Abstract
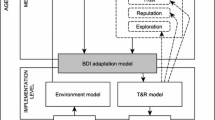
Understanding agent trustworthiness in a multiagent system is a prerequisite for evaluating network state and determining when corrective actions are needed. Untrustworthy agents may disrupt network operation by sending erroneous data or initiating malicious or inadvertently dangerous transactions. This chapter defines key parameters of trust and reputation and surveys the state-of-practice in trust ontology, modeling, and evaluation. Agent health is a key aspect of trust but is not often included in conventional trust analyses. This chapter describes a means for accommodating health information as a component of trust and discusses architectures for collecting and using health information. The concluding section demonstrates one model of trust based on an experimental approach developed for a large system of systems.
Currently employed at Jet Propulsion Laboratory, California Institute of Technology. This work was done as a private venture and not in the author’s capacity as an employee of the Jet Propulsion Laboratory, California Institute of Technology.
Similar content being viewed by others
References
Wang Y and Vassileva J (2003) “Trust and Reputation Model in Peer-to-Peer Networks,” in Proc. Third International Conference on Peer-to-Peer Computing (P2P2003), Linkoping, Sweden, pp. 150–157
Avizienis A, Laprie J.-C, Randell, B, and Landwehr C (2004) “Basic concepts and taxonomy of dependable and secure computing,” IEEE Transactions on Dependable Computing, vol. 1, no. 1, pp. 11–33, https://doi.org/10.1109/tdsc.2004.2.
Komiak SX and Benbasat I (2004) “A Process Tracing Study on Trust Formation in Recommendation Agents,” Proceedings of the Third Annual Workshop on HCI Research in MIS, Washington, D.C.
Guzmán R, Harrison R, Abarca N, and Villena MG (2020) “A game-theoretic model of reciprocity and trust that incorporates personality traits,” Journal of Behavioral and Experimental Economics, Volume 84
Chin SH (2009) “On application of game theory for understanding trust in networks,” 2009 International Symposium on Collaborative Technologies and Systems, Baltimore, MD, pp. 106–110, https://doi.org/10.1109/CTS.2009.5067469.
Abusitta A, Bellaiche M, and Dagenais M (2018) “A trust-based game theoretical model for cooperative intrusion detection in multi-cloud environments,” 2018 21st Conference on Innovation in Clouds, Internet and Networks and Workshops (ICIN), Paris, pp. 1–8, https://doi.org/10.1109/ICIN.2018.8401625.
Sabater J and Sierra C (2005) “Review on Computational Trust and Reputation Models,” Artificial Intelligence Review 24, pp. 33–60, 2005, https://doi.org/10.1007/s10462-004-0041-5
Huang J, and Fox MS (2006) “An Ontology of Trust – Formal Semantics and Transitivity,” Proceedings of the International Conference on Electronic Commerce, Association of Computing Machinery, pp. 259–270
Sievers M, Madni AM, and Pouya P (2019) “Trust and Reputation in Multi-Agent Resilient Systems,” 2019 IEEE International Conference on Systems, Man and Cybernetics (SMC)
Viljanen L (2005) Towards an ontology of trust. In: Katsikas, S, López, J, Pernul, G (eds.), TrustBus 2005. LNCS, 3592, pp. 175–184. Springer, Heidelberg
Ceolin D, Nottamkandath A, Fokkink W, and Maccatrozzo M (2014) “Toward the Definition of an Ontology for Trust in (Web) Data,” CEUR Workshop Proceedings. 1259
Alnemr R, Paschke A, and Meinel C (2010) “Enabling reputation interoperability through semantic technologies,” I-SEMANTICS, pp. 1–9. ACM
O’Hara K (2012) “A General Definition of Trust,” Technical Report, University of Southampton
Veloudis S, Paraskakis I, Petsos C, Verginadis Y, Patiniotakis I, Gouvas P, and Mentzas G (2019) “Achieving security-by-design through ontology-driven attribute-based access control in cloud environments,” Future Generation Computer Systems, 93, 373–391, ISSN 0167-739X, https://doi.org/10.1016/j.future.2018.08.042
Amaral G, Prince Sales T, Guizzardi G, and Porello D (2019) “Towards a Reference Ontology of Trust,” https://doi.org/10.1007/978-3-030-33246-4_1
Mui L, Mohtashem M, and Halberstadt A (2002) “A Computational Model of Trust and Reputation,” Proceedings of the 35th Hawaii International Conference on System Sciences
Janiszewski M (2017) “Towards an Evaluation Model of Trust and Reputation Management Systems,” Intl Journal of Electronics and Telecommunications, vol. 63, no. 4, pp. 411–416
Kamvar SD, Schlosser MT, and Garcia-Molina H (2003) “The Eigen Trust Algorithm for Reputation Management in P2P Networks,” in Proc. of the Twelfth International World Wide Web Conference
Sievers M, Madni AM, and Pouya P (2018) “Assuring Spacecraft Swarm Resilience,” in Proc. AIAA Scitech, San Diego
Michael Sievers, Arun Viswanathan (2021) An Experimental Reputation Algorithm for Detecting Anomalous Peers in Large Communication Networks AIAA ASCEND, pp. 11
Schlosser A, Voss M, and Brückner L (2004) “Comparing and Evaluating Metrics for Reputation Systems by Simulation,” Proceedings of the IEEE Workshop on Reputation in Agent Societies
International Conference on Web Intelligence (WI 2003), Halifax, NS, Canada, 2003, pp. 372–378, https://doi.org/10.1109/WI.2003.1241218.
