 summarizes the D2D discovery results of the proposed TDA and the other discovery algorithms for 100 iterations. Table's results show that TDA has better service quality than other compared algorithms by the obtained best (24%), worst (40%), and mean (32.58%) outage SINR values. Besides, TDA shows better results than the others according to the number of matching pairs. In the result of pair number discovered by TDA, the best pair number is 39, worst is 31, and the mean is 33.71 pairs, among 50 pairs after evaluating 100 UEs. Looking at the throughput statistics results, SDA gives the best results in terms of average and worst values of throughput, but SDA can only discover two pairs by its nature among 50 pairs. MSLA (50 m) has the best throughput value with 27.35 Mbps. According to the results regarding energy efficiency and capacity metrics, the proposed TDA approach did not yield the best results. The throughput values of device pairs that are close to each other are naturally high in post-disaster area, so this situation causes high energy efficiency and high capacity values in short distance. However, in post-disaster situations, it is important that the devices in the disaster area communicate with each other from the shortest distance to the farthest distance. Therefore, it is very critical that as many devices as possible can communicate with an uninterrupted communication. For all these reasons, it is anticipated that the proposed TDA approach will provide a more realistic solution in a possible post-disaster scenario.
Figure 7 shows the average number of active D2D pairs discovered by each algorithm for the different numbers of devices. The performances of the MSNA and MSLA are found to close to each other. The reason for being a constant average number of active pairs (2) in the SDA is related to the fact that there are only two pairs at the closest distance to each other with SINR values that exceed the threshold level in this algorithm. It is clear that as increasing the number of devices in PSN for post-disaster, the number of D2Ds discovered by TDA is higher than those by other discovery algorithms.
In Fig. 8, the SINR outage probability values of the matching pairs are shown by each algorithm for the different numbers of devices. Outage SINR is expected to be low values. It is concluded that it cannot find enough matching pairs for the discovery algorithms with high SINR deduction values. As can be seen from the outage SINR values of SDA in Fig. 8, the SDA selects only 2 pairs at the closest distance. As a result, SDA’s the outage SINR probability is found higher than the others. It has been observed that the outage SINR of TDA is achieved in lower levels compared with other discovery algorithms, especially for more than 20 UEs. Therefore, it is clear that the proposed algorithm finds better matching D2D pairs than other algorithms.
The curves of the throughput, energy efficiency and capacity values for TDA and the other discovery algorithms are shown in Figs. 9, 10 and 11, respectively. In here, the subfigures on the right show the results as CDF (Cumulative Distribution Function) for 50 UEs.
In the subfigures on the left, the relationships of throughput, energy efficiency, and capacity values with numbers of devices are shown. In the case where the number of devices is more than 12, it seems that the results of TDA and the other discovery algorithms are close to each other. In the CDF plot of throughput results for TDA and all discovery algorithms, TDA has the throughput outcome in the range of 3.5 Mbps and 33Mbps. The highest throughput value belongs to the TDA. According to the energy metric, TDA's result ranges from 360 Mbit/Joule-1600 Mbit/Joule. As can be seen from the capacity CDF results for TDA and the other discovery algorithms, the proposed TDA has a capacity between 25 and 150 Mbps for 50 devices.
The proposed TDA approach has one parameter (Rth) named throughput threshold. We made an analysis to see the effects of different values of this parameter. The simulation result done with the different values of the Rth parameter for the 20 UEs in the disaster area is shown in Fig. 12. Rth value ranges from 0 to 10. When looking at the number of matching device pairs from figure, it is understood that the D2D pair cannot be found after 7 Mbps of Rth. It is seen that as the Rth value gets smaller, the number of matching devices increases as expected.
