Abstract
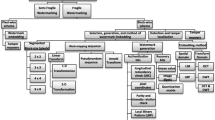
Fragile watermarking is one of the most effective approaches to insure the integrity of digital images. In this paper, an efficient self-recovery and tamper localization scheme using fragile watermarking is proposed. The proposed method generates 12-bit tamper detection data and 20-bit self-recovery data for each 4 \(\times \) 4 block. The generated tamper detection and self-recovery features are encrypted by utilizing user secrete key. A random block mapping scheme is used to embed the encrypted block features into its mapping block. The proposed two-level tamper detection creates high capacity for tamper detection data which improves the security and tamper localization. The performance of the proposed scheme and its robustness against famous security attacks is analyzed. The experimental results demonstrate the high efficiency of the proposed scheme in terms of tamper detection rate, tamper localization and self-recovery. This method is robust against security attacks such as collage attack and constant average attack.
Access provided by Autonomous University of Puebla. Download to read the full chapter text
Chapter PDF
Similar content being viewed by others
References
Dadkhah, S., Manaf, A.A., Sadeghi, S.: Efficient digital image authentication and tamper localization technique using 3lsb watermarking. International Journal of Computer Science Issues (IJCSI) 9 (2012)
Lin, P.L., Hsieh, C.-K., Huang, P.-W.: A hierarchical digital watermarking method for image tamper detection and recovery. Pattern Recognition 38(12), 2519–2529 (2005)
Lee, T.-Y., Lin, S.D.: Dual watermark for image tamper detection and recovery. Pattern Recognition 41(11), 3497–3506 (2008)
Yang, C.-W., Shen, J.-J.: Recover the tampered image based on vq indexing. Signal Processing 90(1), 331–343 (2010)
Patra, B., Patra, J.C.: Crt-based fragile self-recovery watermarking scheme for image authentication and recovery. In: IEEE International Symposium on Intelligent Signal Processing and Communication Systems (ISPACS), pp. 430–435 (2012)
Tong, X., Liu, Y., Zhang, M., Chen, Y.: A novel chaos-based fragile watermarking for image tampering detection and self-recovery. Signal Processing: Image Communication 28(3), 301–308 (2013)
Chang, C.-C., Chen, K.-N., Lee, C.-F., Liu, L.-J.: A secure fragile watermarking scheme based on chaos-and-hamming code. Journal of Systems and Software 84(9), 1462–1470 (2011)
Zhu, X., Ho, A.T., Marziliano, P.: A new semi-fragile image watermarking with robust tampering restoration using irregular sampling. Signal Processing: Image Communication 22(5), 515–528 (2007)
Wang, L.-J., Syue, M.-Y.: A wavelet-based multipurpose watermarking for image authentication and recovery. International Journal of Communications 2(4) (2013)
Qian, Z., Feng, G., Zhang, X., Wang, S.: Image self-embedding with high quality restoration capability. Digital Signal Processing 21(2), 278–286 (2011)
Holliman, M., Memon, N.: Counterfeiting attacks on oblivious block-wise independent invisible watermarking schemes. IEEE Transactions on Image Processing 9(3), 432–441 (2000)
Fridrich, J., Goljan, M., Memon, N.: Cryptanalysis of the yeung-mintzer fragile watermarking technique. Journal of Electronic Imaging 11(2), 262–274 (2002)
Chang, C.-C., Fan, Y.-H., Tai, W.-L.: Four-scanning attack on hierarchical digital watermarking method for image tamper detection and recovery. Pattern Recognition 41(2), 654–661 (2008)
Ng, T.-T., Chang, S.-F., Hsu, J., Pepeljugoski, M.: Columbia photographic images and photo realistic computer graphics dataset, Columbia Univ., New York, ADVENT Tech. Rep., 205–2004 (2005)
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2014 Springer International Publishing Switzerland
About this paper
Cite this paper
Dadkhah, S., Manaf, A.A., Sadeghi, S. (2014). An Efficient Image Self-recovery and Tamper Detection Using Fragile Watermarking. In: Campilho, A., Kamel, M. (eds) Image Analysis and Recognition. ICIAR 2014. Lecture Notes in Computer Science(), vol 8814. Springer, Cham. https://doi.org/10.1007/978-3-319-11758-4_55
Download citation
DOI: https://doi.org/10.1007/978-3-319-11758-4_55
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-319-11757-7
Online ISBN: 978-3-319-11758-4
eBook Packages: Computer ScienceComputer Science (R0)