Abstract
This paper presents a theoretical framework using multiple reconfigurable intelligent surfaces (RISs) for enhancing the secrecy performance of wireless systems. In particular, multiple RISs are exploited to support transmitter-legitimate user communication under the existence of an eavesdropper. Two practical scenarios are investigated, i.e., there are only transmitter-eavesdropper links (case 1) and there are both transmitter-eavesdropper and transmitter-RIS-eavesdropper links (case 2). We mathematically obtain the closed-form expressions of the average secrecy capacity (ASC) of the considered system in these two investigated cases over Nakagami-m fading channels. The impacts of the system parameters, such as the locations of the RISs, the number of REs, and the Nakagami-m channels, are deeply evaluated. Computer simulations are used to validate our mathematical analysis. Numerical results clarify the benefits of using multiple RISs for improving the secrecy performance of wireless systems. Specifically, the ASCs in cases 1 and 2 are significantly higher than that in the case without RISs. Importantly, when the locations of the RISs are fixed, we can arrange the larger RSIs near either the transmitter or legitimate user to achieve higher ASCs. In addition, when the numbers of reflecting elements (REs) in the RISs increase, the ASCs in cases 1 and 2 are greatly enhanced.
Similar content being viewed by others
Avoid common mistakes on your manuscript.
1 Introduction
In the age of the Internet of Things, besides coverage and capacity improvements, security and reliability enhancements of wireless communication systems are the key requirements, especially in the fifth and beyond generations (5G and B5G) of wireless systems [1, 2]. For the security requirements of the 5G and B5G wireless systems, physical layer security (PLS) has been proposed [3]. Unlike classical cryptographic algorithms, PLS utilizes the random nature of wireless channels for information security. Consequently, the PLS can provide secrecy performance without depending on the computation resources of wireless devices [3, 4]. As a result, the PLS is now widely considered and applied to enhance information security in 5G and B5G wireless systems [5,6,7].
On the other hand, the emergence of reconfigurable intelligent surfaces (RISs) used for assisting wireless systems has greatly attracted the attention of wireless researchers and designers [8, 9]. In particular, the RISs are equipped with many reflecting elements (REs) that can reflect signals transmitted from transmitter to receiver without signal processing [10, 11]. In addition, the RISs can work without power supply, decoding, encoding, and amplifying signals [12]. Consequently, the usage of RISs is much more effective than the usage of classical relays in wireless systems [13, 14]. Therefore, the RISs are promising candidates that can be deployed in B5G wireless systems. Nowadays, the RISs are widely used not only for improving capacity and reducing outage probability but also enhancing information security of the wireless systems [15, 16].
1.1 Related Works
In the literature, the secrecy performance of the RIS-assisted wireless systems has been analyzed in different scenarios such as in vehicular communications [5, 17], cognitive systems [18], and non-orthogonal multiple access networks [19]. Specifically, the key performance metrics such as secrecy outage probability (SOP) and secrecy ergodic capacity (SEC) have been derived for evaluating the security performance of the RIS-assisted wireless systems [4, 5, 16,17,18,19,20,21,22,23,24]. In [5, 20, 21], the authors investigated the case that the reflected signals generated by RIS were not arrived at an eavesdropper. Consequently, the eavesdropper only receives signals transmitted from the transmitter. Their numerical results observed the potential of the RIS for improving the secrecy performance of wireless systems.
In practice, besides receiving signals directly from the transmitter, the eavesdropper can receive signals reflected by the RIS. Thus, the works in [4, 16,17,18,19, 22,23,24] investigated the case that the reflected signals generated by RIS also arrive at the eavesdropper. The SOP expression was derived for the system performance analysis. It was shown that the SOP performance of the wireless systems is greatly improved when the number of REs increases [4, 16, 23]. In addition, the RIS-assisted wireless systems outperform the multiple-input multiple-output systems in terms of PLS [23]. However, the case of utilizing multi-RIS-assisted wireless systems for further enhancing the secrecy performance has not been analyzed yet.
1.2 Motivations and Contributions
As aforementioned, the secrecy performance of one-RIS-assisted wireless systems has been analyzed for both with and without reflected paths generated by RIS [4, 16, 18, 19, 21, 25,26,27]. Unfortunately, these works used only one RIS. The case of multiple RISs was not considered due to the computational complexity. Meanwhile, in practical scenarios, multiple RISs are often deployed in wireless systems [28]. In particular, multiple RISs are arranged in different areas; thus, either all RISs or some RISs can be used to assist the wireless systems depending on the specific goals [28, 29]. Generally, when multiple RISs are exploited, the performance of wireless systems is significantly improved compared with the case of only one RIS. However, the usage of multiple RISs to improve the secrecy performance of wireless systems was not studied. Furthermore, previous works only considered either the direct link or reflected RIS links at the legitimate users and/or eavesdroppers. The case that signals traveled on both direct link and reflected RIS links are combined at the legitimate users and/or eavesdropper was not considered. These issues motivate us to consider the secrecy performance of the wireless systems under the support of multiple RISs. Specifically, two practical scenarios where the eavesdropper receives signals either via only the transmitter-eavesdropper link or via transmitter-eavesdropper and transmitter-RISs-eavesdropper links are investigated. Also, the considered system is evaluated over Nakagami-m fading channels where the channel parameters are proposed for the 5G standard such as 3rd Generation Partnership Project [28, 30]. The main contributions of this paper can be summarized as follows:
-
We consider a multi-RIS-assisted wireless system under the existence of an eavesdropper. Specifically, the eavesdropper receives signals via either direct transmitter-eavesdropper links (case 1) or both direct transmitter-eavesdropper and transmitter-RIS-eavesdropper links (case 2). Additionally, multiple RISs are arranged in different areas to enhance the secrecy performance of the considered system.
