Abstract
A new optimization metaheuristic algorithm based on the mechanisms of self-defense of plants in nature in this work is presented. The proposed optimization algorithm is applied to optimize mathematical functions of CEC 2015, this suite of functions are proposed as a challenge for the area of algorithm bio-inspired, with the purpose of creating a competition of performance and stability between algorithms of search and optimization. We propose a new meta-heuristic inspired in the coping techniques of plants in nature, as there techniques are developed by plants as a defense from predators. The proposed algorithm is based on the Lotka and Volterra model better known as the prey predator model, this model consists of two non-linear equations and is used to model the growth of two populations that competing with each other.
Access provided by CONRICYT-eBooks. Download conference paper PDF
Similar content being viewed by others
Keywords
1 Introduction
In the literature there are many optimization algorithms that have been applied to multiple problems and in some cases are successful and in others not. Each algorithm is selected depending on the problem to be solved. In the area of engineering sciences and computation there have been different meta-heuristics of optimization that have ben proposed, such as Particle swarm optimization (PSO) [15], Genetic algorithm (GA) [12], Flower pollination algorithm (FPA), Gravitational Search Algorithm (SGA), Ant colony optimization (ACO), Bee colony optimization (BCO) [1, 8].
The aforementioned algorithms have been applied to various problems such as optimization of neurons, in a neural network to improve the level of recognition of people’s faces, others for optimizing fuzzy controllers, other authors apply it to optimize mathematical functions in some cases normal functions and also in hybrid or composite functions [14, 15, 17].
All over the planet, all living organisms are exposed to a large number of threats that inhabit the environment. Therefore they force us to be in constant fight and adaptation to be immune to this type of threats [3, 4, 6]. The meta-heuristic proposed in this paper uses as a basis the Lotka and Volterra model predator-prey, which is a system formed by two nonlinear equations, are used to model the behavior of two interacting populations [7, 10].
2 Self-defense Techniques of Plants in the Nature
In nature, all living organisms on the planet are constantly fighting against different predators (fungi, bacteria, for mention some), which cause extinction or death of species [8, 13, 14, 17, 18].
Self-defense techniques are natural or developed processes that protect every living organism against different threats. The Plants are also sensitive to different stimuli. In [3,4,5, 9] the authors define the mechanisms of defense of plants in nature.
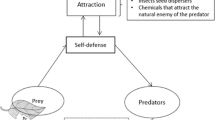
In Fig. 1 we can observe a general scheme of the behavior of the plants when they detect the attack of a predatory organism [3, 4, 9].
All plants have different strategies for example, defense techniques against predators, also techniques for adaptation to different climates such as humid, cold, sunny areas, these strategies prevent the extension of the species. However at the same time the predatory species also develop other adaptation and coping techniques, therefore both species prey and predator are always in constant fight for the survival of the best. In this work we only consider the self-defense strategies of the plants in nature.
3 Predator-Prey Model
The Lotka-Volterra equations are a biomathematical model that represents the growth of two populations interacting with each other, and the model is formed by the following Eqs. (1) and (2) [1, 3, 10,11,12]:
The definition of the parameters are observed below.
Where:
-
x: Represent the number of prey
-
y: Represent the number of predators
-
\( \frac{dx}{dt} \) Represent the growth of the population of prey time t
-
\( \frac{dy}{dt} \) Represent the growth of the population of predator at time t
-
α: It represents the birth rate of prey in the absence of predator
-
β: It represents the death rate of predators in the absence of prey.
-
δ: Measures the susceptibility of prey.
-
λ: Measures the ability of predation.
4 Case Study
In this work we propose a new application of the algorithm of plant defense, in the previous works the algorithm was used to optimize traditional mathematical benchmark functions with different methods of biological reproduction [5, 6].
In this work the proposed metaheuristic was used to optimize the functions of CEC 2015 competition, in this set of functions there are some that are composed and others that are hybrid [12, 15, 18]. Figure 2 shows a graphical representation of the proposed algorithm and the prey predator model.
In Fig. 2 we can observe both methods, the predatory prey and our proposal, where we can observe that we are applying evolutionary processes in the plant population, however the population of predators are also affected since its size is dependent on the size of the population of prey in time (t).
Plants and any other living thing in nature have different methods of biological reproduction, and in this work we are only considering the most common. For example: pollen, clone and graft. In [5, 6, 9], the authors define the different reproduction operators.
Prey and predator populations are created using the Lotka and Volterra equations, where equation one is used to generate the population of the plants and Eq. (2) is used to generate the population of the predators. In Fig. 3 shows a diagram that describes the steps of the optimization metaheuristics.