5 Conclusion and Future Works
D2D discovery and communication provide communication services in disaster without network infrastructure assistance and reduce call traffic in the cellular communication network. In this scope, Throughput based discovery algorithm (TDA) was proposed for D2D peer discovery on PSN. The D2D scenario proposed by 3GPP was used for the discovery of post-disaster D2D. This scenario is tested separately for the MSNA, SDA, MSLA versions (50-250 m), and the proposed TDA using simulation parameters, and the results were obtained in terms of different metrics. UE's which are distributed randomly on simulation are examined in terms of the SINR outage percentage, average energy, capacity, throughput values, the number of the matching D2D pairs for the disaster area.
According to the statistical results, SDA and MSLA (50 m) give better results in terms of throughput, energy efficiency, and capacity metrics; but SDA discovers only two pairs at the closest distance and MSLA (50 m) finds D2D pairs within 50 m according to the SINR values of UE pairs, in this way, throughput, energy efficiency and capacity results were obtained as high. The average values of the outage SINR are obtained as 53.04% for MSLA (50 m) and 98% for SDA. These values fall behind the TDA's outage SINR values for the disaster area scenario in terms of D2D discovery and service quality. The TDA produces 32.58% for mean outage SINR, and 33.71 dB for mean SINR of the discovered D2D pairs, so these are better results than the other discovery algorithms. In the analysis made according to the numbers of users in the network, it was observed that the proposed TDA gives better results than other discovery algorithms, especially in cases with more than 20 devices in throughput and outage SINR values.
In accordance with the purpose of the study, TDA discovered the most D2D pairs in the disaster area and it was the best among other algorithms in terms of service quality. For further studies, it is recommended to focus on comparisons of TDA with different channel modes, clustering, and communication of UEs discovered outside the disaster area.
References
Nishiyama, H., Ito, M., & Kato, N. (2014). Relay-by-smartphone: Realizing multihop device-to-device communications. IEEE Communications Magazine, 52(4), 56–65. https://doi.org/10.1109/MCOM.2014.6807947.
Hicham, M., Abghour, N., & Ouzzif, M. (2016). Device-to-device (D2D) communication under LTE-advanced networks. International Journal of Wireless & Mobile Networks, 8(1), 11–22. https://doi.org/10.5121/ijwmn.2016.8102.
Baldini, G., Karanasios, S., Allen, D., & Vergari, F. (2014). Survey of wireless communication technologies for public safety. IEEE Communications Surveys and Tutorials. https://doi.org/10.1109/SURV.2013.082713.00034.
He, D., Chan, S., & Guizani, M. (2017). Drone-assisted public safety networks: the security aspect. IEEE Communications Magazine, 55(8), 218–224. https://doi.org/10.1109/MCOM.2017.1600799CM.
Shah, S. T., Hasan, S. F., Seet, B. C., Chong, P. H. J., & Chung, M. Y. (2018). Device-to-device communications: A contemporary survey. Wireless Personal Communications. https://doi.org/10.1007/s11277-017-4918-4.
Kumbhar, A., Koohifar, F., Güvenç, I., & Mueller, B. (2017). A survey on legacy and emerging technologies for public safety communications. IEEE Communications Surveys and Tutorials. https://doi.org/10.1109/COMST.2016.2612223.
Yu, W., Xu, H., Nguyen, J., Blasch, E., Hematian, A., & Gao, W. (2018). Survey of public safety communications: User-side and network-side solutions and future directions. IEEE Access. https://doi.org/10.1109/ACCESS.2018.2879760.
Pinelli, J. P., Esteva, M., Rathje, E. M., Roueche, D., Brandenberg, S. J., Mosqueda, G., Padgett, J., & Haan, F. (2020). Disaster risk management through the designsafe cyberinfrastructure. International Journal of Disaster Risk Science, 11(6), 719–734. https://doi.org/10.1007/s13753-020-00320-8.
Qadir, Z., Ullah, F., Munawar, H. S., & Al-Turjman, F. (2021). Addressing disasters in smart cities through UAVs path planning and 5G communications: A systematic review. Computer Communications, 168, 114–135. https://doi.org/10.1016/j.comcom.2021.01.003.