-
We exploit the benefits of the traditional wireless channel and advanced RISs by combining the direct transmitter-receiver and reflect transmitter-RISs-receiver links to achieve higher signal-to-noise ratio (SNR) power at the receiver. We successfully obtain the closed-form expressions of the average secrecy capacity (ASC) of the considered system in cases 1 and 2 over Nakagami-m fading channels. We validate all derived expressions via computer simulations.
-
We evaluate the ASCs of the considered system with the channel model proposed for the 5G standardFootnote 1 Numerical results show that the ASCs of the considered system in cases 1 and 2 are significantly higher than that in the case without RISs (case 3). This observation confirms the benefits of using RISs for improving the secrecy performance of wireless systems. Another important observation is that the RISs located near either transmitter or receiver can reflect signals better than the RISs located far from either transmitter or receiver. In addition, the impacts of the number of REs, the total number of REs, the locations of the RISs, and other system parameters are also studied.
The rest of this paper is organized as follows. Section 2 describes the system and signal models, where the formulas of the received signals at the legitimate user and eavesdropper in two cases are provided in detail. Section 3 analyzes the secrecy performance of the considered system by mathematically deriving the ASC expressions in two cases. Section 4 presents the numerical results and discussions to get insights into the system behaviors. Finally, Section 5 concludes this paper.
Notations
The cumulative distribution function (CDF) and probability density function (PDF) are, respectively, denoted by F(.) and f(.); the gamma, lower, upper incomplete gamma, and Meijer functions are, respectively, denoted by \(\gamma (.,.)\), \(\Gamma (.)\), \(\Gamma (.,.)\), and \(G_{.,.}^{.,.}(.)\); the probability of an event and the expectation operator are, respectively, denoted by \(\textrm{Pr}\{.\}\) and \(\mathbb {E}\{.\}\); the Gaussian noise variable with zero mean and variance of \(\sigma ^2\) is denoted by \(C\mathcal {N}(0,\sigma ^2)\).
2 System Model
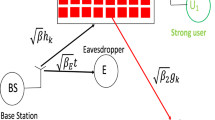
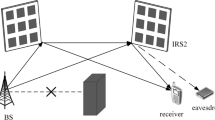
Figure 1 illustrates the multi-RIS-assisted wireless system with eavesdropper links. In particular, a base station (S) transmits signals to a legitimate user (D) via S-D direct link and S-RIS-D reflected links. Meanwhile, an eavesdropper (E) attempts to receive and decode the signals transmitted from S via S-E direct link and S-RIS-E reflected links. In the considered system, K RISs are used to assist S-D communication, where each RIS is equipped with L REs. In addition, all transceivers (S, D, and E) are equipped with a single antenna for transmitting/receiving.
Since multiple RISs are deployed to support S−D communication, the channels from RISs to E may or may not be available. As a result, we consider two scenarios: i) E only receives signals via the S-E link. The reflected links via RISs are not available at E due to blocking objects (similar to the works in [5, 20, 21]); ii) E receives signals via both S-E link and RIS reflected links.
The received signal at the legitimate user D is expressed as
where \(\hat{h}_{sd}\), \(\hat{g}_{kl}\) and \(\hat{h}_{kl}\) are, respectively, the channels from S to D, from S to the lth RE of the kth RIS, and from the lth RE of the kth RIS to D; \(\varphi _{kl}\) is the phase shift of the lth RE of the kth RIS; \(x_s\) is the transmitted signal at S; \(z_d \sim C\mathcal {N}(0,\sigma ^2_d)\) is the Gaussian noise at the D.
Using the magnitudes and phases of the complex numbers, we can represent \(\hat{h}_{sd}\), \(\hat{g}_{kl}\), and \(\hat{h}_{kl}\) as \(\hat{h}_{sd} = h_{sd} e^{-j \phi _{sd}}\), \(\hat{g}_{kl} = g_{kl} e^{-j \theta _{kl}}\), and \(\hat{h}_{kl} = h_{kl} e^{-j \psi _{kl}}\), where \(h_{sd}\), \(g_{kl}\), and \(h_{kl}\) are the magnitudes and \(\phi _{sd}\), \(\theta _{kl}\), and \(\psi _{kl}\) are the phases of \(\hat{h}_{sd}\), \(\hat{g}_{kl}\), and \(\hat{h}_{kl}\), respectively.