Population sizes (prey, predators) and the values of the variables (α, β, δ, λ) In [4, 6] we explain the recommended values for the variables used in the equations of the model in our proposal and also the values recommended by the creators of the prey and predator model. In [3,4,5] the authors publish results with other variants of the algorithm and we can also consult the definition of the proposed biological operators for this algorithm.
5 Simulation Results
This section shows the results obtained from the experiments performed using the optimization algorithm bioinspired on the self-defense mechanisms of the plants to the set of eight functions of the CEC-2015 [15, 18]. Based on previous publications the authors recommend using the method of pollination as reproduction operator, because it has a higher performance. 30 experiments were performed for the following mathematical functions and the evaluation is for 10, 30 Variables, Some data of the functions used can be find in Table 1, for more information of the functions please review [15, 18].
6 Parameters for the Algorithm
For this work the parameters for the variables of (α, β, δ, λ), were moved in a specific range, as mentioned before some publicaciones of the algorithm where the authors recommend a range of optimum values to improve the performance of the metaheuristic [5, 6]. And also the configuration of other parameters such as the size of populations of prey (plants), predators (herbivores).
For the CEC 2015 function problem, they recommend a range of values to be able to compete against the results found by other algorithms, in this work we only want to show that the proposed algorithm can also be used to optimize complex problems. The configuration parameters are defined below: we use plants = 400, Herbivores = 350, and the ranges for the iterations were 1000–900 to observe the behavior.
In Table 2 we can find the results obtained for the case study used in this paper. In the table we observed the results of 30 experiments for each function, using 10 and 30 dimensions, we consider important to the reader the following data the worse, best, average, and standard deviation [4, 6].
In Tables 2 and 3, we show the results obtained from 30 experiments performed for 10 and 30 variables, we can observe that in the experiments it was very difficult to approximate the value of the function to zero. The mathematical functions used are very complex, some are hybrid, multimodal and composite, and this increases the complexity therefore the algorithms need to be more efficient or use the help of other intelligent techniques such as fuzzy logic or the hybridization with another optimization algorithm. It is important to mention that some of the functions do not have their objetive value as zero.
However, in some functions, for example: f2, f4, f7, the algorithm was able to find a very good near to zero, in comparison to the others, this was for 10 variables see Table 2. Also in Table 3 we can observe the performance of the algorithm for 30 variables, where we only succeeded in the following functions: f3, f4, f6.
To conclude this work it is necessary to make a statistical comparison against other published results, the test used is z-test, in Table 4 we can observe the parameters used in this test, the results obtained with the algorithm of the mechanisms of the plants (MSPA) are compared with the Dynamic Search Fireworks Algorithm (dynFWA) [20].
In applying the statistic Z-test, with a significance level of 0.05, and the alternative hypothesis says that the average of the proposed method is lower than the average of dynFWA [20], and of course the null hypothesis tells us that the average of the proposed method is greater than or equal to the average of dynFWA [20], with a rejection region for all values fall below of −1.6715. In the Table 5 we can observe the results of the statistical comparison.
The authors of this work can observe that the comparison is not fair, the algorithm of fireworks uses fuzzy logic to adjust the parameters and our proposal is simple algorithm, however in some functions the results are very similar.
7 Conclusions
To conclude this work we consider important to mention that the main contribution of this work is to demonstrate that the proposed algorithm can also be applied to more complex problems and in this case we decided to use it for mathematical functions of the CEC-2015 benchmark, however we managed to find some values close to zero in some functions. We consider it important to mention that in this work we only use the method of reproduction by polinization, and this is recommended by the authors based on the previous experiments using this algorithm in other simpler problems for example using traditional benchmark functions. Based on the results obtained we can conclude that it is necessary to consider some improvements to the algorithm, we observe problems of local minima, and it is important to investigate other biological processes of the plants to apply them to the algorithm to solve the problem of local minima.