Ali, K., Nguyen, H. X., Shah, P., & Vien, Q. T. (2017). Energy efficient and scalable D2D architecture design for public safety network. In 2016 International Conference on Advanced Communication Systems and Information Security, ACOSIS 2016 - Proceedings. https://doi.org/10.1109/ACOSIS.2016.7843929
Kar, U. N., & Sanyal, D. K. (2020). A critical review of 3GPP standardization of device-to-device communication in cellular networks. SN Computer Science. https://doi.org/10.1007/s42979-019-0045-5.
Akyildiz, I. F., Nie, S., Lin, S. C., & Chandrasekaran, M. (2016). 5G roadmap: 10 key enabling technologies. Computer Networks, 106, 17–48. https://doi.org/10.1016/j.comnet.2016.06.010.
Gandotra, P., & Jha, R. K. (2016). Device-to-device communication in cellular networks: A survey. Journal of Network and Computer Applications. https://doi.org/10.1016/j.jnca.2016.06.004.
Mukherjee, P., & De, T. (2021). Content independent location based clustering for 5G device to device communications. Wireless Personal Communications. https://doi.org/10.1007/s11277-021-08143-6.
Chakraborty, C., & Rodrigues, J. J. C. P. (2020). A comprehensive review on device-to-device communication paradigm: Trends, challenges and applications. Wireless Personal Communications, 114, 185–207. https://doi.org/10.1007/s11277-020-07358-3.
Hayat, O., Ngah, R., & Zahedi, Y. (2019). In-band device to device (D2D) communication and device discovery: A survey. Wireless Personal Communications, 106(2), 451–472. https://doi.org/10.1007/s11277-019-06173-9.
Lin, X., Andrews, J. G., Ghosh, A., & Ratasuk, R. (2014). An overview of 3GPP device-to-device proximity services. IEEE Communications Magazine, 52(4), 40–48. https://doi.org/10.1109/MCOM.2014.6807945.
Gomez, K., Goratti, L., Rasheed, T., & Reynaud, L. (2014). Enabling disaster-resilient 4G mobile communication networks. IEEE Communications Magazine, 52(12), 66–73. https://doi.org/10.1109/MCOM.2014.6979954.
Ben Halima, N., & Boujemâa, H. (2019). Optimal routing and one hop routing for D2D communications in the presence of mutual interference. Telecommunication Systems, 71(1), 55–64. https://doi.org/10.1007/s11235-018-0512-7.
Chen, G., Tang, J., & Coon, J. P. (2018). Optimal routing for multihop social-based D2D communications in the internet of things. IEEE Internet of Things Journal, 5(3), 1880–1889. https://doi.org/10.1109/JIOT.2018.2817024.
Shaikh, F. S., & Wismuller, R. (2018). Routing in multi-hop cellular device-to-device (D2D) networks: A survey. IEEE Communications Surveys & Tutorials, 20(4), 2622–2657. https://doi.org/10.1109/COMST.2018.2848108.
Babun, L., Yürekli, A. I., & Güvenç, I. (2015). Multi-hop and D2D communications for extending coverage in public safety scenarios. In Proceedings - conference on local computer networks, LCN (Vol. 2015-Decem, pp. 912–919). https://doi.org/10.1109/LCNW.2015.7365946
Ali, K., Nguyen, H. X., Vien, Q. T., Shah, P., & Chu, Z. (2018). Disaster management using D2D communication with power transfer and clustering techniques. IEEE Access, 6, 14643–14654. https://doi.org/10.1109/ACCESS.2018.2793532.
Fodor, G., Parkvall, S., Sorrentino, S., Wallentin, P., Lu, Q., & Brahmi, N. (2014). Device-to-device communications for national security and public safety. IEEE Access, 2, 1510–1520. https://doi.org/10.1109/ACCESS.2014.2379938.
Kuang, Z., Liu, G., Li, G., & Deng, X. (2019). Energy efficient resource allocation algorithm in energy harvesting-based D2D heterogeneous networks. IEEE Internet of Things Journal, 6(1), 557–567. https://doi.org/10.1109/JIOT.2018.2842738.