Now, the received signal at D becomes
where \(\zeta _{kl} = \varphi _{kl} - \theta _{kl}- \psi _{kl} +\phi _{sd}\) is the phase error induced by the lth RE of the kth RIS [28].
As demonstrated in previous works on one-RIS or multi-RIS-assisted wireless systems, the phase of the RIS \(\varphi _{kl}\) can be adjusted to achieve maximum received signal power [8, 13, 28, 31]. Specifically, \(\varphi _{kl}\) can be chosen from a set of discrete phases so that \(\zeta _{kl} = 0\) [28]. This value of \(\varphi _{kl}\) is the optimal phase of the RIS, which is computed as
With \(\varphi _{kl}^*\) of the RISs, the received signal at D now is
Since \(|e^{-j \phi _{sd}}|^2 =1\), the instantaneous signal-to-noise ratio (SNR) at D is
where \(\rho _d = P_s/\sigma ^2_d\) is the average SNR at D.
At the eavesdropper E, the received signal is computed as
where \(\hat{h}_{se}\) and \(\hat{r}_{kl}\) are, respectively, the channels from S to E and from the lth RE of the kth RIS to E; \(z_e \sim C\mathcal {N}(0,\sigma ^2_e)\) is the Gaussian noise at the E.
In the literature on RIS-assisted multi-user systems, when RISs configure their phases to maximize the SNR at one user, the SNRs at other users may not be maximized [32]. However, the case that maximum SNRs at all users is often assumed [33]. This assumption has been widely used not only for legitimate users but also for eavesdroppers [4, 16, 18, 19, 21]. Similar to these works, in this paper, we assume that the received signal at E can be maximal. In other words, we consider the worst case of the secrecy performance, where maximum SNR at the E is achieved. As a result, the received signal at E can be presented as
where \(h_{se}\) and \(\phi _{se}\) are, respectively, the amplitude and phase of \(\hat{h}_{se}\); \(r_{kl}\) is the amplitude of \(\hat{r}_{kl}\).
In case 1, due to the blocking objects, the reflected paths from the RISs are not available at E. In other words, we have \(r_{kl} =0\). Thus, the instantaneous SNR at E is expressed as
where \(\rho _e = P_s/\sigma ^2_e\) is the average SNR at E.
In case 2, the reflected paths from the RISs are available at E. Thus, the instantaneous SNR at E is
On the other hand, the CDF and PDF of the channel amplitudes (\(h_{sd}, h_{se}, g_{kl}, h_{kl}\), and \(r_{kl}\)) which follow the Nakagami-m distributions are, respectively, given by
where \(X \in \{sd, se, g_{k}, h_{k}, r_{k}\}\); \(m_{X}\) and \(\Omega _{X}\) are, respectively, the shape and spread parameters. The spread parameter calculated by the path loss model applied in the 5G standard is given as [13, 28, 30]
where \(G_\textrm{tx}\) \((\textrm{tx} \in \{s, ris\})\) and \(G_\textrm{rx}\) \((\textrm{rx} \in \{ris, d, e\})\) are, respectively, the antenna gains of the transmitter and receiver; \(f_c\) is the carrier frequency; d and \(d_0\) are, respectively, the transmitter-receiver and reference distances.
Furthermore, the variance of the Gaussian noise is given as [28]
where \(N_0\), \(\textrm{BW}\), and \(\textrm{NF}\) are, respectively, the thermal noise power density, bandwidth, and noise figure.
3 Secrecy Performance Analysis
In this section, we will derive the average secrecy capacity expression of the considered system over Nakagami-m fading channels. In particular, the ASC of the considered system is defined as the difference between the capacities of the legitimate channel and the wiretap channel. Mathematically, it is computed as [21]
where \(\beta _d\) is given in Eq. 5; \(\beta _e\) is given in Eq. 8 for case 1 and Eq. 9 for case 2; \([x]^+ = \max \{x,0\}\).
From the properties of expectation [34], Eq. 14 can be rewritten as
We should note that in case 2, \(\beta _d\) and \(\beta _e\) are not independent because of \(g_{kl}\); however, Eq. 15 is still correct due to the expectation properties. As a result, Eq. 15 has been widely utilized when calculating the ASC of RIS-assisted wireless systems [4, 19,20,21,22,23].
Consequently, the ASC of the considered system in these two cases can be, respectively, expressed as
where \(\mathcal {C}_d = \mathbb {E} \left\{ \log _2(1 + \beta _d) \right\} \), \(\mathcal {C}_e^{c1} = \mathbb {E} \left\{ \log _2(1 + \beta _e^{c1}) \right\} \), and \(\mathcal {C}_e^{c2} = \mathbb {E} \left\{ \log _2(1 + \beta _e^{c2}) \right\} \). Notice that if \(\mathcal {C}_d < \mathcal {C}_e^{c1}\), we have \(\mathcal {C}^{c1} =0\). It is similar for \(\mathcal {C}^{c2}\).
Based on Eqs. 16 and 17, we obtain the ASCs of the considered system in the following Theorem.
