Abstract
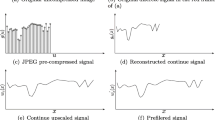
With the availability of highly sophisticated editing tools, the authenticity of digital images has now become questionable. The level of image tampering is getting higher and higher, and the tampering procedures become more and more complicated. To recognize the tampering area of the original image, the tampered image is usually executed a series of post-processing. This behavior has greatly increased the difficulty of forgery detection. In this paper, a blind JPEG image forgery detection and localization technique based on JPEG and resampling artifacts analysis is proposed. The process of tampering is to first tamper with JPEG images by bitmaps. Then original JPEG image and tampered area are manipulated by a series of operations, that is, the image is enlarged and then saved as JPEG. A novel tampering localization method is presented based on resampling and JPEG blockness artifacts. Theoretical analysis and experimental results show that the proposed method can effectively identify and locate the tampered region of a spliced image with a JPEG-resampling-JPEG operation chain.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Haouzia, A., Noumeir, R.: Methods for image authentication: a survey. Multimed. Tools Appl. 39(1), 1–46 (2008)
Sreenivas, K., Kamkshi, P.V.: Fragile watermarking schemes for image authentication: a survey. Multimed. Tools Appl. 9(7), 1193–1218 (2018)
Qazi, T., Hayat, K., Khan, S.U.: Survey on blind image forgery detection. IET Image Process. 28(2), 660–670 (2013)
Birajdar, G.K., Mankar, V.H.: Digital image forgery detection using passive techniques: a survey. Digit. Investig. 10(3), 226–245 (2013)
Singh, A.K.: Improved hybrid algorithm for robust and imperceptible multiple watermarking using digital images. Multimed. Tools Appl. 76(6), 8881–8900 (2017)
Kim, C., Shin, D., Leng, L., Yang, C.N.: Lossless data hiding for absolute moment block truncation coding using histogram modification. J. Real-Time Image Process. 14(1), 101–114 (2018)
Lin, O., Yan, H., Huang, Z.: An ID-based linearly homomorphic signature scheme and its application in blockchain. IEEE Access. 6, 20632–20640 (2018)
Alpar, O., Harel, J., Krejcar, O.: Online signature verification by spectrogram analysis. Appl. Intell. 48(5), 1189–1199 (2018)
Huang, Y., Cao, L., Zhang, J., Pan, L., Liu, Y.: Exploring feature coupling and model coupling for image source identification. IEEE Trans. Inf. Forensic Secur. 13(12), 3108–3121 (2018)
Sameer, V., Sugumaran, S., Naskar, R.: K-unknown models detection through clustering in blind source camera identification. IET Image Process. 12(7), 1204–1213 (2018)
Qiao, T., Zhu, A., Retraint, F.: Exposing image resampling forgery by using linear parametric model. Multimed. Tools Appl. 77(2), 1501–1523 (2018)
Hilal, A.: Image re-sampling detection through a novel interpolation kernel. Forensic Sci. Int. 287, 25–35 (2018)
Birajdar, G.K., Mankar, V.H.: Blind method for rescaling detection and rescale factor estimation in digital images using periodic properties of interpolation. AEU-Int. J. Electron. Commun. 68(7), 644–652 (2014)
Shin, H.J., Jeon, J.J., Eom, I.K.: Color filter array pattern identification using variance of color difference image. J. Electron. Imaging 26(4), 1501–1523 (2018)
Chang, T.Y., Tai, S.C., Lin, G.S.: A passive multi-purpose scheme based on periodicity analysis of CFA artifacts for image forensics. J. Vis. Commun. Image Represent. 25(6), 1289–1298 (2014)
Yao, H., Wang, S., Zhang, X.: Detecting image splicing based on noise level inconsistency. Multimed. Tools Appl. 76(10), 12457–12479 (2017)
Yao, H., Cao, F., Tang, Z.: Expose noise level inconsistency incorporating the inhomogeneity scoring strategy. Multimed. Tools Appl. 77(14), 18139–18161 (2018)