D’Angelo G, Rampone S, & Palmieri F (2007) “Developing a trust model for pervasive computing based on A priori association rules learning and Bayesian classification,” Soft Comput 21, 6297–6315, https://doi.org/10.1007/s00500-016-2183-1
Sardana N, Cohen R, Zhang J, and Chen S (2018) “A Bayesian Multiagent Trust Model for Social Networks,” in IEEE Transactions on Computational Social Systems, vol. 5, no. 4, pp. 995–1008, https://doi.org/10.1109/TCSS.2018.2879510.
Bellman R (1956) “Dynamic Programming and Lagrange Multipliers,” Proc Natl Acad Sci USA, vol 42, no. 10, 767–769
Kaelbling LP, Littman ML, and Cassandra AR (1998) “Planning and Acting in Partially Observable Stochastic Domains,” Artificial Intelligence 101, pp. 99–134
Wang N, Pynadath D, Hill S, and Merchant C (2017) “The Dymanics of Human-Agent Trust with POMDP-Generated Explanations,” In: Beskow J., Peters C., Castellano G., O’Sullivan C., Leite I., Kopp S. (eds) Intelligent Virtual Agents, Lecture Notes in Computer Science, vol 10498. Springer, Cham. https://doi.org/10.1007/978-3-319-67401-8_58: Beskow J., Peters C., Castellano G., O’Sullivan C., Leite I., Kopp S. (eds) Intelligent Virtual Agents. IVA 2017. Lecture Notes in Computer Science, vol 10498. Springer, Cham. https://doi.org/10.1007/978-3-319-67401-8_58
Chen M, Nikolaidis S, Soh H, Hsu D, and Siddhartha S (2018) “Trust-Aware Decision Making for Human-Robot Collaboration: Model Learning and Planning,” In: Proceedings of the 2018 ACM/IEEE international conference on human–robot interaction, pp 307–315
Okamura K and Yamada S (2020) “Empirical Evaluations of Framework for Adaptive Trust Calibration in Human-AI Cooperation,” IEEE Access, vol. 8, pp. 220335–220351, https://doi.org/10.1109/ACCESS.2020.3042556
Sun YL, Han Z, Yu W, and Liu K.J, “Attacks on Trust Evaluation in Distributed Networks,” 2006 40th Annual Conference on Information Sciences and Systems, Princeton, NJ, 2006, pp. 1461–1466, https://doi.org/10.1109/CISS.2006.286695
Koppel A, Warnell G, Stump E, Stone P, and Ribeiro A, “Policy Evaluation in Continuous MDPs with Efficient Kernelized Gradient Temporal Difference,” IEEE Transactions on Automatic Control, https://doi.org/10.1109/TAC.2020.3029315, 2020
Sardana N, Cohen R, Zhang J, and Chen S (2018) “A Bayesian Multiagent Trust Model for Social Networks,” IEEE Transactions on Computational Social Systems, vol. 5, no. 4, pp. 995–1008, https://doi.org/10.1109/TCSS.2018.2879510
Mitra S and McCluskey E (2000) “Which Concurrent Error Detection Scheme to Choose,” Proceedings International Test Conference 2000 (IEEE Cat. No.00CH37159), Atlantic City, NJ, USA, pp. 985–994, https://doi.org/10.1109/TEST.2000.894311.
Mahmood A and McCluskey E (1998) “Concurrent error detection using watchdog processors-a survey,” in IEEE Transactions on Computers, vol. 37, no. 2, pp. 160–174, https://doi.org/10.1109/12.2145.
Gizopoulos D, et al. (2011) “Architectures for online error detection and recovery in multicore processors,” 2011 Design, Automation & Test in Europe, Grenoble, pp. 1–6, https://doi.org/10.1109/DATE.2011.5763096.
Yu Y, Li X, Leng X, Song L, Bu K, Chen Y, Yang J, Zhang L, Cheng K, and Xiao X (2019) “Fault Management in Software Defined Networking: A Survey, IEEE Communications Surveys and Tutorials, vol 21, no. 1, pp. 349–392
Caballero J, Yin H, Liang Z, and Song D, (2007) “Polyglot: Automatic Extraction of Protocol Message Format Using Binary Analysis,” CCS’07, Alexandria, Virginia, USA
Alharbi S, Rodriguez P, Maharaja R, Iyer P, Subaschandrabose N, and Ye Z (2017) “Secure the Internet of Things with Challenge Response Authentication in Fog Computing,” 2017 IEEE 36th International Performance Computing and Communications Conference (IPCCC), San Diego, CA, pp. 1–2, 2017, https://doi.org/10.1109/PCCC.2017.8280489.