Theorem
The ASCs of the considered system in cases 1 and 2 over Nakagami-m fading channels are, respectively, given by
where \(\Xi _d\), \(\Psi _d\), \(\Xi _e\), and \(\Psi _e\) are, respectively, given in Eqs. 61,62,63 and 64.
Proof
: To derive the ASCs in Eqs. 18 and 19, we must firstly derive \(\mathcal {C}_d\), \(\mathcal {C}_e^{c1}\), and \(\mathcal {C}_e^{c2}\), then replace them into Eqs. 16 and 17.
First, \(\mathcal {C}_d\), \(\mathcal {C}_e^{c1}\), and \(\mathcal {C}_e^{c2}\) can be calculated as
Next, we have to obtain the CDFs of \(\beta _d\), \(\beta _e^{c1}\), and \(\beta _e^{c2}\) and then replace them into Eqs. 20,21 and 22. Mathematically, \(F_{\beta _d}(x)\), \(F_{\beta _e^{c1}}(x)\), and \(F_{\beta _e^{c2}}(x)\) are, respectively, computed as
From these above expressions, we can obtain \(F_{\beta _d}(x)\), \(F_{\beta _e^{c1}}(x)\), and \(F_{\beta _e^{c2}}(x)\) as (the detailed calculations are presented in Appendix)
On the other hand, using [35, Eq. (8.4.2.5)] and [35, Eq. (8.4.16.2)], we have
Now, \(\mathcal {C}_d\), \(\mathcal {C}_e^{c1}\), and \(\mathcal {C}_e^{c2}\) are, respectively, calculated as
Applying [35, Eq. (2.24.1.1)], Eqs. 31 and 33 respectively become
Using [36, Eq. (7.811.5)], Eq. 32 becomes
Finally, replacing Eqs. 34, 36 and 35 into Eqs. 16 and 17, we obtain the ASCs of the considered system as in Eqs. 18 and 19. The proof is thus complete.
4 Numerical Results and Discussions
In this section, the secrecy performance of the considered system is examined by using the analysis expressions. Computer simulations are used to verify our numerical expressions. Besides investigating the ASCs in cases 1 and 2, the ASC in the case without RISs (denoted by “Case 3" in all below figures) is also provided to show the benefits of using RISs. Unless otherwise specified, in all scenarios, we set \(K =5\) RISs and \(m_{sd} = m_{se} = m_{g_k} = m_{h_k} = m_{r_k} = m\). To obtain the spread parameter and noise power given in Eqs. 12 and 13, respectively, we set \(G_s = G_d = G_{ris}= 5\) dB, \(G_e= 0\) dB, \(f_c =3\) GHz, \(d_0 = 1\) m, \(d_{sd} = 100\) m, \(d_{se} =150\) m, \(\textrm{BW}=10\) MHz, \(N_0 = -174\) dBm/Hz, and \(\textrm{NF}=10\) dBm. The number of REs in each RIS is determined via vector \(\textbf{L}\), i.e., \(\textbf{L} =[L_1 \; L_2 \; L_3 \; L_4 \; L_5]\), where \(L_k\) \((k \in \{1,2,..,5\})\) denotes the number of REs in the kth RIS. Additionally, we use the coordinate axis \((x_k,y_k)\) to indicate the location of the kth RIS, with (0, 0) is the location of S.
Figure 2 illustrates the ASCs of the considered system in cases 1 and 2 in comparison with the ASC in the case without RISs (case 3) for \(m = 2\), \(\textbf{L} = [40 \; 40 \; 40 \; 40 \;40]\), and \((x,y) = (30,10), (40,10), (50,10), (60,10)\), and (70, 10). We use Eqs. 18 and 19 to obtain the analysis curves in cases 1 and 2, respectively. Notice that with the investigated parameters, the numbers of REs in all RISs are equal. However, they are located in different locations, where the 1st RIS is located nearest to the S and the 5th RIS is located furthest from the S. It is easy to see in Fig. 2 that the ASC in case 1 is the best while the ASC in case 3 is the worst. This result demonstrates the benefits of using RISs for improving the ASC of wireless systems. For example, when \(P_s =16\) dBm, the ASCs in the cases 1, 2, and 3 are, respectively, 4.4, 3.5, and 1.3 bit/s/Hz. That means cases 1 and 2 can achieve 3.1 and 2.2 bit/s/Hz higher ASC in comparison with case 3. As \(P_s\) increases, the ASCs of three cases increase. However, the increasing rates of the ASCs in cases 2 and 3 are slow in the high transmit power regime (\(P_s > 25\) dBm). Also, all ASCs gradually reach the capacity ceiling when \(P_s > 30\) dBm.