Marttin, V., Yuzgec, U., Bayilmis, C., Kucuk, K. (2018). D2D Communication and Energy Efficiency on LTE for Public Safety Networks. In UBMK 2018 - 3rd ınternational conference on computer science and engineering (pp. 547–551). https://doi.org/10.1109/UBMK.2018.8566602
Kwak, Y., Ro, S., Kim, S., Kim, Y., & Lee, J. (2014). Performance evaluation of D2D discovery with eNB based power control in LTE-advanced. In 2014 IEEE 80th vehicular technology conference (VTC2014-Fall) (pp. 1–5). https://doi.org/10.1109/VTCFall.2014.6966122
Ever, E., Gemikonakli, E., Nguyen, H. X., Al-Turjman, F., & Yazici, A. (2020). Performance evaluation of hybrid disaster recovery framework with D2D communications. Computer Communications, 152, 81–92. https://doi.org/10.1016/j.comcom.2020.01.021.
Hayat, O., Ngah, R., & Mohd Hashim, S. Z. (2020). Performance analysis of device discovery algorithms for D2D communication. Arabian Journal for Science and Engineering, 45(3), 1457–1471. https://doi.org/10.1007/s13369-019-04006-2.
Hayat, O., Ngah, R., & Mohd Hashim, S. Z. (2021). Sector scanning algorithm (SSA) for device discovery in D2D communication. International Journal of Electronics, 108(1), 45–66. https://doi.org/10.1080/00207217.2020.1756453.
Osman, E. A. M. (2018). Device discovery methods in D2D communications for 5G communications system. . Tallinn University of Technology.
Kar, U. N., & Sanyal, D. K. (2018). An overview of device-to-device communication in cellular networks. ICT Express. https://doi.org/10.1016/j.icte.2017.08.002.
Araniti, G., Raschellá, A., Orsino, A., Militano, L., & Condoluci, M. (2016). Device-to-Device communications over 5G systems: Standardization, challenges and open issues. In 5G mobile communications (pp. 337–360). https://doi.org/10.1007/978-3-319-34208-5_12
Doppler, K., Rinne, M., Wijting, C., Ribeiro, C. B., & Hug, K. (2009). Device-to-device communication as an underlay to LTE-advanced networks. IEEE Communications Magazine, 47(12), 42–49. https://doi.org/10.1109/MCOM.2009.5350367.
Doppler, K., Ribeiro, C. B., & Kneckt, J. (2011). Advances in D2D communications: Energy efficient service and device discovery radio. In 2011 2nd ınternational conference on wireless communication, vehicular technology, ınformation theory and aerospace and electronic systems technology, wireless VITAE 2011. https://doi.org/10.1109/WIRELESSVITAE.2011.5940857
Tang, H., Ding, Z., & Levy, B. C. (2014). Enabling D2D communications through neighbor discovery in LTE cellular networks. IEEE Transactions on Signal Processing, 62(19), 5157–5170. https://doi.org/10.1109/TSP.2014.2348950.
Simsek, M., Merwaday, A., Correal, N., & Güvenç, I. (2013). Device-to-device discovery based on 3GPP system level simulations. In 2013 IEEE globecom workshops, GC Wkshps 2013 (pp. 555–560). https://doi.org/10.1109/GLOCOMW.2013.6825046
Vasudevan, S., Adler, M., Goeckel, D., & Towsley, D. (2013). Efficient algorithms for neighbor discovery in wireless networks. IEEE/ACM Transactions on Networking, 21(1), 69–83. https://doi.org/10.1109/TNET.2012.2189892.
Sun, G., Wu, F., Gao, X., Chen, G., & Wang, W. (2013). Time-efficient protocols for neighbor discovery in wireless Ad Hoc networks. IEEE Transactions on Vehicular Technology, 62(6), 2780–2791. https://doi.org/10.1109/TVT.2013.2246204.