Kushwaha P, Sonkar H, Altaf F, Maity S (2021) “A Brief Survey of Challenge–Response Authentication Mechanisms.” In: Fong S., Dey N., Joshi A. (eds) ICT Analysis and Applications. Lecture Notes in Networks and Systems, vol 154. Springer, Singapore, https://doi.org/10.1007/978-981-15-8354-4_57
Isermann R (2005) “Model-Based Fault Detection and Diagnosis – Status and Applications,” Annual Reviews in Control, no. 29, pp. 71–85
Kocio K, Fesq L, and Mackey R (2017) “Model-Based Approach to Rover Health Assessment for Increased Productivity,” 2017 IEEE Aerospace Conference, Big Sky, MT, pp. 1–13, https://doi.org/10.1109/AERO.2017.7943835
Uesato J, Kumar A, Szepesvari C, Erex T, Ruderman A, Anderson K, Dvijotham K, Heess, N, and Kohli P (2018) “Rigorous Agent Evaluation: An Adversarial Approach to Uncover Catastrophic Failures,” arXiv:1812.01647
Alford A, Wilkes M, and Kawamura K (2000) “System Status Evaluation: Monitoring the State of Agents in a Humanoid System,” SMC 2000 conference proceedings. 2000 IEEE International Conference on Systems, Man and Cybernetics, vol. 2, pp. 943–948, Nashville, TN, https://doi.org/10.1109/ICSMC.2000.885971
Sievers M and Madni AM (2015) “Defining Credible Faults, A Risk-Based Approach,” AIAA Space
Xie T, Ma Y, and Wang Y-X (2019) “Towards Optimal Off-Policy Evaluation for Reinforcement Learning with Marginalized Importance Sampling, “33rd Conference on Neural Information Processing Systems (NeurIPS 2019), Vancouver, Canada
Abdelgayed T, Morsi W, and Sidhu T (2018) “Fault Detection and Classification Based on Co-training of Semisupervised Machine Learning,” in IEEE Transactions on Industrial Electronics, vol. 65, no. 2, pp. 1595–1605, https://doi.org/10.1109/TIE.2017.2726961
Zidi S, Moulahi T, and Alaya B (2018) “Fault Detection in Wireless Sensor Networks Through SVM Classifier,” in IEEE Sensors Journal, vol. 18, no. 1, pp. 340–347, https://doi.org/10.1109/JSEN.2017.2771226
Umer M, Sher M, and Bi Y (2017) “Flow-Based Intrusion Detection: Techniques and Challenges,” Computer and Security, vol 70, pp. 238–254
U.S. Department of Homeland Security, “Cyber Security Division Technology Guide,” vol. 1 https://www.dhs.gov/sites/default/files/publications/CSD%20Tech%20Guide-.pdf
U.S. Department of Homeland Security, “Cyber Security Division Technology Guide,” vol. 2 https://www.dhs.gov/sites/default/files/publications/csd-ttp-technology-guide-volume-2.pdf
Peón, PG, Steiner, W, and Uhlemann, E, “Network Fault Tolerance by Means of Diverse Physical Layers,” 2020 25th IEEE International Conference on Emerging Technologies and Factory Automation (ETFA), Vienna, Austria, 2020, pp. 1697–1704, https://doi.org/10.1109/ETFA46521.2020.9212131.
Lamport L, Shostak R, and Pease M (1982) “The Byzantine Generals Problem,” ACM Transactions on Programming Languages and Systems, vol. 4, no. 3, pp. 382–401
Gao, S, Yu, T, Zhu, J, and Cai, W, “T-PBFT: An EigenTrust-based practical Byzantine fault tolerance consensus algorithm,” in China Communications, vol. 16, no. 12, pp. 111–123, Dec. 2019, https://doi.org/10.23919/JCC.2019.12.008
ElDefrawy, K, and Kaczmarek, T, “Byzantine Fault Tolerant Software-Defined Networking (SDN) Controllers,” 2016 IEEE 40th Annual Computer Software and Applications Conference (COMPSAC), Atlanta, GA, USA, 2016, pp. 208–213, https://doi.org/10.1109/COMPSAC.2016.76
Sievers, M, Madni, AM, Pouya, P, “Assuring Spacecraft Swarm Byzantine Resilience,” AIAA Scitech, 2019
NASA, Office of Inspector General, “Cybersecurity Management and Oversight at the Jet Propulsion Laboratory, Report No. IG-19-022, June, 18, 2019
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Section Editor information
Rights and permissions
Copyright information
© 2022 Springer Nature Switzerland AG
About this entry
Cite this entry
Sievers, M. (2022). Modeling Trust and Reputation in Multiagent Systems. In: Madni, A.M., Augustine, N., Sievers, M. (eds) Handbook of Model-Based Systems Engineering. Springer, Cham. https://doi.org/10.1007/978-3-030-27486-3_52-1
Download citation
DOI: https://doi.org/10.1007/978-3-030-27486-3_52-1
Received:
Accepted:
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-030-27486-3
Online ISBN: 978-3-030-27486-3
eBook Packages: Springer Reference Intelligent Technologies and RoboticsReference Module Computer Science and Engineering