Figure 3 investigates the effects of the distance between S and E (\(d_{se}\)) on the ASCs of the considered system. As shown in Fig. 3, even \(d_{se} = 100\) m, the ASCs in cases 1 and 2 are still high, especially in case 1. Meanwhile, the ASC in case 3 equals zero. In other words, even though the distances between transmitter and legitimate user and between transmitter and eavesdropper are identical (\(d_{sd} = d_{se} = 100\) m), the usage of RISs still significantly enhances the ASC of wireless systems. Another observation is that when \(d_{se} = 100\) m, the ASCs with \(P_s = 15\) and \(P_s = 30\) dBm are similar for cases 2 and 3. Meanwhile, they are different for case 1. As \(d_{se}\) increases, the ASCs in three cases increase for both \(P_s = 15\) and \(P_s = 30\) dBm. In particular, when \(d_{se} = 200\) m, the ASCs in cases 1 and 2 are greatly higher than that in case 3 for both \(P_s = 15\) and \(P_s = 30\) dBm. Specifically, the ASCs in cases 1 and 2 with \(P_s = 15\) dBm are higher than the ASC in case 3 with \(P_s = 30\) dBm. Thus, besides enhancing the secrecy performance, the RISs help to reduce the power consumption of the transmitter. As a result, the usage of RISs can significantly improve the secrecy performance and energy efficiency of wireless systems.
In Fig. 4, the impacts of the locations of the RISs on the ASCs of the considered system are investigated. Unlike Figs. 2 and 3, the locations of all RISs in Fig. 4 are similar for each investigated scenario. For example, the 1st: (50, 10) in Fig. 4 indicates that \((x,y) = (50,10), (50,10), (50,10), (50,10)\), and (50, 10). In other words, all RISs in the 1st scenario are located right in the middle between S and D. Meanwhile, all RISs in the 2nd and 3rd scenarios are located near to S and far from S, respectively. As observed in Fig. 4, the ASCs in the 3rd scenario are the best, and the ASCs in the 1st scenario are the worst among the three scenarios. On the other hand, the ASCs of the 1st and 2nd scenarios of case 2 are nearly similar. Meanwhile, they are significantly different in case 1. Hence, the locations of the RISs greatly affect the ASCs of the considered system. Additionally, we can locate RISs near either transmitter or receiver in practice to achieve higher ASCs.
In Fig. 5, three investigated scenarios such as \(\textbf{L} = [40 \; 40 \; 40 \; 40 \;40]\), \(\textbf{L} = [10 \; 30 \; 40 \; 55 \;65]\), and \(\textbf{L} = [10 \; 20 \; 30 \; 40 \;100]\) are evaluated, where the number of REs in each RIS is varied. We should note that the total number of REs in all RISs is identical, i.e., equal to 200, in three scenarios. We also provide the ASCs in cases 1 and 2 with only one RIS (denoted by “One-RIS" in Fig. 5). Note that the ASCs with only one RIS are obtained by setting \(K=1\) RIS, \(L=200\) REs, and \((x,y) = (50,10)\). Figure 5 confirms the great benefits of the considered multi-RIS-assisted wireless system in comparison with one-RIS-assisted wireless systems presented in the previous works [4, 19, 20]. It is obvious from Fig. 5 that with these parameter settings, the ASCs in the 3rd scenario are the best while the ASCs in the 1st scenario are the worst. As a result, when the locations of the RISs are different, the ASCs can be higher with different numbers of REs in the RISs. In particular, when \(P_s = 30\) dBm, the ASCs are 5.6, 6, and 6.8 in case 1 and 3.9, 4.4, and 4.9 bit/s/Hz in case 2 corresponding to the 1st, 2nd, and 3rd scenarios. Furthermore, when the numbers of REs in the RISs vary from the 1st to the 3rd scenarios, the ASCs increase 1.2 and 1 bit/s/Hz for cases 1 and 2, respectively. Therefore, besides locating the RISs in suitable areas, we should choose an appropriate number of REs in each RIS to improve the ASC of the wireless systems.
Unlike Fig. 5, where the total number of REs in all RISs is constant, the total number of REs in all RISs in Fig. 6 is varied, i.e., \(\textbf{L} = [10 \; 10 \; 10 \; 10 \;10]\), \(\textbf{L} = [20 \; 20 \; 20 \; 20 \;20]\), ..., and \(\textbf{L} = [50 \; 50 \; 50 \; 50 \;50]\). As shown in Fig. 6, an increase of the number of REs in the RISs significantly enhances the ASCs of the considered system. Specifically, even when the number of REs in the RISs is small (i.e., \(L=10\)), the ASCs in cases 1 and 2 are still higher than that in case 3. When L increases, i.e., \(L=20, 30, 40\), and 50, the ASCs in cases 1 and 2 greatly increase, especially in case 1. Another observation is that the ASCs in cases 1 and 2 are almost linearly proportional to L. Thus, we can use larger L to achieve higher ASCs of the considered system.
