Abstract
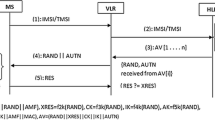
Future mobile networking will involve the convergence of different wireless networks such as 2G, 3G, WiMax and Long Term Evolution. The wide scale deployment of such heterogeneous networks will precipitate a radical change in the network infrastructure, where currently closed systems such as 3G will have to operate in an open environment. This brings to the fore certain security issues which must be addressed, the most important of which is the initial Authentication and Key Agreement to identify and authorize mobile nodes on these various networks. This paper proposes a new security protocol to authenticate the mobile terminal in heterogeneous networks.
Access provided by Autonomous University of Puebla. Download to read the full chapter text
Chapter PDF
Similar content being viewed by others
References
Jochen, S.: Mobile Communications. Addison Wesley (2003)
Aiash, M., Mapp, G., Lasebae, A.: A QoS framework for Heterogeneous Networking. In: ICWN 2011 (2011)
International Telecommunication Union (ITU-T), Global Information Infrastructure, Internet Protocol Aspects and Next Generation Networks, Y.140.1 (2004)
Almeida, M., Corujo, D., Sargento, S., Jesus, V., Aguiar, R.: An End-to-End QoS Framework for 4G Mobile Heterogeneous Environments. In: OpenNet Workshop (2007)
Lowe, G., Broadfoot, P., Dilloway, C., Hui, M.: Casper, A compiler for the Analysis of security protocol, http://www.comlab.ox.ac.uk/gavin.lowe/Security/Casper/ (accessed January 1, 2013)
Ryan, P., Schneider, S., Goldsmith, M., Lowe, G., Roscoe, A.W.: The modelling and analysis of security protocols. Pearson Ltd. (2010)
Formal Systems (Europe) Ltd.: Failures-Divergence Refinement. FDR2 User Manual, http://www.fsel.com/documentation/fdr2/fdr2manual.pdf (accessed January 1, 2013)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2013 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Aiash, M. (2013). A Formally Verified Initial Authentication and Key Agreement Protocol in Heterogeneous Environments Using Casper/FDR. In: Lopez, J., Huang, X., Sandhu, R. (eds) Network and System Security. NSS 2013. Lecture Notes in Computer Science, vol 7873. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-38631-2_65
Download citation
DOI: https://doi.org/10.1007/978-3-642-38631-2_65
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-38630-5
Online ISBN: 978-3-642-38631-2
eBook Packages: Computer ScienceComputer Science (R0)