Abstract
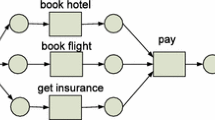
Artifact-centric modeling is an approach for modeling business processes based on business artifacts, i.e., entities that are central for the company’s operations. Existing process mining methods usually focus on traditional process-centric rather than artifact-centric models. Furthermore, currently no methods exist for discovering models in Guard-Stage-Milestone (GSM) notation from event logs. To bridge this gap, we propose a method for translating Petri Net models into GSM which gives the possibility to use the numerous existing algorithms for mining Petri Nets for discovering the life cycles of single artifacts and then generating GSM models.
Access provided by Autonomous University of Puebla. Download to read the full chapter text
Chapter PDF
Similar content being viewed by others
References
Bose, R.P.J.C., Verbeek, H.M.W., van der Aalst, W.M.P.: Discovering Hierarchical Process Models using ProM. In: Proc. of CAiSE Forum, CEUR Workshop Proc., vol. 734, pp. 33–40 (2011)
Cohn, D., Hull, R.: Business artifacts: A data-centric approach to modeling business operations and processes. IEEE Data Eng. Bull. 32, 3–9 (2009)
Günther, C., van der Aalst, W.: Mining activity clusters from low-level event logs, BETA Working Paper Series, WP 165, TU/e (2006)
Hein, J.L.: Discrete Structures, Logic, and Computability. Jones and Bartlett Publishers (2010)
Hull, R., Damaggio, E., Fournier, F., Gupta, M., Heath III, F(T.), Hobson, S., Linehan, M., Maradugu, S., Nigam, A., Sukaviriya, P., Vaculin, R.: Introducing the Guard-Stage-Milestone Approach for Specifying Business Entity Lifecycles. In: Bravetti, M. (ed.) WS-FM 2010. LNCS, vol. 6551, pp. 1–24. Springer, Heidelberg (2011)
Hull, R., et al.: Business Artifacts with Guard-Stage-Milestone Lifecycles: Managing Artifact Interactions with Conditions and Events. In: DEBS 2011, pp. 51–62 (2011)
Johnson, R., Pearson, D., Pingali, K.: The Program Structure Tree: Computing Control Regions in Linear Time. In: Proc. of the ACM SIGPLAN 1994 Conference on Programming Language Design and Implementation, pp. 171–185. ACM (1994)
Murata, T.: Petri nets: Properties, Analysis and Applications. In: Proc. of the IEEE, pp. 541–580 (1989)
Nigam, A., Caswell, N.S.: Business artifacts: An approach to operational specification. IBM Systems Journal 42(3), 428–445 (2003)
Ouyang, C., Dumas, M., Breutel, S., ter Hofstede, A.H.M.: Translating Standard Process Models to BPEL. In: Martinez, F.H., Pohl, K. (eds.) CAiSE 2006. LNCS, vol. 4001, pp. 417–432. Springer, Heidelberg (2006)
Rozinat, A., van der Aalst, W.M.P.: Decision Mining in ProM. In: Dustdar, S., Fiadeiro, J.L., Sheth, A.P. (eds.) BPM 2006. LNCS, vol. 4102, pp. 420–425. Springer, Heidelberg (2006)
van der Aalst, W., Barthelmess, P., Ellis, C., Wainer, J.: Proclets: A Framework for Lightweight Interacting Workflow Processes. Int. J. Cooperative Inf. Syst. 10(4), 443–481 (2001)
Verbeek, H., Buijs, J.C., van Dongen, B.F., van der Aalst, W.M.P.: Prom: The process mining toolkit. In: Proc. of BPM Demonstration Track. CEUR Workshop Proc., vol. 615 (2010)
Wilson, J.: Algorithms for obtaining normal forms of logical expressions. International Journal of Computer Mathematics 27(2), 85–90 (1989)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2013 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Popova, V., Dumas, M. (2013). From Petri Nets to Guard-Stage-Milestone Models. In: La Rosa, M., Soffer, P. (eds) Business Process Management Workshops. BPM 2012. Lecture Notes in Business Information Processing, vol 132. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-36285-9_38
Download citation
DOI: https://doi.org/10.1007/978-3-642-36285-9_38
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-36284-2
Online ISBN: 978-3-642-36285-9
eBook Packages: Computer ScienceComputer Science (R0)