In Fig. 7, the severity of Nakagami-m fading is varied, i.e., \(m=1,3\), and 5. Other system parameters are similar to those in Fig. 2. Notice that in the case \(m=1\), the Nakagami-m fading channels become the Rayleigh fading channels. Obviously, the ASCs in the three cases remarkably increase when m increases from 1 to 3. However, when m increases from 3 to 5, these ASCs are nearly unchanged. Specifically, with high transmission power, i.e., \(P_s =30\) dBm, the ASCs are similar for different m. As a result, higher values of m cannot improve the ASCs of the considered system in cases 1 and 2, even with high transmission power. Therefore, when the considered system operates in environments with higher m, we should use a suitable transmission power to exploit the benefit of these environments and avoid the ASC ceilings. On the other hand, since we set \(\rho _d = \rho _e\), the ASCs of the considered system are saturated in the high transmit power regime. This feature is reasonable because \(\beta _d\) and \(\beta _e\) are nearly parallel when \(P_s\) increases. As a result, the subtraction of \(\log _2(1 + \beta _d) - \log _2(1 + \beta _e)\) becomes a constant in the high transmit power regimeFootnote 2
5 Conclusion
This paper exploits multiple RISs to enhance the secrecy performance of a wireless system with an eavesdropper. We successfully derived the closed-form expressions of the average secrecy capacity of the considered system over Nakagami-m fading channels in two cases, where the eavesdropper receives signals from either transmitter-eavesdropper link or both transmitter-eavesdropper and transmitter-RIS-eavesdropper links. Numerical results showed that using multiple RISs significantly increases the ASCs of the considered system compared to the case without RISs. Specifically, when the number of REs in each RIS is constant, by choosing suitable locations of the RISs, the ASCs of the considered system are significantly enhanced. When the locations of the RISs are fixed, the locations near either the base station or legitimate receiver should be used for RISs with a larger number of REs to achieve higher secrecy performance. On the other hand, using RISs with larger sizes is also a suitable method for improving the secrecy performance of the considered system.
Data Availability
Data will be made available on reasonable request.
Notes
We should note that previous works, such as [4, 16], often normalized the system parameters. Thus, their results may not be suitable in 5G and B5G networks. Meanwhile, our results fully reflect the behaviors of 5G and B5G networks because the system and channel parameters are set based on practical measurements.
In the previous works, since \(\rho _e\) is fixed while \(\rho _d\) is increased when \(P_s\) increases, the ASC avoids the saturation ceilings in the high transmit power regime [4].
References
Lu W, Ding Y, Gao Y, Hu S, Wu Y, Zhao N, Gong Y (2022) Resource and trajectory optimization for secure communications in dual unmanned aerial vehicle mobile edge computing systems. IEEE Trans. Ind. Informatics 18(4):2704–2713
Hoang TM, Dung LT, Nguyen BC, Tran XN, Kim T (2021) Secrecy outage performance of FD-NOMA relay system with multiple non-colluding eavesdroppers. IEEE Trans. Veh. Technol. 70(12):12 985--12 997
Hoang TM, Duong TQ, Tuan HD, Lambotharan S, Hanzo L (2021) Physical layer security: Detection of active eavesdropping attacks by support vector machines. IEEE Access 9:31 595--31 607
Do D, Le A, Ha NX, Dao N (2022) Physical layer security for internet of things via reconfigurable intelligent surface. Future Gener. Comput. Syst. 126:330–339
Ai Y, de Figueiredo FAP, Kong L, Cheffena M, Chatzinotas S, Ottersten BE (2021) Secure vehicular communications through reconfigurable intelligent surfaces. IEEE Trans. Veh. Technol. 70(7):7272–7276
Ha D, Duy TT, Son PN, Le-Tien T, Voznák M (2021) Security-reliability trade-off analysis for rateless codes-based relaying protocols using NOMA, cooperative jamming and partial relay selection. IEEE Access 9:131 087--131 108
Thai CDT, Bao V-NQ, Vo N-S (2022) Secure communication using interference cancellation against multiple jammers. IEEE Trans. Veh, Technol
Atapattu S, Fan R, Dharmawansa P, Wang G, Evans JS, Tsiftsis TA (2020) Reconfigurable intelligent surface assisted two-way communications: Performance analysis and optimization. IEEE Trans. Commun. 68(10):6552–6567
Yu H, Tuan HD, Nasir AA, Duong TQ, Poor HV (2020) Joint design of reconfigurable intelligent surfaces and transmit beamforming under proper and improper gaussian signaling. IEEE J. Sel. Areas Commun. 38(11):2589–2603
Basar E, Renzo MD, de Rosny J, Debbah M, Alouini M, Zhang R (2019) Wireless communications through reconfigurable intelligent surfaces. IEEE Access 7:116 753--116 773
Björnson E, Sanguinetti L (2020) Power scaling laws and near-field behaviors of massive MIMO and intelligent reflecting surfaces. IEEE Open J. Commun. Soc. 1:1306–1324
Chen Y, Ai B, Zhang H, Niu Y, Song L, Han Z, Poor HV (2021) Reconfigurable intelligent surface assisted device-to-device communications. IEEE Trans. Wirel. Commun. 20(5):2792–2804