References
Amador-Angulo, L., Castillo, O.: A new algorithm based in the smart behavior of the bees for the design of Mamdani-style fuzzy controllers using complex non-linear plants. In: Design of Intelligent Systems Based on Fuzzy Logic, Neural Networks and Nature-Inspired Optimization, pp. 617–637. Springer (2015)
Awad, N., Ali, M.Z., Reynolds, R.G.: A differential evolution algorithm with success-based parameter adaptation for CEC 2015 learning-based optimization. In: 2015 IEEE Congress on Evolutionary Computation (CEC), pp. 1098–1105. IEEE, May 2015
Caraveo, C., Valdez, F., Castillo, O.: Bio-inspired optimization algorithm based on the self-defense mechanism in plants. In: Advances in Artificial Intelligence and Soft Computing, pp. 227–237. Springer (2015)
Caraveo, C., Valdez, F., Castillo, O.: Optimization mathematical functions for multiple variables using the algorithm of self-defense of the plants. In: Nature-Inspired Design of Hybrid Intelligent Systems, pp. 631–640. Springer (2017)
Caraveo, C., Valdez, F., Castillo, O., Melin, P.: A new metaheuristic based on the self-defense techniques of the plants in nature. In: 2016 IEEE Symposium Series on Computational Intelligence (SSCI), pp. 1–5. IEEE (2016)
Duffy, B., Schouten, A., Raaijmakers, J.M.: Pathogen self-defense: mechanisms to counteract microbial antagonism. Annu. Rev. Phytopathol. 41(1), 501–538 (2003)
Jwa, N.S., Agrawal, G.K., Tamogami, S., Yonekura, M., Han, O., Iwahashi, H., Rakwal, R.: Role of defense/stress-related marker genes, proteins and secondary metabolites in defining rice self-defense mechanisms. Plant Physiol. Biochem. 44(5), 261–273 (2006)
Karaboga, D., Basturk, B.: On the performance of Artificial Bee Colony (ABC) algorithm. Appl. Soft Comput. 8(1), 687–697 (2008)
Koornneef, A., Pieterse, C.M.: Cross talk in defense signaling. Plant Physiol. 146(3), 839–844 (2008)
Laumanns, M., Rudolph, G., Schwefel, H.P.: A spatial predator-prey approach to multi-objective optimization: a preliminary study. In: Parallel Problem Solving from Nature—PPSN V, pp. 241–249. Springer, Heidelberg (1998)
Lawson, L.M., Spitz, Y.H., Hofmann, E.E., Long, R.B.: A data assimilation technique applied to a predator-prey model. Bull. Math. Biol. 57(4), 593–617 (1995)
Li, X.: A real-coded predator-prey genetic algorithm for multiobjective optimization. In: International Conference on Evolutionary Multi-Criterion Optimization, pp. 207–221. Springer, Heidelberg, April 2003
Liang, J.J., Qu, B.Y., Suganthan, P.N., Chen, Q.: Problem definitions and evaluation criteria for the CEC 2015 competition on learning-based real-parameter single objective optimization. Technical Report 201411A, Computational Intelligence Laboratory, Zhengzhou University, Zhengzhou China and Technical Report, Nanyang Technological University, Singapore (2014)
Ochoa, P., Castillo, O., Soria, J.: Fuzzy differential evolution method with dynamic parameter adaptation using type-2 fuzzy logic. In: 2016 IEEE 8th International Conference on Intelligent Systems (IS), pp. 113–118. IEEE (2016)
Olivas, F., Valdez, F., Castillo, O., Melin, P.: Dynamic parameter adaptation in particle swarm optimization using interval type-2 fuzzy logic. Soft. Comput. 20(3), 1057–1070 (2016)
Peraza, C., Valdez, F., Castillo, O.: A harmony search algorithm comparison with genetic algorithms. In: Fuzzy Logic Augmentation of Nature-Inspired Optimization Metaheuristics, pp. 105–123. Springer (2015)
Pérez, J., Valdez, F., Castillo, O.: Modification of the bat algorithm using fuzzy logic for dynamical parameter adaptation. In: 2015 IEEE Congress on Evolutionary Computation (CEC), pp. 464–471. IEEE (2015)
Rodríguez, L., Castillo, O., Soria, J.: Grey wolf optimizer with dynamic adaptation of parameters using fuzzy logic. In: 2016 IEEE Congress on Evolutionary Computation (CEC), pp. 3116–3123. IEEE (2016)
Tanweer, M.R., Suresh, S., Sundararajan, N.: Improved SRPSO algorithm for solving CEC 2015 computationally expensive numerical optimization problems. In: 2015 IEEE Congress on Evolutionary Computation (CEC), pp. 1943–1949. IEEE (2015)
Yu, C., Kelley, L.C., Tan, Y. Dynamic search fireworks algorithm with covariance mutation for solving the CEC 2015 learning based competition problems. In: 2015 IEEE Congress on Evolutionary Computation (CEC), pp. 1106–1112. IEEE (2015)
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2018 Springer International Publishing AG
About this paper
Cite this paper
Caraveo, C., Valdez, F., Castillo, O. (2018). A New Optimization Metaheuristic Based on the Self-defense Techniques of Natural Plants Applied to the CEC 2015 Benchmark Functions. In: Kacprzyk, J., Szmidt, E., Zadrożny, S., Atanassov, K., Krawczak, M. (eds) Advances in Fuzzy Logic and Technology 2017. EUSFLAT IWIFSGN 2017 2017. Advances in Intelligent Systems and Computing, vol 641. Springer, Cham. https://doi.org/10.1007/978-3-319-66830-7_34
Download citation
DOI: https://doi.org/10.1007/978-3-319-66830-7_34
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-319-66829-1
Online ISBN: 978-3-319-66830-7
eBook Packages: EngineeringEngineering (R0)