Yao, H., Wang, S., Zhao, Y.: Detecting image forgery using perspective constraints. IEEE Signal Process. Lett. 19(3), 123–126 (2012)
Bhardwaj, D., Pankajakshan, V.: Image overlay text detection based on JPEG truncation error analysis. IEEE Signal Process. Lett. 23(8), 1027–1031 (2016)
Yang, J., Zhu, G., Huang, J.: Estimating JPEG compression history of bitmaps based on factor histogram. Digit. Signal Prog. 41, 90–97 (2015)
Thanh, H.T., Cogranne, R., Retraint, F.: JPEG quantization step estimation and its applications to digital image forensics. IEEE Trans. Inf. Forensic Secur. 12(1), 123–133 (2017)
Li, B., Ng, T.T., Li, X.: Revealing the trace of high-quality JPEG compression through quantization noise analysis. IEEE Trans. Inf. Forensic Secur. 10(3), 558–573 (2015)
Luo, W., Huang, J., Qiu, G.: JPEG error analysis and its applications to digital image forensics. IEEE Trans. Inf. Forensic Secur. 5(3), 480–491 (2010)
Taimori, A., Razzazi, F., Behrad, A.: Quantization-unaware double JPEG compression detection. J. Math. Imaging Vis. 54(3), 269–286 (2016)
Yang, J., Xie, J., Zhu, G.: An effective method for detecting double JPEG compression with the same quantization matrix. IEEE Trans. Inf. Forensic Secur. 9(11), 1933–1942 (2014)
Pasquini, C., Boato, G., Perez-Gonzalez, F.: Multiple JPEG compression detection by means of Benford-Fourier coefficients. In: 2014 IEEE International Workshop on Information Forensics and Security (WIFS), pp. 113–118 (2014)
Milani, S., Tagliasacchi, M., Tubaro, S.: Discriminating multiple JPEG compression using first digit features. In: 2012 IEEE International Conference on Acoustics, Speech and Signal Processing, pp. 2253–2256 (2012)
Farid, H.: Exposing digital forgeries from JPEG ghosts. IEEE Trans. Inf. Forensic Secur. 4(1), 154–160 (2009)
Wang, W., Dong, J., Tan, T.: Exploring DCT coefficient quantization effects for local tampering detection. IEEE Trans. Inf. Forensic Secur. 9(10), 1653–1666 (2014)
Iakovidou, C., Zampoglou, M., Papadopoulos, S.: Content-aware detection of JPEG grid inconsistencies for intuitive image forensics. J. Vis. Commun. Image Represent. 26(4), 155–170 (2018)
Chen, Z., Zhao, Y., Ni, R.: Detection of operation chain: JPEG-Resampling-JPEG. Signal Process.-Image Commun. 57, 8–20 (2017)
Mahdian, B., Saic, S.: Blind authentication using periodic properties of interpolation. IEEE Trans. Inf. Forensic Secur. 3(3), 529–538 (2008)
Schaefer, G., Stich, M.: UCID - An uncompressed colour image database. In: 2014 Conference on Storage and Retrieval Methods and Applications for Multimedia, pp. 472–480 (2004)
Acknowledgments
This work was supported in part by the National Natural Science Foundation of China (61702332, 61672354, 61562007), Research Fund of Guangxi Key Lab of Multi-source Information Mining & Security (MIMS16-03), the Guangxi Natural Science Foundation (2017GXNSFAA198222), the Guangxi Collaborative Innovation Center of Multi-source Information Integration and Intelligent Processing. The authors would like to thank the anonymous reviewers for their helpful comments.
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2020 Springer Nature Switzerland AG
About this paper
Cite this paper
Wei, H., Yao, H., Qin, C., Tang, Z. (2020). Automatic Forgery Localization via Artifacts Analysis of JPEG and Resampling. In: Yang, CN., Peng, SL., Jain, L. (eds) Security with Intelligent Computing and Big-data Services. SICBS 2018. Advances in Intelligent Systems and Computing, vol 895. Springer, Cham. https://doi.org/10.1007/978-3-030-16946-6_18
Download citation
DOI: https://doi.org/10.1007/978-3-030-16946-6_18
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-030-16945-9
Online ISBN: 978-3-030-16946-6
eBook Packages: Intelligent Technologies and RoboticsIntelligent Technologies and Robotics (R0)