Björnson E, Özdogan Ö, Larsson EG (2020) Intelligent reflecting surface versus decode-and-forward: How large surfaces are needed to beat relaying? IEEE Wirel. Commun. Lett. 9(2):244–248
Boulogeorgos AA, Alexiou A (2020) Performance analysis of reconfigurable intelligent surface-assisted wireless systems and comparison with relaying. IEEE Access 8:94 463--94 483
ElMossallamy MA, Zhang H, Song L, Seddik KG, Han Z, Li GY (2020) Reconfigurable intelligent surfaces for wireless communications: Principles, challenges, and opportunities. IEEE Trans. Cogn. Commun. Netw. 6(3):990–1002
Yang L, Yang J, Xie W, Hasna MO, Tsiftsis T, Renzo MD (2020) Secrecy performance analysis of RIS-aided wireless communication systems. IEEE Trans. Veh. Technol. 69(10):12 296--12 300
Makarfi AU, Rabie KM, Kaiwartya O, Li X, Kharel R (2020) Physical layer security in vehicular networks with reconfigurable intelligent surfaces. In 91st IEEE Vehicular Technology Conference, VTC Spring 2020, Antwerp, Belgium, May 25-28, 2020. IEEE, pp. 1–6
Nguyen ND, Le A, Munochiveyi M (2021) Secrecy outage probability of reconfigurable intelligent surface-aided cooperative underlay cognitive radio network communications. In 22nd Asia-Pacific Network Operations and Management Symposium, APNOMS 2021, Tainan, Taiwan, September 8-10, 2021. IEEE, pp. 73–77
Tang Z, Hou T, Liu Y, Zhang J (2021) Secrecy performance analysis for reconfigurable intelligent surface aided NOMA network. In IEEE International Conference on Communications Workshops, ICC Workshops 2021, Montreal, QC, Canada, June 14-23, 2021. IEEE, pp. 1–6
Ferreira RC, Facina MSP, de Figueiredo FAP, Fraidenraich G, de Lima ER (2021) Secrecy analysis and error probability of LIS-aided communication systems under Nakagami-m fading. Entropy 23(10):1284
Khoshafa MH, Nkouatchah TMN, Ahmed MH (2021) Reconfigurable intelligent surfaces-aided physical layer security enhancement in D2D underlay communications. IEEE Commun. Lett. 25(5):1443–1447
Trigui I, Ajib W, Zhu W (2021) Secrecy outage probability and average rate of RIS-aided communications using quantized phases. IEEE Commun. Lett. 25(6):1820–1824
Zhang J, Du H, Sun Q, Ai B, Ng DWK (2021) Physical layer security enhancement with reconfigurable intelligent surface-aided networks. IEEE Trans. Inf. Forensics Secur. 16:3480–3495
Youn J, Son W, Jung BC (2021) Physical-layer security improvement with reconfigurable intelligent surfaces for 6g wireless communication systems. Sensors 21(4):1439
Tuan PV, Son PN, Duy TT, Nga TTK, Koo I et al (2022) Information security in intelligent reflecting surface-aided two-way network. In 2022 IEEE Ninth International Conference on Communications and Electronics (ICCE). IEEE, pp. 155–159
Gong C, Yue X, Wang X, Dai X, Zou R, Essaaidi M (2022) Intelligent reflecting surface aided secure communications for NOMA networks. IEEE Trans. Veh. Technol. 71(3):2761–2773
Cao K, Ding H, Li W, Lv L, Gao M, Gong F, Wang B (2022) On the ergodic secrecy capacity of intelligent reflecting surface aided wireless powered communication systems. IEEE Wirel. Commun. Lett. 11(11):2275–2279
Tran PT, Nguyen BC, Hoang TM, Le XH, Nguyen VD (2022) Exploiting multiple RISs and direct link for performance enhancement of wireless systems with hardware impairments. IEEE Trans. Commun. 70(8):5599–5611
Yang L, Yang Y, da Costa DB, Trigui I (2021) Outage probability and capacity scaling law of multiple RIS-aided networks. IEEE Wirel. Commun. Lett. 10(2):256–260
Yildirim I, Uyrus A, Basar E (2021) Modeling and analysis of reconfigurable intelligent surfaces for indoor and outdoor applications in future wireless networks. IEEE Trans. Commun. 69(2):1290–1301
Hou T, Liu Y, Song Z, Sun X, Chen Y, Hanzo L (2020) Reconfigurable intelligent surface aided NOMA networks. IEEE J. Sel. Areas Commun. 38(11):2575–2588
Tahir B, Schwarz S, Rupp M (2021) Analysis of uplink IRS-assisted NOMA under nakagami-m fading via moments matching. IEEE Wirel. Commun. Lett. 10(3):624–628
Alnwaimi G, Boujemaa H (2021) Non orthogonal multiple access using reconfigurable intelligent surfaces. Wirel. Pers. Commun. 121(3):1607–1625
Leon-Garcia A, Leon-Garcia A (2008) Probability, statistics, and random processes for electrical engineering. Pearson/Prentice Hall, 3rd ed. Upper Saddle River, NJ
Prudnikov AP (1998) Integrals and series. vol 3, More special functions; Prudnikov AP, Brychkov Yu A, Marichev OI; translated from the Russian by Gould GG. Gordon and Breach
Jeffrey A, Zwillinger D (2007) Table of integrals, series, and products. Academic press
Nguyen BC, Dung LT, Hoang TM, Tran XN, Kim T (2021) Impacts of imperfect CSI and transceiver hardware noise on the performance of full-duplex DF relay system with multi-antenna terminals over nakagami-m fading channels. IEEE Trans. Commun. 69(10):7094–7107
da Costa DB, Ding H, Ge J (2011) Interference-limited relaying transmissions in dual-hop cooperative networks over nakagami-m fading. IEEE Commun. Lett. 15(5):503–505
Funding
The authors did not receive support from any organization for the submitted work.