Yang, Z. J., Huang, J. C., Chou, C. T., Hsieh, H. Y., Hsu, C. W., Yeh, P. C., & Alex Hsu, C. C. (2013). Peer discovery for device-to-device (D2D) communication in LTE in LTE-A networks. In 2013 IEEE globecom workshops, GC Wkshps 2013 (pp. 665–670). https://doi.org/10.1109/GLOCOMW.2013.6825064
Zou, J., Wang, M., Zhang, J., Shu, F., Wang, J., Qian, Y., Sheng, W., & Chen, Q. (2013). Discovery signal design and its application to peer-to-peer communications in OFDMA cellular networks. IEEE Transactions on Wireless Communications, 12(8), 3995–4009. https://doi.org/10.1109/TWC.2013.071613.121395.
Zou, K. J., Wang, M. W., Yang, K., Zhang, J., Sheng, W., Chen, Q., & You, X. (2014). Proximity discovery for device-to-device communications over a cellular network. IEEE Communications Magazine, 52(6), 98–107. https://doi.org/10.1109/MCOM.2014.6829951.
Yang, K., Wang, M., Zou, K., Hua, M., Hu, J., Zhang, J., Sheng, W., & You, X. (2014). Device discovery for multihop cellular networks with its application in LTE. IEEE Wireless Communications, 21(5), 24–34. https://doi.org/10.1109/MWC.2014.6940430.
Hayat, O., Ngah, R., & Zahedi, Y. (2018). Device discovery for D2D communication in in-band cellular networks using sphere decoder like (SDL) algorithm. Eurasip Journal on Wireless Communications and Networking. https://doi.org/10.1186/s13638-018-1083-8.
Yuan, H., Guo, W., & Wang, S. (2014). Emergency route selection for D2D cellular communications during an urban terrorist attack. In 2014 IEEE ınternational conference on communications workshops, ICC 2014 (pp. 237–242). https://doi.org/10.1109/ICCW.2014.6881202
Ali, K., Nguyen, H. X., Shah, P., Vien, Q. T., & Bhuvanasundaram, N. (2016). Architecture for public safety network using D2D communication. In 2016 IEEE wireless communications and networking conference workshops, WCNCW 2016 (pp. 206–211). https://doi.org/10.1109/WCNCW.2016.7552700
Wang, X., Zhou, H., Zhong, L., Ji, Y., Takano, K., Yamada, S., & Xue, G. (2016). Capacity-aware cost-efficient network reconstruction for post-disaster scenario. IEEE International Symposium on Personal, Indoor and Mobile Radio Communications, PIMRC. https://doi.org/10.1109/PIMRC.2016.7794910.
Hossain, M. A., Ray, S. K., & Lota, J. (2020). SmartDR: A device-to-device communication for post-disaster recovery. Journal of Network and Computer Applications, 171, 102813. https://doi.org/10.1016/j.jnca.2020.102813.
Rappaport, T. S. (2001). Wireless Communications: Principles and practice (Prentice Hall Communications Engineering & Emerging Technologies Series). Optimization.
Wu, Y., Liu, W., Wang, S., Guo, W., & Chu, X. (2015). Network coding in device-to-device (D2D) communications underlaying cellular networks. In IEEE ınternational conference on communications (Vol. 2015-Septe, pp. 2072–2077). https://doi.org/10.1109/ICC.2015.7248631
Author information
Authors and Affiliations
Corresponding author
Ethics declarations
Conflict of interest
The authors declare that they have no known competing financial interests or personal relationships that could have appeared to influence the work reported in this paper.
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
About this article
Cite this article
Marttin, V., Yüzgeç, U., Bayılmış, C. et al. A Novel Approach to D2D Discovery in PSN for Post-Disaster: Throughput Based Discovery Algorithm (TDA). Wireless Pers Commun 119, 3339–3363 (2021). https://doi.org/10.1007/s11277-021-08407-1
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11277-021-08407-1