Author information
Authors and Affiliations
Corresponding author
Ethics declarations
Competing Interests
The authors have no competing interests to declare that are relevant to the content of this article.
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Appendix
Appendix
This appendix detailedly provides the step-by-step derivations of the CDFs of \(\beta _d\), \(\beta _e^{c1}\), and \(\beta _e^{c2}\).
Firstly, \(F_{\beta _e^{c1}}(x)\) can be derived directly by using the CDF of the channel gain following Nakagami-m fading channels [37], i.e.,
Secondly, \(F_{\beta _d}(x)\) and \(F_{\beta _e^{c2}}(x)\) are calculated as follows. Let \(\mathcal {X}_{dkl}= g_{kl} h_{kl} \), \(\mathcal {Y}_{dk} = \sum _{l=1}^{L_k} \mathcal {X}_{dkl} \), \(\mathcal {Z}_{d} = \sum _{k=1}^{K} \mathcal {Y}_{dk}\), \(\mathcal {T}_{d} = h_{sd} + \mathcal {Z}_d\), \(\mathcal {X}_{ekl}= g_{kl} r_{kl} \), \(\mathcal {Y}_{ek} = \sum _{l=1}^{L_k} \mathcal {X}_{ekl} \), \(\mathcal {Z}_e = \sum _{k=1}^{K} \mathcal {Y}_{ek}\), and \(\mathcal {T}_e = h_{se} + \mathcal {Z}_e\) be new variables, Eqs. 23 and 25 respectively become
It is obvious that \(F_{\beta _d}(x)\) and \(F_{\beta _e^{c2}}(x)\) have similar types. Thus, in the following parts, we focus on deriving \(F_{\beta _d}(x)\), \(F_{\beta _e^{c2}}(x)\) can be derived similarly as \(F_{\beta _d}(x)\).
Since the Nakagami-m fading channels are considered, the nth moment of \(h_{sd}\) is given by [28]
From Eq. 40, we obtain the first and second moments of \(h_{sd}\) as
Since \(\mathcal {X}_{dkl}= g_{kl} h_{kl} \), the PDF of \(\mathcal {X}_{dkl}\) is calculated as
Replacing the PDF given in Eq. 11 into Eq. 43, we have
Applying [36, Eq. (3.478.4)], Eq. 44 becomes
where \(\alpha _{kl} = \sqrt{\frac{m_{g_k} m_{h_k}}{\Omega _{g_k} \Omega _{h_k}}}\).
Now, the nth moment of \(\mathcal {X}_{dkl}\) is computed as
Using [36, Eq. (6.561.16)], Eq. 46 becomes
Then, the CDF of \(\mathcal {X}_{dkl}\) is given by
Now, we can derive the CDF of \(\mathcal {Y}_{dk} = \sum _{l=1}^{L_k} \mathcal {X}_{dkl} \) as
Based on [38], we obtain the nth moment of \(\mathcal {Y}_{dk}\) as
where \({a \atopwithdelims ()b} = \frac{a!}{b!(a-b)!}\), and the nth moment of \(\mathcal {Z}_d = \sum _{k=1}^{K} \mathcal {Y}_{dk}\) is
From Eqs. 47,50 and 51, we compute the first and second moments of \({\mathcal {Z}_d}\) as
Then, the nth moment of \({\mathcal {T}_{d}} = h_{sd} + {\mathcal {Z}_d}\) is calculated as
Consequently, the first and second moments of \({\mathcal {T}_d}\) calculated from Eq. 54 are
Similarly, the first and second moments of \({\mathcal {T}_e}\) are expressed as
Therefore, the CDFs of \({\mathcal {T}_d}\) and \({\mathcal {T}_e}\) are, respectively, given by
where
Next, we can calculate the CDFs of \(\beta _d\) and \(\beta _e^{c2}\) from Eqs. 38 and 39 as
Applying Eqs. 59 and 60,65, and 66 become Eqs. 26 and 28, respectively. The proof is thus complete.
Rights and permissions
Springer Nature or its licensor (e.g. a society or other partner) holds exclusive rights to this article under a publishing agreement with the author(s) or other rightsholder(s); author self-archiving of the accepted manuscript version of this article is solely governed by the terms of such publishing agreement and applicable law.
About this article
Cite this article
Nguyen, B.C., Van, QN., Dung, L.T. et al. Secrecy Performance of Multi-RIS-Assisted Wireless Systems. Mobile Netw Appl 28, 1206–1219 (2023). https://doi.org/10.1007/s11036-023-02125-7
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11036-023-02125-7